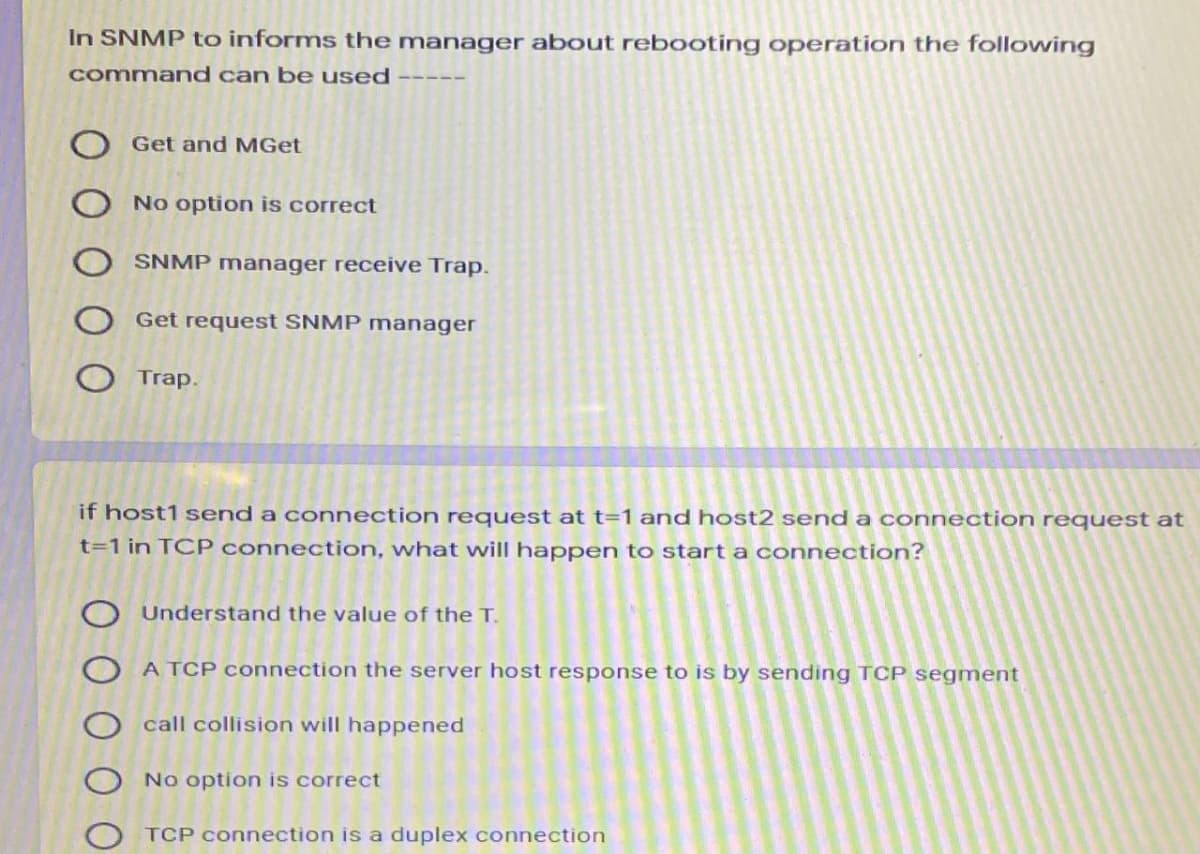
In SNMP to informs the manager about rebooting operation the following command can be used O Get and MGET No option is correct SNMP manager receive Trap. Get request SNMP manager Trap.
Q: What command can you use to view journald log entries on a system that uses Systemd?a. lessb.…
A: Command for viewing log entries on a system The systemd journal command is responsible for…
Q: collection address and the delivery address. Quickly design a prototype to present to the board and…
A: Solution: The code with the required functionality is given below. ->It has been executed in…
Q: Using exec system call list all the files and directories of home then store the result in…
A: According to the Question below the Solution:
Q: 131. Once deadlock has been detected, some strategy is needed for a. Control b. Access c. Recovery…
A: Deadlock is a circumstance where a bunch of cycles are impeded on the grounds that each interaction…
Q: PLZ help with the following: Open System Configuration (enter exe command). Click the Services TAB…
A: Open System Configuration: On the overall tab, faucet or click the conventional Startup…
Q: Identi fy the SQL statement used to extract data from a database. a. GET b. OPEN C. SELECT d.…
A: Given:
Q: Which diagram type is shown in this figure? Describe the diagram completely. Medical Receptionist…
A: Answer : The diagram shown in figure is Sequence diagram.
Q: PLZ help with the following: Open Event Viewer in the Administrative Tools group or by using the…
A: I am answering for Windows OS 1. You have to open the Event Viewer first. To do this, press…
Q: users user_id action date start 1-1-20 1 cancel 1-2-20 1-3-20 publish 1-4-20 1-5-20 start start…
A: Task set : Create table users with three attributes: user_id, action, date Fill the data in the…
Q: Each process utilizes resources in following order: TRue or false release use request
A: Given : Each process utilizes resources in following order: TRue or falsereleaseuserequest
Q: the command to delete a user: tom Write the command to change the password of a user: tom
A: here is the Solution:- command to delete a user:- ans :- sudo userdel tom…
Q: Describe how the getpid() system call is implemented. Assume that a user program executes the line…
A: getppid() and getpid() getppid() and getpid() are inbuilt functions defined in hlibrary. getppid()…
Q: Which command can list the files that could be impacted if you terminate the rogue process
A: -> Find the answer in the Step 2.
Q: Why doesn't eigrp have an auto summary command?
A: Introduction: EIGRP (Enhanced Interior Gateway Routing Protocol) is a distance-vector routing…
Q: The “find” command is running in the background. Write the command that will kill that process.
A: Since you have not mentioned the Operating System. We will be answering this in context of Linux.
Q: Create a program that a user can use to manage the primary email address and phone number for a…
A: In this program using python functions based on the Do while loop and the menu constructed under it.
Q: Which access control principle limits a user’s access to the specific information required to…
A: Access control Access control is one of the mechanisms that ensure authorized users can have the…
Q: PS command can show the PID, UID, priority, and control terminal of processes. Explain other…
A: To discuss some of the details ps command can show.
Q: Console if the contacts file is not found Contact Manager Could not find contacts file! Starting new…
A: According to the information given:- We have to follow the instruction mentioned in order to get the…
Q: TEST CASES: You have an Active Voters account! Your full name is Juan Dela Cruz. You are 25 years…
A: Please find the answer below :
Q: shell command interpretation [ Choose ] Second Third Fork() a child process Fifth First Fourth…
A: Answer:
Q: which command allows for one off running of scheduled tasks by a normal user ? a) cron b) anacron…
A: I have provided solution in step2
Q: Create a program that a user can use to manage the primary email address and phone number for a…
A: Since no programming language is mentioned, I am using python. Code: contacts=[[1,"Guido van…
Q: The at command is used to ________.a. schedule processes to run periodically in the backgroundb.…
A: “at” command: In computing, “at” is a command in Unix-like operating systems, Microsoft Windows,…
Q: To execute the use case Issue certificate, an actor Professor is required; in addition, an actor…
A: Lets see the solution.
Q: When a command is not available for selection until certain other conditions are met, it is called…
A: unavailable command: When the command is not supported or not present in the system. dialog box:…
Q: You manage an Azure subscription named Sub1. Sub1 is associated to an Azure Active Directory (Azure…
A: The question has been answered in step2
Q: Customer Employee PK CustomerPhoneKey PK Employeekey CustomerLastName EmployeeLastName…
A: As per the rules of Bartleby, I could only solve the first 3 subparts Kindly post the other parts…
Q: NTFS permissions are cumulative unless a user is denied permissions. True False QUESTION 3 Users can…
A: NTFS permissions are cumulative unless a user is denied permission True Explanation On the off…
Q: ystem must produce an attendance report Change password asks new password to enter s capable of…
A: Q.
Q: Create a program that a user can use to manage the primary email address and phone number for a…
A: //Python code below
Q: Which diagram type is shown in this figure? Describe the diagram completely. Medical Receptionist…
A: Given that Which diagram type is shown in this figure? Describe the diagram completely. Given…
Q: if(firstpassword==secondpassword){return true; } else{ alert("password must be samel"); return…
A: In the given program segment, if statement compares first password and second password for equality.…
Q: Explain why user access administrator should never be granted the ability to initiate a new user…
A: People having user access administrator rights have a wide range of roles to play. They provide…
Q: In order for the public to view Web pages on the Internet that have been placed in a directory, the…
A: Language is one of the most widely used programming language which has been used to create different…
Q: How many account records will be created by the given code? Account a = new Account(Name='Acme');…
A: According to the given code: We have to find out how many account records will created by mention…
Q: How many account records will be created by the given code? Account a = new Account(Name='Acme');…
A: The answer is
Q: Each request requires that the system consider the _____________ to decide whether the current…
A: Resource allocation is the process of allocating processes so that they can start task competing.
Q: You manage an Azure Artifacts feed named Feed1. Feed1 contains a package named Package1. You need…
A: I will explain all things in details,
Q: en push r4 command is executed, dete wing:
A: Program counter is one of the resisters and its role is to store the address of the current…
Q: User account 2. The system allows user to register and create the account 3. Users allowed…
A: It is defined as a particular behavior of function of the system when certain conditions are met,…
Q: Users can request certificates that aren't configured for autoenrollment by using the Certificates…
A: The given statement is true i.e. By using the snap-in Certificates, users can request certificates…
Q: D2 User User Credentials Log In Credentials Post/Like/ View Feed User Posts Store Posts Retrieve…
A: A sequence diagram is a Unified Modeling Language (UML) diagram that illustrates the collection of…
Q: State true or false: Every cascadeless schedule is also recoverable
A: this is a true statement that Every cascadeless schedule is also recoverable. correct answer is a.…
Q: To query Azure Active Directory (Azure AD) logs in Log Analytics, you can use the AuditLogs table…
A: The above question is answered in step 2 :-
Q: By defaults if command have two versions the internal and external version, the internal run by…
A: There is One command in the Linux with contains both the versions ie. Internal as well as External…
Q: Which command can be used to kill background process "(sleep 160; who)"?
A: answer is kill 12804
Q: NIS clients use NIS records to access their configuration information. True or False?
A: NIS: NIS stands for Network Information System which is a client-server directory service protocol…
Q: Opsequences alert x1x op5 x2:X op1 op2 x3:X op3 y1:Y op4 op2 op3 Z1:Z new remove ZA
A: Answer: Belwo are the right options. a. The op2 message of x2 invoked by the object x3 is not the…
Step by step
Solved in 2 steps

- Please answer all thefollowing two questions from the choosing the answer option. Thanks a lot in advance. 10) _______________A passive IDS can send an alart, but it is the network administrator's job to interpret the degree of the threat and to respond acfcordingly. Answer: True or False 13) Which of the following ACL configuration command on your router is correct for taking actions such that Only 120.3.6.7 has the right to access. Any other incoming packets from any other source will be blocked and denied any service. (Assuming that you can use any ACL name and any ACL number within the correct range. And using Basic-ACL Category) a) Rule is Deny source IP Address 10.3.65.7 configure a rule with ID 10 b) Rule is deny Source IP address 20.3.67, Configure the second rule without specifying an ID. c) Rule is permit source IP Address 120.3.67, Configure a rule with ID 20. d) All of the aboveAssume a web server can only receive TCP connections on port 80 (HTTP) and 22 (SSH), but not on any other ports. The web server can only establish connection to a database server hosted on private IP 192.168.100.100 on port 3000, but to no other machines inside or outside the network. Imagine this web server is running Linux, and we’re using iptables to define host-based firewall rules for it. Show the set of iptables commands to install necessary rules for this security policy.Your DHCP server now uses these alternative DNS servers. In general, what is the best way for your consumers to get the new settings? * Two separate computer restarts are required. Enter ipconfig /registerDNS on the client. Wait for the DHCP client to request a lease renewal. O Type ipconfig /renew into the client's terminal. Server DNS cache must be cleared.
- You are supposed to connect to HSBC.COM server, however, a TCP session hijacking attack was successfully issued between your desktop PC and the server HSBC.COM. Explain how could this attach affect the security of your connection in relevance to the security principals [Confidentiality|Integrity|Availability]Router5 is in rom mode, and there is an enable password on it which we don't know. Bring it back to boot in normally, set new enable password of 'cisco' and restore its configuration. IF the original configuration is restored, the router should be able to ping the others without any further configuration. If the interface (on Router5) are down (it will be red) after you restore, bring the interface up with 'no shutdown command' Wait until you see the messege "from loading to FULL, LOADING done" BEFORE TRYING TO TEST PING 0x2102 (boot normally) (default)0x2120 (rom mode)0x2142 (ignore nvram content) This is all ONE question, please answer full question.I NEED ONLY CORRECT OPTION NO NEED TO EXPLAIN IN DEPTH,PLEASE SOLVE ALL THE QUESTION, DON'T LEAVE ANY QUESTION AND IF YOU DON'T KNOW THE CORRECT ANSWER THEN PLEASE LEAVE IT OTHERWISE I WILL DOWNVOTE IT.... 1. Which of the following statements are correct?I. The User Datagram Protocol (UDP) is used for applications that requires constantdata flow.Il.The header size in Transmission Control Protocol (TCP is small when compared tothe header size of User Datagram Protocol (UDP).I!.The Transmission Control Protocol (TCP) is byte oriented.IV. The User Datagram Protocol (UDP) is used for routing.(a) I, II, and III only(b) II, Ill, and IV only(c) I, Ill, and IV only(d) I, Il, and IV only 2. Which of the following statements are true when the block size in a fixed block size filesystem is increased?1. disk throughput is increased2. disk throughput is decreased3. disk space utilization is increased4. disk space utilization is decreased 3. What is the output of below…
- Godwin Pharmaceuticals has a private web server for its corporate network that runs on a Linux operating system. A.You have been contacted to make its network remotely accessible to the IT department so that the IT department can have secure access to the workstations and, at the same time, the transmissions remain encrypted. Which of the following protocols would you apply so that the employees can have secured remote access to the computer server? 1.SSH 2.Telnet 3.RDP 4.POP3The scenario includes one DHCP server in an Active Directory domain. The server is configured to provide IP addresses to DHCP clients on two different subnets. The subnets are separated by a router that has DHCP Forwarding enabled. In this scenario, you use ten of the excluded IP addresses to configure servers and other devices with static IP addresses and five additional IP addresses are left available for static configuration of new devices that you might want to add in the future. Write up the Powershell script for the following according to scenario IP configuration: Installing DHCP role (DHCP1) Creating DHCP security group (your Arid Number) in DHCP1 Note: Security Group should create with your arid number. Authorizing the DHCP1server in DC1 How to getClient4 adapter hardware information Disable and Enable a Network Adapter of Client4The University (U) has developed a new protocol, called UAPP, that is used by a client application on computers in its different branches around the world to send students information to a central server in the U campus in Kuwait. The TCP/IP stack is used by the protocol. Based on your strong knowledge of OpenSSL libraries, you have been hired by the U to pertest and configure the client/server applications so that all sessions between client/servers are became secure. After securing the application, a secure session and connection has been established. The following information is stored by the client computer for this session/connection: Session ID: id Compression method: null Cipher Suite: TLS DHE RSA WITH AES 128 CBC SHA Master secret: s Server random: Client random: Server MAC secret: Client MAC secret: Server encrypt key: Client encrypt key: The following figure shows the general operation of SSL record protocol: Draw a protocol…
- All clients computers ae configured to receive IP addresses from thr DHCP server. However, clients on subnet B cannot access clients on subnet A.What is the most likely cause of this problem?a.IPV6 is disabledb. The IP address for the DNS Server is not available in scope optionc. The IP address is not available in DHCP scoped. Server option is disabledYour DHCP server now uses these alternative DNS servers. In general, what is the quickest way for your clients to get the new settings? * Try a double restart of the computer. Enter ipconfig /registerDNS on the client. Watch for the DHCP client to request a lease renewal. O Launch ipconfig /renew on the client. Clear the server's DNS cache.On the receiver's return, I want all TCP traffic from my internal network to pass via the firewall. This traffic is allowed by what rule? Port 80/HTTP Standard Established ICMP







