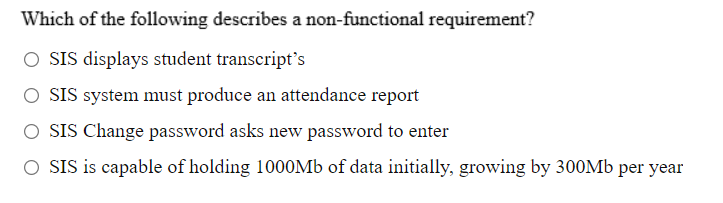
ystem must produce an attendance report Change password asks new password to enter s capable of holding 1000M6 of data initially, growing by
Q: Client-dependent data is defined as data contained across all clients in the system. False True
A: Client-dependent data is defined as data contained across all clients in the system. False.
Q: If you are unsure of the location of the update.txt file on your computer, print one copy.
A: The txt file do: A text document with the. TXT extension is one that includes plain text in the form…
Q: Generate random password using cpp langugae
A: The CPP code for generating a random password
Q: In MS Access, to ensure that a promised date valued entered must a future point in time,…
A: Now() function:The Now() function in Microsoft Access is used to return current date and time based…
Q: Her public key certificate is valid from 1000 hours on the 9th November 2013 to 1000 hours on the…
A: For a variety of reasons, a certificate may be revoked (which we'll go over in more depth in the…
Q: In Windows, the md command Lust be used to create a folder a. True b. False
A: In Windows, the Md command is not used to construct new files.
Q: What is the main purpose of PKI? O Signature generation and verification O Distribute Keys O…
A: PKI is public key infrastructure
Q: The best passwords are 8 to 10 letters long. a. True b. False
A: Answer as follows:
Q: Locking will help prevent multiple simultaneous requests or use a synchronization mechanism. This…
A: Locking will help prevent multiple simultaneous requests or use a synchronization mechanism this…
Q: the command to delete a user: tom Write the command to change the password of a user: tom
A: here is the Solution:- command to delete a user:- ans :- sudo userdel tom…
Q: adding data may resu
A: Constraint violation A problem that signals a request that is syntactically correct but…
Q: What functions are used to create Authenticator? Describe in depth
A: The answer is given in the below step
Q: Lli 4 The following code is true if you want to: Dim I as integer |= l+1 If password = "matrix" Then…
A: Here we have given the code and we have to tell which of the following statement is true according…
Q: Enter account balance: PhP 10000 Enter acount interest: 10 Enter the nunber of nonths until…
A: The C++ program is given below.
Q: MS SQL server Create a Scalar UDF that receives a social security number of a client, and…
A: Lets see the solution.
Q: Audit logs should be protected by time stamps and can be digitally-signed? true or false
A: Audit logs are a document that is used to record of security-relevant data that documents the…
Q: 30. A shared lock allows which of the following types of transactions to occur? a. Delete b. Insert…
A: The problem is based on properties of the shared lock.
Q: def check_password exclusive(passwd: str) -> bool: **"An exclusive strong password has a length…
A: Please find the answer below :
Q: • Create Mini-Password Manager Write a simple code to create hash value of passwords Store the…
A: Please upvote. I am providing you the correct answer below. Please Please. SHA3-512 is…
Q: bank code name address customer Fname Lname phone Birth date gender ssn Customer_location | address…
A: Normalization means splitting the large table into many smaller tables in order to minimise the data…
Q: Locking may cause which of the following problems? a. Erroneous updates b. Deadlock c. Versioning d.…
A: A deadlock happens when multiple lock waits happen in such a manner that none of the users can do…
Q: Type the following command and press Enter, to add a user to the system. Type msfadmin for the…
A: Adding users in Linux. Explanation: Sudo useradd screenshot. screenshot of the new user. As you…
Q: It is possible that the user's attempt at adding data may result in the creation of a record that…
A: The data in the database must be updated, added, or deleted according to the user's requirements.…
Q: Which diagram type is shown in this figure? Describe the diagram completely. Medical Receptionist…
A: Given that Which diagram type is shown in this figure? Describe the diagram completely. Given…
Q: We using thé fóllówing methods in HTTP: insert data to database Choose. Upload a document to the…
A: Get method is used to retrieve a document via HTTP from the server GET is used to request (retrieve)…
Q: Client 001Client 001 in SAP R/3 customizing is basically a copy of 000 and can be used as a basis…
A: The question has been answered in step2
Q: Submit a write up that describes the steps of creating a database of Certificates using MongoDb. Be…
A: Answer : Submit a write up that describes the steps of creating a database of Certificates using…
Q: 5. Write a script to add new user to a specific group (Exist and new group) and give an initial…
A: We need to write shell script to add a user with password. ***As per guidelines, only 1st question…
Q: if(firstpassword==secondpassword){return true; } else{ alert("password must be samel"); return…
A: In the given program segment, if statement compares first password and second password for equality.…
Q: 2. Create a new user named user 1 and assign a password to it. Also show how to disable and delete…
A: ADDING NEW USER ONE
Q: er is shown an error r and password both v navigated to homep
A: Decision table is a brief visual representation for specifying which actions to perform depending on…
Q: 2. Create a new user named (Your_Name) and assign a password (Your Roll_No.) to it. Also show how to…
A: Disclaimer: Since you haven't specified the operating system we are answering the question for…
Q: system Student 1. Login 2. Verify login 3. Wrong password 4.Borrow book- Alternative if (The book…
A: Answer : Explanation of first sequence diagram : Student first login the system by entering the…
Q: In SCAN – EDF, requests with the same deadlines are ordered according to : a. SCAN policy b. EDF…
A: Given that: In SCAN – EDF, requests with the same deadlines are ordered according to: a. SCAN policy…
Q: What types of privileges are available in Oracle 12c? Define each type
A: When a database has multiple accesses, then it is important to ensure control of authorized…
Q: Users can request certificates that aren't configured for autoenrollment by using the Certificates…
A: The given statement is true i.e. By using the snap-in Certificates, users can request certificates…
Q: Special set of characters that computer associates with specific user identification is classified…
A: Required: Special set of characters that computer associates with specific user identification…
Q: Purchase module responsible for sharing date and maintaining the integrity of data transferred to…
A: Required: Purchase module responsible for sharing date and maintaining the integrity of data…
Q: def check_password_exclusive (passwd: str) -> bool: """An exclusive strong password has a length…
A: Python Code to form a strong password
Q: You are asked to implement a group policy in your company's AD domain. Your security implementation…
A: Solution: Given,
Q: ssume you had a function named update) that updates shared data. Illustrate how a mutex lock named…
A: Race condition is a situation in OS where two or more operation are being done at a same time. It…
Q: Write any 4 basic security your authentication factors.
A: Authentication factor It is one of the security credentials that verify someone's identity and…
Q: In which of the following authentication methods the user needs to enter a registered username and…
A: Username/Password Authentication Method : Every time you've signed up for a website, you've likely…
Q: q14) Name the key stored in a Digital certificate ? a. User's private key + public key b. None c.…
A: Answer: c
Q: AUTHENTICATION SYSTEM HHHH PK Loginld INTEGER password VARCHAR(20) PUBLISHER login +H manages A…
A: It is defined as the diagram that displays the relationship of entity sets stored in a database. It…
Q: Select the correct statement about authentication using passwords O a. Salt value will be sent from…
A: Hello Student, hope you are doing well, I will be trying my best to explain and fulfill your query.…
Q: NIS clients use NIS records to access their configuration information. True or False?
A: NIS: NIS stands for Network Information System which is a client-server directory service protocol…
Q: Opsequences alert x1x op5 x2:X op1 op2 x3:X op3 y1:Y op4 op2 op3 Z1:Z new remove ZA
A: Answer: Belwo are the right options. a. The op2 message of x2 invoked by the object x3 is not the…
Step by step
Solved in 2 steps with 1 images

- You're the IT administrator for CSM Tech Publishing. You've just had a meeting with the general manager about a data storage problem the company has been having. You've been asked to find solutions for the following problem: Two satellite offices have been complaining about slow access to shared files on the servers at the company's headquarters. One office has about 25 client computers running Windows 10, and one server running Windows Server 2016 provides DHCP and DNS services but isn't heavily loaded. The other office has only four client machines running Windows 10. There's no budget for additional hardware at either location. What solution do you propose for this problem? Include implementation details.Which of the following is not an advantage of choosing a hosted software solution for the new CRM solution rather than setting up and installing the software on each individual's computer? a. The time to get users set up and using the system is likely to be shorter. b. The data associated with the application will be safely stored off-site at a third-party vendor's location. c. The management of the application (support, maintenance, upgrades, etc.) is outsourced to others who are already experts in the application. d. High start-up complexities and hardware and software costs can be avoided.QUESTION 22 Which utility is used to browse events stored in system event logs? a. Device Manager b. Event Viewer c. Shared Folders d. Resource Monitor
- 1note:Answer Should Be Minimal ..Answer Must Be In " BismarckFormat"; No Copy Paste ..ANSWER QUICK AS POSSIBLE..Answer Must Be In " Bismarck Format' i.e Hktct x YYT Format ..Answer In Minimum Words Please..Answer With Keeping My Demands InMind:NOTE: IF YOUR ANSWER IS NOT RESPECTING MY 3 DEMANDS ; I WILL DISLIKE YOUR SOLUTION ... ...................................,1 : What is a part of a programme that assists the user through specific processes in most programmes?A company has three discrete servers: a file server running Linux, a contact and email server running Windows Server, and a DNS & DHCP server running an earlier version of Windows Server. Make a case for or against going virtual with this setup. Case Project #2 - Research both Infrastructure as a Service and Platform as a Service and submit a comparison between the two cloud offerings.In this lab your task your task is to perform the following, On CorpDC, create a user account for Sean Smythe in the Partner. ChannelPartners OU. Use the following naming standards and specifications as you create this account: User account name: first name = Last name. Logon name: first initial = lastname@BizCorp.com. Initial password 1234abcd$. On CorpDC, rename the Emma Simmons user account in the engineering OU and restrict her logon hours: Replace Simmons with Tomco in her account name, full name, display name and both logon names. Limit Emma Tomcos logon hours to allow logon only from 7:00 am to 5:00 pm, Monday to friday. On CorpDC, create a domain locval distribution group called Team Leads andf add members to the group. Create the Teams Leads group in the Users container. Ass Jill Soares user account as a member of the team Leads group. On CorpDC, change ther scope and type of the managers group in the Users container from domain local distribution to global security
- You can use Kusto to query Azure Active Directory (Azure AD) logs stored in Log Analytics to define a rule of an Azure Monitor alert. Select Yes if the statement is true. Otherwise, select No.ABC Accounting Company is a company that manages the financials for various small companies on a national scale. They specialize in using the “Quick Books” accounting application that is accessed by ABC’s employees via a “Software as a Service” (SaaS) arrangement where ABC pays a monthly fee per employee for access to the application. Accounting data for ABC’s clients is stored by the application service provider on their cloud and also may be stored in a redundant fashion locally on ABC’s servers and individual ABC employee hard drives (depends on up the option chosen by the ABC employee for the backup for a given client’s information). ABC is an interesting company in that it recruits its small (from tens of thousands of dollars in revenue to a few million per year) clients via newspaper and magazine advertisements nationally and its website. Therefore, clients are almost always remotely located with respect to ABC’s small main office in the San Francisco area of California. Another…Task 1: Demonstrate how to install some user and system applications such as firefox, and Dolphin file manager) is user applications and (nmap, and conky) as administrator applications. Task 2: Install, configure Samba service and demonstrate how to connect to your server from remote computer. Task 3: Install, configure Web Server and demonstrate how to browse a simple website hosted in your server. You may deploy a simple website (or web application) – from the Internet, in your server. Task 4: Install, configure FTP Server and demonstrate how to browse files hosted in your server.
- Support and maintenance costs are less on a single server than it would be to maintain each installation or upgrade on a desktop client because the data layer adds scheduling and priqritization for work in progress. Select one: O a. True O b. FalseIn this question, you need to verify and provide evidence of the installed domain and virtual machine.Do this by completing the following tasks: Q.1.4 Answer/complete this question using the correct client and/or server machines. Capture the screen of each of the following installations and configurations and saveeach in the Q.1.4 folder:• The three Windows client machines. • The correct use of name conversions.A company is moving most of its customer-facing production systems to the cloud-facing production systems to the cloud. IaaS is the service model being used. The Chief Executive Officer is concerned about the type of encryption available and requires the solution must have the highest level of security. Which of the following encryption methods should the cloud security engineer select during the implementation phase? Options: A Instance-based B Storage-based C Proxy-based D Array controller-based ~If you could explain why for each choice, I’d appreciate it. Thank you!



