In which model, a user is granted permissions to access a resource by being placed on an access control list (ACL)? O a. RBAC O b. DAC O c. МАС O d. MAC & RBAC
Q: 5. Which command from the following is used to check the script execution policy in the windows…
A: option a is used for setting the policy to RemoteSigned option b is used for get the polity to…
Q: User A is trying the login with his account, but he is getting the following message: “The trust…
A: The Complete answer is given below.
Q: Nicole, a system administrator, is configuring basic NTFS permissions on folders on a common…
A: An operating system is a large and complex system that can only be created by partitioning into…
Q: Consider the below commands i) sed “s/CSH/csh/g" temp >| Is ~/newtemp 11) Is -v grep wc -1 iii) Is…
A: Ans: B) ii, iii only
Q: The service used to automatically assign address to Linux hosts is known as? a) ifconfig b) DHCP…
A: DHCP - stands for dynamic host configuration protocol is a network protocol which is used to assign…
Q: Using Unix shell commands, write a script that counts the number of .html files in the current…
A: To Count the number of html files we use the find command and then redirect the output to
Q: Clients are reporting slowness when attempting to access a series of load-balanced APIs that do not…
A: To use OAuth 2.0 to protect an API so that an application can access it on behalf of a user The flow…
Q: 3. a) Which of the following does Linux use for access control? O Access Control Matrix O Access…
A: Ans:) Access control mechanisms are used for managing files, directories permissions in OS.
Q: Which of the following is correct about passive attack? a. Involve modification of the data stream O…
A: Passive Attacks are in the nature of eavesdropping on or monitoring of transmission.
Q: A user downloaded a program from a website. After saving the file, the user cannot find the…
A: A user downloaded a program from the website. After saving the file , the user cannot file…
Q: On servers with Linux operating system, access logs are kept under which of the following…
A: As per our policy, "Since you have asked multiple questions, we will solve the first question for…
Q: Write code that when executed in PowerShell, will satisfy the following requirements: • List all of…
A: PowerShell commands List all of the processes on a remote computer. use invoke command with script…
Q: Which of the following situations would best described an incident request? a. A user is unable to…
A: Introduction:- This is objective type question ...choose one option and explanation below in step 2
Q: What is a function of a command banner motd# O a. To give a welcoming message O b. To give a warning…
A: I have Provided This answer with full description in step-2.
Q: Which of the following is the file extension for a firewall policy file in Windows?Group of answer…
A: File extension for a firewall policy fileA WFW file is a settings file created by windows firewall…
Q: NFS can be used to share files natively with computers running the Microsoft Windowsoperating…
A: NFS is developed by SUN micro system in 80's. NFS allow you to store, view or update the on the…
Q: An attacker detects that commands such as "cd,ls,rm" do not work when they provide an SSH connection…
A: An attacker detects that commands such as "cd,ls,rm" do not work when they provide an SSH connection…
Q: "chmod" is a well known command line utility, that is used for manually managing the access and…
A: After execution of the given command: The command “chmod” is used for changing the access…
Q: QUESTION 25 Typically, the daemons are not responsible for: Create user account, Run scheduled…
A: Typically the daemons are not responsible for Answer: Monitor systems such as hardware storage…
Q: ____________allows for a single configuration to be set and then deployed to many or all users. a.…
A: Given question is multiple choice question.and it's related to windows _____________allows for a…
Q: w can this issue be resolved? Reset the Windows 10 computer account in Act
A: Cause for this errorThis workstation's trust link to the parent domain has broken down. ResolutionTo…
Q: The separator character in your path can vary depending on the operating system. A relative path is…
A: The separator character in your path can vary depending on the operating system. --> True A…
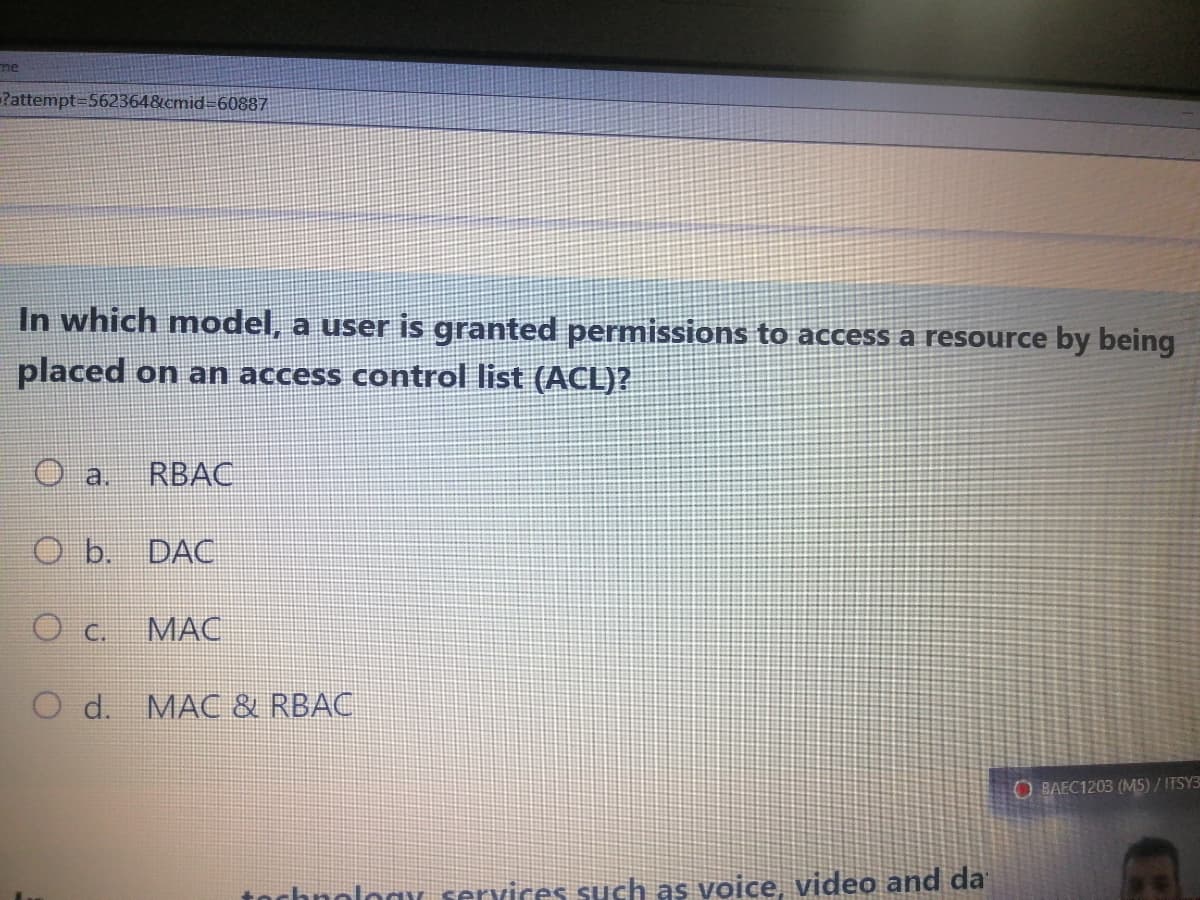
Q: In which model, a user is granted permissions to access a resource by being placed on an access…
A: Access Control List (ACL) An access control list (ACL) is a table listing the permissions attached…
Q: Question 18 Given the following code for a program called runme, choose the correct outp ut when it…
A: Dear Student, The code will not compile as gcc -o runme is not executed , it must be executed before…
Q: Which of the following actions should you first take to secure your Linux computeragainst network…
A: First Action to Secure Linux Computer: To overcome the network attack, only the necessary network…
Q: Which of the following command line environment is used for interacting with Git? a) GitHub b) Git…
A: Question. Which of the following command line environment is used for interacting with Git? a)…
Q: Winona has set up AppLocker rules to protect computers on the company network from being infected by…
A: Lets discuss the solution in the next steps
Q: Discussion about NTFS and the Share permission role in Windows Server 2016?
A: Introduction: In Microsoft Windows settings, NTFS and sharing permissions are often utilized. While…
Q: What will be stored into cx after executing the following commands? x1 DW 13 DUP(?),5,4,8 mov cx,…
A: In Registers -> There are processor register which are divided into general register, control…
Q: You have provisioned a Linux server on Amazon's EC2 cloud. To allow login from your Putty client on…
A: Amazon Elastic Compute Cloud (EC2) offers the broadest and deepest compute platform, with over 400…
Q: Consider the below commands i) sed "s/CSH/csh/g" temp> Is ~/newtemp 11) Is -v grep wc -1 111) Is -a…
A: As per time boundation. Below is the correct answer. I hope this will help.
Q: What is your opinion on the NTFS and Share permission roles in Windows Server 2016?
A: Lets see the solution.
Q: Consider the set of configuration commands shown in the picture below. What will be the final prompt…
A: Considering a Switch in Cisco Packet Tracer hostname sets the name of the switch to S1 line console…
Q: 14. Which of the following is default permission set for directories? a) rw-rw-rw- b) rwxrwxrwx…
A: 14. Which of the following is default permission set for directories? a) rw-rw-rw- b) rwxrwxrwx c)…
Q: If a Web application doesn't validate any client's access to any system resource, which of the…
A: To Do: To find the OWASP Vulnerability.
Q: 7. Which is the file system from the following is commonly used in windows server 2016? a. EXFAT O…
A: Explanation:- ExFAT is the file system from the following is commonly used in windows server 2016.…
Q: Which git command would you use to update a remote repository with the current changes made in a…
A: In this question, we have to choose one correct answer out of given options. Here question is about…
Q: In DAC a user is granted permissions to a resource by being placed on an access control list (ACL)?…
A: Answer: In DAC a user is granted permissions to a resource by being placed on an access control list…
Q: Which of the following definitions best describe a snap-in? a. It is a Windows PowerShell…
A: - We need to highlight the correct option among the provided ones for snap in. - Snap-in is the…
Q: Which DNS resource record is an alias to other records?a. Ab. AAAAc. CNAMEd. NS
A: DNS record alias to other record A Domain Name System records are instructions that provide…
Q: Which of the following will work when trying to hack a login screen? O Try a list of commonly used…
A: Hacking: It is the process of attacking the computer and software to steal the information of the…
Q: SELinux is an example of what kind of Access Control? RBAC O DAC МАС O Rule-based Access Contral
A: SELinux stands for Security Enhanced Linux and this is a security architecture for Linux system that…
Q: Which of the following can be used to restrict the installation of a USB drive on a Windows 10…
A: To Do: To choose the correct option.
Q: Which of the following is the most common form of registry entry? REG_SZ REG_DWORD…
A: Answer:- REG_DWORD
Step by step
Solved in 2 steps

- A Windows 10 local administrator would like to access a corporate messaging application to send message to users in the Active Directory domain. He tried to access the application and received error message that he doesn’t have required permissions. How can this issue be resolved? Reset the Windows 10 computer account in Active Directory. Create a domain account for the Windows 10 local administrator. Remove the Windows 10 computer from the domain. Add the Windows 10 local administrator account to the Domain Users security group.Q131Which option restricts access to shared files when users are not connected to a network?Select from the following:Permissions for the Caching Permission LevelSnap-in of shared nodesWhich DNS resource record is an alias to other records?a. Ab. AAAAc. CNAMEd. NS
- Create a script that uses the ping and fping commands to do the following tasks: I want the software to say Hello your name> The system ip address> is alive (or not alive) after it asks for your first and last names, does six pings with ping, then one ping with fping simply to say a system is alive, then I want the software to say Hello your name> The system ip address> is alive (or not alive). Please send screenshots of the issues.Scenario Your manager, a senior Windows Administrator, has asked you to collect information from Windows Server using commands only. Your manager has also asked that you work together with a colleague by reviewing and troubleshooting their script. Tasks 1. Create, test and use the following list of commands, taking a record of each step. Get-Command Get-ChildItem Export-Csv.Write a script and save it as /opt/book/chapter10/exercise2. This script performs thefollowing functions d. Counts backwards from 10 to 1e. Displays the current numberf. Pauses for 1 second between numbersRun the script in terminal using the command: bash /root/Desktop/exercise2
- which feature that makes the domain controllers more flexible, both to audit and to authorize for access to files. * A) Active Directory Domain Services (AD DS) B) Windows Server Containers C) Active Directory Rights Management Services (AD RMS) D) All of the above.Scenario Your manager, a senior Windows Administrator, has asked you to collect information from Windows Server using commands only. Your manager has also asked that you work together with a colleague by reviewing and troubleshooting their script. Create, test and use the following list of commands, taking a record of each step. Get-Command Get-ChildItem Export-Csv.In HomeController.cs, set three session states to get course name, student id and date. Use Course, StudentId and CurrentDate(yyyymmdd) as the session variables. Set these states in the IActionResult Tools ( ) method. ASP.NET MVC
- You installed your new Windows Server 2012, but after the first day, the server was compromised by a malicious download. What post-installation task was not correctly implemented? installed a. Windows Server security patches were not b. A TCP/IP firewall exception was improperly made c. IE enhanced security was not enabled d.All of the aboveprofile-image Time remaining: 00 : 09 : 41 Computer Science PowerShell Practical Congratulations! You’ve been hired VaultTech as a Windows Server 2012 R2 administrator. Your first assigned project is to create some PowerShell scripts to automate certain administration functions. a. We need a script that will search for AD accounts that have not logged into the Domain within 30 days, and then disable those accounts. b. We need a script that can search for “Critical Errors only” in the Windows Event Viewer, sorted by date, and then output those results to a CSV file on the Servers desktop. c. We need a script that can see if a Process is using more than 90% CPU usage, and then terminate that Process, but write a message to the screen that it was terminated for reaching X% CPU. d. Because of a new phone system installed, all users phone numbers have changed. We need a script that will read the new phone numbers from a CSV file and update Active Directory (this is where HR gets its…Question 13 sum.Why would you want to run the RODC (read-only domain controller) on Windows 2008 and newer versions? What are available in the newer versions that's not available in previous versions. Full explain this question and text typing work only We should answer our question within 2 hours takes more time then we will reduce Rating Dont ignore this line

