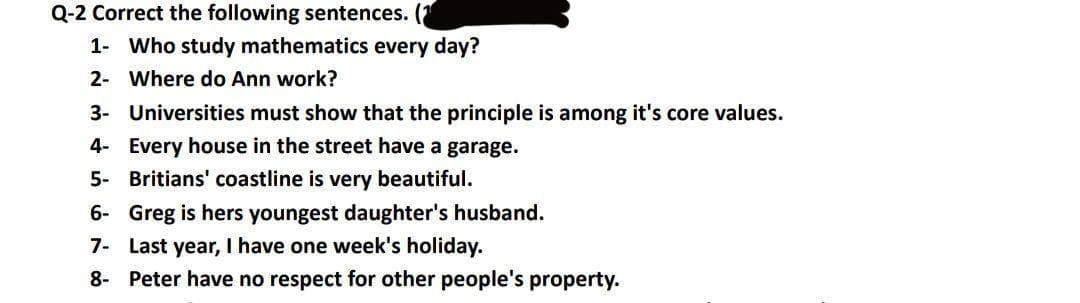
ing sente 1- Who study mathematics every day? 2- Where do Ann work? 3- Universities must show that the principle is among it's core values. 4- Every house in the street have a garage. 5- Britians' coastline is very beautiful. 6- Greg is hers youngest daughter's husband. 7- Last year, I have one week's holiday. 8- Peter have no respect for other people's property.
Q: sklearn should be used to load the digits dataset. Divide the dataset into two sections: training…
A: You can find code in below steps. see below steps for code.
Q: List the six essential guidelines for analysing articles from the Internet or other sources.
A: Intro Six basic tips for evaluating articles individually via the Internet or other sources:…
Q: Q3: A MATLAB function used to clear a selected variable value from workspace :
A: A matlab function used to clear a selected variable value from workspace
Q: Explain information technology (IT)
A: Intro Information technology (IT) is defined as the use of a computer or electronic devices to…
Q: Question 8. Determing if the statement "Vx, y = R, if x is irrational and y is rational then xy is…
A: I will explain it in details,
Q: The topic of building web-based application interfaces for diverse cultural and [inter]national…
A: User Interface (UI) design aims to anticipate what users will need to do and ensure that the…
Q: An examination of connectionless protocols as a possible replacement for connection-based protocols…
A: Advantages of connection-based protocols include: It is quite dependable. The goal is followed by…
Q: What part does MVC play in the overall organization of web applications? What are some of the…
A: The answer is given below.
Q: How exactly do you go about locating weak spots in information systems? Think
A: Information Systems A collection of various pieces of technology engaged in the gathering,…
Q: This chapter has outlined a few of the most important benefits of a database. Are there any other…
A: According to the information given:- We have to define the most important benefits of a database.…
Q: What are the primary functions of the Compiler's Phases? Are there examples for each phase?
A: Given: What are the fundamental functions of Compiler Phases? Give examples to each phase? Phases of…
Q: The following are some differences between a two-tier and a three-tier application architecture:…
A: Introduction: The distinction between two-tier and three-tier database architecture is as follows:
Q: (1), (2), and (3) is accepted by the Scala compiler Question 26: Consider the following Scala code:…
A: 26. A is printed because a class is called refer opps concepts. E is the answer. 27. A is the answer…
Q: What's the difference between on-premises and cloud-based IT security solutions?
A: correct answer is given below
Q: What is a challenge–response system for authentication? Describe it here. When compared to a…
A: Introduction: System of challenge–response In a client-server system, password-based authentication…
Q: Choose the correct MATLAB nmand to rotate matrix A 180 nter clockwise:
A: "rot90" is command used to rotate the array by 90 degrees. We will see it with the help of code…
Q: What are the odds of include an introduction to the compiler as well as an explanation of why…
A: Intro A compiler is backend software.It takes input as any high-level language like C++/Java/etc.And…
Q: Internet search engines have legal and ethical ramifications that need to be considered.
A: Inspection: This question discusses the legal and ethical ramifications of using internet search…
Q: explain the challenges of designing, testing, and sustaining web applications.
A: I will explain it in details,
Q: Differentiate between Internet access and a phone network.
A: internet access is the capacity of people and associations to interface with the Internet utilizing…
Q: In the following ways, a three-tier application architecture is different from a two-tier design:…
A: Introduction: Three-tier architecture is preferable for web applications. In the following ways,…
Q: expression "passing structure pointers
A: Given :- In the above question, the statement is mention in the above given question Need to write…
Q: What is the key difference between a variable that is used just once and a static variable?
A: In this question we have to understand the key difference between a variable that is used just once…
Q: Q13: In the given MATLAB code identify the problem? x=1; while x<=10 y=x^2 end while command must…
A: Answer in step 2
Q: When it comes to the construction of a web application, what part does XLST play?
A: XLST is the extensible stylesheet languages transformations. It is the xml languages which contains…
Q: Given the 1101011011 data frame and generator polynomial G(x)=x^4+x+1. Derive the transmitted frame.
A:
Q: What value will RAX contain after the following instructions execute? .data dwordVal DWORD 84326732h…
A: The step by step is below:
Q: What are the advantages of making use of the exception handling method?
A: Given: In the following, we will discuss the advantages of using exception handling. Handling…
Q: Q2: Choose the correct MATLAB command to plot the given function with a black solid line and circle…
A: Please refer below for your reference: The correct option isplot(x,y,'-ko')
Q: Is there any advantage to using bytecode instead of machine code?
A: Given: When the interpreter is accessible, Bytecode executes. Only the Java virtual machine is used…
Q: What part does MVC play in the overall organization of web applications? What are some of the…
A: MVC: The Model-View-Controller (MVC) design divides an application into three logical components:…
Q: Risk analysis as it pertains to information security: what does it mean?
A: Risk assessment: The uncertainty of predicted cash flow streams, the variance of portfolio or stock…
Q: 2) What will be the value in EAX after the following lines execute? mov eax, 30020000h dec ax
A: Complete answer is below..
Q: Each of the following methods for storing a relational database has two benefits and two drawbacks.…
A: Relational database : A relational database is a collection of data components connected by…
Q: has several advantages. Search engine optimization may be explained
A: Notes: As per the rules, we can solve only one question at a time. Hence resubmit the question for…
Q: Use Matlab to plot the function range 0<x<3 and -3<x<6 f(x) = (x + 1)(x + 2)(2x -0.25) - e*,
A: We need to generate the plot for above function. See below steps for code and output.
Q: What are the best solutions for developing old systems? In what cases would it be more cost…
A: Intro In the present current endeavor, speed is the situation. Furthermore, with an incorporated…
Q: Compared to connection-based protocols, consider the benefits and drawbacks of connectionless…
A: Given: Connectionless services provide a number of advantages. It has modest operating costs. It…
Q: What strategies do hackers use in the practise of social engineering in order to get a user's login…
A: The social engineering can be denoted as the study of the techniques that are utilized by hackers or…
Q: What is the rationale for the placement of disc folders on discs by various operating systems? What…
A: Beginning: Folders may be put in a variety of locations on the disc. 1>Placement in the middle…
Q: Why are VPNs more secure than public internet access?And how does VPN tunnel mode work? Explain!Why…
A: Introduction: Why are virtual private networks (VPNs) more secure than public internet access? When…
Q: Even though we know the CPU is printed and electrical speed cannot be changed, what happens…
A: The above question is solved in step 2 :-
Q: Compared to connection-based protocols, consider the benefits and drawbacks of connectionless…
A: Inspection: Actually, there was a question about connectionless and connection-based protocols.…
Q: Do you have any suggestions for reducing the danger that the network poses?
A: Solution: Network security: Data is a company's most important resource, thus network security is…
Q: Computing at the user level
A: Intro End-user computing (EUC) is a term that refers to the technologies that IT professionals use…
Q: What mechanisms of the World Wide Web standards are required for an application environment that is…
A: The answer is given below.
Q: Provide some examples that illustrate the differences and similarities between two-tier and…
A: Web applications: A web application benefits both the end-user and the organisation. Web…
Q: 4. Provide a description of mobile applications, including popular apps and app shops.
A: Intro Mobile Apps: Mobile apps are software applications that are intended to run on mobile…
Q: Instead of an HTTP-based webpage, why use a file system?
A: File system site and HTTP(Hyper Text transfer protocol) site both are utilized for correspondence or…
Q: What is the definition of routing? Describe in detail the key components of a router and the routing…
A: Introduction: Routing is the process of determining a route for data to be moved from source to…
Step by step
Solved in 2 steps

- In "Computing Machines and Intelligence," the English mathematician Alan Turing (1912-1954) wrote, "If each man had a definite set of rules of conduct by which he regulated his life, he would be a machine, but there are no such rules, so men cannot be machines." Using what you now know about Logic, determine whether this statement make sense and explain. Construct a truth table for Turing's statement and determine if this statement is a tautology.Determine whether the passage expresses an argument. Mark Yes or No. If it does express an argument, highlight the premise(s) (P) and underline the conclusion. 1. John must be in the library. I've checked the dorm, the cafeteria, and the game room, and I know he doesn't have a class now. 2. As TikTok video viewing has increased, the reading ability of public school children has decreased. Therefore, TikTok viewing contributes to reading problems. 3. If God is all good, he would not will evil. If he is all powerful, he would not permit evil. But there is evil. Therefore, God is not all powerful, or he is not all good. 4. If the Republicans win the next election, there will be a recession, federal revenues will fall, and the deficit will grow. If the Democrats win the next election, there will be increased spending and the deficit will grow. Since either the Republicans or the Democrats will win the next election, the deficit will grow. 5. Because I failed to study, I didn't pass the…Part I. Let p, q, and r be the following simple statements: p: Sydney is the capital of Australia. q: Thirteen is a prime number. r: The Trinity University of Asia is in Quezon City. Express each of the following propositions as an English sentence and determine its truth value. Part II. Use the truth table to determine whether the following pairs of statement are logically equivalent or not . 1. ~(p↑q)and~p↑-q 2. p↓(q↑r)and(p↑q)↓(p↑r)
- Determine whether the following statements are logically equivalent or not. Show your work to clearly indicate your answer. p→¬qand¬(p→q)Prove ⊢ (¬A → A) → A in Hilbert deductive system. Note: In addition to the axioms and rule of inference of H, you may use any of the derived rules and/or theorems 3.20-3.30 (as numbered in the textbook). You may not use theorem 3.31, as this is precisely that theorem.book Mordechai Ben-Ari Mathematical Logic for Computer Science Third Edition Prove {¬A} ⊢ (¬B → A) → B in Hilbert deductive system. Note: In addition to the axioms and rule of inference of H, you may use any of the derived rules and/or theorems 3.20-3.30 (as numbered in the textbook). book Mordechai Ben-Ari Mathematical Logic for Computer Science Third Edition PLEASE solve these with the help of 3 axioms and 1 rule of inference with the derived proof 3.20-3.30.i) Carefully explain why p ↔ q can be written as “p is necessary and sufficient for q”. ii) Verify the second part of De Morgan’s laws, ∼ (p∨q) ≡ (∼ p) ∧(∼ q), in two ways: (a) Explain it using conversational English, using your own particular examples of statements for p and q. (b) Use a truth table.
- Determine which pairs of statements are equivalent.Note: You should be able to do this without a truth table.i. If I am happy, then the Giants won.ii. If the Giants win, then I am happy.iii. If the Giants lose, then I am unhappy.iv. If I am unhappy, then the Giants lose.Select all that apply:A. ii and ivB. i and ivC. iii and ivD. i and iiE. ii and iiiF. i and iiiThe king and the Chees board. A king is so impressed by one of his courtiers thet he offers to give him whatever he desires. The wily courtier replies that all he wants are some grains, as many as could be placed on each square of a chess board. Specially, grains are to be placed on each square of a chess board, as follows. One grain is to be placed in the first square,two in the second square , four in the third square and so on. (We'll assume the squares are big enough to accommodate the increasing numbers of grains they're each expected to hold). Assuming anNxN chess board, WAP in java that displays the exacy number of grains required to cover an NxN board. Input: integer N , Output:integer P (number of grains)The king and the Chees board. A king is so impressed by one of his courtiers thet he offers to give him whatever he desires. The wily courtier replies that all he wants are some grains, as many as could be placed on each square of a chess board. Specially, grains are to be placed on each square of a chess board, as follows. One grain is to be placed in the first square,two in the second square , four in the third square and so on. (We'll assume the squares are big enough to accommodate the increasing numbers of grains they're each expected to hold). Assuming anNxN chess board, WAP that displays the exacy number of grains required to cover an NxN board. Input: integer N , Output:integer P (number of grains)
- Suppose you wish to prove a theorem of the form “if p then q .”(a) If you give a direct proof, what do you assume and what do you prove?(b) If you give a proof by contraposition, what do you assume and what do you prove?(c) If you give a proof by contradiction, what do you assume and what do you prove?Problem 4) Translate the given statement into propositional logic using the propositions provided. (Do not simplify the expressions.) “It is not true that you can go out without a hat only if it is warm and not rainy.” Express your answer in terms ofh: “You can go out without a hat”, w: “It is warm”, andr: “It is rainy”.Solve the following puzzle by translating statements into logical expressions and reasoning fromthese expressions.Four friends have been identified as suspects for an unauthorized access into a computer system.They have made statements to the investigating authorities.1-Alice said Carlos did it.2-John said I did not do it.3-Carlos said Diana did it.4-Diana said Carlos lied when he said that I did it.If the authorities also know that exactly one of the four suspects is telling the truth, who didit?

