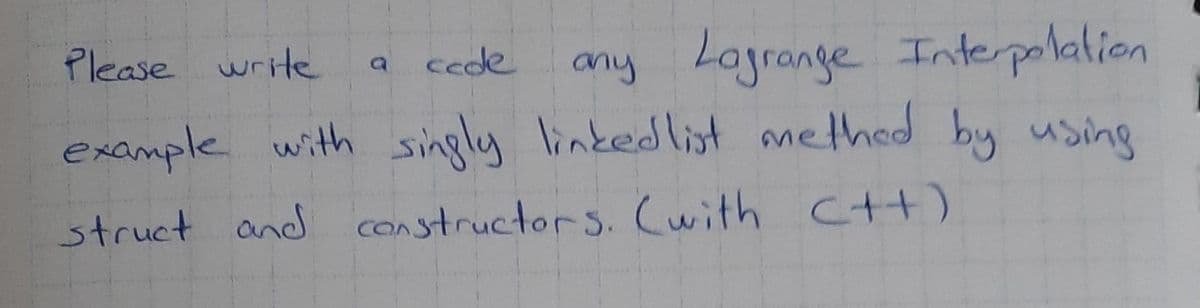
Lagrange Interpolalion Please write cede any example with singly linkedlist methed by using struct and constructors. (with Ctt)
Q: Computer science Which protocol utilises SSL or TLS to safeguard browser-to-webserver connections?
A: Introduction: Which protocol utilises SSL or TLS to safeguard browser-to-webserver connections?
Q: Given the classical sets A = {9,5,6,8,10}, B = {1,2,3,4,7,9} and C = {1,0}, define on universe X = {...
A: According to answering policy we can answer only 1st question. For remaining questions you can resub...
Q: CPSC 131: Introduction to Computer Programming II Program 3: Inheritance and Interface
A: Ans: Program for inheritance: class Animal{ void eat(){System.out.println("eating...");} } cla...
Q: JAVA PROGRAMMING: Lesson – Overloading Constructors 1. a .Create a class named Circle with fields n...
A: As per our guidelines, we are supposed to answer only one question. Kindly repost the remaining ques...
Q: Explain why the allocation of records to blocks has a significant impact on database system performa...
A: Introduction: The following is the justification behind record distribution:
Q: 1 Description of the Program In this assignment, you will make two classes, Student and Instructor, ...
A: According to the Bartleby rules, only one question can be solved at a time. //Instructor.java ...
Q: A Telecommunication channel in form of a copper cable has 4 kHz bandwidth. Calculate the amount of d...
A: The amount of the data that has to be transmitted can be done in two ways. One is with noise and the...
Q: 8. Determine the twos' complement for decimal 94. Provide 10 answer in binary in a WORD size memory ...
A: Given decimal number is (94)10
Q: What does the superparamagnetic limit signify in terms of disc drives?
A: Introduction: What does the superparamagnetic limit signify in terms of disc drives?
Q: Explain how the size of the organization and the size of the program are factors that influence soft...
A: let us see the answer:- Introduction:- The art and discipline of organising and supervising software...
Q: tly is the issue with NRZ? And, more importa
A: Below the exactly is the issue with NRZ
Q: Here is a loop that starts with an initial estimate of the square root of a, x, and improves it unti...
A: Introduction This is for Python Please see attachment
Q: Define the concept of dynamic random access memory.
A: Dynamic Random Access Memory is a common type of RAM(Random Access Memory) So first, let's talk abou...
Q: Write a static method that displays all combinations of picking two numbers from the array list: pu...
A: let us see the answer:- INTRODUCTION:- The elements of the Java ArrayList class are stored in a dyna...
Q: Slot Machine Simulation A slot machine is a gambling device that the user inserts money into and the...
A: Solution :: Let's see the above question in Java programming language.. Code ::
Q: What is the purpose of the edit menu commands?
A: The problem is based on the basic tools in microsoft office softwares.
Q: Write JavaScript codes to validate a name text field so that when a user submits the form with the n...
A: function validateform() { var name = document.myform.name.value; var Regex =...
Q: What exactly is a consistent database state, and how does one go about achieving one?
A: Consistency of data implies no duplication or mismatching of data.
Q: List four different types of external disk interfaces.
A: INTRODUCTION: Here we need to answer the four different types of external disk interfaces.
Q: What are the primary components of the database system
A: Introduction: A database management system (or DBMS) is simply a computerized data storage system. U...
Q: It is beyond our scope to discuss how operating systems implement processes.
A: Introduction: It is beyond the scope of this project to figure out what operating systems to use and...
Q: Python program using function as ojcets in High order function.This assign call the actual function,...
A: Below the python program using function as ojcets in High order function.
Q: Explain the case of deadlock that may arise during inter process communication. What role does the o...
A: Deadlock is a condition in which a set of processes are blocked because each process holds an applic...
Q: What is the significance of the Bevco.xls file?
A: Introduction: An XLS file is a spreadsheet file generated with Microsoft Excel or exported from anot...
Q: Apply mergesort to sort the list [14, 13, 11, 12, 16, 12, 18, 15, 19, 17] in increasing order.
A: The solution for the above given question is given below:
Q: Is there a point to Big-existence? O's What is the most dire scenario for Big-O? Why should you be c...
A: Introduction: Big-purpose: O's The big-O notation is used to express how the time required to execut...
Q: (4) Make use of the Givens rotations to determine the QR factorization of the following martrix. Mak...
A: PROGRAM INTRODUCTION: Declare and initialize the required matrix. Define two components Q and R tha...
Q: What factors can cause an input stream to fail? When an input stream hits the fail state, what happe...
A:
Q: How are truly distributed systems modeled?
A: The answer of these is given below.
Q: Create an ER Diagram that describes the following requirement: John is trying to help his price-...
A: An ER diagram is an entity-relationship diagram. It is used to represent the relationship between en...
Q: How do I rewrite this code so that when I print it the numbers come out like this (xxx)-xxx-xxxx or ...
A: Here is the approach :- First create one more empty string. Then iterate over the string of phone ...
Q: Explain the differences between the bounded and unbounded implementations of the stack.
A: Stack: Stacked data structures are defined by the order in which elements are added and removed (mai...
Q: 1. Resolve Ip address and route table: 192.168.22.30 /25 2. What is the difference b/w NAT and PAT 3...
A: "Since you have asked multiple questions I am solving the first 2 for you if you want an answer for ...
Q: 3. Which ISA classified architecture makes the efficie main memory because the complexity (or more c...
A: Answer: The CISC architecture is designed for the efficient use of main memory because, in the CISC,...
Q: Predict the output of the following code: 1 var msg = 'hello!"; for(var x = 24; x > msg.length + 6; ...
A: msg is initialized with hello! Then we have a loop which is iterating for some times and printing th...
Q: Create a function that reverses an array This challenge is particularly helpful if you're planning t...
A: Introduction: A collection of things stored in contiguous memory spaces is referred to as an array. ...
Q: Write a program in C++ that defines a class named StringOps. Declare data members of this class as d...
A: A class is a group of objects which have common properties. A constructor is a method that is used ...
Q: Apply suitable graph traversal technique which uses queue as a supporting component to carry out the...
A:
Q: Can you explain the high level steps you will normally follow to connect to a database of your choic...
A: We may use the cascade interaction to identify the required assignments, as well as the information ...
Q: The user decides whether 1. Trapezoid, 2. Ellipse, or 3. Equilateral Triangle. Compute the area of t...
A: The Code is given below.
Q: Engineering students were working on their final projects. Before finalizing their projects, they we...
A:
Q: Determine whether the following assertion is true or false; if it is true then prove it, and if it i...
A: We are given an assertion on Euler cycle, we will see if the assertion is true or false. Please refe...
Q: Define collapse which reduces a list of MkType a b to two lists of type a and b respectively. You sh...
A: The collapse which reduces a list of MKType a b to two lists of type a and b respectively respecting...
Q: Computer science Is there any benefit to employing many fact tables?
A: Introduction Computer science Is there any benefit to employing many fact tables?
Q: 2. What type of architecture, under ISA classification, directly uses the memory, instead of a regis...
A: The expression "CISC" (complex instruction set computer or computing) alludes to PCs planned with a ...
Q: Explain two reasons why a national educational technology standard is required.
A: What are National Educational Technology Standards? National Educational Technology Standards(NETS)...
Q: Interpreter and compiler are two different things.
A: INTRODUCTION: Compiler: It is a computer program that converts high-level programming code to machin...
Q: Provide a Python program (In Python IDLE or PyCharm) that will ask the user to type the student’s na...
A: Program Approach:- 1. Declare variables 2. Take the inputs from the user 3. Create the user-defined ...
Q: The several methods of file access are listed here. I'm wondering about the benefits and drawbacks o...
A: Introduction: The most basic file access method is: File organization is nothing more than gathering...
Q: Is there a list of the many forms of malware and what they do?
A: Introduction: Malware is a broad phrase that refers to harmful software, including Malware, ransomwa...
Step by step
Solved in 3 steps with 3 images

- do the changes in this program according to the given instruction like coaches instead of teachers,sports name instead of courses etc, import java.util.*;class CourseManager{//toatl students each section can holdstatic int max_Students;//mapping of each sections w.r.t to courseHashMap<String,ArrayList<Section> > courses ; //constructor for CourseManagerpublic CourseManager(int max){max_Students = max;courses = new HashMap<>();}//class Person which will be used by teacher and students to inherit its propertiesstatic class Person{String name;int age;public Person(String name , int age ){this.name = name;this.age = age;}}//teacher classstatic class Teacher extends Person{int id;public Teacher(int id , String name , int age ){super(name , age );this.id = id;}}//student classstatic class Student extends Person{int id;public Student(int id , String name , int age ){super(name , age );this.id = id;}}//section classstatic class Section{int section;String course ;Teacher…Using Java write a method, reverse(), that reverses the order of elements in a DLListIf N represents the number of elements in the collection, then the contains method of the ArrayCollection class is O(1). True or False If N represents the number of elements in the list, then the index-based add method of the ABList class is O(N). True or False
- Which methods from the List interface are not supported by ArrayList and LinkedList? Explain why you think such methods aren't a part of List.In java, how do I implement the following methods into a linkedlist class. 1) removeLast() – remove the last number of the list 2) removeLeast()- remove least number in the list 3) removeMax()- remove largest number in the list 4) removeFirst() – remove the first number of the list 5) addNum()- add another number to the listSo i am implementing a set template using a LinkedList here is what I've tried so far: template<typename T>T LinkedList<T>::set(int index, T element){ int i=0; if(index==i) return -1; Node<T>*current=head; while(index!=i) { current=current->next; i++;}return current(element);} I am not confident about it so any suggestions and pointers are welcome... its a template that I want to use to find the element and its index in a list. this is c++
- For the sake of argument, let's say you've created ADT LinkedStack with the stack's top node being the chain's terminal link. Please describe how the following methods may be defined without using traversal. verbs meaning to "pop" or "peek"If operations given below is applied on a stack, what will be the result? For array implementation we need is_full() operation, however in linked list case this function is not required. Explain the reason createStack()push(1)push(2)push(1)peek()push(2)pop()pop()pop()push(2)push(1)push(2)Apart from the main list in the list above, elements with the same value are also linked. According to this; a) Write the Generic Node class. b) Write the method that adds a new element to the end of the list. JAVA CODE
- Removes the element with key k if it exists. The position of current is// unspecified after calling this method.The first element of the returned pair // indicates whether k was removed, and the second is the number of key// comparisons made.Pair<Boolean, Integer> remove(K key); // Returns all keys of the map as a list sorted in increasing order. List<K> getAll(); } write this method javapackage Linked_List; public class RefUnsortedList<T> implements ListInterface<T> {protected int numElements; // number of elements in this listprotected LLNode<T> currentPos; // current position for iteration// set by find methodprotected boolean found; // true if element found, else falseprotected LLNode<T> location; // node containing element, if foundprotected LLNode<T> previous; // node preceeding locationprotected LLNode<T> list; // first node on the listpublic RefUnsortedList(){numElements = 0;list = null;currentPos = null;}public void add(T element)// Adds element to this list.{LLNode<T> newNode = new LLNode<T>(element);newNode.setLink(list);list = newNode;numElements++;}protected void find(T target)// Searches list for an occurence of an element e such that// e.equals(target). If successful, sets instance variables// found to true, location to node containing e, and previous// to the node that links to location. If not successful,…package Linked_List; public class RefUnsortedList<T> implements ListInterface<T>{protected int numElements; // number of elements in this listprotected LLNode<T> currentPos; // current position for iteration// set by find methodprotected boolean found; // true if element found, else falseprotected LLNode<T> location; // node containing element, if foundprotected LLNode<T> previous; // node preceeding locationprotected LLNode<T> list; // first node on the listpublic RefUnsortedList(){numElements = 0;list = null;currentPos = null;}public void add(T element)// Adds element to this list.{LLNode<T> newNode = new LLNode<T>(element);newNode.setLink(list);list = newNode;numElements++;}protected void find(T target)// Searches list for an occurence of an element e such that// e.equals(target). If successful, sets instance variables// found to true, location to node containing e, and previous// to the node that links to location. If not successful,…

