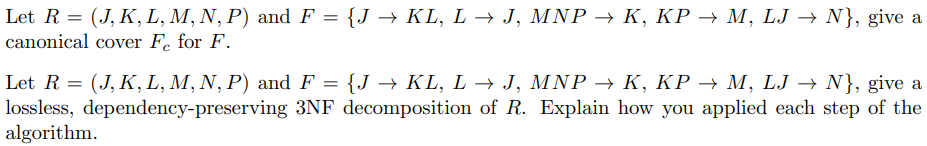
Let R = (J,K, L, M, N, P) and F = {J → KL, L → J, MNP → K, KP – M, LJ → N}, give a canonical cover F. for F.
Q: The first two bytes of a 4M x 16 main memory have the following hex values: Byte 0: FF Byte 1: 01 If...
A: Below is the answer to above question. I hope this will be helpful for you...
Q: What is the maximum number of arguments that a catch block can have
A: Exception handling: The most common sorts of mistakes that a programmer may encounter are logical an...
Q: What are the six different types of organizational structures? Is it possible to create a comparison...
A: Introduction: An organizational structure is a framework that directs particular operations to fulfi...
Q: design an application for the ABC Company that will process inventory from a file called ABC_Invento...
A: Code: count=0summ=0 f = open("ABC_INVENTORY.txt", "r")for x in f: count=count+1 if(count%3==0)...
Q: Provide proofs or disproofs of the following arguments (use conditional proof and 4 quantifier rules...
A: Explain: x represents anyone. R (x): He fixes his own car. H (x): High skill. S (x): Save a lot of m...
Q: What exactly do the terms static media and dynamic media mean? Please offer at least two examples of...
A: Static media defines the media articles which generally doesn't get changed or modified. Dynamic med...
Q: Write a code in C language that will create graphs and write them to a file in a particular format. ...
A: Introduction Write a code in C language that will create graphs and write them to a file in a partic...
Q: What is the output in c++
A: 1. The given program implements a do-while loop as follows : Initialization : product = 1 i = 2 It...
Q: Give two examples of typical fingerprinting algorithms.
A: Introduction Fingerprinting Algorithms: An arbitrarily large data object (for example, a computer ...
Q: Computer science What is forensic software's purpose, and how does it help investigators?
A: Introduction: The function of forensic software is discussed in this question, as well as how it off...
Q: Which of these devices is responsible for ensuring the integrity of data transferred through a netwo...
A: Intro These devices is in charge of maintaining the integrity of the data that is sent via a networ...
Q: Exercise 3: Let G be the grammar with vocabulary V {S, A, a, b}, set of terminals T-(ab} starting sy...
A: I'm providing the answer of both questions. I hope this will be helpful for you
Q: Define supertype, subtype, and discriminator
A: Introduction: A corporation having more than one connection may also be a company with fewer than on...
Q: Computer science What impact has the rise of mobile devices had on IT professionals?
A: Introduction: It is made up of two-way portable communication devices, computer devices, and the net...
Q: Write a swap function, that swaps the values of two variables in main, but use pointers instead of r...
A: Please refer to the following steps for the complete solution to the problem above.
Q: ctive of this lab is to create the beginnings for a python-based card game. We DO NOT expect a fully...
A: % define a packagefrom random import randint % define and assign valuesNumCard = 52DECK = 0Player = ...
Q: Explain how a publish-subscribe system, such as Apache Kafka, may be used to run several operations ...
A: System for Publishing and Subscribing An operation is kept in a topic in like the publish-subscribe ...
Q: Is a self-transition required in every State Diagram? What gives you the impression that this is the...
A: Introduction: The transition between states is defined by a state diagram, which is dependent on the...
Q: Computer Science What are the different risk treatment options and provide an example how one of the...
A: Risk Treatment is the process of selecting and implementing of measures to modify the risk. Risk tre...
Q: Why should the IV in CBC be safeguarded?
A: Introduction: Because an initialization vector differs from a key in terms of security, it typically...
Q: "A complex number is defined as z=a+i*b, where a is the real part, and b is the imaginary part. In o...
A: According to the information given:- We have to write a complex number method that define the real a...
Q: Why is payroll seen to be an excellent application for batch processing using magnetic tape storage ...
A: Introduction: The batch processing utility takes the input data in bulk, checks its specifications, ...
Q: What exactly is the distinction between abstraction and polymorphism?
A: answer is
Q: ssume that A and B are known to be true, X, Y, and Z are known to be false, and that the truth value...
A: As per our policy we can only solve three subquestions . Please post other questions separately . A...
Q: Python: How do I get the total of bal of top4(which can be specified)) bal = { "bal": [ 3955,...
A: I have provided PYTHON CODE along with CODE SCREENSHOT and OUTPUT SCREENSHOT--------------...
Q: What are the applications of computers in design, given examples?
A: Introduction Computer: It is a device that can be used to carry out a set of athematic and logical ...
Q: Exercise • Write a program that asks the user -Do you want to use this program? (y/n) • If the user ...
A: Code: #include <iostream> using namespace std; int main(){ string c="y"; int count=1; ...
Q: Make a list of all PDUs that will be encapsulated
A: Intro Protocol Data Units and Encapsulation In order for application data to travel from one host to...
Q: What are the Advantages and Disadvantages of Using Cloud Storage for a Small Business?
A: Cloud: Advantages Accessibility: Files in the cloud can be accessed from anywhere with an Internet ...
Q: approach for system development definition
A: System development methodology: The whole purpose of system development is the enhancement of the p...
Q: What does the term "Cell" mean in terms of computer architecture and design? (Include details)
A: Introduction
Q: What is the maximum number of arguments that a catch block can have?
A: Introduction: Put any code that could raise or throw an exception in a try block, and any lines that...
Q: Is there a distinction between mobile devices and laptop computers? Give an example to back up your ...
A: Introduction: The most obvious distinction between a mobile phone and a personal computer is their s...
Q: 2)primary DRAM
A: RAM It is a component of the computer's Main Memory, which the CPU can access directly. Random-acc...
Q: Is it a description of how a computer works? Then we'll discuss computer components, right?
A: let's see the solution
Q: Explain why domain shuffles are caused by exon shuffles.
A: Intro Domain Shuffling Although certain bacteria have gained domains from eukaryotic species by ho...
Q: Write a Java program to take a list of non-negative integers, print an integer list of the rightmost...
A: Create two arrays, one to store the integer and list and one to store the right most digit. Input th...
Q: What is the connection between Vigenere cipher and Fibonacci sequence?
A: Answer :
Q: H.W Find the inverse to the following matrices by using adjoint method. 21 c. A = 3 4 1 4 3. 3. 4. 2...
A:
Q: What is one advantage to consumers of having a non-biased, trusted source test ultrasonic devices an...
A: let us see the answer:- Introduction:- Ultrasonic testing (UT) is a practical and adaptable non-dest...
Q: Open with Google Docs A Company decided to give a bonus for the employees based on their skills and ...
A: Use if else if ladder to calculate the bonus based on the input years
Q: Write a program that computes the following. Use while loop. Define a function as follows: public st...
A: Here I have defined the function addAll(). In this function, I have used a while loop till the value...
Q: Q1 Direct proof is a method of mathematical proof. Name at least two other methods of proof: Us...
A: Direct proof example and to other method in below step
Q: Set A consist of D1, D2, D4 and C1 bits; Set B consist of D1, D3, D4 and C2 bits; Set C consists of ...
A: Given, D1 D2 D3 D4 = 1 1 0 1 C1 C2 C4 = 0 0 1 Let the flag values of respective check bits C1 C2 C4 ...
Q: Q1/ Find the derivative () of the following functions using the Matlab dx program 1) f(x) = sin ( 6x...
A: Differentiate each term with respect to xx, then solve for f dfdx = -y sinxyx + 6 cos6xx - ...
Q: Explanation and examples: 1)The primary SRAM 2)first-generation DRAM
A: Intro RAM It is a component of the computer's Main Memory, which the CPU can access directly. Rand...
Q: Write a pseudocode for a divide-and-conquer algorithm for fnding a position of the largest element i...
A: Divide And Conquer Algorithm Divide-and-Conquer is an algo. design paradigm. A divide-and-conquer al...
Q: Many times, the needs of several stakeholders are conflicting. Describe ONE technique for reaching c...
A: Introduction: Stakeholders in a company include its employees, suppliers, local communities, credito...
Q: Question 6 Which of the following have to be true for a collision resistant hash function? O difficu...
A: The correct option will be (a) and (d) Explanation:- Option(a) Collision resistant is a property of...
Q: e I need Thank
A: HTML CODE is below with CSS designining:
Computer Science
Trending now
This is a popular solution!
Step by step
Solved in 3 steps

- Consider the Omega network and Butterfly network from p nodes in the leftmost column to p nodes in the rightmost column for some p=2^k. The Omega network is defined in Chapter 2 of the text book such that Si is connected to element S j if j=2i for or j=2i+1-p for See Chapter 2 in text book for its definition. The Butterfly network is an interconnection network composed of log p levels (as the omega network). In a Butterfly network, each switching node i at a level l is connected to the identically numbered element at level l + 1 and to a switching node whose number differs from itself only at the lth most significant bit. Therefore, switching node Si is connected to element S j at level l if j = i or j . Prove that for each node Si in the leftmost column and a node Sj in the rightmost column, there is a path from Si to Sj in the Omega network. Prove that for each node Si in the leftmost and a node Sj in the rightmost, there is a path from Si to Sj in the Butterfly network.Suppose there is undirected graph F with nonnegative edge weights we ≥ 0. You have also calculated the minimum spanning tree of F and also the shortest paths to all nodes from a particular node p ∈ V . Now, suppose that each edge weight is increased by 1, so the new weights are we′ = we + 1. (a) Will there be a change of the minimum spanning tree? Provide an example where it does or prove that it cannot change. (b) (3 points) Will the shortest paths from p change? Provide an example where it does or prove that it cannot change.6. Consider a binary classification problem using 1-nearest neighbors with the Euclidean distance metric. We have N 1-dimensional training points x(1), x(2), . . . x(N ) and corresponding labelsy(1), y(2), . . . y(N ) with x(i ) ∈ R and y(i ) ∈ {0, 1}. Assume the points x(1), x(2), . . . x(N ) are in ascending order by value. If there are ties during the 1-NN algorithm, we break ties by choosing the labelcorresponding to the x(i ) with lower value.
- The set of letters S consists of 30 As, 6 Bs, 24 Cs, 15 Ds, and 15 Es. The set of letters T consists of 25 As, 20 Bs, 15 Cs, 5 Ds and 35 Es. What is the mutual index of coincidence between sets S and T? Leave your answer as a fraction in lowest termsQuestion 1: In graph theory, a graph X is a "complement" of a graph F if which of the following is true? Select one: a. If X is isomorph to F, then X is a complement of F. b. If X has half of the vertices of F (or if F has half of the vertices of X) then X is a complement of F. c. If X has the same vertex set as F, and as its edges ONLY all possible edges NOT contained in F, then X is a complement of F. d. If X is NOT isomorph to F, then X is a complement of F. Question 2: Which statement is NOT true about Merge Sort Algorithm: Select one: a. Merge Sort time complexity for worst case scenarios is: O(n log n) b. Merge Sort is a quadratic sorting algorithm c. Merge Sort key disadvantage is space overhead as compared to Bubble Sort, Selection Sort and Insertion Sort. d. Merge Sort adopts recursive approachThe Barabasi and Albert model ´• A discrete time network evolution process,relating the graph G(t + 1) to G(t).• Start at t=0 with a single isolated node.• At each discrete time step, a new node arrives.• This new node makes m edges to already existing nodes.(Why m edges? i.e., what happens if m = 1?)• The likelihood of a new edge to connect to an existing node jis proportional to the degree of node j, denoted dj.• We are interested in the limit of large graph size, n → ∞.Visualizing a PA graph (m = 1) at n = 5000Probabilistic treatment (kinetic theory)• Start at t = 0 with one isolated node (or a small core set).– At time t the total number of nodes added n = t.– At time t the total number of edges added is mt.• Let dj(t) denote the degree of node j at time t.• Probability an edge added at t + 1 connects to node j:P r(t + 1 → j) = dj(t)/Pjdj(t).• Normalization constant easy (but time dependent):Pjdj(t) = 2mt(Each node 1 through t, contributes m edges.)(Each edge augments the degree of…
- Suppose that the road network is defined by the undirected graph, where the vertices represent cities and edges represent the road between two cities. The Department of Highways (DOH) decides to install the cameras to detect the bad driver. To reduce the cost, the cameras are strategically installed in the cities that a driver must pass through in order to go from one city to another city. For example, if there are two cities A and B such that the path that goes from A to B and the path that goes from B to A must pass the city C, then C must install the camera. Suppose that there are m cities and n roads. Write an O (m + n) to list all cities where cameras should be installed.Consider F = {BC -> D, B -> E, CE -> D, E -> CA, BF -> G} and R(A,B,C,D,E,F,G) 1.Find a minimal cover for F. 2.Find all many keys for R.Let A, B, C, D be the vertices of a square with side length 100. If we want to create a minimum-weight spanning tree to connect these four vertices, clearly this spanning tree would have total weight 300 (e.g. we can connect AB, BC, and CD). But what if we are able to add extra vertices inside the square, and use these additional vertices in constructing our spanning tree? Would the minimum-weight spanning tree have total weight less than 300? And if so, where should these additional vertices be placed to minimize the total weight? Let G be a graph with the vertices A, B, C, D, and possibly one or more additional vertices that can be placed anywhere you want on the (two-dimensional) plane containing the four vertices of the square. Determine the smallest total weight for the minimum-weight spanning tree of G. Round your answer to the nearest integer. Note: I encourage you to add n additional points (for n=1, 2, 3) to your graph and see if you can figure out where these point(s) need to…
- Let A, B, C, D be the vertices of a square with side length 100. If we want to create a minimum-weight spanning tree to connect these four vertices, clearly this spanning tree would have total weight 300 (e.g. we can connect AB, BC, and CD). But what if we are able to add extra vertices inside the square, and use these additional vertices in constructing our spanning tree? Would the minimum-weight spanning tree have total weight less than 300? And if so, where should these additional vertices be placed to minimize the total weight? Let G be a graph with the vertices A, B, C, D, and possibly one or more additional vertices that can be placed anywhere you want on the (two-dimensional) plane containing the four vertices of the square. Determine the smallest total weight for the minimum-weight spanning tree of G. Round your answer to the nearest integer. Attention: Please don't just copy these two following answers, which are not correct at all. Thank you.…Consider a Diffie-Hellman scheme with a common prime q = 17 and a primitive root α = 3. a) If user A has a private key XA=4, what is A’s public key, YA? b) A sends YA to B. If B has a private key XB=6, what is the shared secret key, K that B can calculate and share with A? c) If B computes YB and sends it to A, what is the shared secret Key, K computed by A?Consider the following knowledge base Prove that Q is true with: 1. P → Q 2. L ∧ M → P 3. B ∧ L → M 4. A ∧ P → L 5. A ∧ B → L 6. A 7. B Forward-Chaining Backward-Chaining Resolution Prove t → s: 1. p → q 2. [q ∧ r] → s 3. [t ∧ u] → r 4. u → w 5. t → y 6. y → u 7. r → p 8. p → m i. Express in clause form ii. Forward-Chaining iii. Backward-Chaining iv. Resolution











