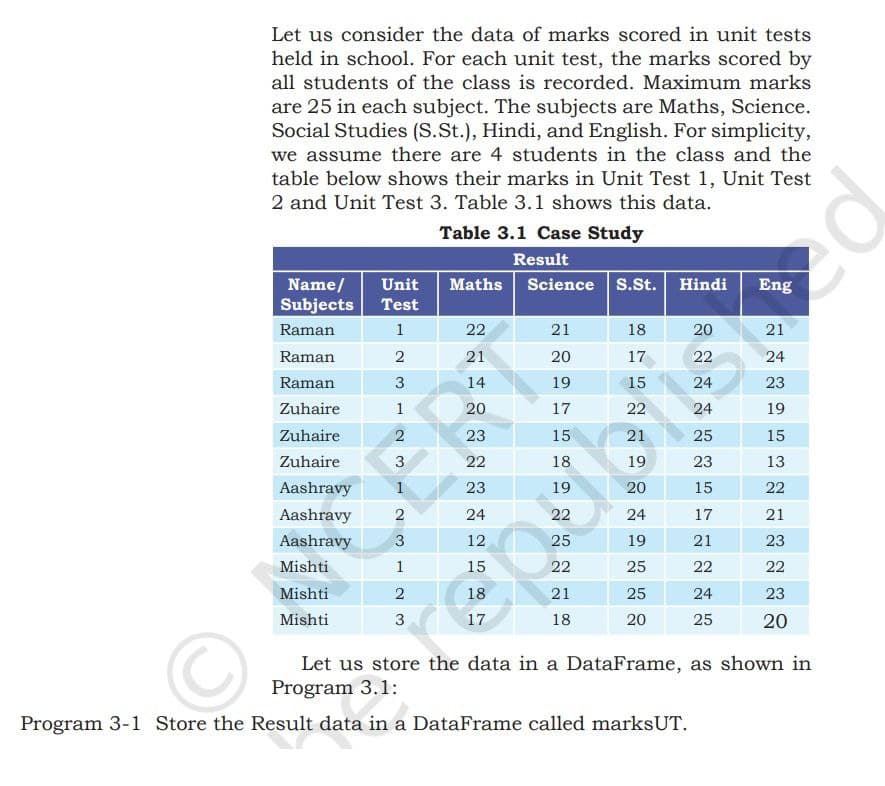
Let us consider the data of marks scored in unit tests held in school. For each unit test, the marks scored by all students of the class is recorded. Maximum marks are 25 in each subject. The subjects are Maths, Science. Social Studies (S.St.), Hindi, and English. For simplicity, we assume there are 4 students in the class and the table below shows their marks in Unit Test 1, Unit Test 2 and Unit Test 3. Table 3.1 shows this data. Table 3.1 Case Study Result Maths Science S.St. Hindi Name/ Unit Subjects Test Raman 1 Raman 2 Raman 3 Zuhaire 1 Zuhaire 2 Zuhaire 3 Aashravy 1 Aashravy 2 Aashravy 3 Mishti 1 Mishti 2 Mishti 3 22 21 14 20 23 22 23 24 12 15 587 18 17 21 20 19 17 15 22222 18 19 25 21 18 18 17 15 22 21 19 20 24 19 25 25 20 20 22 24 24 25 23 15 17 21 22 24 25 Eng 21 24 23 19 15 13 22 21 23 22 23 20 Let us store the data in a DataFrame, as shown in
Let us consider the data of marks scored in unit tests held in school. For each unit test, the marks scored by all students of the class is recorded. Maximum marks are 25 in each subject. The subjects are Maths, Science. Social Studies (S.St.), Hindi, and English. For simplicity, we assume there are 4 students in the class and the table below shows their marks in Unit Test 1, Unit Test 2 and Unit Test 3. Table 3.1 shows this data. Table 3.1 Case Study Result Maths Science S.St. Hindi Name/ Unit Subjects Test Raman 1 Raman 2 Raman 3 Zuhaire 1 Zuhaire 2 Zuhaire 3 Aashravy 1 Aashravy 2 Aashravy 3 Mishti 1 Mishti 2 Mishti 3 22 21 14 20 23 22 23 24 12 15 587 18 17 21 20 19 17 15 22222 18 19 25 21 18 18 17 15 22 21 19 20 24 19 25 25 20 20 22 24 24 25 23 15 17 21 22 24 25 Eng 21 24 23 19 15 13 22 21 23 22 23 20 Let us store the data in a DataFrame, as shown in
Operations Research : Applications and Algorithms
4th Edition
ISBN:9780534380588
Author:Wayne L. Winston
Publisher:Wayne L. Winston
Chapter20: Queuing Theory
Section20.2: Modeling Arrival And Service Processes
Problem 3P
Related questions
Question
Transcribed Image Text:Let us consider the data of marks scored in unit tests
held in school. For each unit test, the marks scored by
all students of the class is recorded. Maximum marks
are 25 in each subject. The subjects are Maths, Science.
Social Studies (S.St.), Hindi, and English. For simplicity,
we assume there are 4 students in the class and the
table below shows their marks in Unit Test 1, Unit Test
2 and Unit Test 3. Table 3.1 shows this data.
Name/ Unit
Subjects Test
Raman
1
Raman
2
Raman
3
Zuhaire
1
Zuhaire
2
Zuhaire
3
Aashravy 1
Aashravy 2
Aashravy 3
Mishti
1
Mishti
2
Mishti
3
Table 3.1 Case Study
Result
Maths Science S.St. Hindi
22
21
14
20
23
22
23
24
12
15
587
18
17
21
20
19
17
15
18
19
22
25
22
21
18
18
17
15
22
21
19
20
24
19
25
25
20
20
22
24
24
25
23
15
17
21
22
24
25
Eng
21
24
23
19
15
13
22
21
23
22
23
20
Let us store the data in a DataFrame, as shown in
Program 3.1:
Program 3-1 Store the Result data in a DataFrame called marksUT.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole