Loop: Exit: addi x9, X9, 1 sub X14, X13, X9 addi X10, X10, 4 sub X11, X10, X9 CBNZ X14 Loop Which would be the most appropriate branchĺpredictor? O predict not taken Opredict taken O predict most often taken // increment loop index: k = k + 1 // test loop index: if limit > k then X14!=0 // compute loop body: x = x + 4 // compute loop body: y = x - k // loop-body is done; goto loopback point predict least often taken
Loop: Exit: addi x9, X9, 1 sub X14, X13, X9 addi X10, X10, 4 sub X11, X10, X9 CBNZ X14 Loop Which would be the most appropriate branchĺpredictor? O predict not taken Opredict taken O predict most often taken // increment loop index: k = k + 1 // test loop index: if limit > k then X14!=0 // compute loop body: x = x + 4 // compute loop body: y = x - k // loop-body is done; goto loopback point predict least often taken
Programming Logic & Design Comprehensive
9th Edition
ISBN:9781337669405
Author:FARRELL
Publisher:FARRELL
Chapter5: Looping
Section: Chapter Questions
Problem 3RQ
Related questions
Question
Question 13 sum
.
Full explain this question and text typing work only
We should answer our question within 2 hours takes more time then we will reduce Rating Dont ignore this line
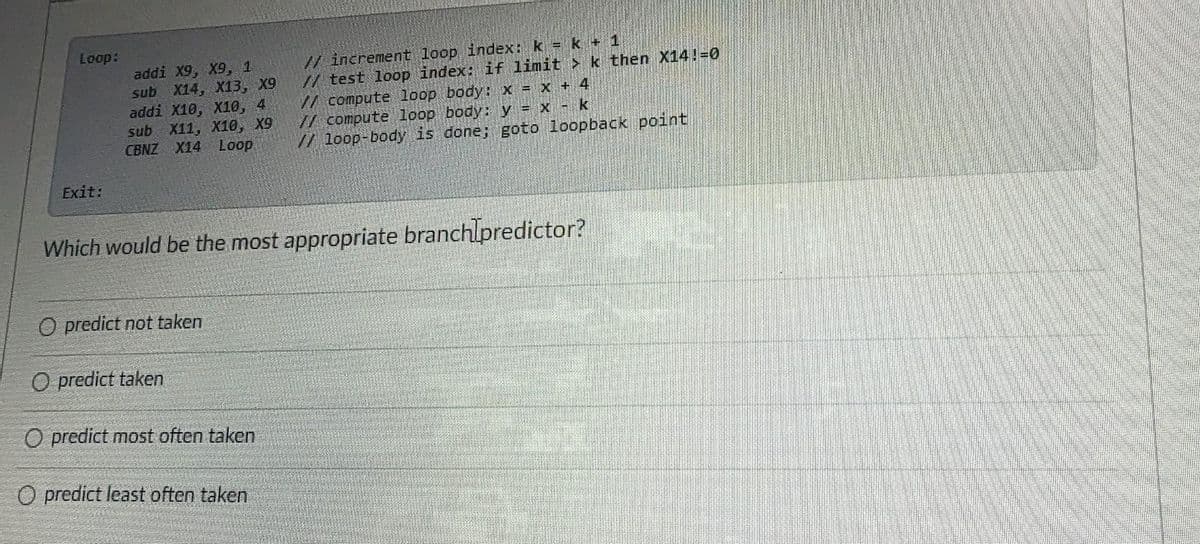
Transcribed Image Text:Loop:
Exit:
addi X9, X9, 1
sub X14, X13, X9
addi X10, X10, 4
sub X11, X10, X9
CBNZ X14 Loop
O predict not taken
O predict taken
Which would be the most appropriate branch predictor?
O predict most often taken
O predict least often taken
// increment loop index: k = k + 1
// test loop index: if limit
k then X14!=0
// compute loop body: x = x + 4
// compute loop body: y = x - k
// loop-body is done; goto loopback point
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 4 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage