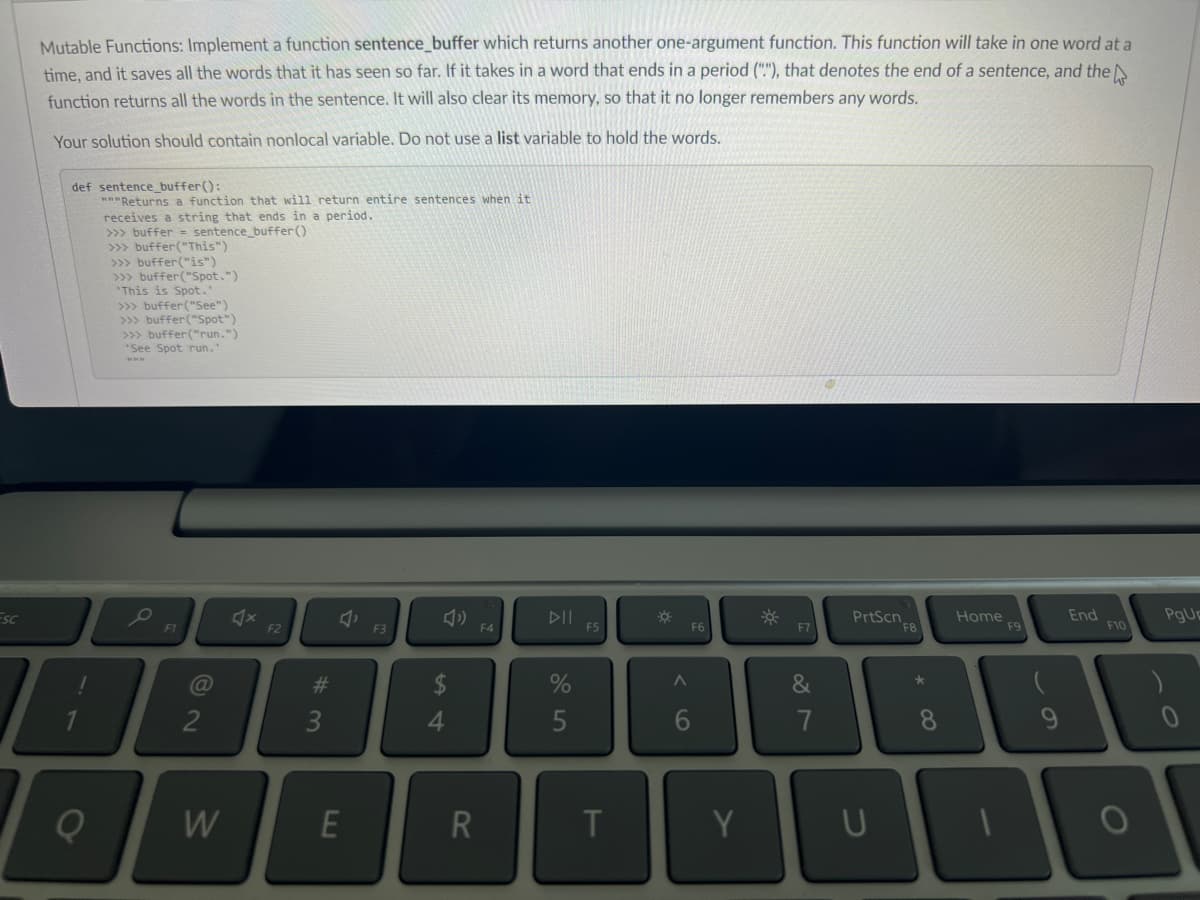
Mutable Functions: Implement a function sentence_buffer which returns another one-argument function. This function will take in one word at a time, and it saves all the words that it has seen so far. If it takes in a word that ends in a period (""), that denotes the end of a sentence, and the function returns all the words in the sentence. It will also clear its memory, so that it no longer remembers any words. Your solution should contain nonlocal variable. Do not use a list variable to hold the words. def sentence_buffer(): "Returns a function that will return entire sentences when it receives a string that ends in a period. >>> buffer= sentence_buffer() >>> buffer ("This") >>> buffer("is") >>> buffer("Spot.") This is Spot." >>> buffer("See") >>> buffer("Spot") >>> buffer("run.") "See Spot run."
Mutable Functions: Implement a function sentence_buffer which returns another one-argument function. This function will take in one word at a time, and it saves all the words that it has seen so far. If it takes in a word that ends in a period (""), that denotes the end of a sentence, and the function returns all the words in the sentence. It will also clear its memory, so that it no longer remembers any words. Your solution should contain nonlocal variable. Do not use a list variable to hold the words. def sentence_buffer(): "Returns a function that will return entire sentences when it receives a string that ends in a period. >>> buffer= sentence_buffer() >>> buffer ("This") >>> buffer("is") >>> buffer("Spot.") This is Spot." >>> buffer("See") >>> buffer("Spot") >>> buffer("run.") "See Spot run."
Chapter3: Data Representation
Section: Chapter Questions
Problem 12VE
Related questions
Question
Help now please
Python
Transcribed Image Text:Esc
Mutable Functions: Implement a function sentence_buffer which returns another one-argument function. This function will take in one word at a
time, and it saves all the words that it has seen so far. If it takes in a word that ends in a period (""), that denotes the end of a sentence, and the
function returns all the words in the sentence. It will also clear its memory, so that it no longer remembers any words.
Your solution should contain nonlocal variable. Do not use a list variable to hold the words.
def sentence_buffer():
"""Returns a function that will return entire sentences when it
receives a string that ends in a period.
>>> buffer= sentence_buffer()
>>> buffer ("This")
>>> buffer ("is")
>>> buffer("Spot.")
This is Spot."
>>> buffer("See")
>>> buffer ("Spot")
>>> buffer("run.")
'See Spot run."
www
F1
@
2
W
X
F2
#3
J
E
F3
54
Ĝ
R
F4
%
5
F5
T
☀
A
F6
6
Y
☀
&
7
PrtScn
8
U
Home
F9
End
F10
100
PgUr
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 4 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning