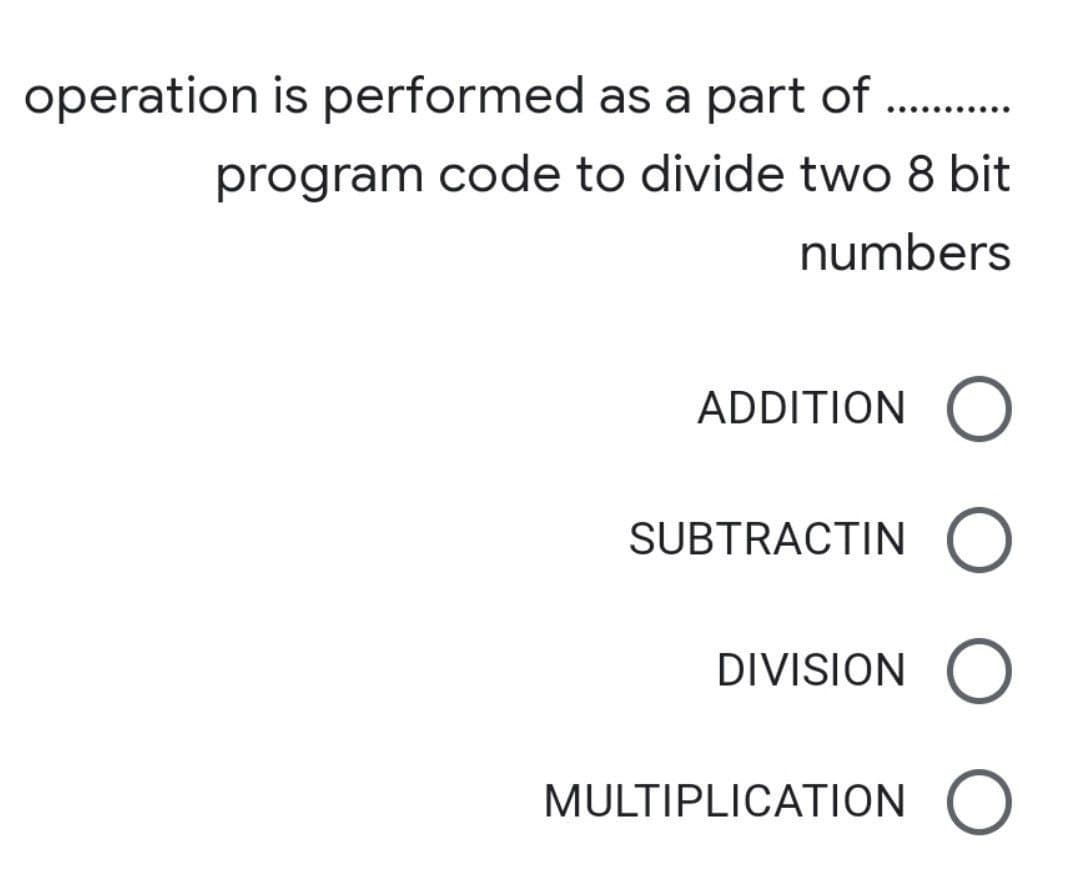
operation is performed as a part of program code to divide two 8 bit numbers
Q: To what end and how does synchronous time-division multiplexing error and flow control function?
A: Answer : The physical layer of the OSi model is the medium and hardware infrastructure of the…
Q: What measures should be followed to assure the stability and availability of a local area network?
A: Introduction: In computing, a local area network (LAN) collects small computers or other workstation…
Q: Where applicable, adopt object oriented design. When the context asks for it, structured design is…
A: Define: A programming language uses objects, as the name indicates. Things like hiding and…
Q: 1. What will the following program print out: >>> x - 15 >>> x- x +5 print(*) >>> a. 20 b. 15 с. 5…
A: As given, we need to find out the output of the following code - x = 15 x = x + 5 print(x)
Q: Wireless networks are prone to flaws that cause issues. Describe three of these concerns and their…
A: Wireless networks: Wireless networks are susceptible to faults that cause issues. Describe three of…
Q: Identify firewalls as a critical component of network security. Define the term and provide specific…
A:
Q: 1. Simplify the boolean expressions: а. А * (А+ B +C)+ B* (А'+ В') b. A * ( A' + B' + D' ) + C * ( C…
A:
Q: What is the connection between firewalls and traffic analysis and alert?
A: - We must discuss the link between Traffic Analysis and Traffic Alert, as well as firewalls. -…
Q: What are the current federal regulations for data protection and breach response?
A: Security breach notification laws, also known as information breach notification laws, are laws that…
Q: So, what exactly does "cooperative" multithreading imply in the context of a multithreading system?…
A: Explanation: In a multithreading system, what does "cooperative" multithreading involve and how does…
Q: 19. What will the following code print out: if x < 2 : print ('Small) elif x < 1 : print ('Medium)…
A: ANSWER:-
Q: ffects people and the tactics used to commit it Do you know what you can do to av
A: Introduction: Below the how you can do to avoid being a victim of cyber-crime?
Q: ge faults using the OPTIMAL, LRU, FIFO page replacement algorithms with pure demand paging. Assume…
A: Solution - In the given question, we have to find the number of page faults using the OPTIMAL, LRU,…
Q: Write a C++ program to print the text "C++ Programming." in the output along with the quotes.…
A: Your C++ program is given below as you required with an output.
Q: Write a complete interactive program that displays the alphabet on the canvas. • Each time the user…
A: ANSWER:-
Q: Do you know what are the parts of a computer? Briefly describe the situation.
A: Introduction: DRAM is a kind of semiconductor memory that allows a computer processor to store data…
Q: For the most part, what are computer systems designed to do, and why? show your point with an…
A: A computer system performs four basic functions: Input, processing, storage, and output are the four…
Q: Explain the workings of a computer system, including its components.
A: Central Processing Unit The computer does its primary work in a part of the machine we cannot see, a…
Q: a. Consider the following (2, 4) tree: (2, 4) Tree 4 3 6 10 What is the sequence of keys encountered…
A: Here in this question we have given a 2 4 tree and we have asked to find out the sequence for…
Q: Identify firewalls as a critical component of network security. Define the term and provide specific…
A: Network Security: Network Security safeguards your network and data against breaches, invasions, and…
Q: Justify the relevance of traffic analysis as a vital network defence and cJustify the role of…
A: To be decided: Justify the relevance of traffic analysis as a critical component of network defense…
Q: Do you think it's feasible to be stuck in a deadlock with just one single-threaded process? Give an…
A: Do you think it's feasible to be stuck in a deadlock with just one single-threaded process? Give an…
Q: Is there a difference between preventing deadlock and resolving deadlock?
A: Answer: The main difference between deadlock prevention and deadlock avoidance is that deadlock…
Q: 1:If the hexadecimal value 0xF0A2 is a two’s complement, halfword value, what would it be in base…
A: According to the information given:- We have to choose the correct option to satisfy the statement.…
Q: Write a C++ program that takes a prefix expression and evaluates it. It should support variables and…
A: The given expression is:= a (+ 1 (* 2 3))), (* a a)
Q: Qustion) The following character string is to be transmitted using dynamic Huffman coding: BABIATA…
A: Huffman coding is a method for efficient data compression. In this algorithm, the most frequent…
Q: Data transformation may take various shapes and forms, ranging from a simple change in data format…
A: Given: Transformation of data from one format to another, often from the format of a source system…
Q: Write loops that perform each of the following one-dimensional array operations: a. Read the 20…
A: I give the code in C along with output and code screenshot
Q: Name and describe all “Defense Methods” to secure our data?
A: Method of defence: As part of a defensive strategy, defence tactics are applied at the physical,…
Q: Consider you have an matrix of 100 elements A of which you need to calculate transpose of the…
A: An adaptive parallel matrix transpose algorithm optimized for distributed multicore architectures…
Q: Write a C++ program to print the text "C++ Programming." in the output along with the quotes.…
A: Coded using C++.
Q: What is the connection between firewalls and traffic analysis and alert?
A: Firewalls and traffic analysis and alerting must be discussed in terms of their connection with one…
Q: What precisely is a computer system, and how does it function?
A:
Q: You know, the kind of person that hacks or cyber-terrorizes? Isn't hacking an enemy organization a…
A: Cyberterrorists : The effect of the September 11, 2001 terrorist attacks also changed the…
Q: Compressed Post Office Protocol (CPOS) is a computer protocol in compressed form.
A: Introduction: The Post Office Protocol (POP) is a network protocol that enables a user client…
Q: IP spoofing is a term for what? Is it possible that IP spoofing is a security flaw?
A: Introduction Spoofing is a kind of cyber-attack in which hackers gain access to computers in order…
Q: Please show two examples of multithreading outperforming a single threaded solution.
A: Introduced: Multi-threading is a technique of programme execution that separates a process into…
Q: What are the six stages of computer forensics? Any three of the six stages should be explained.
A: What are the six stages in a computer forensic investigation? Solution: Forensic Investigation is a…
Q: When you execute your program it should ask user to input any number then check if the number is…
A: I have provided C CODE along with CODE SCREENSHOT and 2 OUTPUT SCREENSHOTS----------
Q: How are computer systems put together? Explain?
A: system of computers 1) A computer system is a set of hardware and software that is used to receive,…
Q: Q3. (a) Write a function with header [y] input value. Where: myfunction (x) where y is the output…
A: Matlab functions are created with the keyword "function". The function takes input arguments and…
Q: When it comes to overflow and underflow, what exactly is the difference, and what exactly are the…
A: Overflow and Underflow: Both faults result from a lack of space. They first appear in knowledge…
Q: Explain why SSD is faster than magnetic disks? Explain how data is read and written in the magnetic…
A: "Since you have asked multiple questions I am solving the first 2 for you If you want an answer to…
Q: Let be the discrete source on the alphabets {I, B, D, R, .} which defines a series of 5 possible…
A: Answer has been explained below:-
Q: To what end do TCP-based protocols like HTTP, SMTP, and POP3 serve?
A: Given that: HTTP, FTP, SMTP, and POP3 protocols all demand that application data be received in the…
Q: Question 7 A lto 4 De-multiplexer is represented by the following block diagram, build the…
A: Here in this question we have given a 1*4 demux and we have asked to find truth table for this and…
Q: Explain the programming language hierarchy. This hierarchy's symbol is a triangle. What gives it…
A: A programming language has a hierarchical structure is defined as follows: It is typical for more…
Q: Write a program in the Python language to find the sum of all natural numbers in the range n to 150…
A: Write a program in the Python language to find the sum of all natural numbers in the range n to 150…
Q: 4. Which of the parts of a computer execute the program instructions b. main memory a. central…
A: Question 4: The CPU which is known as Central processing is said to be the heart of the computer. A…
Q: What are the advantages and disadvantages of IPSec, as compared to alternative network security…
A: IPsec Internet protocol security is a secure network protocol that are used to encrypt the data…
Step by step
Solved in 2 steps

- 43. The time interval between adjacent bits is called the a. Word-time b. Bit-time c. Turn around time d. Slice timeGiven a bit array A = [ 0 0 1 1 0 1] on which the operations are workable:i) Can you use OR to change any desired bit of A to 1?ii) Can you use AND to change any desired bit of A to 0?iii) Can you use XOR to invert or toggle any desired bit of A?7. Add the following two 8-bit binary numbers, producing an 8-bit result. Indicate the status of the carry and overflow bits at the end of the addition by circling the appropriate choices. The space in between is only for readability. 1101 0110 + 1001 0111 -------------- Overflow? Yes or No Carry? Yes or No
- In most cases, character devices are able to transmit data at a faster rate than block devices. Is this a true or false statement?You are hired to decrypt a message that has the following binary sequence: 0100 0101 0100 1100 0100 0011 0110 1111 0110 0100 0110 1001 0100 0111 0110 1111 0100 0101 0101 0011 0011 0011 0011 0111 0011 0101 0011 0001 0011 0110 0011 0010 The message must be displayed on a 7-segment display, it is only known that the encoding is in ASCII. 1.Approach, encoding of the message and truth table. 2.Functional electronic circuit to display the message.This is computer architecture! PLEASE HELP ME FIX THE CODE AS THERE IS ERROR! # This program corrects bad data using Hamming codes # It requests the user to enter a 12-bit Hamming code and determines if it is correct or not # If correct, it displays a message to that effect. If incorrect, it displays a message # saying it was incorrect and what the correct data is (the 12-bit Hamming code) again in hex. # This program is designed to handle single bit errors only. .data prompt: .asciiz "Enter a 12-bit Hamming code: " correct_msg: .asciiz "The Hamming code is correct." incorrect_msg: .asciiz "The Hamming code is incorrect. The correct code is: " newline: .asciiz "\n" .text .globl main main: # Display prompt to enter Hamming code li $v0, 4 la $a0, prompt syscall # Read Hamming code from user li $v0, 5 syscall move $t0, $v0 # Calculate parity bits andi $t1, $t0, 0b1111 # Parity bit p1 andi $t2, $t0, 0b011001100110 # Parity bit p2…
- a) Assume 185 and 122 are unsigned 8-bit decimal integers. Calculate 185 – 122. Is there overflow, underflow, or neither? b) Assume 185 and 122 are signed 8-bit decimal integers stored in signmagnitude format. Calculate 185 + 122. Is there overflow, underflow, or neither? c) Assume 185 and 122 are signed 8-bit decimal integers stored in signmagnitude format. Calculate 185 - 122. Is there overflow, underflow, or neither?What bit pattern is stored for the following characters assuming an 8-bit byte? a. A b. a c. 8 d. % 2. What character is represented by the following bit patterns? a. 0011 0000 b. 0100 0011 c. 0111 1000 d. 0010 1010Please show all steps and assumptions for the following problem: Use Excel to introduce noise-like errors into a binary bitstream. See if you can relate the level of noise to the probability of an error. Note: Use erfc(sqrt(Eb/N0) as your target metric.
- Q.1) Mark the following statements as true or false and correct the second part if false: 1. The number (1.638125x235) expressed in IEEE 32-bit floating-point format as: 10010011 10100010000000000000000 2. The header of the CD-ROM format contains the block address and the mode byte, in which:-Mode 0 and Mode 1 : Blank data Field, Mode 2: use of an ECC. 3. When X=1.000000000000000000000000x21 and Y=1.111111111111111111111111x20, The result of (Z=X-Y) will be Z=1x2-20 without guard bits and Z=1x2-22 when adding four guard bits. 4. The simple interrupt cycle of control unit actually consists of 3 steps and 3 micro-operations. 5. In the instruction cycle sequence, after each execute cycle is a fetch cycle. 6. The Wilkes control technique is a horizontal microprogramming format. 7. After implementation Booth`s algorithm for the operation (7 * 3) the contents of registers: A=0001 and Q= 0101. 8. Double side hard disk drives have: 8 platters, and 128 sectors per track. When the size of…A random positive integer between 0 and 35767 is generated by the computer. Write aprogram which sets bits 3, 5, 8, 12 and 15 using logical operators only. You are onlyallowed to use 1 bitwise operator. Also, the bitwise operator you are choosing can only beused once. Show the originally generated number and the modified number using 16 bitrepresentation using showbits().Bit Manipulation We reviewed bitwise logical operations in C (&=AND, |=OR, ^=XOR): A = 0011 1100 B = 0000 1101 --------------------- A&B = 0000 1100 A|B = 0011 1101 A^B = 0011 0001 For the following three questions, assume: A = 1010 1010 1010 B = 0000 1111 0000 And compute the results of these bitwise operations: (A & B)& B 1 Answer: (A | B)| B 2 Answer: (A ^ B)^ B 3 Answer: We also discussed the C shift operations (shift left=<< and shift right=>>). For the following two questions, assume: C = 0001 1001 1010 And compute the results of these shift operations: 4. C >> 3 4 Answer: 5. C << 2 5 Answer:





