ownvote for incorrect code attach screen shot.
Q: Is there a gain or a disadvantage to utilizing multipurpose microcontroller pins?
A: Advantages:- The operation takes a short amount of time to complete.…
Q: Fix all the syntax errors in the following program. 1.//Program to calculate the area of circle…
A: Fixing syntax error in following java code
Q: What does copyright law say about work, such as a photograph, a diagram, a chart, or an entire…
A: Copyright: Authors have the right to govern the use of their work under copyright, with certain…
Q: Give an example of a Named Entity Recognition application. In the context of the reference…
A: Solution:: INTRODUCTION: Recognizing named things/businesses involves mostly identifying their…
Q: In what ways may cloud storage and processing improve our lives?
A: NOTE :- Below i explain the answer in my own words by which you understand it well. The cloud…
Q: Justify the requirement for business continuity methods in each situation. For one week, the local…
A: Start: Some firefighting techniques concentrate on cooling the fire to eliminate the heat required…
Q: Is it true that Data Structures and Algorithms are no longer used in the age of Machine Learning?…
A: Introduction: If you need to tackle real-world problems and create a cool product or algorithm,…
Q: The network layer protocol is required to provide packetizing services to the transport layer for…
A: Introduction The purpose of transport layer is to provide communication services between two…
Q: Computer science What is electromagnetic interference (EMI)?
A: Introduction: What is electromagnetic interference (EMI)?
Q: How do microcontrollers affect the industry?
A: Microcontrollers are utilised in products and devices that are automatically operated, such as car…
Q: How to take use of a cookie-based online authentication scheme?
A: Introduction: A web-based cookie-based authentication technique is being targeted by attackers:
Q: rogram
A: A central processing unit (CPU), additionally called a central processor, fundamental processor or…
Q: Explain the notion of Instruction Set Architecture (ISA) in detail.
A: Instruction Set Architecture (ISA): It is an abstract model of computer. It is useful in defining…
Q: are testing and what are the be
A: Below exactly is manual software testing
Q: Explain how the convergence of computers, telecommunications, and media has resulted in the…
A: Intro Disruptive Technology: Disruptive technology is one that displaces a settled technology and…
Q: In mesh topology, each device has its own topology of Multipoint connecting explain?
A: Mesh topology: A mesh topology is a network configuration in which each computer and network device…
Q: Which one is the right answer? 1. Generating alternative initial designs would most likely be done…
A:
Q: What modifications should or should not be made by an organisation in the future to improve the…
A: Introduction: In a complex information system, the information is stored in a database, which makes…
Q: What steps do you need to take to become a successful manager?
A: Successful Managers: Delegation is usually a strength of effective managers. They may delegate…
Q: Create a c++ program that ask user for a certain number and display all prime numbers from 1 to that…
A: Algorithm: for (initialExpression; testExpression; updateExpression){ // body of the…
Q: with figure the Relationship between FIVE (5) Compiler, Interpreter, Assembler, Link
A: Lets see the solution.
Q: What exactly is SDLC?Fill in the blanks with the names of their various phases.
A: SDLC stands for Software Development Life Cycle. It involves the steps that are taken in building…
Q: How does a computer's organization and design define its applicability and cost? Use an example to…
A: Introduction: Computer organization:- It's the configuration of a computer system's many hardware…
Q: Assume that your app has a layout file called activity_display.xml. What is the name of the binding…
A: what is the name of the binding class generated for this layout file if view binding is enabled for…
Q: A single individual is capable of initiating a distributed denial of service (DDoS) attack.
A: Answer:- One person can slow down a network of sites. It all depends on the methods/types of…
Q: When it comes to a cloud-based network, how do you host the services and applications?
A: Cloud computing allows us to access and store data over the internet rather than on a local hard…
Q: Convert below base7 number to base30 number format (654)base 7 = (?)base30
A: HI THEREI AM ADDING ANSWER BELOWPLEASE GO THROUGH ITTHANK YOU
Q: denial-of-ser
A: A botnet is various Internet-associated gadgets, every one of which runs at least one bots. Botnets…
Q: of using
A: A programming language is any arrangement of decides that converts strings, or graphical program…
Q: DDoS attacks may be launched by a single individual, but how do they work?
A: Intro DDoS is also known as distributed denial-of-service.
Q: This page contains a list of the five subtypes of DoS attacks.
A: Introduction: Denial of Service (Dos) attack definition A "denial of service attack" occurs when an…
Q: Describe how Google Dorks works and why it was created.
A: Introduction: Google Docs is a free web-based utility for creating, editing, and storing documents…
Q: Create an algorithm to delete all nodes in a linkedlist that have a duplicate key.
A: Algorithm : Algorithm for deleting all nodes in a LinkedList that have a duplicate key. As an…
Q: Network?
A: A virtual private network (VPN) expands a private network across a public network and empowers…
Q: using System; class Program { static void Main() { string text = "civic";…
A: Loop in C# It is used to run the loop statements for particular number of times. It is purely depend…
Q: What is the cause of diskthrashing? What can you do to lessen the impact?
A: When the system does not have enough memory: It is described as the state of a process in which the…
Q: QI/By Using the following schema, answer the following SQL queries and commands…
A: here we have given the queries for the first three subparts as per the guidelines. you can find…
Q: ebating whether to prototype before implementing. The project team is concerned about the need to…
A: Your data warehousing team is debating whether to prototype before implementing. The project team is…
Q: Create a c++ program that ask user for a certain number and display all prime numbers from 1 to that…
A: Here I have created a function named isPrime(). Inside the function, I have checked whether the…
Q: Is there anything fundamentally missing from the fundamentals of software engineering? explain?
A: Software development: Software engineering is described as a method for developing, operating, and…
Q: There are two VPN protocols listed. Describe the tunneling method used to create Virtual Private…
A: A VPN protocol is a collection of instructions or rules that govern data transfer between your…
Q: Describe how to store data in a computer's internal memory.
A: Introduction: In most computers, the hard disc drive serves as the main data storage device. It…
Q: A PRIME number is a number whose factors are one and it itself. A COMPOSITE number is a number with…
A: INTRODUCTION: Here we need to create a C program that will input a number and determine if the…
Q: In a few words, describe two well-known recommended practices for IP models. Compare these…
A: IP considerations: In today's commercial world, intellectual property has become an increasingly…
Q: It is necessary to explain how DDoS attacks use botnets and how they are built.
A: Intro The points below may be utilized to build a botnet: Prepare host systems to discover the…
Q: What are the three requirements that must be satisfied in order for a network to be successful and…
A: Introduction: Production planners decide how and where products will be made and the layout of…
Q: Various types of malware are described; Define a botnet and its operation; Define a botnet. Describe…
A: It is any program or file meant to harm a computer, network, or server known as malware. Malware is…
Q: Make a C program to input an integer. If the integer is divisible by 3 and 7, change its value so…
A: What Needs To Be Done? C Program needs to input a number and based on the inputted number it will…
Q: It is critical to understand how botnets are created and how they might be used in distributed…
A: Start: Botnets are created by infecting a large number of computers with malware (malicious…
Q: Why is it important for the network layer protocol to provide transport layer packetizing services??…
A: Introduction Why does the transport layer require packetizing services from the network layer…
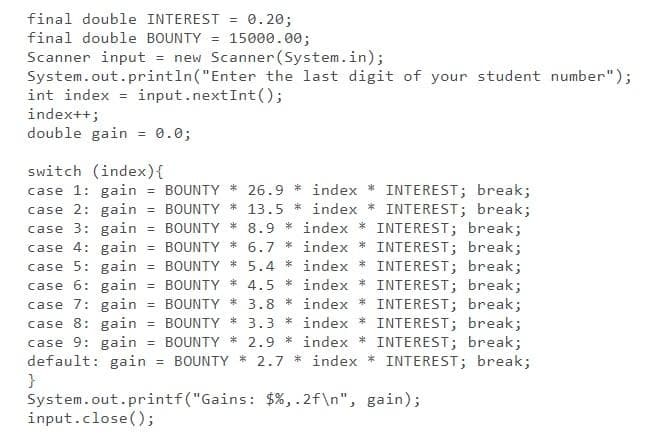
I would downvote for incorrect code attach screen shot.
Step by step
Solved in 2 steps with 1 images

- import java.util.Scanner; public class LabProgram { public static Roster getInput(){ /* Reads course title, creates a roster object with the input title. Note that */ /* the course title might have spaces as in "COP 3804" (i.e. use nextLine) */ /* reads input student information one by one, creates a student object */ /* with each input student and adds the student object to the roster object */ /* the input is formatted as in the sample input and is terminated with a "q" */ /* returns the created roster */ /* Type your code here */ } public static void main(String[] args) { Roster course = getInput(); course.display(); course.dislayScores(); }} public class Student { String id; int score; public Student(String id, int score) { /* Student Employee */ /* Type your code here */ } public String getID() { /* returns student's id */…/* * rotate4 - Rotate x to the left by 4 * Examples: rotate4(0x87654321) = 0x76543218 * Legal ops: ~ & ^ | + << >> ! * Max ops: 10 * Rating: 2 */int rotate4(int u) { return 2;} Do not use any control constructs such as if, do, while, for, switch, etc.Write a unit test for addInventory(), which has an error. Call redSweater.addInventory() with parameter sweaterShipment. Print the shown error if the subsequent quantity is incorrect. Sample output for failed unit test given initial quantity is 10 and sweaterShipment is 50: Beginning tests. UNIT TEST FAILED: addInventory() Tests complete. // ===== Code from file InventoryTag.java =====public class InventoryTag {private int quantityRemaining; public InventoryTag() {quantityRemaining = 0;} public int getQuantityRemaining() {return quantityRemaining;} public void addInventory(int numItems) {if (numItems > 10) {quantityRemaining = quantityRemaining + numItems;}}}// ===== end ===== // ===== Code from file CallInventoryTag.java =====import java.util.Scanner; public class CallInventoryTag {public static void main(String [] args) {Scanner scnr = new Scanner(System.in);InventoryTag redSweater = new InventoryTag();int sweaterShipment;int sweaterInventoryBefore; sweaterInventoryBefore =…
- Java - Encapsulation Create a class Point with attributes x and y which are both integers. Create getters and setters for these attributes and implement the following methods: 1. calculateDistance() - calculates the distance from the origin to the point. Returns a double, formula is sqrt(x^2 + y^2) 2. printCoordinates() - prints "(x,y)" Ask for user inputs for x and y. Use the methods printCoordinates() and calculateDistance() respectively. Inputs 1. X 2. Y Sample Output Enter x: 20 Enter y: 15 (20,15) 25.00import java.util.Scanner;/** This program computes the time required to double an investment with an annual contribution.*/public class DoubleInvestment{ public static void main(String[] args) { final double RATE = 5; final double INITIAL_BALANCE = 10000; final double TARGET = 2 * INITIAL_BALANCE; Scanner in = new Scanner(System.in); System.out.print("Annual contribution: "); double contribution = in.nextDouble(); double balance = INITIAL_BALANCE; int year = 0; // TODO: Add annual contribution, but not in year 0 do { year++; double interest = balance*(RATE/100); balance = (balance+contribution+interest); } while(balance< TARGET); System.out.println("Year: " + year); System.out.printf("Balance: %.2f%n", balance); }}2.1.3: Basic if-else. Jump to level 1 Write an if-else statement for the following: If userTickets is less than 8, execute awardPoints = 1. Else, execute awardPoints = userTickets. Ex: If userTickets is 3, then awardPoints = 1. import java.util.Scanner; public class TicketCounter { public static void main (String [] args) { int awardPoints; int userTickets; Scanner scnr = new Scanner(System.in); userTickets = scnr.nextInt(); // Program will be tested with values: 5, 6, 7, 8. if (userTickets < 8) { awardPoints = 1; System.out.println(awardPoints); } else { System.out.println(awardPoints); }}
- import java.util.Scanner; public class LabProgram { public static void main(String args[]) { Scanner scnr = new Scanner(System.in); int credits; int seed; GVDie die1, die2; die1 = new GVDie(); die2 = new GVDie(); // Read random seed to support testing (do not alter) seed = scnr.nextInt(); die1.setSeed(seed); // Read starting credits credits = scnr.nextInt(); int rounds = 0; while (credits > 0) { // Step 1: Roll both dice die1.roll(); die2.roll(); int total = die1.getValue() + die2.getValue(); if (total == 7 || total == 11) { // Player wins one credit credits++; } else if (total == 2 || total == 3 || total == 12) { // Player loses one credit credits--; } else { // Set the goal for future rolls int goal = total;…import java.util.Scanner;public class LabProgram { public static void main(String args[]) { Scanner scnr = new Scanner(System.in); int credits; int seed; GVDie die1, die2; die1 = new GVDie(); die2 = new GVDie(); // Read random seed to support testing (do not alter) seed = scnr.nextInt(); die1.setSeed(seed); // Read starting credits credits = scnr.nextInt(); int rounds = 0; while (credits > 0) { // Step 1: Roll both dice die1.roll(); die2.roll(); int total = die1.getValue() + die2.getValue(); if (total == 7 || total == 11) { // Player wins one credit credits++; // UPDATE - print the dice total here System.out.println("Dice total: " + total); //UPDATE - break the loop and end the round break; } else if (total == 2 ||…import java.util.Scanner; public class sample { public static double totalProfit = 0.00; public static double totalTax = 0.00; static void ProfitandTax(double S , double E , int count){ double Tax = (S * 30.00)/100.00; /* Tax is 30% of sales and it is also considered as expenses of business so this will be a type of expenses */ double totalExpense = (E + Tax ); double Profit = (S - totalExpense); // Profit is given by sales subtracted by expenses System.out.println("Profit for " + count + " branch is : " + Profit); System.out.println("Tax for " + count + " branch is : " + Tax); totalProfit += Profit; totalTax += Tax; } public static void main(String[] args){ Scanner sc = new Scanner(http://System.in); System.out.println("Enter no of branches you have "); int k = sc.nextInt(); for(int i=0;i< k ;i++){ System.out.println("Enter Sales for " + (i+1 )+ " branch " ); double S = sc.nextDouble(); System.out.println("Enter Expenses for " + (i+1) + " branch " ); double E = sc.nextDouble();…
- Please Help Solve, Thank You! 3.25.2: Basic if-else. Write an if-else statement for the following: If userTickets is not equal to 6, execute awardPoints = 10. Else, execute awardPoints = userTickets. Ex: If userTickets is 14, then awardPoints = 10. import java.util.Scanner; public class TicketCounter { public static void main (String [] args) { int awardPoints; int userTickets; Scanner scnr = new Scanner(System.in); userTickets = scnr.nextInt(); // Program will be tested with values: 5, 6, 7, 8. /* Your code goes here */ System.out.println(awardPoints); }}def new_line(): print('.') def three_lines(): new_line() new_line() new_line() def nine_lines(): three_lines() three_lines() three_lines() def clearScreen(): print('Printing nine lines') nine_lines() print('Printing nine lines') nine_lines() print('Printing three lines') three_lines() print('Printing three lines') three_lines() print('Printing new line') new_line() print('Line from main function')print('Calling clearScreen function') clearScreen() Assessment The following items will be used in the grading rubric for this assignment. Make sure that you have addressed each item in your assignment. Does the assignment implement new_line, three_lines, nine_lines, and clear_screen functions, as well as a main section of the program which calls the functions? Does the assignment demonstrate the use of nested function calls? Does the assignment produce the appropriate output when executed? The output should be recorded in a text file, a…Java Program Fix this Rock, Paper and scissor program so I can upload it to Hypergrade and it can pass all the test cases. Here is the program: import java.util.Random;import java.util.Scanner;public class RockPaperScissors { public static void main(String[] args) { if (args.length != 1) { System.out.println("Please provide a seed as a command line argument."); return; } long seed = Long.parseLong(args[0]); Random random = new Random(seed); Scanner scanner = new Scanner(System.in); System.out.println("Enter 1 for rock, 2 for paper, and 3 for scissors."); do { int computerChoice = random.nextInt(3); int userChoice = getUserChoice(scanner); if (userChoice == -1) { continue; } System.out.println("Your choice: " + choiceToString(userChoice) + ". Computer choice: " + choiceToString(computerChoice) + "."); int result =…

