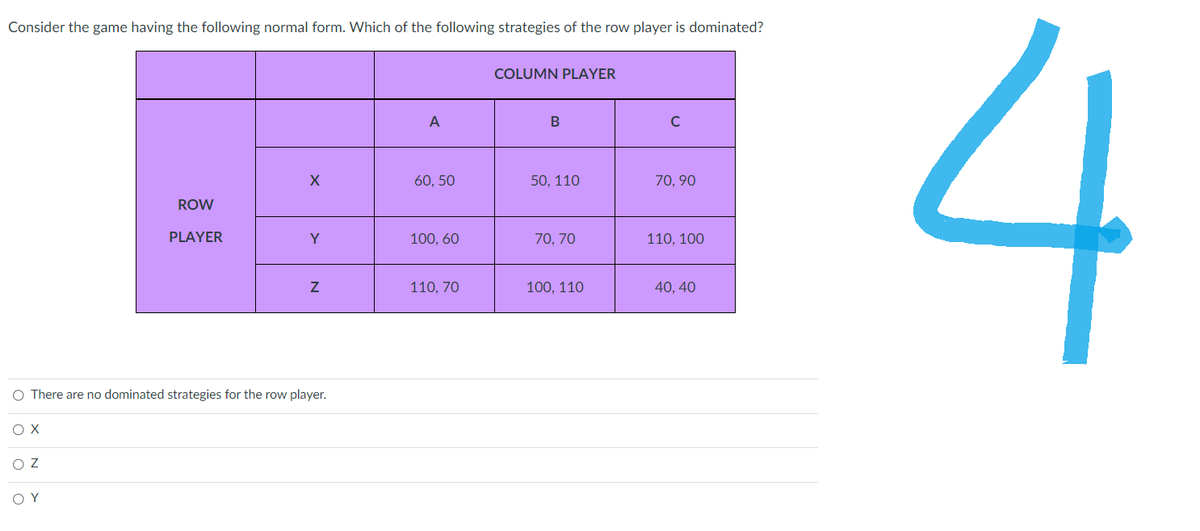
Consider the game having the following normal form. Which of the following strategies of the row player is dominated? ox ROW PLAYER OZ ΟΥ X Y O There are no dominated strategies for the row player. N A 60, 50 100, 60 110, 70 COLUMN PLAYER B 50, 110 70, 70 100, 110 с 70,90 110, 100 40, 40
Q: Part (2) Write a Java application that asks the user to enter the length and width of a room and the…
A: Programs : Note: To better understand the code please see the screenshot of the code at the end of…
Q: Why is it vital to implement a destructor in a class?
A: When a class object and its members are destroyed, destructors are often used to deal locate memory…
Q: Which of the following is true about functions with a return value? OOnly strings may be returned…
A: Functions are set of instructions enclosed within curly braces that aims to perform a specific task…
Q: Removing Complex Operands Which of the following are atomic expressions? 1 True 5+6 Perform the…
A: Below is the answer to above questions. An atomic expression is the most basic sort of expression…
Q: A binary tree that stores the sizes of subtrees in nodes
A: Answer - A binary tree that stores the sizes of subtrees in nodes hence the option A is true
Q: Starting from an empty tree, construct an ordinary (non-self-balancing) Binary Search Tree after…
A: The construction of non-self-balancing, Binary Search Tree with the insertion of given values would…
Q: List and discuss ten AI technologies used for educational system transformation.
A: Introduction: Artificial intelligence is broadly used to give customized suggestions to individuals,…
Q: For a resolution of 0.032 V and an analog sample voltage of 4.030 V, complete the table below:…
A: Below I have provided the handwritten solution of the given question
Q: Explain the different factors affecting the processing speed of CPU.
A:
Q: Management continually wants to know the current financial picture of the company, including profit…
A: The question has been answered in step2
Q: What basic traits and qualities make up a descriptive model?
A: Introduction A descriptive model is an interaction that portrays genuine occasions and the…
Q: Given: MIN-MAX Tree. Using the Alpha-Beta Pruning in the given MIN-MAX Tree below, how many branches…
A: import java.io.*; public class GFG { // Initial values of// Alpha and Betastatic int MAX =…
Q: Aside from social networking blogs, you'll learn about cloud computing and a slew of other relevant…
A: Answer: Cloud computing connection and remote computing are future technologies that have roots in…
Q: Is there a risk to governance when moving from on-premise servers to an IaaS model?
A:
Q: Explain the following terms: Cursor, Embedded SQL, JDBC, SQLJ, stored procedure.
A: Here we have given brief explanation for the following terms, cursor, Embedded SQL, JDBC, SQLJ,…
Q: The post-order traversal of a binary tree is O P Q R S T. Then possible pre-order traversal will be…
A: The post-order traversal of a binary tree is O P Q R S T. Then possible pre-order traversal will be…
Q: What does a motion sensor mean in terms of fitness and health? summarize the main features and each…
A: A motion sensor is a gadget that detects motion in a specific region and uses that information to…
Q: What exactly is the nature of the transmission problem? What are the most prevalent causes of…
A: Introduction: If your automobile has transmission problems, it is critical to discover them early…
Q: In what ways are DNS servers linked to forensic investigation of the Internet's network…
A: DNS converts domain names to IP addresses. It is sometimes called "DNS." "Domain Name Server" is…
Q: On a computer Windows Server operating system, what kind of firewall software is installed?
A: Introduction: Firewalls act as a physical barrier between the outside world and a computer system,…
Q: If you want to learn more about cloud computing and other related issues, it's a good idea to read…
A: DEFINITION: Sites that give data or information on a wide range of subjects include social…
Q: What are double and single threaded trees? a) when both left, right nodes are having null pointers…
A: Answer: a Explanation: They are properties of double and single threaded binary trees respectively.
Q: What exactly does the term "reduced instruction set computer" mean?
A: Introduction: A system with a more limited instruction set: A Reduced Instruction Set Computer…
Q: Without systems analysis, there will be no system development, inadvertently without a proper system…
A: In this question we have to identify and explain the four primary activities that should be carried…
Q: What use does the Toolbox serve in the Visual Studio setting?
A: Toolbox: When the cursor is moved over the Toolbox icon on the left side of the Visual Studio IDE,…
Q: you will take the output from the first task and write an algorithm and matching code to perform the…
A: ALGORITHM TASK 1: STEP 1 : GET THE LIST OF LETTER GRADES IN STEP 1. STEP 2 : GET THE PI NUMBER IN…
Q: It is possible for a computer system to generate and process data in several ways. Everything has to…
A: Computer System: An integrated group of the devices known as a computer system may input, output,…
Q: Question 5 Given: f(x) = 3x³ is the syntax below valid? +5 >>£ - [3 0 51 A True B False
A: Matlab: Matlab stands for MATrix LABoratory. It is used to perform engineering and scientific…
Q: How well do you comprehend the TCSEC orange book?
A: Introduction: computer protection Fundamentally, computer security is the protection of computer…
Q: A binary tree that stores the sizes of subtrees in nodes
A: Answer - A bianry tree that stores the size of subtrees in nodes hence the opotion is A
Q: Since they are now more reasonably priced, what research avenues do motion sensors for health and…
A: Most people focus on and devote more attention to their health and fitness these days. To get in…
Q: Why is it beneficial to use a number of different programming languages?
A: The answer for the above mentioned question is given in the following steps for your reference.
Q: Code Segment struct node { int val; struct node *Left; struct node *Right; } }; void tree_walk…
A: 1 st number in the tree-walk sequence is 5. 1 st number in the tree-walk sequence is 12. 1 st number…
Q: Question 9 a-[1234]: b-10456): c-deconv(a,b) does this code work properly? A True B False
A:
Q: You are given a Point class, which defines a point on a 2D grid (x, y). The program creates a Point…
A: Here we have modified the code according to your requirement. You can find the solution in step 2.
Q: Do you want to learn more about social networking blogs, cloud computing, and a range of other…
A: Given: By reading blogs, you may find out more about cloud computing, social networking, and other…
Q: Under which conditions does: a) A cycle-free graph have an Hamiltonian circuit? b) A complete graph…
A: Euler:- 1) A graph is Euler if and only if the degree of every vertex is even.
Q: Ex. Described each line and write the equation of PA for the follow assembly code: 01 org 100h 02…
A:
Q: How does a server know that one of the distant objects he has made available to clients is no longer…
A: SOLUTION: The acronym RMI (Remote Method Invocation) stands for this technique. It is a feature that…
Q: It is feasible to recognise each individual component of a high-level programming language due to…
A: Given: The act of giving the computer with data and/or instructions is referred to as the "input"…
Q: What part do knowledge workers play in organising and acquiring knowledge?
A: Introduction: Concerning Knowledge Workers Information work may be distinguished from other sorts of…
Q: What is the difference between a pipelined and non-pipelined processor's clock cycle time?
A: Introduction: Clock cycle times of a pipeline: The clock cycle time should be adequate to…
Q: An Artificial Neural Network contains 2 neurons in the Input Layer (called neuron 0 and neuron 1), 2…
A: Solution: output of neuron 2 is 0.00061 output of neuron 3 is 0.87 output of neuron 4 is 0.139
Q: write alogrithms for the following blocks of code... 2nd Block: int main() { //-------defining…
A: - We have to create the algorithm from the code provided.
Q: Complete in Pseudocode Declare an array called ‘numbers’ that will contain the following…
A: The above question is solved in step 2 :-
Q: What two things separate the static-chain technique for static scoped languages from the deep access…
A: Answer: When implementing languages with dynamic scope, the shallow access technique: Access names…
Q: If L is the set of all strings over Σ = {a,b), which has the form xby, where x is any string whose…
A: answer starts from step 2
Q: Consider the Postfix Expression below. Each token below is separated by a space. And each number is…
A: In this question we have to Evaluate the postfix expression Where we need to answer question . Let's…
Q: Briefly Describe the clocking system.
A: Clocking methodology => When data in a state element is fair and stable in relation to the…
Q: Consider the significance of wireless networks in underdeveloped nations today. Wireless technology…
A: Introduction The wireless network is widespread communication nowadays since smartphones and the…
no need for a complete solution. I just need a simple solution with the correct answer. downvote if it is incorrect. skip if you already did this or else get a downvote.
Step by step
Solved in 2 steps

- The Josephus problem is the following game: N people, numbered 1 to N, are sitting in a circle. Starting at person 1, a hot potato is passed. After M passes, the person holding the hot potato is eliminated, the circle closes ranks, and the game continues with the person who was sitting after the eliminated person picking up the hot potato. The last remaining person wins. Thus, if M = 0 and N = 5, players are eliminated in order, and player 5 wins. If M = 1 and N = 5, the order of elimination is 2, 4, 1, 5. Write a C program to solve the Josephus problem for general values of M and N. Try to make your program as efficient as possible. Make sure you dispose of cells. What is the running time of your program? If M = 1, what is the running time of your program? How is the actual speed affected by the delete routine for large values of N (N > 100,000)? ps. provide a screenshot of output, thankssConsider a game in which two players take turns removing any positive number of matches they want from one of two piles of matches. The player who removes the last match wins the game. Show that if the two piles contain the same number of matches initially, the second player can always guarantee a win.You have made it to the final round of “Let’s Make aDeal.” You know that there is $1 million behind either door1, door 2, or door 3. It is equally likely that the prize isbehind any of the three doors. The two doors without a prizehave nothing behind them. You randomly choose door 2.Before you see whether the prize is behind door 2, Montychooses to open a door that has no prize behind it. For thesake of definiteness, suppose that before door 2 is opened,Monty reveals that there is no prize behind door 3. You nowhave the opportunity to switch and choose door 1. Shouldyou switch?Use a spreadsheet to simulate this situation 400 times.For each “trial” use an @Risk function to generate the doorbehind which the prize lies. Then use another @Riskfunction to generate the door that Monty will open. Assumethat Monty plays as follows: Monty knows where the prizeis and will open an empty door, but he cannot open door 2.If the prize is really behind door 2, Monty is equally likelyto open door 1 or…
- Consider the following scenario:A high school has 1000 students and 1000 lockers, one locker for each student. On the first day of school, the principal plays the following game: She asks the first student to open all the lockers. She then asks the second student to close all the even-numbered lockers. The third student is asked to check every third locker. If it is open, the student closes it; if it is closed, thestudent opens it. The fourth student is asked to check every fourth locker. If it is open, the student closes it; if it is closed, the student opens it. The remaining students continue this game. In general, the nth student checks every nth locker. If it is open, the student closes it; if it is closed, the student opens it. After all the students have taken turns, some of the lockers are open and some are closed. The program see in the photo, when ran, should ask the user to enter the number of lockers in the school. The program will output the number of lockers and the…A spinner with three equal sections is being used in a game. One section is labeled “0 points,” and two sections are labeled “2 points.” A player can decide not to spin the spinner and score 1 point. Each player gets one turn, and the player with the higher score wins; in case of a tie, the winner is decided by one flip of a fair coin. Alex takes his turn first. Eddie, knowing Alex’s score, takes his turn next. If both players use strategies that maximize their winning probabilities, what is the probability that Alex wins? a 1/3 b 1/2 c 2/3 d 4/9You must have played this 2 player game, in which there are 9 holes where one player mark Cross and the otherPlayer places Ovals in the game and there are multiple situations at the end of the game in which are as follows.1. Player 1 wins if he became able to mark 3 Cross in any of the row.2. Player 1 wins if he became able to mark 3 Cross in any of the column.3. Player 1 wins if he became able to mark 3 Cross in any of the diagonals of the holes.4. Player 2 wins if he became able to mark 3 Ovals in any of the row.5. Player 2 wins if he became able to mark 3 Ovals in any of the column.6. Player 2 wins if he became able to mark 3 Ovals in any of the diagonals of the holes.7. Match is drawn if all holes are filled but no one could win.Now what is requirement by your side, you have to write a Java program described below1. Create 9 variables of type integer with names given below, which will act like the holes of the game.a. hole1, hole2, hole3, hole4, hole5, hole6, hole7, hole8 and hole9…
- There are four medals (Gold, Silver, Bronze and Wood) on a table, but they are all wrapped with dark wrapping paper, such that it is impossible to distinguish them. You would like to find the gold medal.The game starts as follows. You pick one medal without unwrapping it, and then the game host unwraps one of the remaining medals and reveals that it is a silver medal. (Assume here that the host unwraps a medal with equal probability, but knowing where the gold medal was and avoiding unwrapping the gold medal if still on the table, to keep the game interesting to watch until the end.)You have now three medals left to unwrap (one in your hand, two on the table). At this point, the host gives you the option to change your mind and swap your medal for one of the two left on the table. What would you do at this point? Would you keep your medal, or swap it with one of the two medals left on the table? If so, which one? Hints: Find the solution by using Bayes’ theorem, calculating all the…Imagine playing a number guessing game. A side is a number from 0 to Nhe's holding it, and the other side is trying to find that number by taking turns guessing. Number-holding side estimatehe has to offer one of the following three options in response to the party that did it:1-Your guess is correct, you found the number I kept (Game Over).2-Your estimate is wrong, but you are closer to the correct estimate than the previous estimate.3-the wrong estimate and the correct estimate are further away than the previous estimate.To find the estimated number in an environment where all the information is these, astrategy will be followed: Make a prediction (N/2) from the exact middle of N with 1 Begin:Find out the answer to your guess. [answer=answer_ogren (guess)]If the answer is equal to 1, the game is over, you can leave.If the answer is equal to 2, you are going in the right direction, keep the forecast direction;If you're heading for small numbers, the new N is now N/2.Make a guess…A two-person zero-sum game is given by the matrix A := −2 −3 2 −1, 2 1 −5 2, 0 −4 4 −3, 1 −2 3 0 . Find a pair of optimal strategies for this game as well as the value of the game.
- The game ping has two rounds. Player A goes first. Let mA 1 denote his first move. Player B goes next. Let mB 1 denote his move. Then player A goes mA 2 , and player B goes mB 2 . The relation AWins(mA 1 , mB 1 , mA 2 , mB 2 ) is true iff player A wins with these moves. 1. Use universal and existential quantifiers to express the fact that player A has a strategy with which he wins no matter what player B does. Use mA 1 , mB 1 , mA 2 , mB 2 as variables. 2. What steps are required in the prover–adversary technique to prove this statement? 3. What is the negation of the above statement in standard form? 4. What steps are required in the prover–adversary technique to prove this negated statement?Each day, there are two strategies available to two bakers, Tim and Horton: sell cakes or sell pastries. They cannot do both in any one day. If both sell cakes, Tim will earn an additional $500 and Horton will lose $500. If Tim sells cakes and Horton sells pastries, Tim gains $100 and Horton loses $100. If Horton sells cakes and Tim sells pastries, Tim loses $400 and Horton gains $400. If both sell pastries, Tim gains $400 and Horton loses $400. What will be the outcome if both bakers correctly use game theory? a.None of these outcomes is correct b.Tim will gain $250, on average, each day c.Tim will gain $300, on average, each day d.Tim will gain $100, on average, each day e.Tim will gain $200, on average, each dayConsider the following scenario: A high school has 1000 students and 1000 lockers, one locker for each student. On the first day of school, the principal plays the following game: She asks the first student to open all the lockers. She then asks the second student to close all the even-numbered lockers. The third student is asked to check every third locker. If it is open, the student closes it; if it is closed, the student opens it. The fourth student is asked to check every fourth locker. If it is open, the student closes it; if it is closed, the student opens it. The remaining students continue this game. In general, the nth student checks every nth locker. If it is open, the student closes it; if it is closed, the student opens it. After all the students have taken turns, some of the lockers are open and some are closed. The program below, when ran, will prompt the user to enter the number of lockers in the school. After the game is over, the program will output the number of…

