port matplolib TRANSCRIPT Name English:
Q: What does it mean to "interrupt" someone? What kinds of interruptions are there? What causes…
A: Interrupts: External devices, usually I/O devices, provide interrupt signals to the CPU. They…
Q: Name at least three current intellectual property challenges faced by IT managers and explain how…
A: Information Technology: IT(Information technology) is the creation, processing, storage, security,…
Q: Repetition constructs should be discussed. Describe each one in detail with an example.
A: Repetition constructs, or loops, are used when a program: Loops, or repetition constructions, are…
Q: There is a distinction between information literacy theory and information literacy model. And how…
A: Information theory : A hypothesis is a broad statement that tries to explain something. On the other…
Q: What is the purpose of this talk on CSS and forms?
A: Cascading Style Sheets: CSS defines how HTML elements appear on screen, paper, or other media. CSS…
Q: Is it possible to conduct an information system development project without doing a literature…
A: justification: In the field of software development, software development models refer to the many…
Q: Discuss the many types of protocols and why they are necessary. (Information technology)
A: Transmission Control Protocol (TCP): TCP is a popular communication protocol used for network…
Q: The CPU suspends the current process to deal with an interrupt. Interrupt service is what it's known…
A: There are several steps you can take if an error occurs that causes process instances to be halted.
Q: O What Is The Weakness Of Matlab?
A: WEAKNESS of MATLAB There are two major disadvantage of MATLAB programming language: Interpreted…
Q: Python Modify the code to find the remainder of num when divided by 2 num = int(input("Enter a…
A: Task : Given the code in python. The task is to complete the code.
Q: Why would you put two power supply in a mission-critical server?
A: Introduction: In mission-critical situations, using servers with twin power sources is standard…
Q: Convert NFA to DFA: 1. 2
A:
Q: Give two benefits of a SoC.
A: SoC: SoC is synonymous with a Chip System. It is a microchip that is the whole device, i.e. it is…
Q: What are the two sorts of software?
A: The answer is given below.
Q: Which RAID levels perform best?
A: RAID: RAID stands for redundant array of independent discs in its full form. It's a storage solution…
Q: Don't have to have to had to do you have to don't think you should 1- I . Work very long hours 2-…
A: The answer is given below.
Q: Which MS-DOS function stops a program and leaves a portion of the program in memory?
A: Which MS-DOS function stops a program and leaves a portion of the program in memory?
Q: In terms of information literacy, what is phenemenographic theory?
A: The Phenomenography: Phenomenography was created in the late 1970s by a group of educational…
Q: How many users (100,000-500,000) can be accommodated by a file-server, client- server, or…
A: A client-server architecture consists of a client and a server. The client is the one who requests…
Q: What is the difference between computer architecture and computer organisation?
A: Please refer below for your reference: difference between computer architecture and computer…
Q: What are the difficulties associated with implementing mobile technology? Are the savings comparable…
A: What are the difficulties associated with implementing mobile technology? Are the savings comparable…
Q: Discuss any two issues that current information systems are dealing with.
A: Culture of MIS Management information systems are, on the surface, all about business.They gather…
Q: In the context of an information system, what is the link between the terms data, information, and…
A: Data are stored Information. To get the Information which is in data you need to be human. A…
Q: summarize an essay on top management support for successful IT projects. Your summary should include…
A: Management at the top of the hierarchy Generally speaking, "Top Management" refers to one or group…
Q: What is a hybrid RAID?
A: institution: To make a RAID array, the goal is to mix output and size while keeping overhead low…
Q: JAVA PROGRAMMING Write a generic printArray shown in the sample below. Array contains: ....
A: An Iterator is an object that can be used to loop through collections, like ArrayList and HashSet.
Q: How does the CPU restart execution from where it left off before the interrupt was triggered, after…
A: institution: Your operating system sends an ACPI instruction to the computer at the end of the…
Q: B) Write A Matlab Code To Generate Row Vector At Range (0 5) With (11 Elements) And Then: (Chose 5…
A: Hello student Greetings Hope you are doing great. As per our policy guidelines, in case of multiple…
Q: Question 1: Encoding branches & immediates We want to design a new K-format instruction for a…
A: Here i explain each point: ========================================================================…
Q: What is the difference between an interruption and a pause? Explain why no hardware disruptions are…
A: Introduction: Interrupt An interrupt signal is delivered to the processor to terminate the current…
Q: Asymmetric and symmetric encryption vary in what ways?
A: Asymmetric cryptography is often referred to as public-key cryptography.
Q: Which is the correct statement about an icon bar inside the menu bar? Choose an answer A Provides…
A: The main concept is to find out the functionality of the icon bar of the menu bar of the emacs…
Q: JAVA PROGRAMMING Write a test program that inputs, sorts, outputs Integer and Float. And call the…
A: Answer
Q: Why do active attacks pose a greater threat than passive attacks? Use real-ife examples to back up…
A: Why do active attacks pose a greater than passive attacks? Active attacks pose a greater threat than…
Q: There are ten bits in the instructions and three in the address fields of a computer instruction…
A: Given an instruction format with a 10 bit instruction length and a 3 bit address field size. With…
Q: How can risk be assessed? How do risk assessments work? IT Governance, 6th Edition Calder and…
A: Probability of impact and impact of the event called as risk. Risk can be overcome through risk…
Q: Flash memory, DVD-RW, ROM, hard drive, and CPU are all components of the Von Neumann paradigm.
A: Von Neumann: In 1946, John von Neumann proposed the Von Neumann Model, a computer architecture.…
Q: What kind of operating system is most often used on portable computers?
A: Statement: A portable computer is a computer that can be easily moved from one location to another…
Q: This is the situation because current computers are so powerful. Does anybody have evidence that…
A: Educational shift: The most important learning challenge is the relatively recent educational…
Q: How many orderings of A, B, C, D contain CB.
A: In this question, we have to order A, B, C and D and find out how many orders contains CB.
Q: What does the term "embedded" mean?
A: Origination: to encase tightly in, as if in a matrix, fossils embedded in stone b: to include…
Q: In what situations do hardware and software interruptions come into play, and how do they work…
A: Interrupt: An interrupt is a computer signal or a circuit that signals the computer to stop running…
Q: Create a flowchart or pseudocode for a software that takes three numbers from the user and shows a…
A: 3 numbers pseudocode: Step 1: Declare 5 variables as integers (N1, N2, N3, and Sum) and floats…
Q: Give two examples of how asymmetric and symmetric could be put to use. How is asymmetric encryption…
A: Uses of asymmetric encryption: NIST came up with the digital signature standard, which is in FIPS…
Q: Question 1. Transmit the character "A" using the TTL UART communication. Explain in detail all the…
A:
Q: When it comes to encryption, what are the fundamental distinctions between symmetric and asymmetric…
A: According to the question the symmetric encryption is that conventional method of the encryption and…
Q: Write a script in python that generate random number in time interval and run the script on…
A:
Q: Example 2: Using shift and arithmetic instructions, write the MIPS instructions to multiply $10 by…
A: "Since you have asked multiple question, we will solve the first question for you. If you want any…
Q: The New Telephone Company has the following rate structure for long a. The regular rate for a call…
A: As not mentioned I have solved the question in C++ language Code:…
Q: Answer the following questions with true or false and provide a brief justification for your choice:…
A: The justification: Justification arguments are offered in support of their decision. Something that…
Use Tkinter Design.
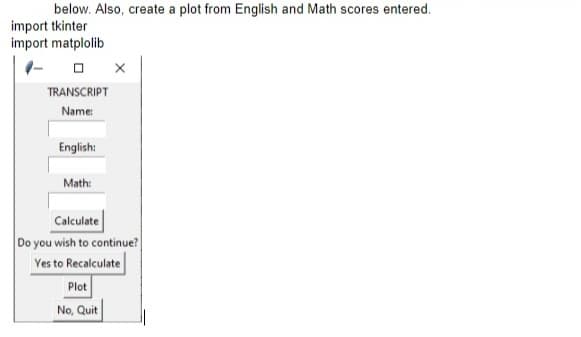
Step by step
Solved in 4 steps with 3 images

- Please answer the correct option and its reasoning. int loc; String str = "The cow jumped over the moon."; loc = str.indexOf("ow"); What is the value of loc? 1. 5 2. 6 3. 4 4. 7Add the purple code to your Main Code Section (type it by hand if you get weird errors). It will call the object’s monitorLevels() method, which we will create in this sprint: userInput = 99while userInput != 0:checkerObj.displayList()userInput = checkerObj.displayMenu()if(userInput == 1):checkerObj.addLevel()checkerObj.writeLevelsToFile() # Write levelsList to LevelsFileelif(userInput == 2):checkerObj.removeLevel()checkerObj.writeLevelsToFile() # Write levelsList to LevelsFileelif(userInput == 3):checkerObj.removeAllLevels()checkerObj.writeLevelsToFile() # Write levelsList to LevelsFileelif(userInput == 4):checkerObj.updateMenuPrice() elif(userInput == 5):userInput = 0 # prevent the app from continuing if the user pressed Ctrl+C to stop itcheckerObj.monitorLevels()Create a simple guessing game, similar to Hangman, in which the user guessesletters and then attempts to guess a partially hidden phrase. Display a phrase inwhich some of the letters are replaced by asterisks: for example, G* T*** (for GoTeam). Each time the user guesses a letter, either place the letter in the correctspot (or spots) in the phrase and display it again or tell the user the guessed letteris not in the phrase. Display a congratulatory message when the entire correctphrase has been deduced. Save the game as SecretPhrase.java. In the nextchapter, you will modify this program so that instead of presenting the user withthe same phrase every time the game is played, the program randomly selects thephrase from a list of phrases. Professor's note: "HINT on Lab #4 : Be sure to check for UPPER & LOWER Case entries from the User when they enter guessed characters for your phrase."
- If, after the following JavaScript code executes, the value of toppings is ["cheese", "mushrooms", "peppers", "sauce"], what belongs in the blank?let toppings = ["sauce", "cheese", "mushrooms"];toppings.pop();_____toppings.sort(); Question options: A toppings.push("peppers"); B toppings.push("sauce", "peppers"); C toppings.unshift("sauce", "peppers"); D toppings.push("mushrooms", "peppers");please help!! (with a screenshot of the code for this, not typed on here, because it gives me errors) JavaCan you please answer the following question? The program is JavaScript and needs to look exactly like the example attached. Thanks!
- Remove and print green in the list by using the pop() method with the list given below: colors = ["navy", "white", "red", "black", "green", "blue", "red"] Just make sure to precisely match the output format below.Write your code in the ANSWER area provided below (must include comments if using code is not covered in the course). Example OutputgreenUsing Java , please provide a CourseInterFace Class in which the user can click multiple interactive buttons with courses. Dashboard Button one will be "Math101.01". Dashboard Button 2 will be named "MATH211.08". Dashboard Button 3 will be named "MATH 267"Consider the following code. Replace the tags _??1_ and _??2_, respectively, by filling in the text fields below, such that the method main() prints the following: GORGONZOLA blue Italy (see image)
- Input a number n and print out n lines of text in the pattern below, shown for example n = 5 * * * * 1 * * * 2 1 * * 3 2 1 * 4 3 2 1 5 4 3 2 1 There is exactly one space between numbe4rs, there is no space at the end of each line, and each line ends with a newline. The first two tests will ignore the whitespace.Using NetBeans, write a program that first asks the user to enter three real numbers using GUI input. Print the sum if all three numbers are positive, print the product of the two positive numbers if only one is negative - use a nested if. Then, ask the user to enter two real numbers from the console. If both numbers are negative, print the quotient.All output should be to a dialog and the console - console output must be done using printf and format specifiers. Use meaningful variable names, informative prompts and label your output. Write a method getFloat to ask for the real numbers. This should be similar to the method getInt above. Good program structure, indentation, a heading and comments are required. Points will be deducted for any program not meeting the requirements. You must indent you code and follow java conventions. Only do what is asked for. That includes methods. Only do the methods that are specified and no packages.#Write your class code here using python word = "CANCEL"spaces = 10border = 'x'b1 = buttons(word, spaces, border)print("=======================================================")b2 = buttons("Notify",3, '!')print("=======================================================")b3 = buttons('SAVE PROGRESS', 5, '$')



