probability density
Fundamentals of Information Systems
9th Edition
ISBN:9781337097536
Author:Ralph Stair, George Reynolds
Publisher:Ralph Stair, George Reynolds
Chapter7: Knowledge Management And Specialized Information Systems
Section: Chapter Questions
Problem 3DQ
Related questions
Question
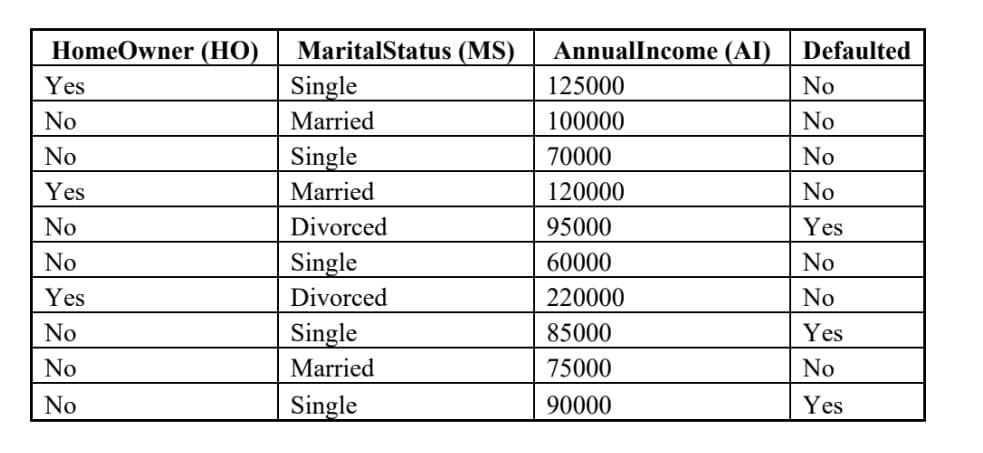
Naive Bayes Classifier) Please show the detailed process of classifying the test instance X = (HM = No, MS = Divorced,
For the continuous attribute AnnualIncome, you may use discretization to convert the attribute as binary attribute by setting threshold 91000 or use probability density estimation to estimate the conditional probabilities.
Transcribed Image Text:HomeOwner (HO)
Yes
No
No
Yes
No
No
Yes
No
No
No
MaritalStatus (MS)
Single
Married
Single
Married
Divorced
Single
Divorced
Single
Married
Single
AnnualIncome (AI)
125000
100000
70000
120000
95000
60000
220000
85000
75000
90000
Defaulted
No
No
No
No
Yes
No
No
Yes
No
Yes
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 3 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Fundamentals of Information Systems
Computer Science
ISBN:
9781337097536
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781305971776
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Fundamentals of Information Systems
Computer Science
ISBN:
9781337097536
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning

Principles of Information Systems (MindTap Course…
Computer Science
ISBN:
9781305971776
Author:
Ralph Stair, George Reynolds
Publisher:
Cengage Learning