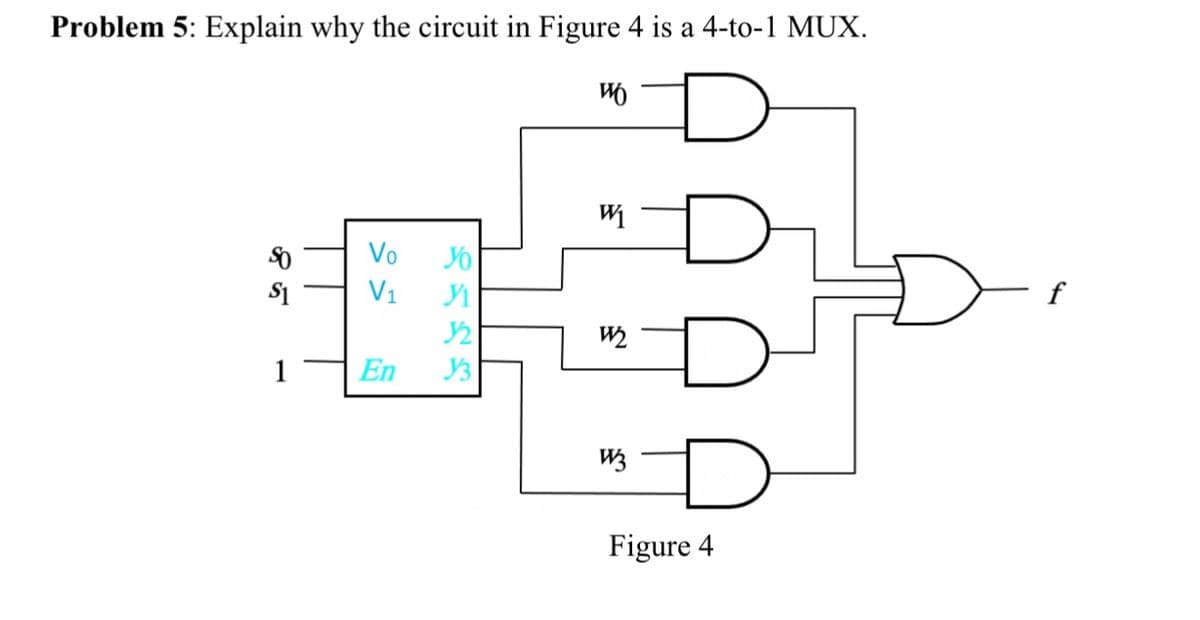
Problem 5: Explain why the circuit in Figure 4 is a 4-to-1 MUX. 注D Vo V1 f W2 En Figure 4
Q: When it comes to data transformation, it may vary from something as basic as a change in data format…
A: INTRODUCTION: In a typical data integration scenario, a client asks the primary server for…
Q: To what extent has the present state of computer security been influenced by past alterations in…
A: Introduction: Cybersecurity, also known as information technology security, is the act of preventing…
Q: In what ways does having "connection points" between networks benefit the parties involved? What…
A: Points to connect network ports, which are nodes where the node is connected to the entire network.…
Q: Put differently, if I am on a private subnet with IP 10.0.0.89/24, how is traffic sent and received…
A: Given that the user has a private subnet we have to find how traffic is sent and received from…
Q: What are the differences between top-down and bottom-up approaches to information security? What are…
A: Introduction: Here we are required to state difference between top-down and bottom-up approaches to…
Q: critical chain
A: Critical Chain: This is the technique used to analyze the schedule network. This comprises task…
Q: Many key challenges must be addressed when information systems are not integrated?
A: Definition: Integrated information systems are information systems that combine data from several…
Q: Do you know the difference between a program and a piece of software?
A: Introduction: Software is a set of programmed that gather and modify data in order to create the…
Q: The table below shows the drag coefficient cp of a sphere as a function of Reynold's number Re. 2000…
A: Matlab Program: %given dataRe=[.2 2 20 200 2000 20000];cD=[103 13.9 2.72 .8 .401 .433];% Re data…
Q: ot recommended to code under the finalize method of a class which executes when the garbage…
A: IntroductionThe finalize () method is a protected pre-defined method in the Object class. The…
Q: Question 5 When writing a recursive method, O you do not need to know ahead of time exactly how many…
A:
Q: Write a command to extract the contents of foo.tar.gz
A: 1) We can use the tar command to unzip or extract a .tar.gz file using command line 2) To extract…
Q: 4. Assuming that we have dumped the following Ip datagram. Identify all the fields of the IP header.…
A: Given IP header: 45 20 03 c5 78 06 00 00 34 06 ca 1f d1 55 ad 71 c0 a8 01 7e
Q: What are some of the reasons why hacking websites is a serious problem?
A: Please find the detailed answer in the following steps.
Q: Examine three firms' recruitment and retention tactics. Assemble methods that take opposing…
A: Recruitment and retention strategies vary from one organization to another in terms of detailed…
Q: Why is a computer program made up of Algorithms expressed in computer language?
A: Almost every aspect of computer science makes use of algorithms. They serve as the foundation of the…
Q: Six components of an information system should be recognised, enumerated and specified.
A: IS (Information System): The term "information system" refers to a system that organizes, stores,…
Q: Problem 1: Prove the following statement: if p and p+2 are twin primes and p > 5, then p³ +3p2 –p -3…
A: Given, p^3 + 3p^2 - p - 3 We can write this expression in products of terms as, p^3 + 3p^2 - p…
Q: If the task runs an average input of size 100, rank the algorithms from least time- complex to…
A: The answer is
Q: When making decisions, teams are also obliged to interact with one another. How car companies make…
A: Computer-aided or computer-assisted is an adjectival word that suggests the usage of a computer as a…
Q: Write a program that checks matching words - First asks the user to enter 2 String variables word1…
A: Note: The program has been provided in Java. Java has two methods to compare strings.…
Q: Analysis of relational schemas and normalization Consider the following conceptual schema of a…
A: Solution :: functional dependency is a restriction that specifies the relationship between two…
Q: Explain the following sprint terminology: Planning for a sprint Backlog for the sprint Goal for the…
A: SPRINT PLANNING: is a term used to describe a type of planning that is done quickly. Sprints are…
Q: The use of common building blocks in multimedia is essential. Show us how multimedia components may…
A: Multimedia Components: Standard building components are crucial in multimedia. Demonstrate how you…
Q: In this java program. Please explain the output of the program. Thank youu Source Code: public…
A: Here, we are given a Java code and we are asked the output. I have run the code and attached the…
Q: Is there a role for database technology in the administration of an organization's data?
A: Database Technology: Administration of data. Database planning, analysis, design, implementation,…
Q: When a corporation uses extranets, what are the strategic and competitive advantages that you see?
A: Introduction
Q: When it comes to data transformation, it may vary from something as basic as a change in data format…
A: Data Transformation: Data transformation is the process of changing data from one format to another,…
Q: Info Systems Security How are Technical safeguards for business and governments used to protect…
A: Technical safeguards contain the unlicensed entrance to protection-liable details, safeguard at…
Q: What are double restrictions and how do they work?
A: DOUBLERESTRICTIONS The double constraint primarily enforces the double or dual variables or…
Q: How is an optical disc organised differently from a magnetic disc?
A: According to the question data in the magnetic disk is the randomly accessed and the read and on the…
Q: Given Stack names=new Stack(); String temp="A"; names.push("John"); names.push("Mary");…
A: Please refer below for your refernce: Initially the stack is filled with John at bottom of stack and…
Q: What are some of the numerous aspects of the software system design process that need to be…
A: Numerous aspects: An input is the information that a computer receives. The data that a computer…
Q: Describe the benefits and drawbacks of using a cloud storage service vs a traditional client storage…
A: Cloud Storage Cloud storage is a cloud computing model that stores information on the Internet…
Q: You are given a string: "4 5 4 * 8 1074 5 2* 6 7 * 2"; Read the string from left and apply following…
A: As per the question, We need stack and queue class. We will define main method which will perform…
Q: In spite of the fact that the article was published in a meteorological journal, it is regarded as…
A: Matlab Program: clearclose allclc init=[1;10^-3*rand;1];%initial conditions,change these as needed%3…
Q: (a) Explain connection-oriented demultiplexing in the context of the transport layer. (b) What is…
A: DEMULTIPLEXING: The signals received at the demultiplexed nodes are split and sent to the…
Q: In a workplace with shared resources like a printer, how do you handle security?
A: Security: Confidentiality, integrity, and availability are three fundamental security principles…
Q: What are the many types of software I can use to back up Windows 10, and what are the main…
A: A computer backup procedure duplicates all of your files, data, and information to generate two…
Q: Disks that can be rewritten? It's possible, right?
A: Introduction: A disc (or diskette) is a flat, spherical plate that can store and encode data. Hard…
Q: 1 import java.io.*; 3v public class Main public static void main(String[] args) throws IOException 5…
A: Let's understand step by step : 1. public static void main(String args[]) throws IOException This…
Q: Hard disc drives and solid-state drives are two different types of storage devices. To what extent…
A: According to the question the HDD and SDD both are working different in our way to perform the…
Q: w would the operating system migrate fro
A: Below the operating system migrate from User Mode to Kernel Mode
Q: When making decisions, teams are also obliged to interact with one another. How can companies make…
A: Computer programming as a decision-making tool has been presented as a technique for supporting…
Q: Please write down the output of following code: ArrayList list = new ArrayList(); list.add("10");…
A: As given, we need to write down the output of the given code. Given code - ArrayList<String>…
Q: The TCP/IP paradigm has what number of layers?
A: Introduction The TCP/IP paradigm has what number of layers?
Q: Demonstrate the corresponding output for the given program. Give your analysis for the program.…
A: #include<iostream> using namespace std; int main() {clrscr(); int x, sum; sum = 0; for (x =…
Q: Can someone show me an example of what 6 records for each table would like in SQLlite? And let us…
A: SQLite enables us to manage relational database systems. SQLite is a lighter version of the SQL…
Q: Moore: Why does he believe he can talk about ICs? What does debugging mean? What does the phrase…
A: The Incident Command System (ICS) is an exceptionally normalized, hierarchical, military-based…
Q: Q2/ what is the difference between the use of (all) and (some) in nested subqueries.
A: SQL stands for Structured Query Language.
Step by step
Solved in 2 steps with 1 images

- Build the following function using only 8x1 Mux: F(a,b,c,d,e) = ∑ (0, 4, 8, 16, 17, 20, 22, 24, 25, 31) [NB: Must show MSB & LSB] [NB: The circuit should be cost efficient. Meaning, try to use lowest number of ICs possible for an optimum design]a) Build your circuit Design and build a state machine that will control the transition between light settings of a traffic light unit as shown in Figure 1. The design should include 3 positive edge triggered D flip-flops. Use 1 flip-flop to control the on and off of a given light, and the state machine should switch from Red (100) -> Red and Amber (110) - > Green (001) -> Amber (010) and repeat the cycle again, with the transition table below.Problem 4 Given the circuit with input of 80HZ, • Find the turns ratio • Find Vp(sec) • Find Vo when capacitor is removed. • Find PIV rating • Find Vripple (p-p) • Find ripple factor (rf) 5:2 Use practical Si diode Rurr 100Vrms RL 3.3 k2 C 100 uF lll
- Perform sequential and one-hot state assignment separately for a circuit with 3 different states A, B, C.R2 R1 RL R3 Given 1 = 4 A R1 = 72 R2 = 20 R3 = 32 For the above circuit, determine VTh and RTh to the left of the (a,b) terminals. Additionally, find RL for maximum power transfer and find that max power, Pmax, delivered to the load resistor RL. You must show all your work, including redrawing circuits as necessary. Clearly show your steps for finding VTh RTh RL, and pmax: Finally, put a box around each of your answers for VTh, RTh: RL, and pmax- Take a picture of your handwritten analysis and upload it as a single PDF or JPG for this problem. 治Design a Mode 11 asynchronous forward counter circuit. (Use JK or T type flip-flops)
- Please show solution to answer The state diagram for a sequential circuit appears in the following figure. Find the state table for the circuit(Logic Gates:* 7404LS (NOT)* 7408LS (AND)* 7432LS (OR)* 7400LS (NAND)* 7402LS (NOR)* 7486LS (EX-OR)* Decoder 74hc138Or you can use 74HCxx versions.) Task 3: Design a Binary Ripple Carry Adder for 5+3 summation in BCDcoding system. Draw the the circuit diagram by using FullAdder Blocks. Simulate the circuit.Show the VBA code for this problem
- 1) Design a synchronous counter by taking account the following counting order;0-5-1-4-6-7-3-0-5-1-4-6-7-3...1. Design and implement a circuit using positive edge triggered DFFs that generates a pulse (p = 1) on the 2nd, 3rd, 5th, and 7th clock cycles after initialization. The sequence should repeat every 8 clock pulses. Include an asynchronous reset signal. 1.1 Implement your design in Verilog (behavioral)Simplify this circuit using Boolean Algebra please provide detailed steps;

