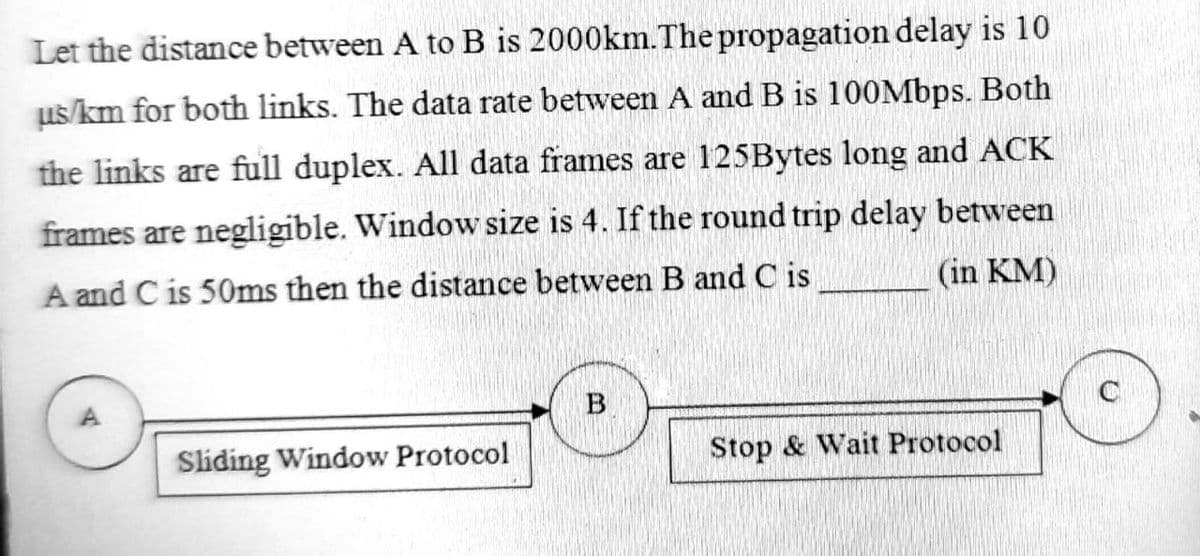
propagation delay is 10 ad B is 100Mbps. Both 5Bytes long and ACK und trip delay between
Q: Consider yourself a system analyst in the workplace. Do you see any similarities or differences…
A: The SDLC is a method for developing high-quality software using well-defined processes. The software…
Q: Raphson Method. Let f(x) = cos(x) – x. Approximate a root of f using (i) the fixed-point method with…
A: Write a MATLAB code for Newton-Raphson Method. Let f(x) = cos(x) – x. Approximate a root of f…
Q: Describe in as few words as possible the address control lines.
A: The control lines determine the direction of data flow and when each device can access the bus.
Q: To solve what kinds of issues does a simultaneous multithreading design need an operating system?
A: SMT is a technique for merging hardware multithreading with superscalar processor technology in a…
Q: Consider yourself a system analyst in the workplace. Do you see any similarities or differences…
A: system development Life Cycle: The SDLC is a method for developing high-quality software using…
Q: What exactly is DNS monitoring, and why is it so crucial?
A: Introduction: Here we are required to explain what is DNS monitoring and why is it so crucial.
Q: Write a C++ program that contain a menu rto call user defined functions on a one dimendional array :…
A: Given: Write a C++ program that contain a menu rto call user defined functions on a one…
Q: The following two statements will generate two strings with the same content: std::string strl =…
A: In this program we have to find out whether these string will create the same content in the C++…
Q: Do a cost-benefit analysis and develop conclusions on the advantages and disadvantages of…
A: A connection-oriented service is a network service that was conceived and developed after the phone…
Q: Use a variety of examples to explain real-time operating systems. Explain how it differs from a…
A: Real-time operating system: It is often used in environments where a significant number of events…
Q: What exactly is meant by the term "preemptive scheduling"?
A: Beginning: Scheduling is selecting which process will execute while another is on hold. 2) The…
Q: Explain the many design models that we use in the software development analysis process.
A: Let's solve it: ModelWaterfallWaterfall is a cascading SDLC paradigm in which development flows…
Q: 2. Draw the following Boolean Expressions into its equivalent K-Map and Logic Diagram. Q = AB + BC…
A:
Q: In shared memory architecture, talk about the bootstrap and application processors.
A:
Q: Convert this integer (which is currently in hexadecimal notation) to binary notation: 95
A: As per the question statement, We need to convert the given hexadecimal number to binary number.
Q: H.W./A 600V voltmeter is specified to be accurate within ± 2% at full scale. Calculate the limiting…
A: here in the question given 600V voltmeter which is specified to be accurate within 2% at full scale.
Q: Define social networking software in the context of computer science.
A: Define "social networking software" using the terminology of computer science. Social Networking…
Q: You have to make aC Program to Convert Celsius from Fahrenheit, Kelvin and Réaumur or to Convert…
A: As per the question statement, we will write program in c language.
Q: ry Mapped I/O : The CPU s l/O ports just as if they eren't memory locations
A: In Memory Mapped I/O: The CPU treats I/O ports just as if they .weren't memory locations True O
Q: What are Hash Tables? What is Map Interface and Linked Implementation What is Chaining and Linear…
A: Hash table is a very important data structure used for fast information retrieval Hash Table is the…
Q: 5-bit Binary numbers rep m of X and Y represe
A:
Q: Explain how circuit-switched networks are built. Briefly
A: Explain how circuit-switched networks are built.Briefly Answer: Network with Circuit Switching: A…
Q: Which criteria for Round Robin Scheduling are the most important to get the best results in terms of…
A: Answer the above question are follows
Q: ingle ROM as a KOR and NAND = (X3X2X1X0 ar ress lines (the le put lines (the le
A: The smallest possible dimensions of the ROM is 64k x 16bits. Explanation: Input to ROM – 2 lines…
Q: In shared memory architecture, talk about the bootstrap and application processors.
A: Solution : Shared Memory Architecture : A shared-memory multiprocessor is an architecture with a…
Q: What exactly is multiple fact taBles, and how does it function?
A: Intro The FACT table contains the metrics, measurements, and facts of the business process, and it…
Q: What is the ultimate goal of an operating system?
A: Operating System: It facilitates communication between application software, computer hardware, and…
Q: What are some of the key differences between agile and conventional methodologies? What are some of…
A: What are a few ways in which the agile methodology differs from the traditional methodology? Answer:…
Q: In programming, specify desk checking.
A: Desk checking It is the manual procedure that are used to verify the programming logic or the…
Q: Can you provide me some more information on Link State Protocols and an example of one?
A: Link state protocols establish the optimal path based on route characteristics such as speed and…
Q: msh7.c can be terminated with exit , but msh8.c cannot. Is this true? Yes! No!
A: Exit command is used to terminate the control of program.
Q: When it comes to scheduling the CPU, what happens if multiple different processes have the same…
A: Introduction: Importance Scheduling is a process scheduling system that prioritizes tasks depending…
Q: In a recovery file, what are the necessary requirements for the entries of transaction status and…
A: Database systems: Database systems, like any other computer system, might fail, but the data they…
Q: When comparing the type declaration of a rvalue reference with a lvalue reference, how can you tell…
A: In C++, every expression is either a value or an r value.
Q: Given three binary features (X, Y and Z), two classes (1 a the examples listed in the table below,…
A: Sol: Since, the class varies accordingly for three times values of feature of X, therefore the…
Q: What exactly do you mean when you say "software"?
A: Software: A collection of computer programmes designed to carry out a certain operation is referred…
Q: Write a for loop program that will accept student name, section and 10 numbers, identify if the…
A: 1.Start 2.Declare structure named student which contains character arrays name ,section and integer…
Q: list of municipalities in north and south cyprus with their websites.
A: Generally speaking, we have 39 municipalities located in Cyprus as this is the third-largest island…
Q: 9. The JFET always operates with a reverse-biased gate-to-source pn junction. True or false 10. The…
A: Disclaimer: As per guidelines, we can only solve one question. Hence resubmit the questions for…
Q: Is there a link between DNS servers and network forensic investigation in any way?
A: Answer:
Q: An interface control that is attached to a data source should be labeled with the proper…
A: Interface Control Document (ICD): Interface Control Document (ICD) is a document that outlines a…
Q: An explanation of the Address Resolution Protocol is required (ARP).
A: Protocol for Address Resolution ARP is a communication technique used to determine the MAC address…
Q: The database design is likely to change frequently: 1. Database Extension 2. Database Intension 3.…
A: For the statement, "The database design is likely to change frequently" The given options are: 1.…
Q: Declare a class named complex with two data members x (int) and y (int). This class contains an…
A: Algorithm to subtract complex objects - Create a class named complex having two data members i.e. x…
Q: write a java program to print the mirror image of right angled in x-direction after taking number of…
A: Required:- Write a Java program to print the mirror image of right-angled in x-direction after…
Q: 2. Write a Java program to illustrate Dynamic Method Dispatch using hierarchical inheritance.
A: I give the code in Java along with output and code screenshot
Q: What's your take on the use of force? Network congestion may be reduced more efficiently by using…
A: Start: High public perceptions of violence lead to lifestyle and housing modifications (Warr, 1994).…
Q: 15. Assuming the following C++ variable declaration statement int i = 2021, *pi = &i, **ppi π…
A: Given: C++ variable declaration statement. int i = 2021 , *pi = &i , **ppi = π…
Q: Declare a class named Vehicle as a base class with two data members model (string) and year (int).…
A: Introduction: In this question, we are asked to declare two classes only that are Vehicle(base…
Q: Q3. A link has a signal-to-noise ratio of 2000 and a bandwidth of 12000 KHz. What is the
A: The answer is
Step by step
Solved in 3 steps with 3 images

- Write a program to simulate the behavior of the CSMA/CD protocol over Ethernet when ther are N stations ready to transmit while a frame is being transmitted. Your program should report the times when each station successfully starts sending its frame. Assume that a clock tick occurs every slot time (51.2 microsec) and a collison detection and sending of a jamming sequence takes one slot time. All frames are the maximum length allowed.Computer A uses the Go-back-N ARQ protocol to send a 110 Mbytes file to computer B with a window size of 15. Given each frame carries 100K bytes data. How long does it take to send the whole file (the total time taken from A sending the first bit of the file until A receiving the last acknowledgment)? Given that the transmission rate of the link is 500 Mbps and the propagation time between A and B is 15ms. Assume no data or control frame is lost or damaged and ignore the overhead due to header and trailer.Consider a full-duplex 256 Kbps satellite link with a 240 millisecond end-to-end delay. The data frames carry a useful payload of size 12,000 bits. Assume that both ACK and data frames have 320 bits of header information, and that ACK frames carry no data. What is the effective data throughput When using sliding windows with a sender window size of W = 5 data frames?
- Write a program to simulate the behaviour of the CSMA/CD protocol over Ethernet when there are N stations ready to transmit while a frame is being transmitted your program should report the times when euch station successfully starts sending its frame. Assume that a clock tick occurs once every slot time (57.2 usec) and a collision detection and sending of a jamming sequence. takes one slot time. All frames are the maximum length allowedThe network referenced is shown in the picture below: Assume the network uses packet switching and 2 Kilobyte packets. Assume both L1 and L2 each have a propagation delay of 0.1 seconds. We are sending a 100 Kilobyte file. If L1 has infinite bandwidth, and L2 has a bandwidth of 1 Megabit (125 Kilobytes) per second, how long does it take to send the entire file? After the entire file is sent, a single acknowledgment is needed to say the file arrived, how long does the entire process take now (you can assume the ack has negligible size)? If a maximum of 10 packets can be sent per an RTT (this is the equivalent of a fixed window size of 10 packets), how long does it take to send the entire file? What if we start with a congestion window of 1 packet in slow start phase and no slow start threshold, How long to send the entire file now (Hint: This is similar to the previous question but with a variable window rather than fixed)? What if we start in congestion avoidance (linear growth)?Suppose that a 20-Mbps 802.11 LAN is transmitting 64-byte frames back-to-back over a radio channel with a bit error rate of 10−7 (i.e., the probability of a bit to flip duringthe transmission). How many frames per second will be damaged on average?(*hint: you would need to calculate the probability that a frame does not suffer any bit errors, thisis equivalent to the fraction of frames that do not suffer any bit errors on average.)
- Consider the window size is 10, bandwidth is 1500 bps, transmission delay is 2 ms atpropagation delay is 50 ms. What is the throughput using Go Back N protocol? a) 294.11 b) 140.23 c) 96 d) 154.21Consider a short, 10-meter link, over which a sender can transmit at a rate of 150 bits/sec in both directions. Suppose that packets containing data are 100,000 bits long, and packets containing only control (e.g., ACK or handshaking) are 200 bits long. Assume that N parallel connections each get 1/N of the link bandwidth. Now consider the HTTP protocol, and suppose that each downloaded object is 100 Kbits long, and that the initial downloaded object contains 10 referenced objects from the same sender. Would parallel downloads via parallel instances of non-persistent HTTP make sense in this case? Now consider persistent HTTP. Do you expect significant gains over the non-persistent case? Justify and explain your answerConsider sending real-time data from Host A to Host B over a packet-switched network. Host A takes an 8-bit measurement every millisecond, and Host A collects these into 64-byte packets. There is one link between Hosts A and B; its transmission rate is 5 Mbps, its propagation delay is 2 × 108 meters/sec, and its length is 3 km. As soon as Host A gathers a packet, it sends the packet to Host B. How much time elapses from the time that Host A begins to take the first measurement in a packet until the entire packet reaches Host B?
- suppose two hosts, A and B, are separated by 20,000 kilometers and are connected by a direct link of R = 2 Mbps. Suppose the propagation speed over the link is 2.5 x 108 meters/sec. 1. Calculate the bandwidth-delay product, R x dprop. 2. Consider sending a file of 800, 000 bits from Host A to Host B. Suppose the file is sent continuously as one large message. What is the maximum number of bits that will be in the link at any given time? 3. Provide an interpretation of the bandwidth-delay product?a) In a bus CSMA/CD network with a data rate of 10 Mbps, a collision occurs 20 µs after the first bit of the frame leaves the sending station. What should the length of the frame be so that the sender can detect the collision? b) There are only two stations, A and B, in a bus 1-persistence CSMA/CD network with Tp = 25.6 µs and Tr = 51.2 µs. Station A has a frame to send to station B. The frame is unsuccessful two times and succeeds on the third try. Draw a flowchart for this problem. Assume that the R is 1 and 2 respectively and ignore the time for sending a jamming signal.This elementary problem begins to explore propagation delay and transmission delay, twocentral concepts in data networking. Consider two hosts, A and B, connected by a single link ofrate R bps. Suppose that the two hosts are separated by m meters, and suppose the propagationspeed along the link is s meters/sec. Host A is to send a packet of size L bits to Host B.a. Express the propagation delay, dprop, in terms of m and s.b. Determine the transmission time of the packet, dtrans, in terms of Land R.c. Ignoring processing and queuing delays, obtain an expression for the endto-end delay.d. Suppose Host A begins to transmit the packet at time t = 0. At time t = dtrans,where is the last bit of the packet?e. Suppose dprop is greater than dtrans. At time t = dtrans, where is the first bit ofthe packet?f. Suppose dprop is less than dtrans. At time t = dtrans, where is the first bit ofthe packet?g. Suppose s = 2.5 · 108, L = 120 bits, and R = 56 kbps. Find the distance mso that dprop equals…

