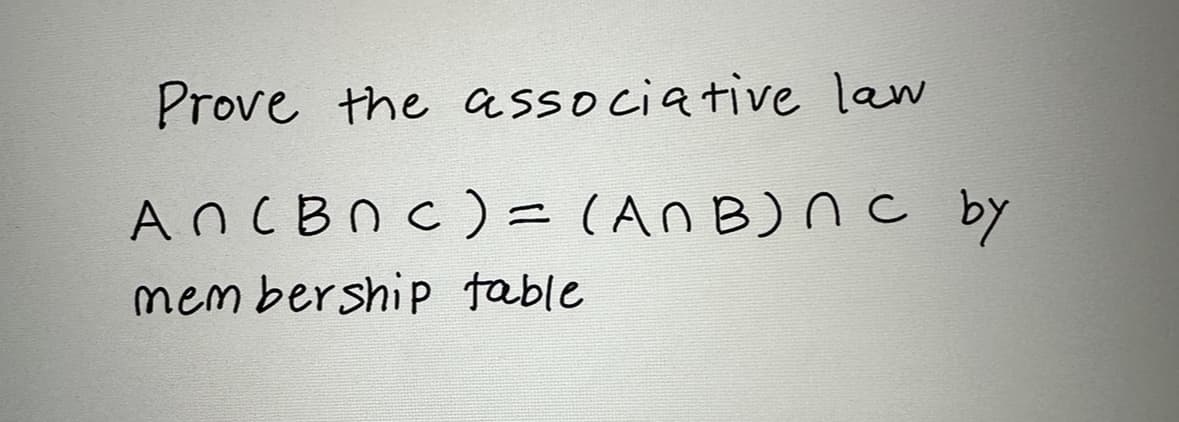
Prove the associative law An (BNC) = (ANB) nc by membership table
Q: Which model is a good choice when oBudget and risk evaluation are important oThere is a medium to…
A: Please refer to the following step for the complete solution to the problem above.
Q: Write a program to search a record using its roll number and display the name of student. If record…
A: I have provided PYTHON CODE along with CODE SCREENSHOT and OUTPUT SCREENSHOT------------
Q: Please answer 6 to 10 also. Thank you so much
A: Answer: We need explain the code and given we need to explain the question number 6 to 10. so we…
Q: what is search engine ?
A: In this question we need to explain search engine.
Q: Simply put, what is the meaning of binary translation? When is it essential, and why is it required?
A: Introduction: A software virtualization technique called binary translation requires an interpreter…
Q: What factors improve the efficacy of intrusion prevention?
A: Intrusion prevention: Intrusion prevention is a security technique that monitors a network or system…
Q: What are some of the difficulties associated with using a database, and how may they be mitigated?
A: 1. A Database Management system (or DBMS). 2. It is essentially nothing more than a computer-based…
Q: Given the formal description below (to be discussed in class on January 27), draw the corresponding…
A: In this question we have to draw a state diagram from the given state table where we need to find…
Q: Clarify the TCP congestion management mechanism and describe its operation.
A: The TCP Congestion Control protocol was developed to help manage congestion in network environments.…
Q: intro_to_sklearn.ipynb 1. Comparing normalized vs raw data Using knns with Euclidean distance and 3…
A: Introduction The most similar instances to the new data should be utilized for making predictions.…
Q: in class Song, write the calculation in method getEstEarnings of class Song to evaluate estimated…
A: Here is the updated code for the getEstEarnings method: public int getEstEarnings() { //…
Q: Read the following description and answer all the questions below. As a project manager at the…
A: Intelligent software: Intelligent software is a type of computer program that performs tasks that…
Q: The virtual circuit is the lowest feasible unit when discussing an automated teller machine. How?
A: We must decide which of the following, in terms of the ATM, is the smallest unit: the virtual…
Q: can you please convert this python code into java? Python code is as shown below: # recursive…
A: The source code of the java program public class Main{public static boolean row_puzzle_rec(int…
Q: To start, let's define precisely what it is that an intrusion prevention system does.
A: Intrusion detection and prevention system (IPS): Network security that recognises and stops detected…
Q: Write a complete program for finding a longest common substring:
A: Brute Force implementation for the above problem in R programming. # Function to find the length of…
Q: Create a node server with the following requirements: Use the dotenv package to manage your…
A: Here is a simple implementation of the server in Node.js using Express.js: const express =…
Q: Write a shell script to display arguments to script. Enter any three input arguments to script and…
A: HI THEREI AM ADDING ANSWER BELOWPLEASE GO THROUGH IT THANK YOU
Q: How has the history of computer security shaped the way it is used today?
A: Computer System Security Overview: Computer System Security is the practice of protecting…
Q: The value in a TextBox is ______________. a. a double b. a string c. It might be any of…
A: In any major programming language like C#, .NET, HTML, or Java, the textboxes are extensively used…
Q: rite an assembly language program that corresponds to the following C program: int num; int main ()…
A: Here is a possible assembly language program that corresponds to the given C program using the Pep/9…
Q: The frontlink() macro calls smallbin_index() or bin_index() (their internal workings are not…
A: The frontlink() macro calls smallbin index() or bin index() to determine the index IDX of a bin…
Q: Explain why cross-validation is used in both supervised learning (classification) and unsupervised…
A: Please find the answer below :
Q: If you're concerned about keeping your network safe online, why is intrusion prevention and…
A: Network: A network is a system of interconnected computers and other electronic devices that…
Q: Numbers are randomly generated and passed to a method. Write a program to find and maintain the…
A: Step-1: StartStep-2: Create an empty list sorted_numbersStep-3: Define the function…
Q: ove cursor to the last line of the file with one key: G Use one key to move cursor to bottom line…
A: Your answers are mostly correct. Here are some minor corrections: Move cursor to the last line of…
Q: Please send me answer within 10 min!! I will rate you good for sure!! Please dont copy from internet…
A: This program generates 15 random demand values using the numpy library and fits a simple linear…
Q: QUESTION 15 Two CFGS, G1 and G2, are given: G1: S-> as | Sb | alb and G2: S -> aSbs | bsas | e (read…
A:
Q: namespace std; // function to print the menu void printMenu() { cout<<"Program 1: Gladiolus"<<endl;…
A: I have included a function named printSpace() which will only print blank spaces instead of :.
Q: عبد الله المغلوث --
A: It seems that the speaker is making a general statement about the relationship between pressure and…
Q: 11. What is the f browser? (A) Nexus B Netscape M Internet Ex
A: Explanation Tim Berners-Lee, the director of the World Wide Web Consortium, invented the first…
Q: me. Like This program prompts a person for come and expense amounts, then calculates their net…
A: The algorithm of the code is given below:- 1. Ask the user how many categories of income they have…
Q: e whole dataa
A: I have Plotted below using MATLAB as given in the question:
Q: The MSP430X family (X stands for eXtended) can handle a larger amount of memory since it has a…
A: The MSP430X family of processors is a group of microcontrollers manufactured by Texas Instruments.…
Q: 5. Using the languages L1 and L2 from the previous problem, enumerate the first 6 strings in the…
A: Introduction:- L1={ 011, 101, 110 } L2={ 00, 100, 001 }
Q: The goals scored in a soccer match may be input as a sequence of 1s and 2s terminated by 0. The…
A: Step-1: StartStep-2: Initialize variables to store the number of goals scored by each team:…
Q: Auto-graded programming assignments have numerous advantages, but have some challenges too. Students…
A: Program Approach:- 1. Include header file 2. Take the input from the user 3. Perform calculation…
Q: The try-throw-catch exception handling mechanism is at the level of a. hardware. b. operating…
A: Introduction Try: In a unique block marked with the "Try" keyword, we identify the section of code…
Q: Using Ackermann’s Function to check how slowly a program can run, Implement the algorithm. Assume…
A: Ackermann's Function is a recursive mathematical algorithm that can be used to calculate the value…
Q: With relation to civil rights, what are the risks provided by databases?
A: 1. Encryption is the study of secure communication techniques that allow only the sender and…
Q: Describe the halting condition for the recursive binary search and the reason why stopping…
A: A binary search algorithm is divide and conquer search algorithm which has logarithmic time…
Q: Output each floating-point value with two digits after the decimal point, which can be achieved as…
A: Algorithm of the code: 1. Ask the user for the current price of the house2. Store input as…
Q: Determine the specific type of addressing mode (SMALL LETTERS only) and compute for the address/es.…
A: The addressing mode refers to the way in which the operand of the instruction is specified. The…
Q: 3. Construct an adjacency matrix for the graph shown in Figure: ( please write it in copy paste…
A: In graph theory, an adjacency matrix is describing the finite graph structure. It is the 2D matrix…
Q: Of the following, the most significant difference between many console applications and GUI…
A: Console applications are text-based, meaning they use the command line interface to receive and…
Q: The PatternAwareLetterFreqGuesser is an improvement over the naive approach, but it can still be…
A: Python code: from collections import Counterfrom string import ascii_lowercase class…
Q: ▪ Given a 1XN vector where N>=2, return the sum of the even indexed numbers.
A: Matlab: Matlab stands for Matrix laboratory. MathWorks developed the Matlab. It is used to perform…
Q: You Try ... 1. Comparing normalized vs raw data Using knns with Euclidean distance and 3 nearest…
A: To answer the second question, we would first need to load the Iris dataset from the URL into a…
Q: 15. Time Calculator Write a program that asks the user to enter a number of seconds and works as…
A: Python Code
Q: Hexadecimal 1D DC 1F7 Decimal 47 179 436 255
A: The solution is given below with calculations
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

- why mongodb is fit in The framework of CAP theorem1. A known relationship mode of R (U, F), U= (c, t, h, r, s, g, q); F={c->tq, cs->g, ht->r,hr->c, hs->r}; find the minimum cover of F, then use the Normal Form decompositionalgorithm to standardize this mode to 3NF, and check if the decomposition has thenonadditive join property.Consider the relation R(A, B, C, D, E) and the set F = {AB → CE, E → AB, C → D}. What is the highest normal form of this relation? Explain your answer.

