Pseudo code:
Database System Concepts
7th Edition
ISBN:9780078022159
Author:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Chapter1: Introduction
Section: Chapter Questions
Problem 1PE
Related questions
Question
Please help me with this using java and provide me with a taxpayer.txt file
Transcribed Image Text:Pseudo code:
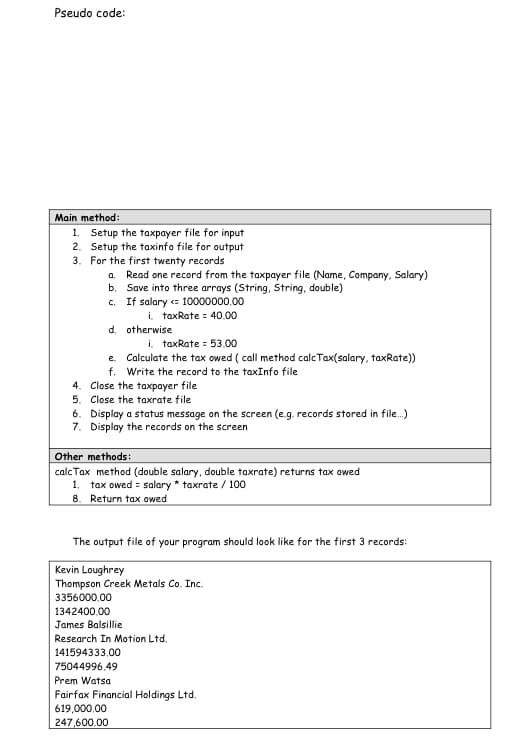
Main method:
1. Setup the taxpayer file for input
Setup the taxinfo file for output
2.
3. For the first twenty records
a. Read one record from the taxpayer file (Name, Company, Salary)
b. Save into three arrays (String, String, double)
c. If salary <= 10000000,00
i. taxRate = 40.00
d. otherwise
i. taxRate = 53,00
e.
Calculate the tax owed (call method calcTax(salary, taxRate))
f. Write the record to the taxInfo file
4. Close the taxpayer file
5. Close the taxrate file
6. Display a status message on the screen (e.g. records stored in file...)
7. Display the records on the screen
Other methods:
calc Tax method (double salary, double taxrate) returns tax owed
1. tax owed = salary * taxrate / 100
8. Return tax owed
The output file of your program should look like for the first 3 records:
Kevin Loughrey
Thompson Creek Metals Co. Inc.
3356000.00
1342400.00
James Balsillie
Research In Motion Ltd.
141594333,00
75044996,49
Prem Watsa
Fairfax Financial Holdings Ltd.
619,000,00
247,600.00
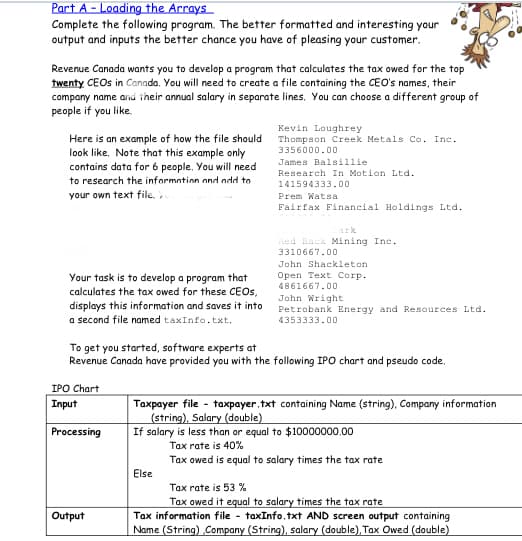
Transcribed Image Text:Part A-Loading the Arrays
Complete the following program. The better formatted and interesting your
output and inputs the better chance you have of pleasing your customer.
Revenue Canada wants you to develop a program that calculates the tax owed for the top
twenty CEOs in Canada. You will need to create a file containing the CEO's names, their
company name and their annual salary in separate lines. You can choose a different group of
people if you like.
Kevin Loughrey
Thompson Creek Metals Co. Inc.
3356000.00
James Balsillie
Here is an example of how the file should
look like. Note that this example only
contains data for 6 people. You will need
to research the information and add to
your own text file. Y
Research In Motion Ltd.
141594333.00
Prem Watsa
Fairfax Financial Holdings Ltd.
ark
Red Back Mining Inc.
3310667.00
John Shackleton
Open Text Corp.
4861667.00
Your task is to develop a program that
calculates the tax owed for these CEOs,
displays this information and saves it into
a second file named taxInfo.txt,
John Wright
Petrobank Energy and Resources Ltd.
4353333.00
To get you started, software experts at
Revenue Canada have provided you with the following IPO chart and pseudo code.
IPO Chart
Input
Processing
Output
Taxpayer file - taxpayer.txt containing Name (string), Company information
(string), Salary (double)
If salary is less than or equal to $10000000.00
Tax rate is 40%
Tax owed is equal to salary times the tax rate
Else
Tax rate is 53 %
Tax owed it equal to salary times the tax rate
Tax information file- taxInfo.txt AND screen output containing
Name (String) Company (String), salary (double), Tax Owed (double)
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps with 4 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Database System Concepts
Computer Science
ISBN:
9780078022159
Author:
Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:
McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:
9780134444321
Author:
Tony Gaddis
Publisher:
PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:
9780132737968
Author:
Thomas L. Floyd
Publisher:
PEARSON

Database System Concepts
Computer Science
ISBN:
9780078022159
Author:
Abraham Silberschatz Professor, Henry F. Korth, S. Sudarshan
Publisher:
McGraw-Hill Education

Starting Out with Python (4th Edition)
Computer Science
ISBN:
9780134444321
Author:
Tony Gaddis
Publisher:
PEARSON

Digital Fundamentals (11th Edition)
Computer Science
ISBN:
9780132737968
Author:
Thomas L. Floyd
Publisher:
PEARSON

C How to Program (8th Edition)
Computer Science
ISBN:
9780133976892
Author:
Paul J. Deitel, Harvey Deitel
Publisher:
PEARSON

Database Systems: Design, Implementation, & Manag…
Computer Science
ISBN:
9781337627900
Author:
Carlos Coronel, Steven Morris
Publisher:
Cengage Learning

Programmable Logic Controllers
Computer Science
ISBN:
9780073373843
Author:
Frank D. Petruzella
Publisher:
McGraw-Hill Education