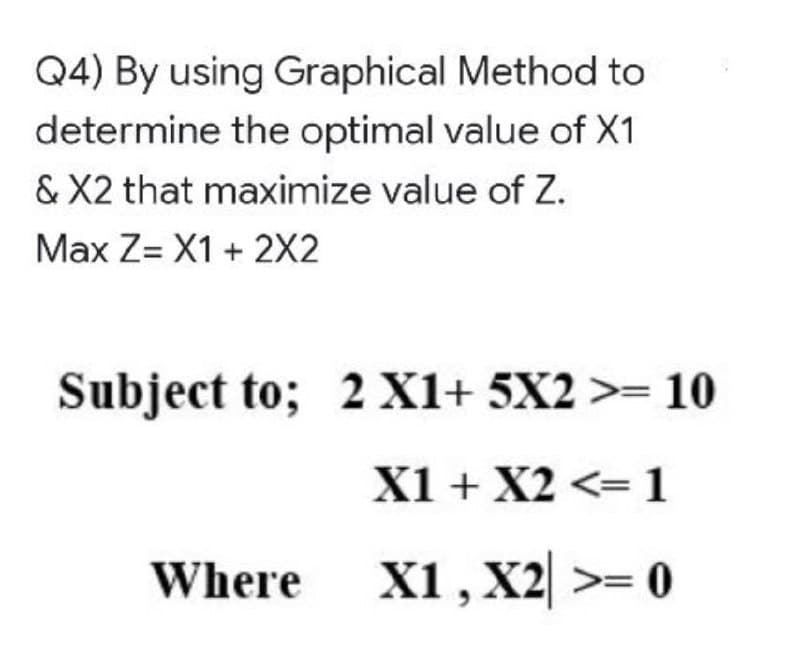
Q4) By using Graphical Method to determine the optimal value of X1 & X2 that maximize value of Z. Max Z= X1 + 2X2
Q: Explain briefly the activities covered by software project management.
A: The following are the activities covered by software project management.
Q: When a child process reads the parent's message buffer using unnamed pipes, what should happen next?
A: Introduction: Named pipes may persist eternally as long as the system is functioning, but ordinary p...
Q: What function does system modeling play in the software development process
A: What function does system modeling play in the software development process?
Q: eld of computer science, expla
A: Below the definition of RFP
Q: Analysis of algorithms is the determination of the amount of time and space resources required to ex...
A: The plan for analysis of general algorithm: Time complexity: 1.Loops a. N elements: if 1 is...
Q: Data is transferred from a source to a destination via a network. The data cannot be sent until it h...
A: Data is transferred from a source to a destination via a network. The data cannot be sent until it h...
Q: What are the THREE advantages that the Microsoft Excel system has brought you in your firm, in your ...
A: here we have given three advantages that the Microsoft excel system has bought
Q: the following
A: We draw truth table for the given statements and rewrite them using NOR operation.
Q: ion that would return single digit sum of a number. Ex. Given: 195 the function returns 6 -> 1...
A: Below function that would return single digit sum of a number.
Q: Give details, and explain briefly on each of the following Core Practices: 1. Pair Programming 2. C...
A: Pair programming is a coding practice in which two programmers work together on a single machine. On...
Q: Simplify the following Boolean expressions to a minimum number of literals: a. (a + b+ c’)(a’b’ + c)...
A: (a + b+ c’)(a’b’ + c) =(a.c) + (b.c) + (c'.c) + (a.a'b') + (b.a'b') + (c'a'b') =(a.c) + (b.c) + (0) ...
Q: Write two overloaded functions maximum as per following definition: returns the maximum of two integ...
A: Overloaded functions are those functions that have the same name but they differ with the help o...
Q: Suppose we are using gradient descent to learn linear regression. The hypothesis is ho(x) = 00 + 01x...
A: h(x) = 1 + 2x at x = 10 h(10) = 21. alpha = 0.5
Q: Can you fill in the blanks? Question: A(n) __ contains final comments or processing instructions in...
A: A Processing instruction contains final comments or processing instructions in an XML document.
Q: There are three exciting new applications becoming possible as a result of the development of the in...
A: Introduction: For starters, as IoT technology progresses, more firms will benefit from IoT applicati...
Q: Describe how registers in a computer processor work.
A: A processor register is an area that a computer's processor can reach fast. The majority of register...
Q: What does system model mean? What should be considered while making basic models?
A: Given: What does the term "system model" imply? What should be kept in mind when creating basic mode...
Q: Create a Java class that displays that accepts a number and displays the left most digit The number...
A: import java.util.*;public class Main{ public static int lastDigits(int num){ // keep looping till o...
Q: A. Write down the last five digits of your NIM p = B. Calculate x with the following formula: x = p...
A: The solution for the subparts A,B and C is given in the below step:
Q: How does a client program recognize a server application running on a different machine on the netwo...
A: Introduction: A thick client is a computer that runs an art application (such as Krita or Sketchup) ...
Q: sms in a trusted compute based? Given me at least 6 of them and explain their function in your own w...
A: Trusted Computing BaseA computer system's trusted computing base is the collection of all hardware, ...
Q: 2. 2 independent problems about Elgamal: (a) what things go badly if Alice picks the private keys 0 ...
A: Plain text in cryptography: Packet headers are generally plain visible text before it will be secure...
Q: Use the problem description below to create: (a) a use case diagram, (b) a class diagram, (c) two va...
A: Introduction Use the problem description below to create: (a) a use case diagram, (b)a class diag...
Q: The program enters the scores of an test for 10 students and saves them as an array. Then the progra...
A: Use a loop to iterate over the array to accept input and then compare the values
Q: How do I write a python program that iterates the integers from 1 to 50? For multiples of three pri...
A: The python program to print different string for some condition and for starting 50 numbers. If num...
Q: Create an application named Numbers whose main() method holds two integer variables. Assign values t...
A: PROGRAM INTRODUCTION: Use the required namespaces. Start the definition of the class to store all t...
Q: t process is sup
A: Traditional system development The process of designing and developing simple software is known as ...
Q: Q:1. What is at put of this logic gate? A F=?
A:
Q: You are given an array with following items in sequence: {14, 7, 3, 12, 9, 11, 6, 12} Sort the item ...
A: We are given an unsorted array and we are going to sort the array using Merge sort algorithm. Merger...
Q: chain with in
A: given - Describe an ideal infrastructure for a private blockchain with integrated security
Q: SECTION I: FILL IN THE BLANKS: PICK EXACT TRUE ANSWER* *******Routers are used to connect networks t...
A: Answer: Break up.
Q: Why do we take into account the worst-case scenario than an average-case scenario?
A: We are going to understand why we perfer using worst case scenario in algorithm rather than their av...
Q: c++ beginers given 10 numbers a1 a2 ... a10 calculate (do not use an array)
A: The cin object is used to accept input from the standard input device i.e. keyboard.
Q: What type of impact will the Internet of Things (IoT) have as it affects our daily lives? Use any ga...
A: Lets see the solution in the next steps
Q: In a C# Console Ap Write a method that takes an int and a double and returns their product.
A: The requested C# program by using a method is provided in next step.
Q: Hash functions and signatures: Signature schemes are typically defined to work for a finite domain o...
A: The Answer is given below step.
Q: edge-triggered from level-triggered interrupt
A: Level triggered interrupt is an indication that a device needs attention. As long as it needs attent...
Q: Suppose that the tuition for a university is $10,000 this year and increases 5% every year. Write a ...
A: To write a code to computes the tuition in ten years and the total cost of 4 years’ worth of tuition...
Q: Use the private key DIAGEKBLXMQI to answer the following questions. 1. Use the private key to encode...
A: 1. Use the private key to encode the message "hello world". Code:- # Taking input from userdata = 'h...
Q: Which encryption technique encrypts individual files such that only the file's owner and authorized ...
A: Symmetric encryption is a sort of encryption where just one key (a mystery key) is utilized to both ...
Q: In this session, we'll go through several protections against Man-in-the-Middle attacks that steal w...
A: The MITM is also known as Man-in-the-Middle attacks.
Q: What does defining a system model imply? When constructing fundamental models, what elements should ...
A: Introduction: The phrase "system model" is used in some domains, areas of application, and various w...
Q: Distinguish between an attack and a threat.
A: The solution to the given problem is given below.
Q: Do the following questions: a. Create a function that takes a source file name and destination file ...
A: The solutions for the subpart A and B are given in the following steps with corresponding output. fi...
Q: Convert the number system, without using calculator. Row number 4
A: We have to solve for the row 14 Now in this we have only hexadecimal numbers Hence we have to cove...
Q: Describe the internet's significance in the realm of information and communication technology.
A: Introduction: The internet has evolved into a critical component of our daily lives. Our lives are ...
Q: Turing machine for UNARY DIVISION with quotient and remainder. Full Steps
A: Turing machine handles a string of 0s and 1s, with 0 represented by the blank symbol.
Q: What is the position of IPv4 in the hierarchy, and how are concerns related to the creation of big n...
A: Introduction: Concerning the state of IPv4 in the hierarchy and challenges relating to the creation ...
Q: Given the Sailor, Boat, and Reservation tables. Sailor Table Reservation Table ID (PK) NAME RATING A...
A:
Q: What data is stored in the C:WindowsSystem32LogFilesSRT SRT Trail txt file?
A: Introduction: Srttrail. txt in Windows 10 can be caused by incompatible hardware, an overloaded powe...
Step by step
Solved in 2 steps

- This problem exercises the basic concepts of game playing, using tic-tac-toe (noughtsand crosses) as an example. We define Xn as the number of rows, columns, or diagonals with exactly n X’s and no O’s. Similarly, On is the number of rows, columns, or diagonals with just n O’s. The utility function assigns +1 to any position with X3 = 1 and −1 to any position with O3 = 1. All other terminal positions have utility 0. For nonterminal positions, we use a linear evaluation function defined as Eval (s) = 3X2(s)+X1(s)−(3O2(s)+O1(s))."Mark on your tree the evaluations of all the positions at depth 2."Which of the following statements are true given A* (admissibility and consistency of heuristics ] ? The heuristic function h[n] is called admissible if h[n] is never larger than h*[n], namely h[n] is always less or equal to true cheapest cost from n to the goal. If the heuristic function, h always underestimates the true cost [h[n] is smaller than h*[n]), then A* is guaranteed to find an optimal solution. When h is inconsistent, it can not be admissible. If h is consistent and h[goal)=0 then h is admissible A* is complete and optimalcomputes and returns the smallest positive integer n for which 1+2+3+...+n equals or exceeds the value of "goal".
- K = 0, L = 18 Write and solve the following linear program using lingo, take screen shots of your model as well as the reports and the optimal solution. Clearly show the optimal solution.NB:K=the second digit of your student number;L=sum of the digits of your student number, For example if your student number is 17400159 thenK=7andL=1+7+4+0+0+1+5+9=27!!!! SAVE YOUR FILE BY YOUR STUDENT NUMBER!!!!minz=t∈T∑(AtYt+PtXt)+k∈K∑(HkUk+BkVk)s.t.Uk+Vk=50∀k∈KXt−CtYt<=0∀t∈Tk∈K∑Vk≥80t∈T∑Xt≥t∈T∑DtXt>=0∀t∈TYt∈{0,1}∀t∈TUk>=0∀k∈KVk>=0∀k∈KThe sets parameters and data are as follows: \[ \begin{array}{l} \mathrm{T}=\{1,2,3,4\} \\ \mathrm{K}=\{0,1,2,3,4\} \\ \mathrm{A}=\{5000,7000,8000,4000\} \\ \mathrm{D}=\{250,65,500,400\} \\ \mathrm{C}=\{500,900,700,800\} \\ \mathrm{P}=\{20, \mathrm{~L}, 25,20\} \\ \mathrm{H}=\{5,3,2, \mathrm{~K}, 9\} \\ \mathrm{B}=\{8,5,4,7,6\} \end{array} \]Which of the following linear programming model has bounded feasible region? Group of answer choices A. max ?=3?+2?subject to the following:??+4???≥4−?≥10≥0≥0max z=3x+2ysubject to the following:x≥4−yx+4y≥10x≥0y≥0 B. max ?=3?+2?subject to the following:?+????≤4≤10−4?≥0≥0max z=3x+2ysubject to the following:x+y≤4x≤10−4yx≥0y≥0 C. None of the above D. max ?=3?+2?subject to the following:??+2???≥10−?≥2≥0≥0We examine a problem in which we are handed a collection of coins and are tasked with forming a sum of money n out of the coins. The currency numbers are coins = c1, c2,..., ck, and each coin can be used as many times as we want. What is the bare amount of money required?If the coins are the euro coins (in euros) 1,2,5,10,20,50,100,200 and n = 520, we need at least four coins. The best option is to choose coins with sums of 200+200+100+20.
- ProblemGiven a value `value`, if we want to make change for `value` cents, and we have infinitesupply of each of coins = {S1, S2, .. , Sm} valued `coins`, how many ways can we make the change?The order of `coins` doesn't matter.For example, for `value` = 4 and `coins` = [1, 2, 3], there are four solutions:[1, 1, 1, 1], [1, 1, 2], [2, 2], [1, 3].So output should be 4. For `value` = 10 and `coins` = [2, 5, 3, 6], there are five solutions: [2, 2, 2, 2, 2], [2, 2, 3, 3], [2, 2, 6], [2, 3, 5] and [5, 5].So the output should be 5. Time complexity: O(n * m) where n is the `value` and m is the number of `coins`Space complexity: O(n)""" def count(coins, value): """ Find number of combination of `coins` that adds upp to `value` Keyword arguments: coins -- int[] value -- int """ # initialize dp array and set base case as 1 dp_array = [1] + [0] * value) ++.Solve the following optimization problems using Gurobi and clearly present the optimal objective function value and decision variable values at optimality. (Java Programming) maximize 3x + 4y − 2z + 10 subject to 2x + 3y − z ≤ 50 x + y + 3z ≥ 30 x unrestricted, y ≥ 0, z ≥ 0, and integerPractice Test Questions: Prove each of the following statements, or give a counterexample: Best-first search is optimal in the case where we have a perfect heuristic (i.e., h(n) = h∗(n), the true cost to the closest goal state). Suppose there is a unique optimal solution. Then, A* search with a perfect heuristic will never expand nodes that are not in the path of the optimal solution. A* search with a heuristic which is admissible but not consistent is complete.
- Subject : Artificial Intelligence Consider a best first search (BFS) algorithm that tries to find the optimal goal state with minimal cost. Consider heuristics h1, h2 with h1(n) > h2(n) for all states n. BFS with h1 is guaranteed to expand fewer nodes or an equal number of nodes to arrive at the optimal goal state than BFS with h2 Select one: True FalseAssuming you possess a total of 'm' dollars, and are accompanied by a group of 'n' friends. For every friend i, where i ranges from 1 to n, the price P[i] of the candy that would bring contentment to the respective friend is known. The objective is to devise a method for allocating a sum of m dollars in a manner that maximizes the number of contented friends. Propose an O(n log n) time greedy algorithm for determining the monetary allocation to be assigned to each friend.Correct answer will be upvoted else downvoted. Computer science. way from block u to obstruct v is a grouping u=x0→x1→x2→⋯→xk=v, where there is a street from block xi−1 to hinder xi for each 1≤i≤k. The length of a way is the amount of lengths over all streets in the way. Two ways x0→x1→⋯→xk and y0→y1→⋯→yl are unique, if k≠l or xi≠yi for some 0≤i≤min{k,l}. Subsequent to moving to another city, Homer just recalls the two exceptional numbers L and R yet fails to remember the numbers n and m of squares and streets, separately, and how squares are associated by streets. Be that as it may, he accepts the number of squares ought to be no bigger than 32 (in light of the fact that the city was little). As the dearest companion of Homer, if it's not too much trouble, let him know whether it is feasible to see as a (L,R)- constant city or not. Input The single line contains two integers L and R (1≤L≤R≤106). Output In case it is difficult to track down a (L,R)- consistent city…

