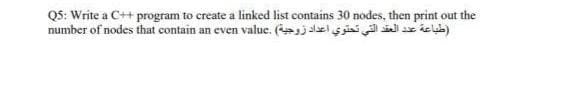
Q5: Write a C++ program to create a linked list contains 30 nodes, then print out the (طباعة عدد العقد التي تحتوي اعداد زوجية) .number of nodes that contain an even value
Q: 8.) Write a method called average that computes the average (arithmetic mean) of all elements in an…
A: ANSWER:-
Q: What impact will artificial intelligence (AI) have on the future? What Artificial Intelligence (AI)…
A: Given: We might imagine a more pleasant future for ourselves with artificial intelligence automating…
Q: Is it prudent to delegate all technical requirements to software service providers? Why do you…
A: Given: Outsourcing is the process of hiring outside workers to do certain tasks and take on certain…
Q: public static void main(String[] args) { MethodTrace trace0bj = new MethodTrace();…
A: 25 and 2
Q: Write a program that read an integer, and then finds and prints the sum of the even and odd…
A: As per the requirement program is developed. Note : As per our guidelines we are suppose to answer…
Q: Your instructor might want you to organize in groups for this project. This chapter included a few…
A: Being computer science students, we come up with the "OSI layered process" for this presentation.…
Q: string strl, str2; char ch; cin >> strl; str2 = strl; cin >> ch; str2 [0] = ch; cout What is the…
A: Output is as follows: i)Initially str1 input is taken by string Bingo ii) str2 is been assigned the…
Q: Given the following Date class public class Date { private int year; private int month; private int…
A: Answer: date d=new Date(2020,20,9);
Q: Make an algorithm and flowchart of the following problem set. 5. Draw a flowchart that computes the…
A: Since factorial of a number is : n * (n-1) * (n-2) * (n-3) * ................* 2 * 1. For example,…
Q: C7 Write a program that will take an integer array(A) and an integer value(v)as input and do the…
A: Please upvote. I am providing you the correct answer below. Please please please.
Q: Which pattern of architectural design is most suited for computer systems in which one component…
A: Introduction: MVC architecture pattern is most suited for applications in which information is…
Q: PYTHON PROGRAMMING
A: let us see the answer:- Introduction:- Python is frequently used by software engineers as a support…
Q: Love Get an input from a user with the question: Who is your favorite professor? If the input is…
A: Note :- You have not mention the language of the program so, i'm answering your question in C++…
Q: 4. Draw a flowchart which will read and print the names and individual scores of 100 students for a…
A:
Q: "Rabenstein code was used to send a message with 4 information bits, you receive 100110001, if you…
A:
Q: Question 14 What type is the most appropriate to use to hold the first name of a person? String int…
A: OPTION: String int double boolean
Q: elect the specialized uses of the EFLAGS register. which is the correct answer? you can choose more…
A: The answer is given below.
Q: Looking at a line in a listing file: 0009 EB05 jmp test the second byte in the jmp test instruction…
A: TRUE
Q: a machine is 30 bit way block set Asso
A:
Q: If a person walks up a mountain for 18 minutes at 20mph and then returns down the same path at 60mph…
A: Create the method with 3 arguments Initialized the variables use the logiclet dist = upTime * upSpd…
Q: Describe why it is difficult to create an appropriate cache replacement strategy for all address…
A: The above question is solved in step 2:-
Q: What are the two key registers used in the x86 to manage the runtime stack? ΕΙΡ SS ESP
A: Introduction A stack register is a register on the core processor of a computer that tracks the call…
Q: discuss why processes must be repeatable and measurable in order to improve them? \
A: Processes are made so as to make the a work easier.
Q: Determine whether the following propositions is true or false. if 1+1=3, then 2+2=4
A: Dear Student, In if and then statements , it is true when the if statement and then statement is…
Q: Do you believe the internet benefits those who are physically or intellectually challenged in any…
A: Internet: The Internet (or internet) is a worldwide network of linked computer networks that use the…
Q: Is it possible that employing a data/security protection solution provided by a third party can…
A: NOTE :- Below i explain the answer in my own words by which you understand it well.…
Q: Which regulatory guidelines are currently in effect for the protection of personally identifiable…
A: Explanation: Information breach notification regulations demand persons or organisations harmed by…
Q: Do Analysis Patterns play a vital role throughout the Requirement Analysis process? What are some of…
A: Analysis Pattern: A pattern is an effective solution form that has been shown to solve a particular…
Q: a) Apply Dijkstra's algorithm to the graph below to compute all the shortest paths from node "J".…
A:
Q: What are the aims of authentication? Distinguish the pros and cons of various authentication…
A: Authentication is the process of determining whether someone or something is, in fact, who or what…
Q: As a systems analyst, do you have experience with any of the following system design foundation…
A: DEFINITION OF THE ROLE OF A SYSTEM ANALYST: The systems analyst is an important player in the SDLC…
Q: 15.) What is printed by the following code fragment? int i = 3; int j = 2; while (i != 0 && j != 0 )…
A: The given code is in Java.
Q: Using matlab by the use of the derivative property discover the Fourier transform of the following…
A: The Answer is given below
Q: When returning from a procedure, the RET instruction pops the top of the stack into the register?…
A: What is RET instruction? The RET instruction transfers control to the return address located on the…
Q: During the course of the cycle in which systems are being developed, what are the key priorities of…
A: In order to develop any software, the framework which is used to define the system is known as SDLC…
Q: Select the specialized uses of the EFLAGS register. each flag is a single binary bit each flag…
A: Introduction: It is a status register that keeps track of a CPU's current condition. The flag bits'…
Q: What impact will artificial intelligence (Al) have on the future? What Artificial Intelligence (Al)…
A: AI is a cutting-edge technology that can recognize a person's facial and digit traits.
Q: Is it worthwhile to write an essay about the significance of networking in the field of information…
A: The significance of networking in information technology is as follows: Information is the…
Q: In your perspective, what function does the internet serve to serve in the lives of persons who have…
A: They have the following alternatives on the internet: Visually impaired or blind people may benefit…
Q: Describe the key distinctions between authenticating a user and authorizing them.
A: Authorization and authentication are used for security in the system because organizations contains…
Q: Make an algorithm and flowchart of the following problem set. 3. Draw a flowchart that calculates…
A: ALGORITHM: Declare the required variables. Start the loop by taking the value of loop variable from…
Q: Define Vampire attack in the sensing domain. Discuss the Carousel attack and the measures to prevent…
A: Vampire attack in sensing domain. Carousel attack and measures to prevent.
Q: Please convert below base10 decimal number into base20 number (459)base 10
A: HI THEREI AM ADDING ANSWER BELOWPLEASE GO THROUGH ITTHANK YOU
Q: Gain an in-depth comprehension of social networking blogs in addition to your knowledge of cloud…
A: Apart from data storage, social networks are now also using clouds for various other tasks. For…
Q: Question 2: Using basic identities of Boolean algebra, show that: (list the identity used at each…
A: Here is the explanation about both the Boolean expressions:
Q: now available use various forms of artific
A: Artificial intelligence (AI) is intelligence shown by machines, instead of the normal intelligence…
Q: In excel, Conditional formatting uses the feature of Select one: a. All of these b. Text…
A: The answer is given below.
Q: Directives are commands that are recognized and acted upon by the assembler but are not part of the…
A: Assembly code is code that is much more human readable than machine code. Machine code is just zeros…
Q: Create a function that takes a string of strings and replaces the same members with only numbered…
A: I give the code in Javascript along with output and code screenshot
Q: If register AL contains the value 0x 89 and register AH contains 0x74, what is the hexadecimal value…
A: Here is the explanation about AX:
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

- Write a program in three parts. The first part should create a linked list of 26 nodes. The second part should fill the list with the letters of the alphabet. The third part should print the contents of the linked list. NOT USE malloc, only use <iostream>. Do not use global variables. The use of global constants c++python programming Write a function that will insert a new value into the middle of a Linked List. INPUT: The head of the Linked List, the value to insert OUTPUT: Nothing is output RETURNED: Nothing is returnedcomplete a C program to delete the first and the last nodes of Linked List by using given functions as below: void Firstnodedelete(); void Lastnodedelete(); void createnodelist (int n); void displaylist ();
- Using C++(DSA, Topic: Singly linked list) Write a simple airline ticket reservation program. The program should display a menu with the following operations: reserve a ticket, cancel a reservation, check whether a ticket is reserved for person, and display the passengers. The information is maintained on an alphabetized linked list of names. In a simper version of the program, assume that tickets are reserved for only one flight. In a fuller version, place no limit on the number of flights. Create a linked list of flights with each node including pointer to a linked list of passengers. Note: Screen shot of working Demo will be shown.C++ question 1.) Write an iterative routine that will take a string, go through each character of the string and enqueue the character if it is a punctuation (.,?!), else toss the character. When end of string is reached, then dequeue the characters, count how many punctuations are there, then print the count. 2.) Write a routine that would receive a pointer to the top of the linked list that has an integer for each node. Change all odd integers to even by adding one. But count the numbers you changed and print the count.Write a program in three parts. The first part should create a linked list of 26 nodes. The second part should fill the list with the letters of the alphabet. The third part should print the contents of the linked list. NOT USE malloc, only use <iostream>
- (c++)write a program to insert node at specified number in single linked list? (c++)write a program to insert node at specified number in double linked list?Which of the following statement is not true about the doubly linked list? A. We can traverse in both the directions. B. It requires extra space C. Implementation of doubly linked list is easier than the singly linked list D. It stores the addresses of the next and the previous nodeint F(node<int>&p){int c=0; while(p!=0){p=p->next; c++; } return c;} This function is a. return the number of items in the linked list b. return the number of items in a linked list and destroy the linked list c. None of these d. destroy the list and free all allocated nodes
- python language Write the lines of code that will print out all of the data in a Linked List.Write a program that prompts the user to input a string and then outputs the string in the pig Latin form. The rules for converting a string into pig Latin form are described in Programming Example: Pig Latin Strings Your program must store the characters of a string into a linked list and use the function rotate, as described in Programming rotate the string.JAVA CODE PLEASE 2. Linked List Quiz by CodeChum Admin Write a function printNodes that takes in the head of a linked list and prints all the values of that linked list using a while loop. Print the values separated by a [space]->[space] Create a program that accepts 10 integer inputs. Assign each input into a node and link them in ascending order then print the linked list. Create another two linked lists: One for nodes with even numbers and the other one for odd numbers. Print them respectively using the printNodes function. Input 1. One line containing an integer 2. One line containing an integer 3. One line containing an integer 4. One line containing an integer 5. One line containing an integer 6. One line containing an integer 7. One line containing an integer 8. One line containing an integer 9. One line containing an integer 10. One line containing an integer Output Enter·number·1:·1 Enter·number·2:·2 Enter·number·3:·3 Enter·number·4:·4…

