Q5. Do only parts b) and c). Exercise 6.2.1: Design a PDA to accept each of the following languages. You may accept either by final state or by empty stack, whichever is more convenient. * a) {0n 1n n ≥ 1}. We shall accept by empty stack. Symbol X will be used to count the 0's on the input. In state q, the start state, where we have seen no l's, we add an X to the stack for each 0 seen. The first X replaces Zo, the start symbol. When we see a 1, we go to state p, and then only pop the stack, one X for each input 1. Formally, the PDA is ({q, p}, {0,1}, {X, Zo}, 8, q, Zo). The rules: 8(q, 0, Zo) = {(q, X)} 8(q,0, X) = {(q, XX)} 8(q, 1, X) = {(p,ɛ)} 8(p, 1, X) = {(p,ɛ)} b) The set of all strings of 0's and 1 's such that no prefix has more l 's than 0's. c) The set of all strings of 0's and 1 's with a n equal number of 0's and I's.
Q5. Do only parts b) and c). Exercise 6.2.1: Design a PDA to accept each of the following languages. You may accept either by final state or by empty stack, whichever is more convenient. * a) {0n 1n n ≥ 1}. We shall accept by empty stack. Symbol X will be used to count the 0's on the input. In state q, the start state, where we have seen no l's, we add an X to the stack for each 0 seen. The first X replaces Zo, the start symbol. When we see a 1, we go to state p, and then only pop the stack, one X for each input 1. Formally, the PDA is ({q, p}, {0,1}, {X, Zo}, 8, q, Zo). The rules: 8(q, 0, Zo) = {(q, X)} 8(q,0, X) = {(q, XX)} 8(q, 1, X) = {(p,ɛ)} 8(p, 1, X) = {(p,ɛ)} b) The set of all strings of 0's and 1 's such that no prefix has more l 's than 0's. c) The set of all strings of 0's and 1 's with a n equal number of 0's and I's.
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter18: Stacks And Queues
Section: Chapter Questions
Problem 1TF
Related questions
Question
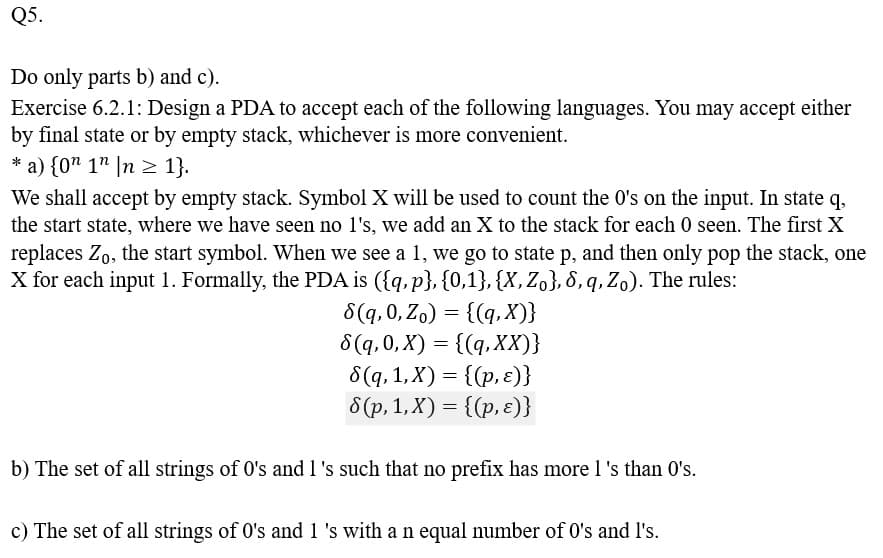
Transcribed Image Text:Q5.
Do only parts b) and c).
Exercise 6.2.1: Design a PDA to accept each of the following languages. You may accept either
by final state or by empty stack, whichever is more convenient.
* a) {0n 1n n ≥ 1}.
We shall accept by empty stack. Symbol X will be used to count the 0's on the input. In state q,
the start state, where we have seen no l's, we add an X to the stack for each 0 seen. The first X
replaces Zo, the start symbol. When we see a 1, we go to state p, and then only pop the stack, one
X for each input 1. Formally, the PDA is ({q, p}, {0,1}, {X, Zo}, 6, q, Zo). The rules:
8(q, 0, Zo) = {(q, X)}
8(q, 0, X) = {(q, XX)}
8(q, 1, X) = {(p, ε)}
8(p, 1, X) = {(p, ε)}
b) The set of all strings of 0's and 1 's such that no prefix has more l 's than 0's.
c) The set of all strings of 0's and 1 's with a n equal number of 0's and I's.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning