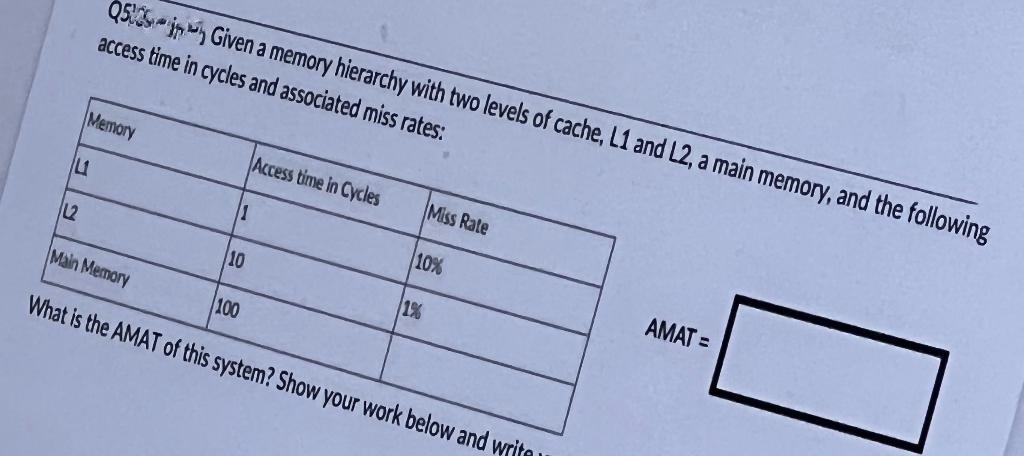
Q5:35i Given a memory hierarchy with two levels of cache, L1 and L2, a main memory, and the following access time in cycles and associated miss rates: Memory Access time in Cycles Miss Rate L 11 10% AMAT = L2 10 1% Main Memory 100 What is the AMAT of this system? Show your work below and write
Q: Which one of the following is not true? a) kernel remains in the memory during the entire computer…
A: In this question we have to understand what is not correct about the kernel from the given…
Q: Specifically, what do you mean by "multiple processes"? I'm confused. Are there any other words you…
A: Multiple processes means several processes, multiple action, numerous process.
Q: mart phone's user interface is a team effort. Is UI design hard? Describe what's done. How do you…
A: Introduction: Below the describe How do you determine whether an item or category list has been…
Q: What are the key distinctions between static variables and instance variables?
A: Static variables and Instance variables: When an object is formed using the 'new' keyword, instance…
Q: How and when does the debugging process take place?
A: The answer is given below:
Q: In SCSI disks used in high end PCs, the controller maintains a list of _________ on the disk. The…
A: Find the required answer given as below :
Q: What are the key characteristics that differentiate a DDBMS from a heterogeneous DDBMS? What could…
A: The above question that is key characteristics that schould differentiate a DDBMS from a…
Q: Assume a MARIE assembly program has an instruction JNS Subr stored at hex address 108 and symbol…
A:
Q: Q2: How can several variables be written in successive lines as outputs with one commands?
A: As per the question statement, We need to find the correct option.
Q: IN C# (reject if you can't do C# please): Write an application that runs 1,000,000 games of craps…
A: public class GameOfCraps {private Random randomNumbers=new Random();private enum Status{Continue,…
Q: The two steps the operating system takes to use a disk to hold its files are _______ and ________
A: A hard disk must be partitioned and formatted before it can be utilized.Partitioning defines the…
Q: What distinguishes an interpreter from a compiler?
A: Language Processors A specific translator system that converts source code (also known as "source…
Q: The operating system maintains a ______ table that keeps track of how many frames have been…
A: In this question we have to understand that what table Operating System keeps track of related to…
Q: The _________ presents a uniform device-access interface to the I/O subsystem, much as system calls…
A: let's see the correct answer to the question
Q: What are the benefits that come with using a cache that does not block?
A: What are the benefits that come with using a cache that does not block answer in below step.
Q: A programmer's perspective should be used to justify why deep access is superior than shallow…
A: According to a programmer or software perspective deep access is superior than shallow access, here…
Q: Explain the distinction between typed variables that are explicitly declared and typed variables…
A: Introduction: Implicit in programming refers to anything that other code does for you behind the…
Q: Create a program that asks the user for any number. Then rounds off the number into its nearest…
A: The code implementation in C++ is given below. The Algorithm: The user is prompted to enter a…
Q: There's no way that one procedure could be delayed in the middle of completing it. Please explain…
A: One Step at a Time: A single process refers to any color service that may be accomplished in only…
Q: Make a list of the core software and hardware needs for your computer lab if you are a network…
A: Given: The requirements of your laboratory will assist you in determining the specific kinds of…
Q: It is important to convey how tough it is to create user interfaces on a smart phone to a software…
A: NOTE :- Below i explain the answer in my own words by which you understand it well. Any point…
Q: Given a flow network as below with S and T as source and sink (destination). The pair of integers on…
A: It is defined as a simple path from source to sink which do not include any cycles and that pass…
Q: Q2: If the matrix B is defined in MATLAB as following: 2 -1 5 3 7 10 4 9 B = -3 7 8 5 1 4 6 12…
A: A matrix is a table with n rows and m columns where size of matrix is given by mxn. The number of…
Q: Was there anything else concerning the creation of a web-based application that you need further…
A: Web-based application: A Web application (Web app) is a software that is stored on a distant server…
Q: The postfix form of the expression (A+ B)*(C*D- E)*F / G is? a) AB+ CD*E – FG /** b) AB + CD* E – F…
A: The given question are multiple choice selected question.
Q: Make sure you're not just arguing for the benefits of deep access over shallow access because of…
A: Diversity of markets, customers, ideas, and talent is driving the need for inclusion as a new…
Q: Answer both questions: A-Write a program to display the name of day by giving the day number as the…
A: read a value convert it into int using Integer.Parse() if x=1 then display “Saturday” else if x=2…
Q: Let's say you're using a code editor and you want to position your mouse cursor on a jagged line and…
A: A text editor with a focus on software development: A source code editor can be used as a standalone…
Q: 1. Draw circuit in Figure 1 in Deeds. E A B [ C D F C d --X
A:
Q: hardware and software to be installed in a computer system, what are the most essential requirements
A: Introduction : Hardware requirements : * Processing power : The faster you can do that, the…
Q: It is important to think about both the benefits and the drawbacks of having global connection.
A: The above question is solved in step 2 :-
Q: 6,8,2,3,1,4 Draw a binary search tree by inserting the above numbers from left to right.and then to…
A: Here in this question we have given some sequence of number .with these number we have to draw…
Q: -True or False: In TCP, FIN segment can be used only to carry control data?
A: SYN and FIN are the only controls that require this protection, and these controls are only used for…
Q: knesses and criticisms of Java. Choose one and discuss what the weakness/criticism entails. Would…
A: Introduction: The language is basic and straightforward to write. The best part about Java is that…
Q: For an effective operating system, when to check for deadlock? a) every time a resource request is…
A: For an effective operating system, when to check for deadlock every time a resource request is made…
Q: Q2: Choose the correct MATLAB command to plot the given function with a black solid line and circle…
A: Please refer below for your reference: The correct option isplot(x,y,'-ko')
Q: The prefix form of A-B/ (C * D ^ E) is? a) -/*^ACBDE b) -ABCD*^DE c) -A/B*C^DE d) -A/BC*^DE
A: The algorithm for infix to prefix conversion. Reverse the infix expression. Obtain the postfix…
Q: What are the numerous different ways that application software may be obtained?
A: The solution to the given question is: System requirements : To run applications effectively , your…
Q: B-Write a code program to find multiplies of all even numbers from 1 to 100 us loop
A: Find the required code in VB given as below and output : As per company guidelines we are supposed…
Q: What are the disadvantages of arrays? a) Data structure like queue or stack cannot be implemented b)…
A: Please refer to the following step for the complete solution of the problem above.
Q: How do you connect two PCs to a network that runs on Unix, and what steps are required in the…
A: You will need to make use of protocols such as FTP, Samba, and Telnet in order to connect to…
Q: Explain the role of the following in web design and development; i) Artist/graphic designer. ii)…
A: Please find the detailed answer in the following steps.
Q: Using Switch case: Write a program that asks the user to input a number from 1 to 3000. Then, print…
A: C++ is the general purpose of the programming languages can be used to develop the high level of…
Q: Create Rock Paper Scissor Game using tkinter and any other necessary Python packages.
A: Tkinter is one of the Python-based libraries used to create and develop Desktop User interfaces and…
Q: In the course of designing an information system, what causes scope creep?
A: let's see the correct answer of thequestion
Q: To perform (X * Y) in Assembly, if the operand (Y) to the MUL instruction i word-sized, where should…
A: The correct option is AX for the above MCQ. The correct option is None of the choices for the…
Q: What exactly does it mean to say that something is computer hardware?
A: The word "computer hardware" refers to all tangible components that make up an analog or digital…
Q: How do you instantiate an array in Java? a) int arr[] = new int(3); b) int arr[]; c) int arr[] = new…
A: An explanation is given below:
Q: For patterns that include frequent reuse, either a low or high reuse factor is recommended. Why not…
A: The Answer start from step-2.
Q: principle states that programs, users, and even the systems be given just enough privileges to…
A: principle of least privilege states that programs, users, and even the systems be given just enough…
Step by step
Solved in 2 steps

- Assume that we have a computer with a cache memory of 512 blocks with a total size of 128K bits. Knowing that the computer uses a word addressable mode and the format of the memory address as seen by the Fully associative cache scheme is as shown below, answer the below questions: Fully Associative Cache Format 19 5 1- How many words do we have in each cache block? 2- What is the size of each word? 3- What is the size of the main memory? 4- How many blocks are there in the main memory? 5- Draw the format of the memory address as seen by the Direct Mapped Cache scheme, showing the fields as well as their sizes.A computer is using a fully associative cache and has 216 bytes of main memory (byte addressable) and a cache of 64 blocks, where each block contains 32 bytes. a. How many blocks of main memory are there? b. What will be the sizes of the tag, index, and byte offset fields? c. To which cache set will the memory address 0xF8C9(hexadecimal) map?Q2) Given a physical memory of 8 k and a cache memory of 512 bytes with block size 64 bytes. The system uses set associative mapping with set size 2 lines per set A- How many sets we will have in the cache memory b-B- How the address will be split to indicate tag, set no, and offset c-Calculate the cache address (set, line no, and offset) that physical address 140 will be mapped.
- Assume that we have a computer with a cache memory of 512blocks with a total size of 128K bits. Knowing that the computer uses a word addressable mode and the format of the memory address as seen by the Fully associative cache scheme is as shown below, answer the below questions: Fully Associative Cache Format 1- How many words do we have in each cache block? 2- What is the size of each word? 3- What is the size of the main memory? 4- How many blocks are there in the main memory? 5- Draw the format of the memory address as seen by the Direct Mapped Cache scheme, showing the fields as well as their sizes.A 32-bit computer has a memory of 256 KB and a cache line size of 64 bytes. The memory cache access time is 5ns. This cache is 4-way associative and use LRU as a replacement algorithm. a) What is the number of lines and sets of this memory cache? b) What is the block size transferred between the cache memory and the main memory? c) If the time to transfer a line to cache memory is 200 ns, what is the hit ratio needed to obtain an average access time of 20 ns?Show work and type answer please. Suppose a computer using fully associate cache has 2G Bytes of main memory and a cache of 256 Blocks, where each cache Block has 8 Words, and the Word Size is 2 Bytes. a. How many blocks of main memory? b. What is the format of a memory address as seen by the cache? c. To which cache block will the memory reference 00001C4A in Hex?
- A computer of 32 bits has a cache memory of 64 KB with a cache line size of 64 bytes. The cache access time is 20 ns, and the miss penalty is 120 ns. The cache is 2-way associative. a) What is the number of cache lines? b) What is the number of cache sets? c) What is the number of lines per set? d) Draw a scheme of this cache. e) Calculate the time to read a word in case of miss.Q2) Given a physical memory of 8 k and a cache memory of 512 bytes with block size 64 bytes. The system uses associative mapping with set size 2 lines per setA- How the memory address will be split to indicate tag, and offset B- What is the size of tag directory.You have a byte-addressable virtual memory system with a two-entry TLB, a 2-way set-associative cache, and a page table for a process P. Assume cache blocks of 8 bytes and page size of 16 bytes. In the system below, main memory is divided into blocks, where each block is represented by a letter. Two blocks equal one frame. Given the system state as depicted above, How many bits are in a physical address? Explain.
- You have a byte-addressable virtual memory system with a two-entry TLB, a 2-way set-associative cache, and a page table for a process P. Assume cache blocks of 8 bytes and page size of 16 bytes. In the system below, main memory is divided into blocks, where each block is represented by a letter. Two blocks equal one frame. Given the system state as depicted above, Given virtual address 0x06 converts to physical address 0x36. Show the format for a physical address (specify the field names and sizes) that is used to determine the cache location for this address. Explain how to use this format to determine where physical address 0x36 would be located in cache. (Hint: Convert 0x36 to binary and divide it into the appropriate fields.)Assume we have a computer with 512 blocks of cache memory with a total capacity of 128K bits. Answer the following questions knowing that the computer operates in a word addressable mode and that the format of the memory address as perceived by the Fully associative cache scheme is as shown below: Cache Format with Full Associativity 19 5 1- How many words are in each cache block? 2- How big are the letters in each word? 3- How large is the primary memory? 4- What is the total number of blocks in main memory? 5- Draw the memory address format as observed by the Direct Mapped Cache technique, including the fields and their sizes.A computer system has 32 address lines and 16K bytes cache. Each cache block size is 32 bytes. For the following cases, (a) a direct mapped cache (b) a fully associative cache (c) a 4-way set associative cache (1) How many comparators are required in each cases? (2) When the CPU references an address 0xABCDEF12, what is the tag value for each cases?

