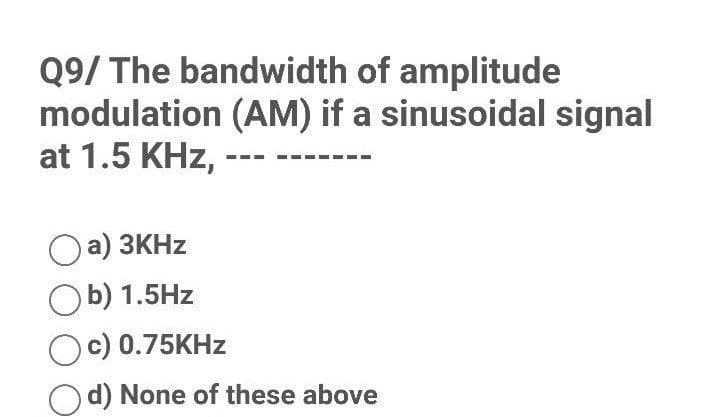
Q9/ The bandwidth of amplitude modulation (AM) if a sinusoidal signal at 1.5 KHz, a) 3KHz Ob) 1.5Hz Oc) 0.75KHz d) None of these above
Q: Why do Chrome OS devices need less internal storage than machines running other desktop operating…
A: Introduction: OS (Operating System): The word "operating system" refers to the software that serves…
Q: Task 5: Write and execute the command to retrieve the item ID, description, invoice number, and…
A: We need to retrieve the item ID, its description, invoice number, and quoted price for all…
Q: Is it possible to explain how policy voids (computer ethics) arise? Detailed explanations are…
A: Computers are remarkable innovations that offer some unique ethical questions. In this essay, I will…
Q: 4. For FLASH memory, what would you say: a. Which memory type is it similar to: EPROM or ROM or RAM…
A: Below is the answer to above question. I hope this will be helpful for you...
Q: ss Point: """ A point in a two-dimensional coordinate plane """ def…
A: The move method in WindTurbine calls the move method from Rectangle, which causes the turbine's…
Q: Why is segmented memory address translation preferable to direct translation, and how does it…
A: A process known as segmentation is a visual process that creates address spaces of various sizes in…
Q: Discuss the importance of network security to you. Is the rationale for its importance different…
A: The three conditions that a network must meet in order to be successful and efficient are as…
Q: An example of a real-world SQL database, as well as an explanation of the database, should be…
A: The question is to give an example of a real-world SQL database, as well as an explanation of the…
Q: What data type in C# should I use in 1.0f / 2
A: What data type in C# should I use in 1.0f / 2
Q: 1 / 2 What is the correct data type that the above expression evaluates to in C#?
A: Find Your Answer Below
Q: For the purpose of offering customers the most value for their money, an airline sought a system…
A: The Pareto Principle is almost universally used. The income generated by 20% of your customers…
Q: Are digital signatures as secure as traditional signatures, or are they more or less so?
A: Answer:
Q: Explain the steps needed in changing the context.
A: Introduction: Context switching is used to save the context or state of a process so that it may be…
Q: Identify the phases of the Cyber Kill Chain model and discuss the technical, management and…
A: According to the information given:- We have to define the phases of the Cyber Kill Chain model and…
Q: Explain the AI Turing test in a nutshell? Briefly describe the role of the Turing test in the…
A: The Turing Test is a method of determining whether or not something Turing's test, coined by Alan…
Q: Let G be the grammar SaA, A Abb b. Show that G is an LR(0) grammar.
A: LR parser or LR(0) parsing is the bottom-up syntax analysis method used in the case pf large class…
Q: Complete this code using Python m1 = [] #Matrix 1 m2 = [] #Matrix 2 #Write a function that will…
A: Code: m1 = [] #Matrix 1m2 = [] #Matrix 2 #Write a function that will return the addition of Matrix A…
Q: Write a program that creates a 32-element array of random integers all from 1 to 100, inclusive.…
A: Please check the step 2 for required code and step 3 for sample output.
Q: Homework 12. Use NAND gates, NOR gates, or combinations of both to implement the following logic…
A:
Q: List the three types of cybercrime and the methods taken to prevent each of them. Give an example of…
A: Intro: Cyberdefense protects computers, servers, mobile devices, electronic systems, networks, and…
Q: pe the size of the memory in bytes. 2. A memory system is required that has 4 million locations. At…
A: We are given a memory system that has 4 million locations and 16 bit world size. We are asked about…
Q: In terms of system maintenance, what are a splitstream upgrade, a patch, a release, and a version?
A: System maintenance It is a system development process and is done by organizations and Individuals.…
Q: computer science - A digital camera captures light on a light-sensitive sensor.
A: Introduction: Standardization uses a number to represent sensitivity to lightweight, and this value…
Q: ۱۰۰۲۵ ۲۰۲۳/۰۵/۳۵ : The serial data input waveform (Data in) and data select input (So and S₁) are…
A: Answer is given below.
Q: It is everyone's responsibility to combat dangerous hacking. Do you believe that to be true? What…
A: Below is the answer to above question. I hope this will be helpful for you...
Q: design an algorithm to find all the common elements in two sorted lists of numbers. For example, for…
A:
Q: What exactly is Database as a Service (DaaS)? What are the benefits and drawbacks of implementing…
A: Data as a service (DaaS) is a data management strategy that uses the cloud to deliver data storage,…
Q: speed=input("Enter your speed in mph: ") speed = int(speed) distance = input("Enter your distance in…
A:
Q: which of the following can be determined from Turnitin's Index? a) How much plagiarism was committed…
A: Turnitin is an authentic testing and anti-cheating service that checks your writing for quote errors…
Q: Q. implement a python program to short array [64, 34,25,12,22,11,98] using merge sort.
A: It is required to write a python program to sort the given array using merge sort. Merge sort uses…
Q: Some of the problems in designing an information system architecture for this new service should be…
A: Infrastructure and architecture of the information system: A well-designed information system…
Q: The name "SMA" refers to the connection used in SMA connectors.
A: SMA refers to (SumMiniature version A) the the connection used in SMA connectors. This is connectors…
Q: What data type in C# should I use in 1/2
A: Answer: C # is a tightly typed language. It means we have to declare the variance that reflects the…
Q: What role do databases play in three-tier apps?
A: Intro Three-tier application: The most common client-server design in relational database…
Q: A code in c++ or python A program that asks you to enter the name of a movie or series, and then…
A: #using python#asking user to enter movie or series namename = input('Enter name of a…
Q: In terms of system maintenance, what are a splitstream upgrade, a patch, a release, and a version?
A: Introduction: Upkeep of the system System maintenance is used to meet the needs of users and the…
Q: 3- Implement onContextItemSelected(). When the user selects a menu item, the system calls this…
A: It is defined as a floating menu that appears when the user performs a long-click on an element. It…
Q: Please help me with the errors I am e having the program below. There are two parts of the program.…
A: • Define EncryptMsg() method means to encrypt the original message. • Define DecryptMsg() method…
Q: What distinguishes a Network layer protocol from a Transport layer protocol?
A: Introduction: The network layer and the transport layer are next to one another. Different tasks are…
Q: ely does it mean when someone says they are "openi
A: Introduction: Below the describe precisely does it mean when someone says they are "opening a file"?
Q: Do you rely more on algorithms or heuristics while addressing a problem? The benefits of each…
A: The algorithm is defined as the set of instructions for accomplishing a task. For example, An ATM…
Q: Is the use of the QR Code system going to be beneficial or detrimental to the services provided by…
A: QR Code system: A rapid response code, often known as a QR code, is a specific kind of…
Q: Are there any software engineering principles that go unnoticed? explain?
A: There is more to software than just a collection of instructions for a computer. A piece of code…
Q: Q. implement a python program to short array [64, 34, 25, 12, 22,11,98] using merge sort.
A:
Q: Why we need Gradle in Android
A: You were probably using Eclipse for your programming before Android Studio, and you didn't know how…
Q: In your opinion, which network topologies are feasible?
A: Network topologies represent the physical configuration of networks. Generally speaking, there are…
Q: Are you of the opinion that error correction is most effectively implemented in wireless…
A: Given: Yes," error correction works best with wireless applications or networks and is seen as a…
Q: Which characteristics are absolutely necessary for computerised systems to possess, and what are the…
A: A computerised system is one in which computers do all of the labour and business processes.It's a…
Q: Is it more harder to design Graphical User Interfaces (GUI) with pixel coordinates?
A: Intro Graphical User Interfaces (GUI) A graphical user interface (GUI) is a user interface that…
Q: Is there a way to make better use of computational decision-making?
A: In response to the question Computational choice technology aids in the fulfilment of the desire.…
Step by step
Solved in 2 steps

- 225. Signal to Noise Ratio is the ratio of the two a. Signals b. Powers c. Noise d. Frequencies163. In the case of Phase Modulation (PM), the value of beta (β) is a. Lower b. Greater c. 0 d. Infinity224. The difference in the delay of the signal may create a difference in a. Phase b. Frequency c. Period d. Decibel
- Subject - computer networking The digital signal is to be designed to permit 160 kbps for a bandwidth of 20 kHz. Determine (a) number of levels and (b) S/N ratio.In _______ encoding, the duration of the bit is divided into two halves. The voltage remains at one level during the first half and moves to the other level in the second half. The transition at the middle of the bit provides synchronization. a. Manchester b. differential Manchester c. both (a) and (b) d. neither (a) nor (b)This is an encoding technique which has three voltage levels namely +, - and 0 a. Polar Encoding b. Unipolar Encoding c. NRZ Encoding d. Bipolar Encoding
- In _______ encoding, the duration of the bit is divided into two halves. The voltage remains at one level during the first half and moves to the other level in the second half. The transition at the middle of the bit provides synchronization.In BPSK the bit rate is equal to the baud rate a. True b. FalseIn ________, the amplitude of the carrier signal is varied to create signal elements. Both frequency and phase remain constant. a. ASK b. PSK c. FSK d. QAM
- Quadrature amplitude modulation (QAM) is a combination of ___________.137. Phase shift keying (psk) method is used to modulate digital signals at 9600 bps using 16 levels. Find the line signaling speed (i.e., modulation rate) a. 1200 bands b. 2400 bands c. 3600 bands d. 4800 bandsAn analog signal carries 8 bits per signal element. If 6000 signal elements are sent per second, find the bit rate.

