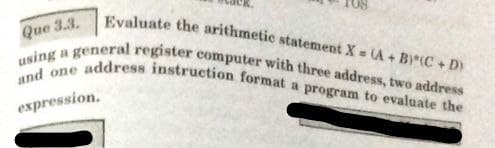
Que 3.3. and one address instruction format a program to evaluate the using address instruction format a program to evaluate the a general register computer with three address, two address Evaluate the arithmetic statement X - A + BI(C + D expression.
Q: Look for 5 IoT Applications. Provide an image including a short description for each. Please provide...
A: Given: Look for the following 5 Internet of Things (IoT) applications. For each, provide an image an...
Q: How do you get the top piece out of a stack?
A: As given, we need to find out, how to get the top element out of stack.
Q: create a program that will compute the area of rectangle given the formula area= length x width. len...
A: SUMMARY: - Hence, we discussed all the points.
Q: Create a DHCP report (Dynamic Host Configuration Protocol). The report should include a literature r...
A: Introduction: The Dynamic Host Configuration Protocol (DHCP) is a client/server protocol that automa...
Q: Prove the following laws of logical equivalence using truth tables
A: p q r p->q q->r (p->q)->r p->(q->r) F F F T T F T F F T T T T T F T F T F F ...
Q: There are three steps in the instruction cycle.
A: Instruction cycle :- The instruction cycle is related to the CPU (Central recycling unit), a list of...
Q: Justify the following statement with the help of a suitable example: “In a class hierarchy of severa...
A: A virtual function is a member function which is declared within a base class and is re-defined or o...
Q: After calling an MS-DOS I/O function, which flag tells you that something went wrong?
A: Introduction: Most of the early versions of the Microsoft Windows operating system were nothing more...
Q: How to to do a flowchart for this project? Project 1: Caesar Cipher Assignment Overview In this assi...
A: Code: def enc():text,s=input("Enter the string to be encoded: "),int(input("Enter the shift value(1-...
Q: can you tell me the manage mode of adobe?
A: can you tell me the manage mode of adobe?
Q: Chomsky Hierarchy is an useful hierarchy of different class of languages in Theory of Computation. W...
A: You answer is given below with an explanation.
Q: Assume a computer has two network interface cards, NIC1, a Wifi USB, and NIC2, an on-board Ethernet....
A: The answer is given below:-
Q: waterfall model ans expalin its advantages and disadvantages? Correct answer will be upvoted
A:
Q: How many cells are in RAM in a 32-bit computer?
A: A 32-bit system can access 232 different memory addresses, i.e 4 GB of RAM or physical memory ideall...
Q: What is Linux Shell? What types of Shells are there in Linux?
A: The answer is given below.
Q: What is copying power program?
A: There is no such thing as copying power program. I think it is coping power program. ------------ Th...
Q: At any given time, how many primary partitions can be active?
A: Introduction: An operating system may be installed on a primary partition. The operating system is ...
Q: Although it will no longer be used, please leave the earlier global variable with the initialized da...
A: I have answered this question in step 2.
Q: Source papers, according to some system analysts, aren't required. They claim that all data should b...
A: Answer : Data management : The separate disciplines that are part of the overall data management pro...
Q: What effect does declaring a variable have on memory allocation?
A: answer is
Q: Source papers, according to some system analysts, aren't required. They claim that all data should b...
A: Introduction: System requirements define the configuration that a system must have for hardware or s...
Q: Specify the different types of interfaces.please help me write 1 page
A: Introduction: Here we are asked to specify different types of Interfaces.
Q: Database manipulation involves specifying the data types, structures, and constraints of the data to...
A: It is Data Definition which involves specifying the data types, structures, and constraints of the d...
Q: Taisie fons that satisiys cacchn of the following conditional statement;s If (A= 1) then (R2 R3) els...
A: Since you have asked multiple questions, so we have provided the answers for the first three questio...
Q: Implement the Boyer Moore algorithm from scratch. Test it and plot c against n and m where n is the ...
A: In computer science, pattern search is a critical problem. Pattern searching methods are used to dis...
Q: Python) Given the code that reads a list of integers, complete the number_guess() function, which sh...
A: import random def number_guess(i): num= random.randint(1,100) if i< num: printf(i, ...
Q: WHAT ARE THE OBSTACLES TO THE GLOBAL ADOPTION OF CRYPTOCURREr
A: given - what are the obstacles to the global adoption of cryptocurrency?
Q: What is the binary encoding of the following RISC-V assembly instruction? Please write your answer a...
A:
Q: What is the total delay of the new packet in arriving at Router B, i.e., how long does it take the ...
A: Given: Length of packet (L)=15,000 Transmission rate (R)= 0.05 mbps Number of packet per wave (N)= 1...
Q: Computer Science code in c++ please .Do NOT use ANY string/character manipulation or arithmeti...
A: Given The answer is given below.
Q: 4. When children visit play zone, at the entry gate their height and age should be checked. He/she s...
A: 4. Algorithm: Start Read height(in cm) and age of child If age<8 and height>122, display "All...
Q: What is the level of node 17, and node 11, respectively? Insert integers 11, 22, 15, 44, 6, 9, 3, 3...
A: Basically we know that BST is defined as the Binary Search Tree. This BST concept is mainly handled ...
Q: When a person uses a regular modem to make a connection to an Internet service provider through POTS...
A: Given: To choose the correct option.
Q: Provide two benefits of implementing virtualization on a network as a networking technology.
A:
Q: Which instruction compares two floating-point numbers before the P6 family?
A: In processors prior to the P6 family FCOM, or FCOMP instruction compares two floating-point values.
Q: Is Public Outrage Fueling the Big Data Market? What are the two advantages and two disadvantages of ...
A: The solution to the given problem is below.
Q: The temperature alone is not enough to provide the answer. Other factors including wind speed, relat...
A: Following is the answer:
Q: drawbacks of reusing in system analysis.
A: Before understanding benefits and drawbacks , we must understand what is Reusing in system analysis....
Q: Kindly type this. This is the answer of one of your expert here. But I can't understand his handwrit...
A: Below I have Re-typed the Same Answer
Q: Given num_rows and num_cols, print a list of all seats in a theater. Rows are numbered, columns lett...
A: Given :- Given num_rows and num_cols, print a list of all seats in a theater. Rows are numbered, col...
Q: Before 350 companies are awarded ISO 9002, few officers are assigned to check all the items manufact...
A:
Q: Please answer all 4 questions in detailes. Number 3 is already answered it needs graph which I alrea...
A: Please upvote me Please. i need it badly. I am providing you the correct answer. 1. Algorithm...
Q: In physics, an object that is in motion is said to have kinetic energy. The follow. formula can be u...
A: PROGRAM EXPLANATION(C++): Include the header file. Define the main function. Take the mass of the o...
Q: 11111101 NOR 1000001 0
A: Introduction: NOR Gate: The Logic NOR Gate output is only true when all of its inputs are false, oth...
Q: Define a splitstream upgrade, patch, release, and version in terms of system upkeep.
A: Introduction: System maintenance is used to help users and organizations achieve their objectives. ...
Q: Instructions employeepay.py 1 # Get the hourly rate An employee's total weekly pay equals hour rate=...
A: just see the below code #code #get the hourly ratehour_rate = float(input("hourly wage:")) #get num...
Q: Write a Java program to display the three highest monthly speeding fines recorded for four different...
A: Algorithm: Start Store the given speeds in 2d array named speeds Store cities names in 1d cities ar...
Q: Given the class SinglyLinkedtist add method colled oountDuplcates that returme the number of duplica...
A: The function implementation is given in the below step.
Q: Which types of devices use NFC transmissions? In a SOHO network, which types of devices are typicall...
A: 1.) The smartphones devices can use NFC transmission. So, the answer is smartphones.
Q: What is -7 in four-bit two's-complement representation? Ex: 0101
A: Please find the solution below
Step by step
Solved in 2 steps with 1 images

- If a microprocessor has a cycle time of 0.5 nanoseconds, what’s the processor clock rate? If the fetch cycle is 40% of the processor cycle time, what memory access speed is required to implement load operations with zero wait states and load operations with two wait states?Provide the type, assembly language instruction, and binary representation of instruction described by the following MIPS fi elds: op=0x23, rs=1, rt=2, const=0x43 Write an assembly language program in 8086 for the addition and average of a series of 8 bit numbers 52H, 13H, 12H, 23H, 1AH, 2B. Program must consider the following specifications (i) Use a conditional jump instruction to implement the logic. (ii) Store the result from memory address 5000 (iii) Display the result on the CRT screen of a microcomputer
- Evaluate the statement below and show how to compile it into MIPS (Million Instructions Per Second) code by using instruction set machine of three-address, two-address, and one-address. F = (X+Y) (VW)Computer Science Consider that the processor fetches the following instruction word: 00010001000101011111111111110001 Assume that the initial values of GPRs are the same as their register numbers. Q). What are the outputs of the sign-extend and its subsequent “Shift left 2” unit for this instruction word?a) Convert 89806910h from machine language to its corresponding assembly language.Show all of your workings. (b) Suppose the instruction MOV DI, [BP+42h], appears in a program. What is its machinelanguage for the given instruction?
- Computer Architecture (Already submit this question, but I think I got wrong solution) Consider a computer that has a number of registers such that the three registers R0 =1500, R1 = 4500, and R2 = 1000 Show the effective address of memory and the registers’ contents in each of the following instructions 1. ADD (R1), R2 2. MOVE 500(R0), R2 3. ADD (40), R1 4. SUBTRACT (5000), R2 5. ADD #30, R2Convert 8B836921h from machine language to its corresponding assembly language. Show ALL of your workings. Suppose the instruction MOV [BX+219], DL, appears in a program. What is its machine language equivalent in octal format?Computer Science c = (a + b) /(a - f) d = c /( a * b – a) e = a * (c + d) Write the assembly to do the following statements for each of the following architectures. Use the least number of instructions. a) Stack ISA b) GPR (0,2) c) GPR (0,3)
- 2. Suppose we have two implementations of the same instruction set architecture.Computer A has a clock cycle time of 250 ps and a CPI of 2.0 for some programand computer B has a clock cycle time of 500 ps and a CPI of 1.2 for the sameprogram. Which computer is faster for this program and by how much?Assume that the state of the 8088’s registers and memory just prior to the executionof each instruction in problem 15 is as follows: * in photos*What result is produced in the destination operand by executing instructions (a)through (k)? *only b,c,e,g* b) ADC SI, AX(c) INC BYTE PTR [0100H] (e) SBB DL, [0200H] (g) NEG BYTE PTR [DI]+0010HDevelop a hypothetical architecture with illustrative instruction and data formats, instruction sets, etc., explain the instruction and machine cycles step-by-step by developing a short program (at least, with two arithmetic operations, three logic operations, three memory or two L/C) operations) and by indicating the corresponding register operations. All architectural, etc., selections must to be justified sufficiently.

