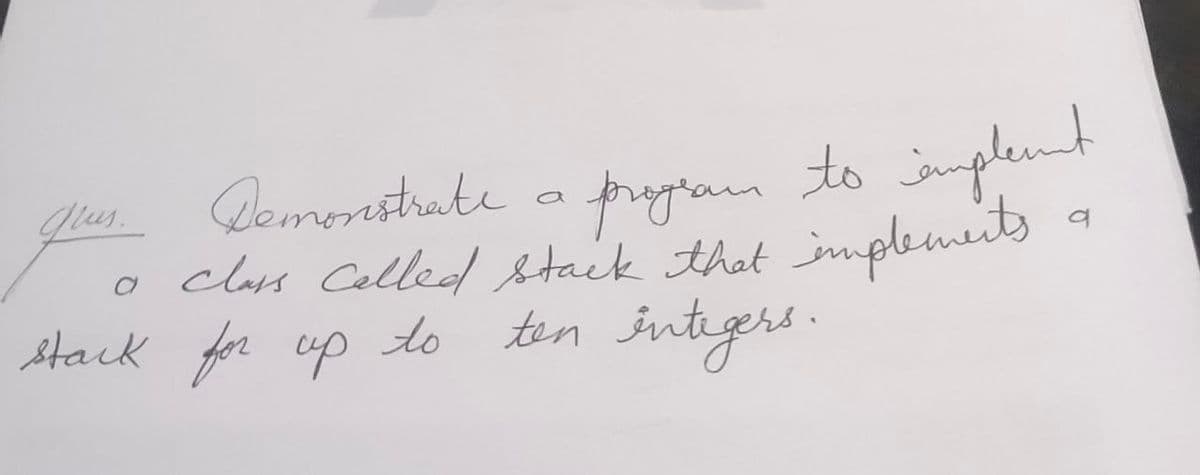
glus. a Demonstrate a program to implent class called stack that implements ten stack for up for up to کہا تھا کہ اگر q
Q: The software development life cycle (SDLC) and approaches now have a significant knowledge gap…
A: SDLC is a process, while Agile is a methodology, thus both SDLC versus Agile must be taken into…
Q: What exactly is the Transmission Control Protocol (TCP)?
A: Introduction: TCP is a network protocol that outlines how to create and sustain a network…
Q: Any values for dynamic characteristics are indicated in instrument data sheets and only apply when…
A: Any values for dynamic characteristics are indicated in instrument data sheets and only apply when…
Q: Talk about the process of creating a new system.
A: Process of a System: Describe a procedure. Processes are all the interconnected actions (components)…
Q: What are the many kinds of software maintenance there to choose from?
A: Examples of software maintenance include: Remedial Maintenance Software fault rectification…
Q: Computer architecture and computer object-oriented design are not the same thing. There is a…
A: Computer Architecture is a practical depiction of necessities and plan execution for the different…
Q: Consider the impact of the personal computer and the Internet on system design.. In order to back up…
A: Introduction: There have been two significant technology advancements that have an impact on system…
Q: Discuss three popular RAID storage systems.
A: Answer: Introduction: RAID stands for Redundant Array of Independent Disks. For the system's two or…
Q: 2. The Lucas series is series based on adding two previous terms defined as follows L₁ = ifn=0 ifn=1…
A: Program: #function definition def L(n): #if n is 0 return 2 if n==0: return 2 #if n is 1 return 1…
Q: Give some examples of how Cleanroom Software Engineering might assist a company. Explain why…
A: Cleanroom Software Engineering: Cleanroom software engineering is a theory-based, team-oriented…
Q: PCs using Chrome OS need less internal storage space than those running rival desktop operating…
A: Android Wear Chrome is a very quick and lean operating system. Because Chrome solely provides Web…
Q: he usable life of a system is nearing its end, therefore what are some signs of this?
A: Answer:- The capacity of a system to provide steady data streams is the first sign of its remaining…
Q: which one is correct 1) Hysteresis is found most commonly in instruments, such as a passive pressure…
A: As per my knowledge. First one is correct I am giving you the reason behind this
Q: What is error control and how does it work?
A: Error control is a method of identifying and fixing data blocks during communication.
Q: capsulation and abstraction d
A: CORRECT ANSWER: OPTION 3 (binding and hiding respectively) SUMMARY Encapsulation binds data, and as…
Q: What are the two requirements that a PDA must meet in order to be deterministic?
A: We are going to understand what are the conditions that needs to be fulfilled for a PDA to be…
Q: Give an explanation of how neural networks "learn."
A: Neural networks, also known as artificial neural networks (ANNs) or simulated neural networks…
Q: List the factors for determining whether a system's usefulness has expired.
A: Given: Every program will eventually reach a point in its timetable when it will repeat itself.…
Q: Here, software development and academic writing are contrasted to see which is more efficient. When…
A: Differences: The objective is achieved by a software developer writing computer code. Research,…
Q: Demonstrate your understanding of machine learning. When it comes to machine learning, how can you…
A: Machine learning: Machine learning is a method used in artificial intelligence that enables…
Q: Because of this, users may choose to input data through the command line rather using the graphical…
A: Introduction: GUI is faster than a CLI because it is visually intuitive. In a command-line…
Q: Describe the influence that software evaluation, control, and change methods have had on the amount…
A: INTRODUCTION: Program upkeep is the method of changing, adjusting, and upgrading program to keep up…
Q: Is there a distinct meaning to the phrase "interdependence" in relation to other terminologies used…
A: Interdependence is a state: In which two or more things depend on or rely on each other in the same…
Q: A potentiometer R5 is put into the apex of the bridge shown in Figure bellow to balance the circuit.…
A: According to the information given:- We have to choose the correct option to match the value of R6.
Q: How and why do we need structured programming in today's world? What are the most important concepts…
A: The paradigm of structured programming: Which is also known as standard programming, is a kind of…
Q: ASSUME 6.2 IS DONE Write a SQL statement to get the list of all the tasks that started after…
A: Let's understand step by step : 1. Here given that 6.2 is already done so 6.2.1 : Task table is…
Q: Has the introduction of new technology increased or decreased the productivity of humans?
A: To clarify the phrase, "Did new technology aid in making humans more productive, or have they…
Q: Incremental delivery is an iterative process paradigm and a middle way of delivering a combination…
A: Incremental delivery: A component of software development known as the Incremental Delivery Model is…
Q: Because of today's strong computers, this is achievable. How did computers become so popular in…
A:
Q: (Java) Data fields are encapsulated with which modifier?
A: Encapsulation in Java is defined as a process of wrapping code and data together into a single unit.…
Q: What are some of the best techniques for managing firewalls? Explain.
A: Firewalls acts as a barrier for preventing the entry of traffic that might be intended to do some…
Q: In the context of software development, what does it mean to "debug" an application?
A: Software development is a series of processes used to develop software. Debug is one such important…
Q: A definition of a real-time operating system coupled with some examples This question focuses on the…
A: The real-time operating system is defined as the operating system used for real-time applications…
Q: Because of this, users can choose to provide data via the command line rather than using the…
A: Answer:
Q: It is well known that Linux and UNIX are command-line systems. Describe in detail how the command…
A: Introduction: Linux and UNIX are command-line system: A proprietary operating system is Unix. Unix…
Q: PCs using Chrome OS need less internal storage space than those running rival desktop operating…
A: Desktop-Operating-System: Filters. The user's machine's control software (desktop or laptop).…
Q: Discuss how the Huffman encoding method is used to determine data compression effectiveness.
A: Introduction: Huffman coding is a method of data storage that does not lose any information. The…
Q: Using real-world operating system examples might help illustrate the idea. What distinguishes this…
A: Answer:
Q: Explain the distinction between ANN Perceptrons and ANN MADALINE, as well as their respective…
A: Introduction: An artificial neural network is an attempt to replicate the network of neurons that…
Q: Discuss Big Data and how businesses are using it these days, as well as why.
A: Introduction: Big data is a collection of tools for collecting, analysing, and managing massive…
Q: What's Hiding Amongst the Crowd? Language - Java Script A word is on the loose and now has tried to…
A: Coded using Javascript.
Q: Defect elimination, not prevention, is the principle of Cleanroom Software Engineering, which…
A: Introduction: A technique for improving the correctness of present software via engineering is…
Q: Sub-band coding is a term used in acoustics and has a specific use in MP3 compression.
A: Sub-band coding : Sub-band coding (SBC) is a kind of transform coding that divides a signal into…
Q: Assume three ready-to-run processes in secondary memory. Process 3 has no priority since 1 is most…
A: The function of the operating system that oversees the completion of a variety of different jobs. It…
Q: Does MVC architecture have a role in the creation of web-based software? The MVC framework comes in…
A: Introduction: The display layer and business logic are separated by MVC. In offices, graphical user…
Q: What methods are utilized to hijack a session? What can you do to stop yourself from becoming a…
A: Session Hijacking is a kind of attack in which unauthorized access is obtained to authorized session…
Q: What is the purpose of formal techniques, and if so, how do they really work? Specification-driven…
A: Given: Describe the aim of formal approaches. Some of the explanations for using formal methods are…
Q: The command-driven interface introduced with MS-DOS is still available in Windows operating systems.…
A: Answer:
Q: rite the HTML code to have the following display on the web page. I. HTML A. List B. C. Form II.…
A: HTML code for unordered list: Square: <html> <body> <ul…
Q: for (int k = 0; k<text.length(); k++) { char c = text.charAt(k); if (c == 'a' c == 'e' c == 'i' || c…
A: In English alphabets a,e,i,o,u are vowels and remaining are the consonants
Step by step
Solved in 2 steps

- Implement a class Stack <E> that manages an array list of elements of type E. Provide methods push, pop, and isEmpty. (JAVA)Write an iterable Stack client that has a static method copy() that takes a stackof strings as argument and returns a copy of the stack. Note : This ability is a primeexample of the value of having an iterator, because it allows development of such functionality without changing the basic API.Modify the Java class for the abstract stack type shown belowto use a linked list representation and test it with the same code thatappears in this chapter. class StackClass {private int [] stackRef;private int maxLen,topIndex;public StackClass() { // A constructorstackRef = new int [100];maxLen = 99;topIndex = -1;}public void push(int number) {if (topIndex == maxLen)System.out.println("Error in push–stack is full");else stackRef[++topIndex] = number;}public void pop() {if (empty())System.out.println("Error in pop–stack is empty"); else --topIndex;}public int top() {if (empty()) {System.out.println("Error in top–stack is empty");return 9999;}elsereturn (stackRef[topIndex]);}public boolean empty() {return (topIndex == -1);}}An example class that uses StackClass follows:public class TstStack {public static void main(String[] args) {StackClass myStack = new StackClass();myStack.push(42);myStack.push(29);System.out.println("29 is: " + myStack.top());myStack.pop();System.out.println("42 is:…
- Implement stack by creating user defined push() method for entering elements and pop() method for retriving elements In java.Implement a class called ReverseWords that uses a stack to output a set of elements input by the user in reverse order.Write a secure Bounded Stack class in Java, where the item type is string. Fail fast by throwing exceptions.
- The implementation of a queue in an array, as given in this chapter, uses the variable count to determine whether the queue is empty or full. You can also use the variable count to return the number of elements in the queue. On the other hand, class linkedQueueType does not use such a variable to keep track of the number of elements in the queue. Redefine the class linkedQueueType by adding the variable count to keep track of the number of elements in the queue. Modify the definitions of the functions addQueue and deleteQueue as necessary. Add the function queueCount to return the number of elements in the queue. Also, write a program to test various operations of the class you defined.Implement an postfix-to-infix translator using stacks. The applicationshould repeatedly read a postfix expression and print the equivalentinfix expression until the user quits. Throw an exception if the postfixexpression entered is invalid.Consider class IntArrayStack that has two instance variables: int[] data and int top. Implement an instance method inside the IntArrayStack, called popBottom(),that extracts and returns as output the element at the bottom of the stack. All other elements in the stack must remain unchanged and in the same order.
- I need help fixing this Java code to output as it's explained in the image below: import java.util.Stack; public class BXT { private TreeNode root; public void buildTree(String postfix) { Stack<TreeNode> stack = new Stack<>(); String[] tokens = postfix.split(" "); for (String token : tokens) { if (isOperator(token)) { TreeNode right = stack.pop(); TreeNode left = stack.pop(); stack.push(new TreeNode(token, left, right)); } else { stack.push(new TreeNode(token)); } } root = stack.pop(); } public double evaluateTree() { return evaluateTree(root); } private double evaluateTree(TreeNode node) { if (isOperator(node.getData())) { double left = evaluateTree(node.getLeft()); double right = evaluateTree(node.getRight()); switch (node.getData()) { case "+": return left +…Write a non-recursive Java method for printing all permutations of the numbers {1,2, ..., n}Hint: use an explicit stackpublic class QueueByStack<E> {Stack<E> a = new Stack<>();Stack<E> b = new Stack<>(); public int size() {//write code here} public boolean isEmpty() {//write code here} public void eneque(E e) {//write code here} public E deque() {//write code here} public E first() {//write code here} @Overridepublic String toString() {//write code here}}Implement generic class ArrayStack as discussed in the lectures having following methods: constructor, push, pop, peek, isEmpty, copy constructor, reallocate (private method). Also add following methods to this class: size: returns number of elements in the stack. contains: Search an element in the stack. If found returns true, else returns false. clear: Deletes all elements of the stack and make it empty stack.

