Question 2: Encoding Cryptography is the study of trying to create secure information by obscuring the original message. One simple encryption method is to substitute letters f decrypt the hidden message, we may also remove clues such as the length of the words in the message and any punctuation or capitalization. Write a function encode that consumes a string message. The function produces a string which is encrypted according the following procedure: • Only the letters from the original message will be encrypted. Other characters such as spaces, punctuation, numeric digits, etc. are not included • The encrypted message will only contain uppercase letters. • Each letter will be replaced by the uppercase letter at the opposite end of the English alphabet. In other words, A or a will become Z, B or b will become Y. c orc will become X. .. z or z will become A. • The encrypted message will have a single space separating each letter. You may assume that the letters in message are English letters only. For example: 1 > (encpde "Cat") 2 "X Z G" > (encode "A") 4 "" 5 > (encode "Is this correct?") 6 "R HGSRHXLIIV X G" Additional Restrictions
Question 2: Encoding Cryptography is the study of trying to create secure information by obscuring the original message. One simple encryption method is to substitute letters f decrypt the hidden message, we may also remove clues such as the length of the words in the message and any punctuation or capitalization. Write a function encode that consumes a string message. The function produces a string which is encrypted according the following procedure: • Only the letters from the original message will be encrypted. Other characters such as spaces, punctuation, numeric digits, etc. are not included • The encrypted message will only contain uppercase letters. • Each letter will be replaced by the uppercase letter at the opposite end of the English alphabet. In other words, A or a will become Z, B or b will become Y. c orc will become X. .. z or z will become A. • The encrypted message will have a single space separating each letter. You may assume that the letters in message are English letters only. For example: 1 > (encpde "Cat") 2 "X Z G" > (encode "A") 4 "" 5 > (encode "Is this correct?") 6 "R HGSRHXLIIV X G" Additional Restrictions
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter10: Classes And Data Abstraction
Section: Chapter Questions
Problem 19PE
Related questions
Question
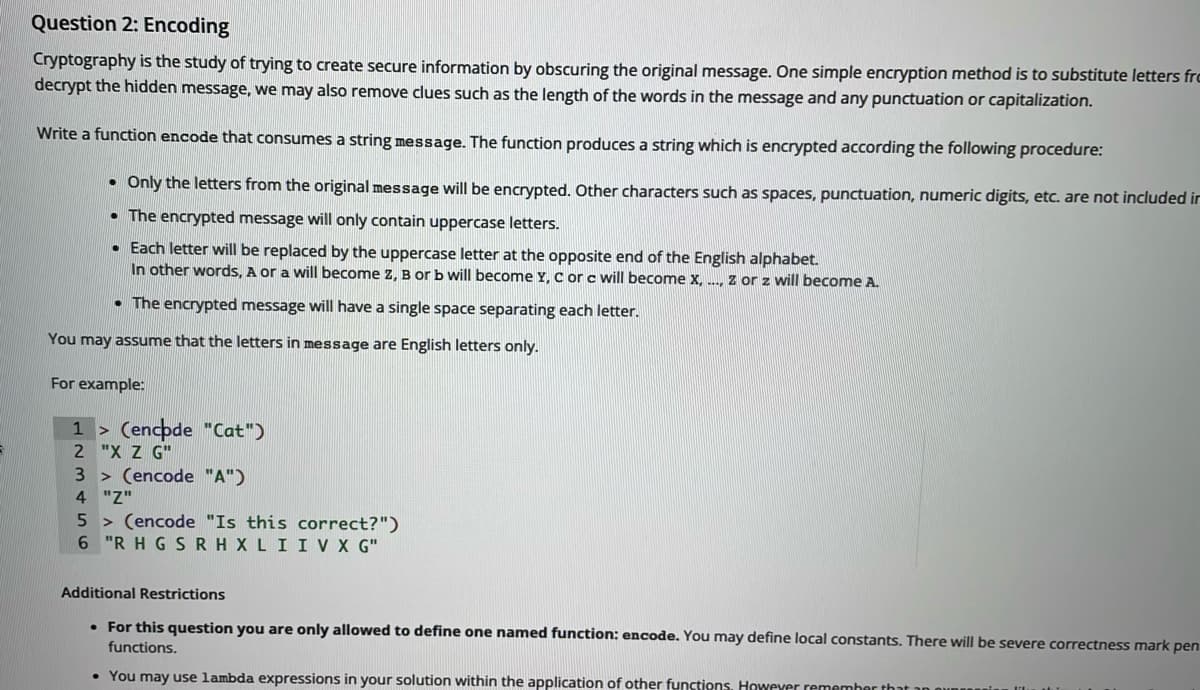
Question 2: Encoding
Cryptography is the study of trying to create secure information by obscuring the original message. One simple encryption method is to substitute letters from the original message with other letters. To make it harder to decrypt the hidden message, we may also remove clues such as the length of the words in the message and any punctuation or capitalization.
Write a function encode that consumes a string message. The function produces a string which is encrypted according the following procedure:
* Only the letters from the original message will be encrypted. Other characters such as spaces, punctuation, numeric digits, etc. are not included in the encrypted message at all.
* The encrypted message will only contain uppercase letters.
* Each letter will be replaced by the uppercase letter at the opposite end of the English alphabet.
In other words, A or a will become Z, B or b will become Y, C or c will become X, ..., Z or z will become A.
* The encrypted message will have a single space separating each letter.
You may assume that the letters in message are English letters only.
For example:
1
2
3
4
5
6
> (encode "Cat")
"X Z
G"
> (encode "A")
"Z"
> (encode "Is this
correct?")
"R H G S R H X L I I V X G"
> (encode "Cat")
"X Z G"
> (encode "A")
"Z"
> (encode "Is this correct?")
"R H G S R H X L I I V X G"
Transcribed Image Text:Question 2: Encoding
Cryptography is the study of trying to create secure information by obscuring the original message. One simple encryption method is to substitute letters frc
decrypt the hidden message, we may also remove clues such as the length of the words in the message and any punctuation or capitalization.
Write a function encode that consumes a string message. The function produces a string which is encrypted according the following procedure:
• Only the letters from the original message will be encrypted. Other characters such as spaces, punctuation, numeric digits, etc. are not included ir
• The encrypted message will only contain uppercase letters.
• Each letter will be replaced by the uppercase letter at the opposite end of the English alphabet.
In other words, A or a will become Z. B or b will become Y. c orc will become x. .. z or z will become A.
• The encrypted message will have a single space separating each letter.
You may assume that the letters in message are English letters only.
For example:
1 > (encpde "Cat")
2 "X Z G"
3 > (encode "A")
4 "Z"
5 > (encode "Is this correct?")
6 "R H G SRH XLI IV X G"
Additional Restrictions
• For this question you are only allowed to define one named function: encode. You may define local constants. There will be severe correctness mark pen
functions.
• You may use lambda expressions in your solution within the application of other functions. However remember that an ounr
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 3 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning