Question 20 A network administrator configures the interface G17 on R1 with the command ip address 178.18.28.234 255.255.255.0. However, when the administrator issues the command show ip route, the routing table does not show the directly connected network. What is the possible cause of the problem? a) The interface Gi7 has not been activated.
Question 20 A network administrator configures the interface G17 on R1 with the command ip address 178.18.28.234 255.255.255.0. However, when the administrator issues the command show ip route, the routing table does not show the directly connected network. What is the possible cause of the problem? a) The interface Gi7 has not been activated.
Comptia A+ Core 1 Exam: Guide To Computing Infrastructure (mindtap Course List)
10th Edition
ISBN:9780357108376
Author:Jean Andrews, Joy Dark, Jill West
Publisher:Jean Andrews, Joy Dark, Jill West
Chapter8: Network Infrastructure And Troubleshooting
Section: Chapter Questions
Problem 8TC
Related questions
Question
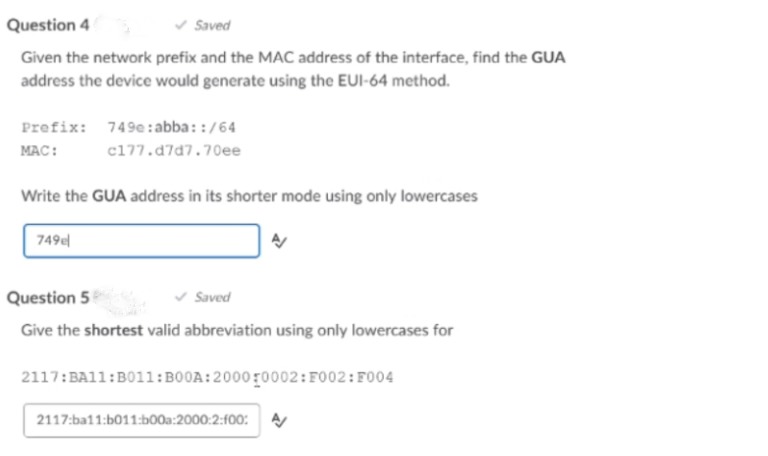
Transcribed Image Text:Question 4
v Saved
Given the network prefix and the MAC address of the interface, find the GUA
address the device would generate using the EUI-64 method.
Prefix: 749e: abba::/64
MAC:
c177.d7d7.70ee
Write the GUA address in its shorter mode using only lowercases
749e
Question 5
v Saved
Give the shortest valid abbreviation using only lowercases for
2117:BA11:B011:B00A:2000r0002:F002:F004
2117:ba11:b011:b00a:2000:2:f00:
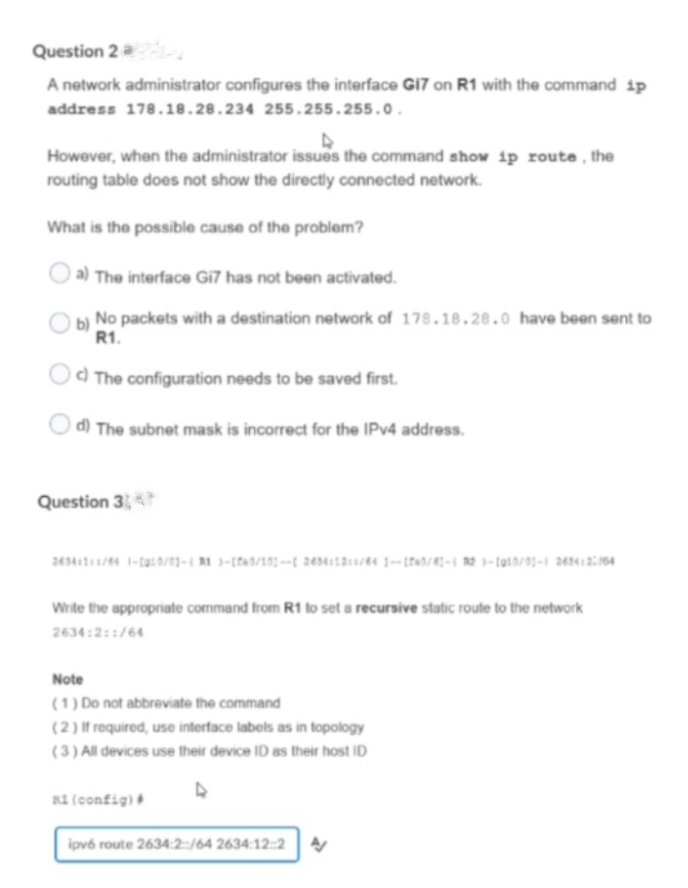
Transcribed Image Text:Question 2 a
A network administrator configures the interface GI7 on R1 with the command ip
address 178.18.28.234 255.255.255.0.
However, when the administrator issues the command show ip route, the
routing table does not show the directly connected network.
What is the possible cause of the problem?
a) The interface Gi7 has not been activated.
No packets with a destination network of 178.18.28.0 have been sent to
R1.
Od The configuration needs to be saved first.
d) The subnet mask is incorrect for the IPV4 address.
Question 3
Write the appropriate command from R1 to set a recursive static route to the network
2634:2::/64
Note
(1) Do not abbreviate the command
(2) If required, use interface labels as in topology
(3) All devices use their device ID as their host ID
R1 (config)
ipvé route 2634:2:/64 2634:12::2
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Comptia A+ Core 1 Exam: Guide To Computing Infras…
Computer Science
ISBN:
9780357108376
Author:
Jean Andrews, Joy Dark, Jill West
Publisher:
Cengage Learning

Comptia A+ Core 1 Exam: Guide To Computing Infras…
Computer Science
ISBN:
9780357108376
Author:
Jean Andrews, Joy Dark, Jill West
Publisher:
Cengage Learning