Question: Jack is always excited about sunday. It is favourite day, when he gets to play all day. And goes to cycling with his friends. So every time when the months starts he counts the number of sundays he will get to enjoy. Considering the month can start with any day, be it Sunday, Monday.... Or so on. Count the number of Sunday jack will get within n number of days. Example 1: Input mon-> input String denoting the start of the month. 13 -> input integer denoting the number of days from the start of the month. Output: 2 -> number of days within 13 days.
Question: Jack is always excited about sunday. It is favourite day, when he gets to play all day. And goes to cycling with his friends. So every time when the months starts he counts the number of sundays he will get to enjoy. Considering the month can start with any day, be it Sunday, Monday.... Or so on. Count the number of Sunday jack will get within n number of days. Example 1: Input mon-> input String denoting the start of the month. 13 -> input integer denoting the number of days from the start of the month. Output: 2 -> number of days within 13 days.
Operations Research : Applications and Algorithms
4th Edition
ISBN:9780534380588
Author:Wayne L. Winston
Publisher:Wayne L. Winston
Chapter17: Markov Chains
Section: Chapter Questions
Problem 4RP
Related questions
Question
$Moer sfr.
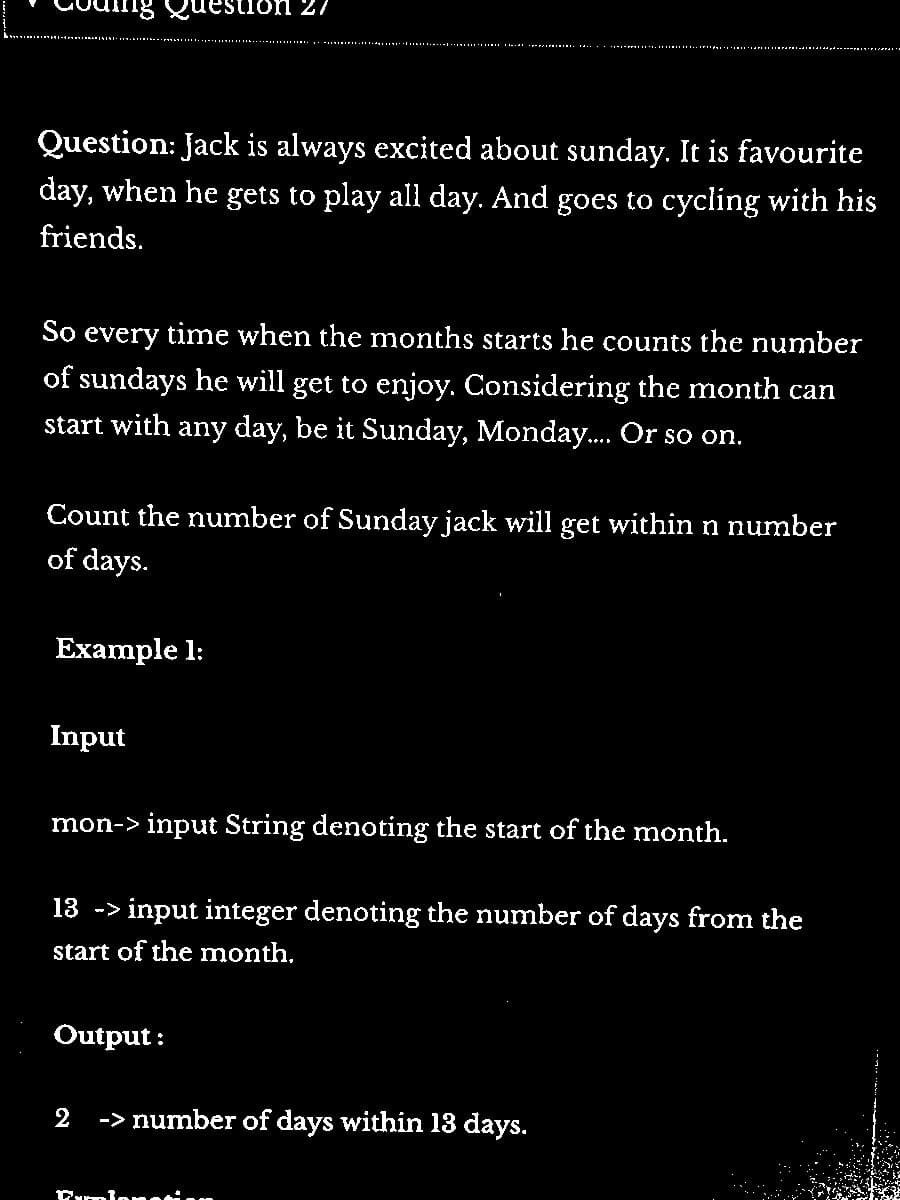
Transcribed Image Text:Question: Jack is always excited about sunday. It is favourite
day, when he gets to play all day. And goes to cycling with his
friends.
So every time when the months starts he counts the number
of sundays he will get to enjoy. Considering the month can
start with any day, be it Sunday, Monday.... Or so on.
Count the number of Sunday jack will get within n number
of days.
Example 1:
estion 27
Input
mon-> input String denoting the start of the month.
13 -> input integer denoting the number of days from the
start of the month.
Output:
2
-> number of days within 13 days.
Damlanation
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 4 steps with 3 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning