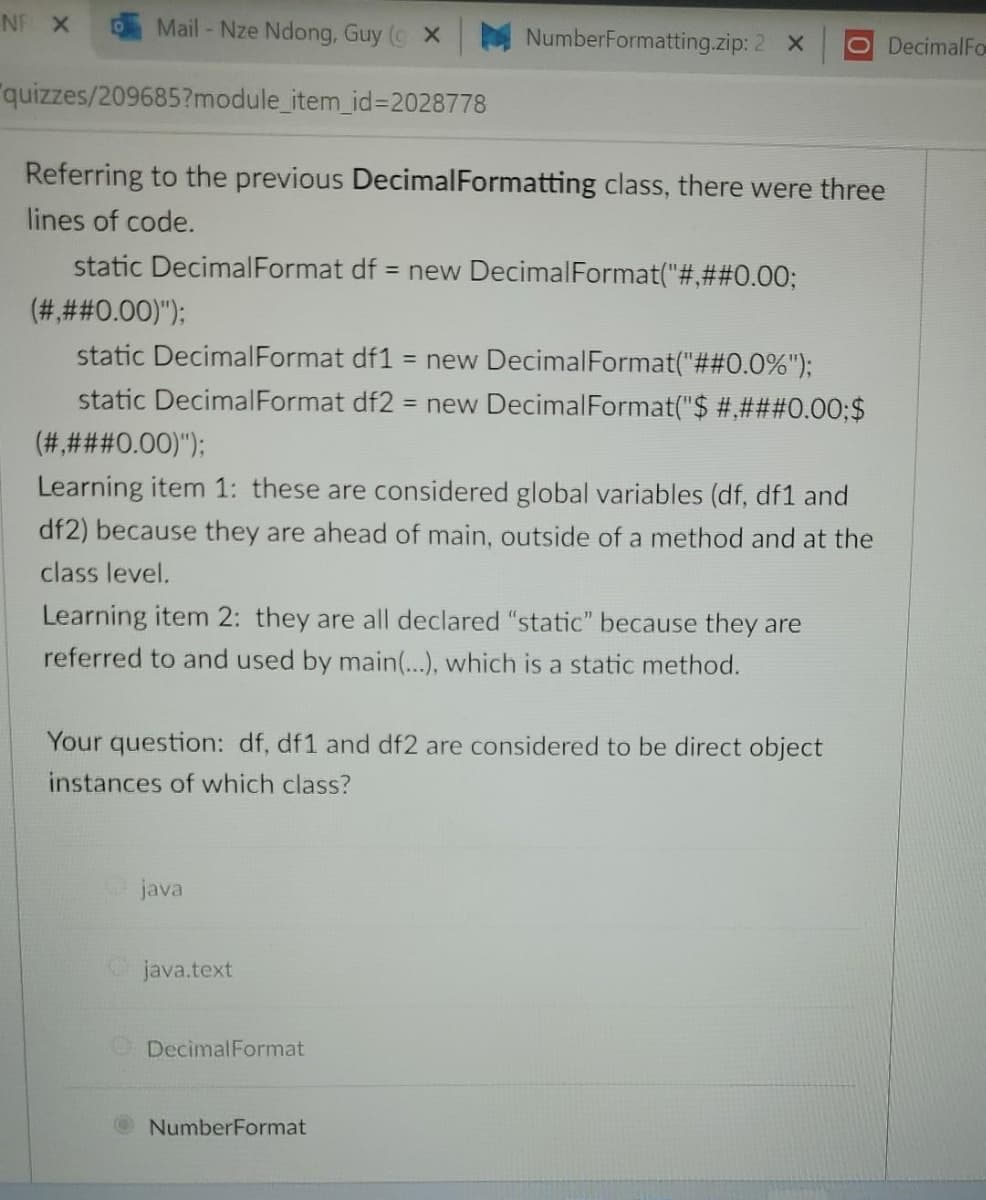
Referring to the previous DecimalFormatting class, there were three lines of code. static DecimalFormat df = new DecimalFormat("#,##0.00; (###0.00)"); static DecimalFormat df1 = new DecimalFormat("##0.0%"); static DecimalFormat df2 = new DecimalFormat("$ #,###0.00;$ (# ###30.00)"); Learning item 1: these are considered global variables (df, df1 and df2) because they are ahead of main, outside of a method and at the class level. Learning item 2: they are all declared "static" because they are referred to and used by main(...), which is a static method. Your question: df, df1 and df2 are considered to be direct object instances of which class? java Ojava.text DecimalFormat NumberFormat
Referring to the previous DecimalFormatting class, there were three lines of code. static DecimalFormat df = new DecimalFormat("#,##0.00; (###0.00)"); static DecimalFormat df1 = new DecimalFormat("##0.0%"); static DecimalFormat df2 = new DecimalFormat("$ #,###0.00;$ (# ###30.00)"); Learning item 1: these are considered global variables (df, df1 and df2) because they are ahead of main, outside of a method and at the class level. Learning item 2: they are all declared "static" because they are referred to and used by main(...), which is a static method. Your question: df, df1 and df2 are considered to be direct object instances of which class? java Ojava.text DecimalFormat NumberFormat
Chapter16: Graphics
Section: Chapter Questions
Problem 1DE
Related questions
Question
Transcribed Image Text:NF X
Mail - Nze Ndong, Guy ( X
NumberFormatting.zip: 2 X
O DecimalFo
"quizzes/209685?module_item_id%3=2028778
Referring to the previous DecimalFormatting class, there were three
lines of code.
static DecimalFormat df = new DecimalFormat("#,##0.003;
(###0.00)");
static DecimalFormat df1
= new DecimalFormat("##0.0%");
static DecimalFormat df2 = new DecimalFormat("$ #,###0.00;$
(#,###0.00)");
Learning item 1: these are considered global variables (df, df1 and
df2) because they are ahead of main, outside of a method and at the
class level.
Learning item 2: they are all declared "static" because they are
referred to and used by main(...), which is a static method.
Your question: df, df1 and df2 are considered to be direct object
instances of which class?
java
Ojava.text
ODecimalFormat
NumberFormat
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781305480537
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781305480537
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning