Select the link library procedure that displays general-purpose registers and flags in hex. WriteBin ReadDec O DumpMem DumpRegs
Q: Question 1 In the code "abort.c" (posted under Process Control), it uses hard-coded bit-manipulation...
A: Given :- The code “abort.c” uses hard-coded bit-manipulation to access the child process termination...
Q: Using a relevant example, explain how a function works.
A: Introduction Using a relevant example, explain how a function works.
Q: Can you tell the difference between a slim and a fat client?
A: Introduction : Fat client: It is also called a thick client. It is nothing but software that implem...
Q: Write a java program to print the numbers from a user entered number till 0 using recursion.
A: Given :- Write a java program to print the numbers from a user entered number till 0 using recursio...
Q: Q2 FILL IN THE BLANKS. No justification is required. Let G be the following graph: 9. 10 11 12 13 14...
A: Degree of vertex : The degree of a vertex in a graph is the number of vertices it is adjacent to. In...
Q: BFF 2:37 p.m. TODAY 2. Consider the following Java statements. int a = 1, b = 5; x = -(a = 3)b + b-(...
A:
Q: In a file named Exercise2.c write the function double sum(double (*f)(double), int start, int end); ...
A: The double is a fundamental data type built into the compiler and used to define numeric variables h...
Q: What Exactly Is Visual Computing?
A: Computing is the process of using computer technology to complete a given goal oriented task.
Q: Design and implement a class representing a circular sorted linked list. The class must have the fol...
A: Introduction Solve it in Standard Template Library (STL) Design and implement a class representing a...
Q: What is the generic term for AMD's Hyper-Transport CPU feature?
A: generic term for AMD's Hyper-Transport CPU.
Q: 1- Analyze and find the worst case complexity of following algorithm: X=0 for ( int i = 1 ;i<=n;++i)...
A: the worst-case complexity measures the resources that an algorithm requires given an input of arbitr...
Q: What may be causing connections to stall in state FIN WAIT 2?
A: INTRODUCTION What may be causing connections to stall in state FIN WAIT 2?
Q: So, what exactly is artificial intelligence? Give at least one example & a) What are the various br...
A: Introduction: Artificial intelligence:- Artificial intelligence (AI) is the replication of human int...
Q: Which of the following indicates a difference between the converse and contraposition of a condition...
A: Let's see the solution in the next steps
Q: that prompts the user to input the length of a string as an integer, followed by the string and outp...
A: #include<iostream>#include<cstring>#include<cctype>using namespace std; int main()...
Q: Write a Java program to display all the elements of the given array with their index in the output i...
A: Write a Java program to display all the elements of the given array with their index in the output i...
Q: at many prime numbers. Iterator() returns an Iterator object that will iterate through the primes, a...
A: Validate all validations with 2 first and last numbers i.e. nbr1 and nbr2. Update nbr1 again and aga...
Q: Time left 047:29 Write a complete C++ program that prompts the user to enter a string, and prints ou...
A: PROGRAM INTRODUCTION: Include the required header files. Start the definition of the main function....
Q: Refer to the snippet, what gets printed?
A: Here, I have to provide an answer to the above question.
Q: What are the rules of a project sponsor and the approval committee during the different SDLC phases
A: SDLC(Software Development Life Cycle): SDLC is an in detail blueprint that defines how software need...
Q: Scheduling can be divided into two types: preemptive and nonpreemptive.
A: Introduction: Scheduling can be divided into two types: preemptive and nonpreemptive.
Q: Given a list of values l = [ao, a1, a2,..., an] , we can construct a continued fraction: 1 ao + 1 a1...
A: Program Explanation:- Python function to compute the continued fraction. The base case, when list l...
Q: I asked for this to be written in c# instead I got C. Please create a console application of you...
A: Given: We need to explain below point in c#. 1. Declare variables with proper data types2. Be able t...
Q: Question 3: Consider the following function void testDefaultParam(int a, int b= 7, char z ="*); prot...
A: Lets see the solution in the next steps
Q: complete the docstring using the information provided:
A: import math EARTH_RADIUS = 6371 NO_KIOSK = 'SMART' def get_lat_lon_distance(lat1, lon1, lat2, lon...
Q: debugg help def print_categories(main_list): if id not in main_list: print("There...
A: def print_categories(main_list): # checking main_list is empty if main_list==None or len(ma...
Q: Should you attempt to adjust your hardware (b
A: Q)Should you attempt to adjust your hardware (by adding drives or RAM) first, or your transactions (...
Q: A) Write a query which shows the employee IDs that are unique to the employee table. Order the empl...
A: Solution A) - In the first part, we need to write a query to employee Ids and the employee should i...
Q: the numbers that are present in both lists. See sample lists and output below. Input two sets of li...
A: given - Write a program that asks the user to input 2 lists of numbers, 5 numbers per list. Your pro...
Q: Binary numbers are inconvenient because they're too long and not easy to read. Write C+ code that co...
A: Here I have created a function named binaryToDecimal(), which takes the input parameter as a binary ...
Q: Is it a cross-site scripting (XSS) attack?
A: Introduction: Cross-site scripting (XSS) is a sort of security flaw that exists in some online appli...
Q: Give the complete program of each of the following. 1. Write a program to input eight integer numbe...
A: Note 1 - As per our guidelines, we can provide solution only for one question. Since you have asked...
Q: find the total number of swaps in a 100 element array
A: Total number of swaps in Heap sort = O(n log n) In Heapsort, elimination of elements one by one fro...
Q: Please define the authentication methods that EIGRP supports.
A: Introduction: Enhanced Interior Gateway Routing Protocol (EIGRP) Please define the authentication m...
Q: the C
A: When a process or an event needs immediate attention, a signal is emitted by hardware or software wh...
Q: Discuss how and why internet fraudsters have adapted.
A: Introduction: Environment on the internet: The environment in which online tasks will be completed i...
Q: Computer networks *(Discuss briefly each acronym of each network and give examples for each)
A: As per guidelines, we can only solve the first three parts of a Multi-subpart question. hence resubm...
Q: What are the differences between HashMap and HashTable in Java?
A: Introduction: What are the differences between HashMap and Hashtable in Java?
Q: Explain how the read-committed isolation level prevents schedules from cascading.
A: Introduction: PostgreSQL's read committed isolation level is the default setting when the database i...
Q: Redo any of the previous programming problems to make them batch- oriented (using text files for inp...
A: We have one simple problem and we have to just converted into a batch oriented . We just only have t...
Q: Explain the ring topology with advantages and disadvantages
A: Hi there, Please find your solution below, I hope you would find my solution useful and helpful. Tha...
Q: Correct the errors in the following statements. Each row in a one-dimensional array could be treate...
A: We can create (Simulate) a one dimensional array as if it is a two Dimensional array. There are two ...
Q: # A set of constants, each representing a list index for station informat ID = 0 NAME LATITUDE = 2 L...
A: Python is a widely programming language with a high level of abstraction. Its design philosophy prio...
Q: void findlyEx(int array, int len, int x); wen an array, its length, and a number x, print true if x ...
A: Please find the answer below
Q: 12. Suppose C is a class of subsets of 2 and suppose BC satisfies B e o(C). Show that there exists a...
A: let 'G' be the union of all σ-algebras generated by countable subsets of CB.
Q: Write a program in C to decrypt a cipher text using Caesar Cipher substitution method without a key ...
A: Caesar Cipher substitution method can be defined as the encryption technique in which each letter is...
Q: Answer the following 4 questions with step by step explanations : Convert 870678(9) = x(27) Convert ...
A: Number Representation: Numerous number base systems exist, each of which determines which digits are...
Q: Do you believe that the accessibility features in the operating system of your computer or mobile de...
A: Introduction The question is about Do you believe that the accessibility features in the operating s...
Q: Explain what this function is and why its needed in coding. Yes No
A: The given symbol is implementing a looping statement in the program. The given symbol executes a blo...
Q: Describe how LDAP may be used to give numerous hierarchical data views without having to duplicate t...
A: Introduction Describe how LDAP may be used to give numerous hierarchical data views without having ...
The class I'm taking is assembly
I am completely stuck. I have attached the problem. Please view attachment before answering. Thank you so much for your help! Any help is greatly appreciated.
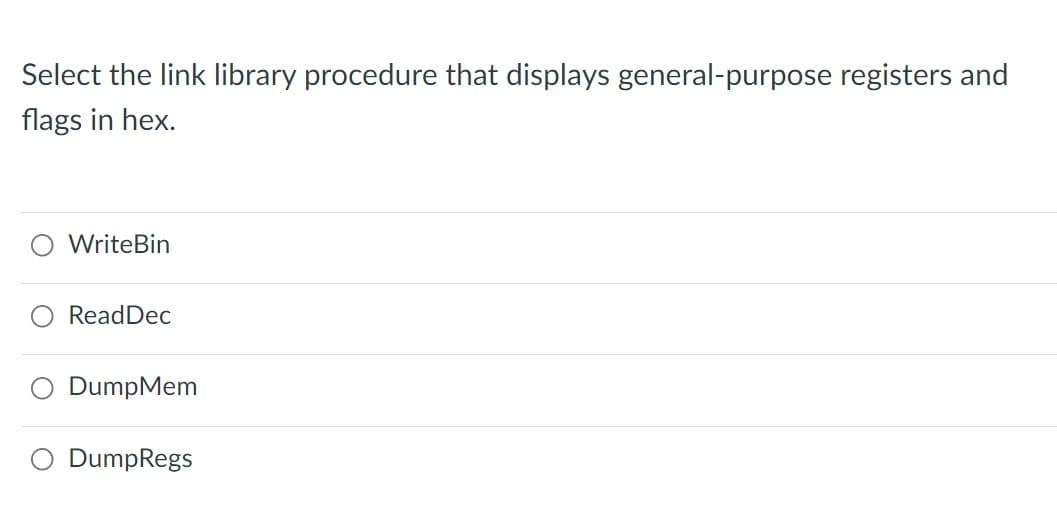
Step by step
Solved in 2 steps

- Refer to image to answer this; Show the runtime stack with the activation record instance for the subprogram snack. Remember the dynamic linkUse select to avoid deadlock goroutines and write go codeuse this formula for this. .386 .model flat, stdcall .stack 4096 ExitProcess PROTO, dwExitCode:DWORD .data .code INVOKE ExitProcess,0 main ENDP END main
- Which setting of the Direction flag results in the reverse direction of the index registers across memory while executing string primitives?For ReadDec, describe what it does.Please include steps and comments. Starter Code: title Title of Program (skel.asm) .model small ; one data segment, one code segment.stack 100h ; reserves 256 bytes for the stack.386 ; for 32 bits.data ; start definition of variables ; your variables go here .code ; start code portion of programmain proc ; start of the main procedure mov eax,@data ; load the address of the data segment into eax mov ds,eax ; load the address of the data segment into ds ; the two previous instructions initalize the data segment ; your code goes here ; the following two instructions exit cleanly from the program mov eax,4C00h ; 4C in ah means exit with code 0 (al) (similar to return 0; in C++) int 21h ; exitmain endp ; end procedure end main ; end program
- Write a windows32 assembly language program in visual studio that utilizes a recursive procedure. The main (_MainProc) procedure should: accept, from the user, an integer greater than 0. Guard against invalid values being entered using a loop. call the recurse sub-procedure using the cdecl protocol, receive the results of the sub-procedure, and display the results. NOTE: The main procedure should do nothing more than this! The recurse sub-procedure should (following the cdecl protocol): recursively find the solution for: recurse(0) = 3, and recurse(n) = 5 * recurse(n-1) + 9, for n > 0. return the value back to the calling procedure. Notes: Both the main procedure and recurse sub-procedure must follow the cdecl protocol. I need commented code otherwise it will be not acceptedWrite a windows32 assembly language program in visual studio that utilizes a recursive procedure. The main (_MainProc) procedure should: accept, from the user, an integer greater than 0. Guard against invalid values being entered using a loop. call the recurse sub-procedure using the cdecl protocol, receive the results of the sub-procedure, and display the results. NOTE: The main procedure should do nothing more than this! The recurse sub-procedure should (following the cdecl protocol): recursively find the solution for: recurse(0) = 3, and recurse(n) = 5 * recurse(n-1) + 9, for n > 0. return the value back to the calling procedure. Notes: Both the main procedure and recurse sub-procedure must follow the cdecl protocol.C++ Programming, TOPIC: Stack queue and dequeImprove the error code below. See attached photo for the instructions and some of the errors. main.cpp #include <iostream> #include <cstring> #include "sllstack.h" using namespace std; int main(int argc, char** argv) { SLLStack* stack = new SLLStack(); int test; string str; cin >> test; switch (test) { case 0: bool ispar(string x); string x=str; stack<char> s; for(int i=0;i<x.length();++i) { if(x[i]=='(' or x[i]=='{' or x[i]=='[') s.push(x[i]); else if (x[i]==')' and !s.empty()) { if(s.top()!='(') return false; s.pop(); } else if(x[i]=='}' and s.empty()!=1) { if(s.top()!='{') return false; s.pop(); } else…
- Which Direction flag setting causes index registers to move backward through memorywhen executing string primitives?write c++ program text editor cut copy paste (using stack) include clipboard history (history of copy saving by stack and calling history of copies)Question 5 Write a program that reads 10 characters from the keyboard and then print the characters to the screen in reverse order. Use a loop, the keyboard interrupt 21h, the console interrupt 10h and the svstem stack to Implement your solution Full explain this question and text typing work only thanks

