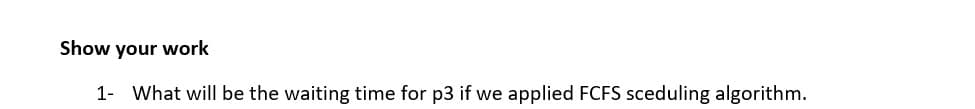
Show your work 1- What will be the waiting time for p3 if we applied FCFS sceduling algorithm.
Q: Use the Time-Hierarchy Theorem to prove that P!= EXP.
A: The answer for the given question is as follows.
Q: How many hidden layers are required for an ANN consisting of sigmoid units to learn an arbitrary…
A: A hidden layer in Artificial Neural Network is only required when we need to classify two non…
Q: Q. Show that the decision problem ISD is NP-complete. Provide complete proof that ISD is in…
A: NP, P, NP-finish and NP-Hard issues: P is set of issues that can be unraveled by a deterministic…
Q: In DL (discrete logarithm) based algorithms the private (secret) key is uniformly selected from the…
A: No, it is not feasible to select the public key uniformly from Zq* and compute the private key.
Q: Use the Pumping Lemma for CFLS to prove that each of the following lan- guages is not context-free.…
A: Pumping lemma for CFL is used to prove the language is not cfl using some valid string s. String s…
Q: 3. Apply both BFS and DFS algorithm to traverse each of the following two graphs. (a) (b) 1 2 6 9)…
A: Using BFS and DFS to traverse the given graph
Q: Recall that nearest neighbor and greedy are heuristic algorithms for the solution of the TSP problem…
A: GREEDY ALGORITHM: This algorithm will try have the minimal cost as much as possible in…
Q: Analyze the graphs about the deadlock conditions with justifications. Write the cycle sequence if…
A:
Q: Let E = {a, b} and L = {ww|w e E and w is of length k}. Show that for each k, no DFA can recognize…
A: We need to show that DFA can't be less than 2^k states for given scenario.
Q: Using the Shortest Remaining Time First (SRTF) and the Round Robin (RR) algorithms, with a given…
A: Given, Process Id Arrival Time CPU Burst A 0 6 B 4 4 C 6…
Q: FCFS algorithm is specifically trouble some for what
A: the answer is
Q: Suppose that we run the RE-to-NFA construction algorithm from the lecture and textbook on the…
A: Dear Student, NFA for the regex is given below , based on it we will find the epsilon transitions.…
Q: In this problem, let REF(x.i) → DEF(x.k) denote that the linkerwill associate an arbitrary reference…
A: /* Module 1 */ /* Module 2 */int main() int…
Q: (b) Use Spin to prove that the algorithm is still correct: use an assertion to prove mutual…
A: The mutual exclusion problem is the problem of restricting the access to the critical section in the…
Q: Explain the principle of BFS or DFS algorithms in detecting the shortest possible path in the map…
A: The algorithm used in detecting the shortest path in google maps is the A* Algorithm. The algorithm…
Q: your work.) Consider the degree-4 LFSR given by P(x) = x² + x² + 1. Assume that the LFSR is…
A: the answer is an 6
Q: To prove that the Chandy-Lamport algorithm passes the safety condition, demonstrate that it does.
A: Given: Each distributed system has a number of processes running on a number of different physical…
Q: 4. Prove that ALLCFG Sm EQCFG-
A: 1. By contradiction. Assume that we have a decider R for EQCFG.2. Using R we construct a decider S…
Q: Let AX=6E3C H, CL=0BH. Show the content of AX and CF after performing: ROR AL,CL.
A: ROR taking first AL , hence bits of AL are rotated CL times, to right, Now given CL = 0B H, in…
Q: java question implement Dijkstra's algorithm using priority queues for a source to destination…
A: Implementation of Dijkstra's algorithm , using java
Q: In a group of four machines {0, 1, 2, 3, 5} machines 0 and 1 send messages simultaneously via…
A: The answer as given below steps:
Q: Consider the following weighted undirected graph with 7 vertices and 11 edges. А C 7 8 9. 15 E D 8.…
A: According to the information given:- We have to consider undirected graph and with the help of…
Q: mulate the node expansion from start state (S) to reach goal state (G) using BFS, DFS, UCS, Greedy,…
A:
Q: You have to show (no explanations necessary) how the following reductions work. Please remember that…
A: Answer: I have given answer in the handwritten format.
Q: CFG ambiguous? Prove
A: Solution - In the given question, we have to prove whether the given CFG is ambiguous or not.
Q: Is the following a CFL? If yes then provide a pushdown automaton for it (no need to prove the…
A: The solution to the given question is:
Q: Q-2) Prove that P = { M is a TM and L(M) = Σ*} is undecidable by defining a mapping reduction from…
A:
Q: Using branch and bound approach to develop algorithm for CryptArithmetic Problem ( Ex.…
A: According to the question, we have to develop algorithm for Crypt Arithmetic Problem using branch…
Q: Draw a non-deterministic PDA that recognizes the following: ‒‒‒‒‒‒ a. {wOwR | w€ {0,1}* } R is for…
A: Non-deterministic PDA (NPDA): It require multiple computation to check acceptance of string .…
Q: We discussed how Prim’s algorithm runs on a graph G = (V,E)in O(|V|2). However, we also noted that…
A: Dear Student, Let a graph consists of very large number of vertices say n and even a larger number…
Q: affermative cases show a derivati
A:
Q: Solving using DFS on the below graph A come before Z
A:
Q: Fc for F.
A: NOTE: ACCORDING TO COMPANY POLICY WE CAN SOLVE ONLY 1 QUESTION. YOU CAN RESUBMIT THE QUESTION AGAIN…
Q: Convert the CNF into a 3CNF (reducing SAT to 3SAT) and thendraw a graph for the 3SAT problem to…
A: Convert the CNF into a 3CNF
Q: BFS or DFS algorithms in shortest possible path detection algorithm.
A: The principle of BFS or DFS algorithms in shortest possible path detection algorithm
Q: Find the new weights using binary sigmoid activation at the end of first iteration using back…
A: I have answered this question in step 2.
Q: For the proces Itsted below, evaluate Avesage waiting time and average tmaround time for DFCFS…
A: The Answer is in Below Steps:-
Q: Problem 3. Recollect that the standard implementation of the Dijkstra's algorithm uses a priority…
A: // C++ is using to write the dijkstra's algorithm uses a priority queue that supports extract-min()…
Q: Use domain splitting with Arc Consistency (AC) to solve the problem. Draw the search tree and at…
A: Domain Splitting is to split a problem into numbers of disjoint cases and solve them separately. If…
Q: Develop an equation that computes how many links in the n-cube (where n is the order of the cube)…
A: Comparing resiliency to failure of n-cube with interconnection network: It is given that there is…
Q: Write the pseudocode of an algorithm to find a TSP tour based on MST. Apply your algorithm on the…
A: PSEUDOCODE: def tsp(int graph[][V], int s) vector<int> vertex for i < V if i…
Q: 2. Let M₂ be the PDA below: M₂: a λ/A bλ/B a A/λ b B/). 8 2.2/2 90 Give the transition table of M₂.…
A: To check whether given strings belongs to the language generated by given pda or not, we have to…
Q: ording to McCabe Cyclomatic Complexity, for 3 connections among 2 nodes, the complexity is а. 4
A: According to Mc CAbe Cyclonatic Complexity Given connection c =3 Nodes=2 Complexity =( no of…
Cpu schedules process,
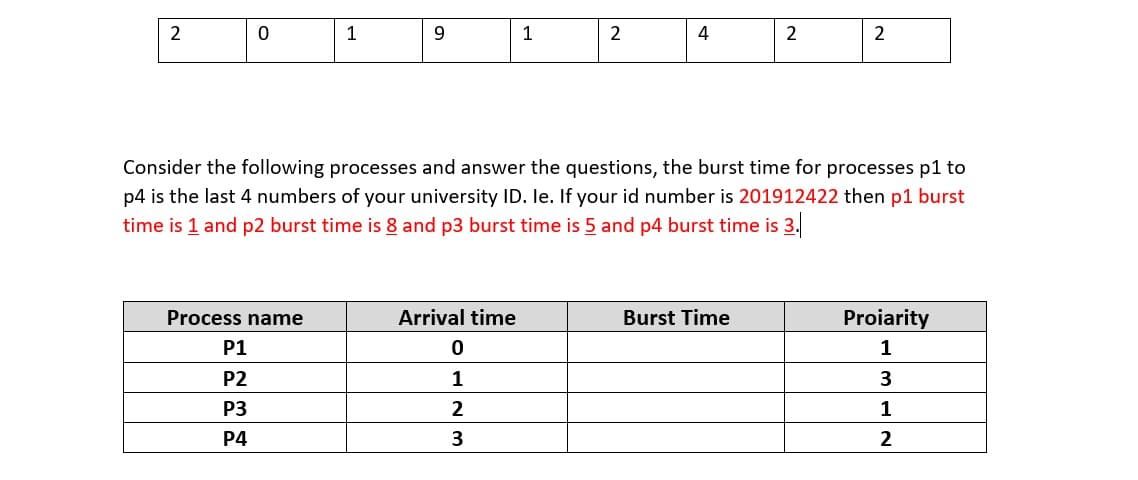
Step by step
Solved in 2 steps

- Answer the following:I. Name any two interrupt/exceptions that can occur during IF and ID stagesII. Contrast superscalar and superpipelined modes of ILPIII. What is the role of write back buffers in write-through and write-back cachesIV. What is the impact of prefetcher on the different kinds of cache missesV. Illustrate why and what kind of hazards are addressed/not-addressed by registerrenamingComputer Science Create a PowerShell script that handles the following information. The script must utilize an arrays and loop. $server1 = "Mercury" $server2 = "Venus" $server3 = "Mars" $server4 = "Pluto" Write-Host "$server1 has been backed up" Write-Host "$server1 has been updated" Write-Host "$server1 has been received vendor files" Write-Host "$server2 has been backed up" Write-Host "$server2 has been updated" Write-Host "$server2 has been received vendor files" Write-Host "$server3 has been backed up" Write-Host "$server3 has been updated" Write-Host "$server3 has been received vendor files" Write-Host "$server4 has been backed up" Write-Host "$server4 has been updated" Write-Host "$server4 has been received vendor files" Answer SkipThe NX (“no execute”) bit can also be supported by modern CPUs. To force a CPU to avoid running the code on a file, set the NX bit to 1 on that page. Currently, the OS and paging hardware implement this maximum quantity. Keep in mind that non-X86-compliant software/hardware can be executed on an OS and hardware How about a parser who wants to enforce NX above the operating system level? The programmer inserts a nX-bit association with each memory page at the bottom (in other words, at each memory location of nX bits.) The programmer imposes a size limit of 4095 bytes for application-level data structures. each stack frame is allocated in its own page, and no stack frame is larger than a page. At a given point in time, a stack frame might look like this: |-----------------------| | | +-----------------------+ entry %esp-->| return address | +-----------------------+ new %ebp---->| saved %ebp | +-----------------------+ | buf[4] | | buf[3] | | buf[1] | | buf[0] |…
- Suppose, you need to service 36 interrupts. At least how many slave-8259chips do you need to fulfil this requirement? Again, let, you need one more interrupt to servicealongside the above 36. Would you need more slave-8259? Explain shortly.Question 7 A serial transmitter with event: Tr_buf is a byte-wide buffer. Serially output its content on a serial line. When Tr_buf is empty, set event TR. On TR event, load Tr_buf from bottom of FIFO. write a verlog code using bhevarioial level Full explainthe this question very fast solution sent me step by step Don't ignore any part all part work u Text typing work only not allow paper workWhich of following is not true for virtual memory? a)In page table of virtual memory, if valid-invalid bit is invalid, then whether the page is in secondary storage or page is not in logical address space of that process b)A page fault occurs when a virtual adress that is referenced is not already loaded into physical address c)A program must be loaded to physical memory (RAM) completely for it to be executed d)Virtual memory makes it possible to execute programs that are larger than physical memory(RAM).
- Consider the following scenario:a main program starts execution at time t = 03 second later device B sends interrupt signal5 second later device A sends interrupt signal2 second later device E sends interrupt signal3 second later device C sends interrupt signal5 second later device D sends interrupt signal5 second later device F sends interrupt signalhighlight on the following figure the paths of execution that realize the mentioned interrupt scenario.With each highlighted path indicate time value (t = ?)Finally draw one more path from the last ISR executed back to the main program and displayreturn time.Assume there is a PCI buffer that is used for data transfers between primary memory and a webcam. The memory transfers 15 frames where each frame is 1M byte in size and the buffer size is 1K byte. 1-How many data transfers will be required? 2-A transfer operation requires 2 interrupts. Start and stop. How many interrupts will occur for the data transfer? 3-What are the two commands that will be issued by the supervisor for each interrupt?Suppose the Vole communicates with a printer using the technique of memory-mapped I/O. Suppose also thataddress 0xFF is used to send characters to the printer, and address 0xFE is used to receive information about theprinter’s status. In particular, suppose the least significant bit at the address 0xFE indicates whether the printeris ready to receive another character (with a 0 indicating “not ready” and a 1 indicating “ready”). Starting ataddress 0x00, write a machine language routine that waits until the printer is ready for another character and thensends the character represented by the bit pattern in register 0x5 to the printer.
- For this assignment, you will create a parallel fixed-length code decompressor using the tools we learned in class to create multiple processes and threads. Computers represent a character as a sequence of 8 bits, which means you can represent up to 256 symbols per character. However, depending on the source, it is common to have messages/files using an alphabet with a size of fewer than 256 symbols. The simplest way to achieve compression is to use a fixed-length code generator. The idea behind this type of code generator is to assign a fixed-length bit sequence to each alphabet symbol. Given an alphabet (where each symbol is represented by a character and a decimal value with the code of the symbol), you need to implement a fixed-length code decompressor based on the following steps: ◦Read the contents of the input file using input redirection (STDIN). The format of the input file is as follow: - An integer value representing the number of symbols in the alphabet - n lines (where…⦁ You are required to make changes in the programs and introduce the use of compaction where required. MVT MEMORY MANAGEMENT TECHNIQUE#include<stdio.h>#include<conio.h>main(){int ms,mp[10],i, temp,n=0; char ch = 'y';clrscr();printf("\nEnter the total memory available (in Bytes)-- "); scanf("%d",&ms);temp=ms;for(i=0;ch=='y';i++,n++){printf("\nEnter memory required for process %d (in Bytes) -- ",i+1); scanf("%d",&mp[i]);if(mp[i]<=temp){printf("\nMemory is allocated for Process %d ",i+1); temp = temp - mp[i];}else{printf("\nMemory is Full"); break;}printf("\nDo you want to continue(y/n) -- "); scanf(" %c", &ch);}printf("\n\nTotal Memory Available -- %d", ms);printf("\n\n\tPROCESS\t\t MEMORY ALLOCATED "); for(i=0;i<n;i++)printf("\n \t%d\t\t%d",i+1,mp[i]); printf("\n\nTotal Memory Allocated is %d",ms-temp);printf("\nTotal External Fragmentation is %d",temp); getch();Computer Science 6. (Interrupt - 20) a. What we mean by ISR? explain and give example b. What is the purpose of the NVIC? explain c. How priority works on MSP432? And how many levels there are? Given that two processes with different priorities which will be executed first, and on what basis? d. Let us say you want to configure an interrupt with exception number 40. Which one of the followings is correct way to set the enable register? NVIC->ISER[1] or NVIC->ISER[0] and why?

