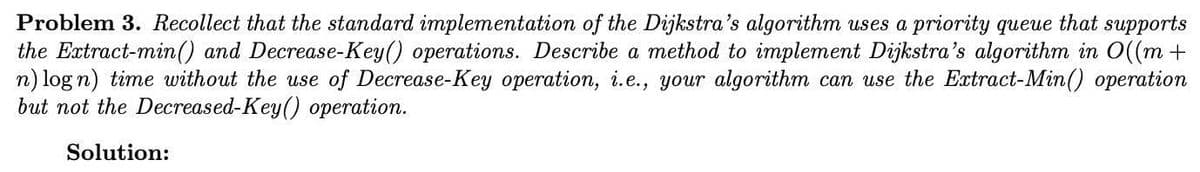
Problem 3. Recollect that the standard implementation of the Dijkstra's algorithm uses a priority queue that supports the Extract-min() and Decrease-Key() operations. Describe a method to implement Dijkstra's algorithm in O((m + n) log n) time without the use of Decrease-Key operation, i.e., your algorithm can use the Extract-Min() operation but not the Decreased-Key() operation.
Q: orized users can only decode and read encry
A: A file's owner and authorized users can only decode and read encrypted data using what kind of encry...
Q: In python write a program that computes and prints the average of the numbers in a text file. Becaus...
A: In Step 2, I have provided TXT FILE SCREENSHOT In Step 3, I have provided PYTHON CODE In...
Q: how a hash table with linear probing collision handling works internally. Illustrate by showing a ha...
A: The hash table is a special collection used to store the KeyValue element.Caution is implemented in ...
Q: Write a program to print the lyrics of the song “Old MacDonald." Your program should print the lyric...
A: Step 1 : Start Step 2 : Using a print() statement to print the first verse of the lyrics. Step 2 : U...
Q: Given two Python lists that stores the x and y coordinates of 5 points. Using matplotlib in Python, ...
A: Given two Python lists that stores the x and y coordinates of 5 points. Using matplotlib in Python, ...
Q: 1 import java.util.Scanner; 2 3 public class DeclaringVariables { public static void main(String[] a...
A: import java.util.Scanner; public class DeclaringVariables { public static void main (String[] args) ...
Q: 3. Explain the output of this program
A: As per the requirement program explanation is given below.
Q: Create a stack-based application to convert infinix to postfix.
A: Introduction: An expression can be written in Infix, Postfix, and Prefix Notation. In Infix Notation...
Q: 11. Input three integers x, y, and z, and then check whether the numbers form a valid Pythagorean tr...
A: Required:- 11. Input three integers x, y, and z, and then check whether the numbers form a valid Pyt...
Q: def is_valid_index(idx, in_list): """ Checks whether the provided index `idx` is a valid...
A: if (idx in in_list - 1): if len(idx) != 0: return idx else: re...
Q: Data Structures and Algorithm In Breadth First Search(BFS): How do you keep track of nodes in you...
A: Given: We need to explain about (BFS) Breadth First Search Algorithm and how do we keep track of no...
Q: c++ beginers given 10 numbers a1 a2 ... a10 calculate (do not use an array)
A: The cin object is used to accept input from the standard input device i.e. keyboard.
Q: Add a command to this chapter's case study program that allows the user to view the contents of a fi...
A: • filesys is the program that obtains information about the filesystem present in the PC. • When t...
Q: Is “the language of valid Java programs” a regular language? Justify your answer. PLEASE provide th...
A: Yes it is gonna a regular language and boom of the world and it's need time to time update
Q: Using Function write a bash script that automates the creation and deletion of users' accounts from ...
A: First, I want to describe the bash script. Bash Script: A Bash script is a text file with a set o...
Q: What exactly does the term "scalability" mean in the context of computers, and what does it imply?
A: Introduction: Scalability refers to an IT system's ability to scale.
Q: Software Functionality: Download a Great Plains software demo programme and analyse its accounts rec...
A: Intro The intense completion and fluctuating sales forced the vendors of enterprise resource plannin...
Q: Convert the number system without using calculator. Binary to any number system.
A: ANS: Binary to decimal: Step 1: take the number from right hand side. step 2: binary = 1 ...
Q: 1. Discuss the Cozy Bear incident of hacktivism. 2. please provide the references website 3.in-tex...
A: INTRODUCTION: Cozy Bear is a Russian hacker organization thought to be linked to one or more Russia...
Q: Iwc (lightning web componentO make a calendar that keeps track of the user Requested Task (a request...
A: This is a very interesting question based on the concept of arithmetic and algorithmic computer scie...
Q: What are the advantages and disadvantages of formal methods? There should be at least four justifica...
A: advantages 1.formal method does not involve hogh complexity rate. 2.its semantics verify self consis...
Q: In this session, we'll go through several protections against Man-in-the-Middle attacks that steal w...
A: The MITM is also known as Man-in-the-Middle attacks.
Q: Write a computer code (or using MS Excel or any technique) to sketch the curves given in polar as: r...
A: Introduction : Note: Answering in python as no language is mentioned. Given : •Range values of theta...
Q: Large computing installations (such as server farms) can have significant impacts on the environment...
A: The server farms or large computing installations are a collection of servers which are usually main...
Q: Question 4 Why must the single-cycle datapath have separate instruction and data memories? The forma...
A: answer is
Q: Draw use case diagram for the blackboard system .
A: 1. Blackboard System.
Q: The simplified expression(s) for the Boolean Function F(A,B,C,D) = 2(2, 4, 12, 14) with Don't-Care c...
A: Here in this question we have given some minterm with some don't care conditions and we have asked t...
Q: In order to transfer traffic from one VLAN to another, what steps must be taken?
A: Introduction: VLANs enable network administrators to automatically limit access to a set of users by...
Q: 3. Write a Python script to save the dictionary words in the 'wordlist.txt' file, and then compress ...
A: Algorithm: Start Store "wordlist.txt" in wordlist Store "protected.zip" in zipFile Initialize the Z...
Q: Illustrate a minimum spanning tree (MST) using Kruskal’s Algorithm for the graph in Figure 4. Determ...
A: A minimum spanning tree or MST is a subgraph of the graph where all the vertices are present and con...
Q: What is Activity Circle Diagram (ACD)? What are the dead and active states? What are the Event Sched...
A: What is Activity Circle Diagram (ACD)? What are the Event Scheduling? Algorithm steps of Event Sche...
Q: What factors should be considered when creating a mobile app? What factors do you believe contribute...
A: Introduction: Some things to think about while creating an app: Always double-check that a programme...
Q: Question 4 a) Demonstrate with the use of simple python line codes on how to: (i) encrypt and (ii) ...
A: According to company guidelines I am able to anser first question only since other two questions are...
Q: Write the appropriate SQL queries a) List the sailor who made the highest number of reservations for...
A: a) select DISTINCT b.name ,s.name,COUNT(*) from boat b JOIN reservation r on b.id =r.bid ...
Q: Program to input the elements(integer type) of a array of size 17 and check if all the elements of t...
A: Return true before checking all the elements of the array. Counter to count the number of odds or e...
Q: Computer science What is the default policy for S3 buckets?
A: Introduction: When setting up inventory for an Amazon S3 bucket and the analytics export, you must d...
Q: need help making a calendar that shows what day they need to show a demo of their product
A: Create a Lightning Web Component and use below code
Q: What is the difference between hardware and software interrupts, and give instances of when each is ...
A: Introduction: the question is about the difference between hardware and software interrupts, and giv...
Q: Problem: Write a Python code that determines whether or not a given positive number is a multiple of...
A: a) code for prime number : num = 600 flag = False if num > 1: for i in range(2, num): ...
Q: Write a java program to reverse a user entered array in groups. Take the size of group from the user...
A: Required:- Write a java program to reverse a user-entered array in groups. Take the size of the grou...
Q: Consider WAN, your preferred wireless access mode. Why is this option better? Is your solution safe ...
A: Introduction: The WAN, in general, covers vast geographical areas (1000kms or more than that). If yo...
Q: in C++ program Try first to generate a one-dimensional Brownian simulation where you can generate a ...
A: in C++ program Try first to generate a one-dimensional Brownian simulation where you can generate a ...
Q: PLEASE DRAW THE DIAGRAM ACCORDING TO THE QUESTION: 4. Company TeaLeaves has recently adopted a new o...
A: Let's see the solution in the next steps
Q: Instructions newton.py + 1 # Modify the code below Restructure Newton's method (Case Study: Approxim...
A: Given: We have to write a Python Program In the Given Instruction Of the Case Study.
Q: Below in my class (Pizza class) created in Python IDLE: How can I add an empty set for pizza topping...
A: Sets are used to store multiple items in a single variable. Sets store unique values. set() creates ...
Q: How does I.R.M. Relate to Information Engineering and Systems?
A: IRM stands for Information Resource Management and it is a form of security technology used to prote...
Q: When it comes to computers, what's the difference between architecture and organisation?
A: Introduction When it comes to computers, what's the difference between architecture and organiz...
Q: ss-level variable called strName using the followi
A: Class levels variables are also called as static variables and they are declared usingstatickeyword ...
Q: w it works: • First, it is randomly determined if the user starts the game or the computer and this...
A: Python implementation of Tic Tac Toe game :- import random class TicTacToe: def __init__(self): ...
Q: gren Website? Include the principles and ele
A: What can you say about the Arngren Website? Include the principles and elements of design used in th...
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 2 images

- The off-line minimum problem maintains a dynamic set T of elements from the domain {1, 2,...,n}under the operations INSERT and EXTRACT-MIN. A sequence S of n INSERT and m EXTRACT-MIN calls are given, where each key in {1, 2,...,n} is inserted exactly once. Let a sequence S berepresented by I1 , E, I2, E, ... , E, Im+1 , where each Ij stands for a subsequence (possibly empty) ofINSERT and each E stands for a single EXTRACT-MIN. Let Kj be the set of keys initially obtainedfrom insertions in Ij. The algorithm to build an array extracted[1..m], where for i = 1, 2, ..., m,extracted[i] is the key returned by the ith EXTRACT-MIN call is given below: Off-Line-Minimum(m, n)for i = 1 to n determine j such that i ∈ Kj if j ≠ m + 1 extracted[j] = i let L be the smallest value greater than j for which KL exists KL = KL U Kj, destoying Kjreturn extracted Given the operation sequence 9, 4, E, 6, 2, E, E, 5, 8, E, 1, 7, E, E, 3; where eachnumber stands for its insertion.…The off-line minimum problem maintains a dynamic set T of elements from the domain {1, 2,...,n}under the operations INSERT and EXTRACT-MIN. A sequence S of n INSERT and m EXTRACT-MIN calls are given, where each key in {1, 2,...,n} is inserted exactly once. Let a sequence S berepresented by I1 , E, I2, E, ... , E, Im+1 , where each Ij stands for a subsequence (possibly empty) ofINSERT and each E stands for a single EXTRACT-MIN. Let Kj be the set of keys initially obtainedfrom insertions in Ij. The algorithm to build an array extracted[1..m], where for i = 1, 2, ..., m,extracted[i] is the key returned by the ith EXTRACT-MIN call is given below: Off-Line-Minimum(m, n)for i = 1 to n determine j such that i ∈ ?? if j ≠ m + 1 extracted[j] = i let L be the smallest value greater than j for which KL exists KL = KL U Kj, destroying ????return extracted (1) Given the operation sequence 9, 4, E, 6, 2, E, E, 5, 8, E, 1, 7, E, E, 3; where eachnumber stands for its…The off-line minimum problem maintains a dynamic set T of elements from the domain {1, 2,...,n}under the operations INSERT and EXTRACT-MIN. A sequence S of n INSERT and m EXTRACT-MIN calls are given, where each key in {1, 2,...,n} is inserted exactly once. Let a sequence S berepresented by I1 , E, I2, E, ... , E, Im+1 , where each Ij stands for a subsequence (possibly empty) ofINSERT and each E stands for a single EXTRACT-MIN. Let Kj be the set of keys initially obtainedfrom insertions in Ij. The algorithm to build an array extracted[1..m], where for i = 1, 2, ..., m,extracted[i] is the key returned by the ith EXTRACT-MIN call is given below: Off-Line-Minimum(m, n)for i = 1 to n determine j such that i ∈ Kj if j ≠ m + 1 extracted[j] = i let L be the smallest value greater than j for which KL exists KL = KL U Kj, destoying Kjreturn extracted Given the operation sequence 9, 4, E, 6, 2, E, E, 5, 8, E, 1, 7, E, E, 3; where eachnumber stands for its insertion.…
- QUESTION 2 There are many algorithms exist for keeping binary search trees balanced, among them are AVL and Splay. Discuss the differences between the AVL and Splay algorithms in keeping a binary search tree balanced. In the big-O notation, what is the cost of splaying amortized over a sequence of retrievals, insertions and deletes? Given the following Figure 3. Show step by step splaying process when node d is accessed. Proceed with accessing node bConsider a sort of items, according to their keys, that inserts all the items one at a time into an initially empty regular binary search tree and then applies an in-order traversal to complete the sort. Assume that all items have distinct keys. Using big-Theta notation, what is the worst-case complexity of the sort? What is the average-case complexity of the sort? Now answer the same two questions if an AVL tree is used instead of a regular binary search tree.Assuming that the graph G = (V, E) is represented in Adjacency List format, justify in detail the fact Greedy independent sets can be implemented in O(n 2 + m) worst-case running time, where n = |V |, m = |E|. This will require you to take real care in how the adjustment of Adj is done in line 10. The key is to only update/delete what is really necessary for the Algorithm, rather than being concerned with an accurate representation of the residual graph.
- A hash table with ordered linear probing maintains an order amongkeys considered during the rehashing process. When the keys are encountered,say, in increasing order, the performance of a failed lookup approaches that ofa successful search. Describe how a key might be inserted into the orderedsequence of values that compete for the same initial table entry. ans in 30 min and give accurateNote: Your solution should have O(n) time complexity, where n is the number of elements in l, and O(1) additional space complexity, since this is what you would be asked to accomplish in an interview. Given a linked list l, reverse its nodes k at a time and return the modified list. k is a positive integer that is less than or equal to the length of l. If the number of nodes in the linked list is not a multiple of k, then the nodes that are left out at the end should remain as-is. You may not alter the values in the nodes - only the nodes themselves can be changed.Problem 4: Let S = {s1, s2, . . . , sn} and T = {t1, t2, . . . , tm}, n ≤ m, be two sets of integers. (ii) Devise an algorithm that uses a hash table of length n to test whether S is a subset of T. What is the expected running time of your algorithm?
- With p processes, where p is a power of 2, derive formulas for the number of receives and additions that process 0 carries out using(a) the original pseudo-code for a global sum (Process 0 directly receives local sums from all other cores), and(b) the tree-structured global sum.Problem 4: Let S = {s1, s2, . . . , sn} and T = {t1, t2, . . . , tm}, n ≤ m, be two sets of integers. (i) Describe a deterministic algorithm that checks whether S is a subset of T. What is the running time of your algorithm? (ii) Devise an algorithm that uses a hash table of length n to test whether S is a subset of T. What is the expected running time of your algorithm?For the traversal log: {X, Y, Z, W, Y, A, B, C, D, Y, C, D, E, F, D, E, X, Y, A, B, M, N}, a. Find maximal forward references. b. Find large reference sequences if the threshold value is 0.3 (or 30%). c. Find maximal reference sequences.

