Subtasks: 1. Create a Doll class. 2. Create the required constructor. 3. Write a method to print the name and the price of the object 4. Use operator overloading for the addition operators. 5. Write a method to handle operator overloading for the ">" logical operator that compares the price of the objects. Hints: • Notice that the price of each object is being checked with the price of obj in the given code. Notice the word Doll in the first 4 outputs and the last output. You have to print exactly as represented here.
Subtasks: 1. Create a Doll class. 2. Create the required constructor. 3. Write a method to print the name and the price of the object 4. Use operator overloading for the addition operators. 5. Write a method to handle operator overloading for the ">" logical operator that compares the price of the objects. Hints: • Notice that the price of each object is being checked with the price of obj in the given code. Notice the word Doll in the first 4 outputs and the last output. You have to print exactly as represented here.
Chapter3: Using Methods, Classes, And Objects
Section: Chapter Questions
Problem 12PE
Related questions
Question
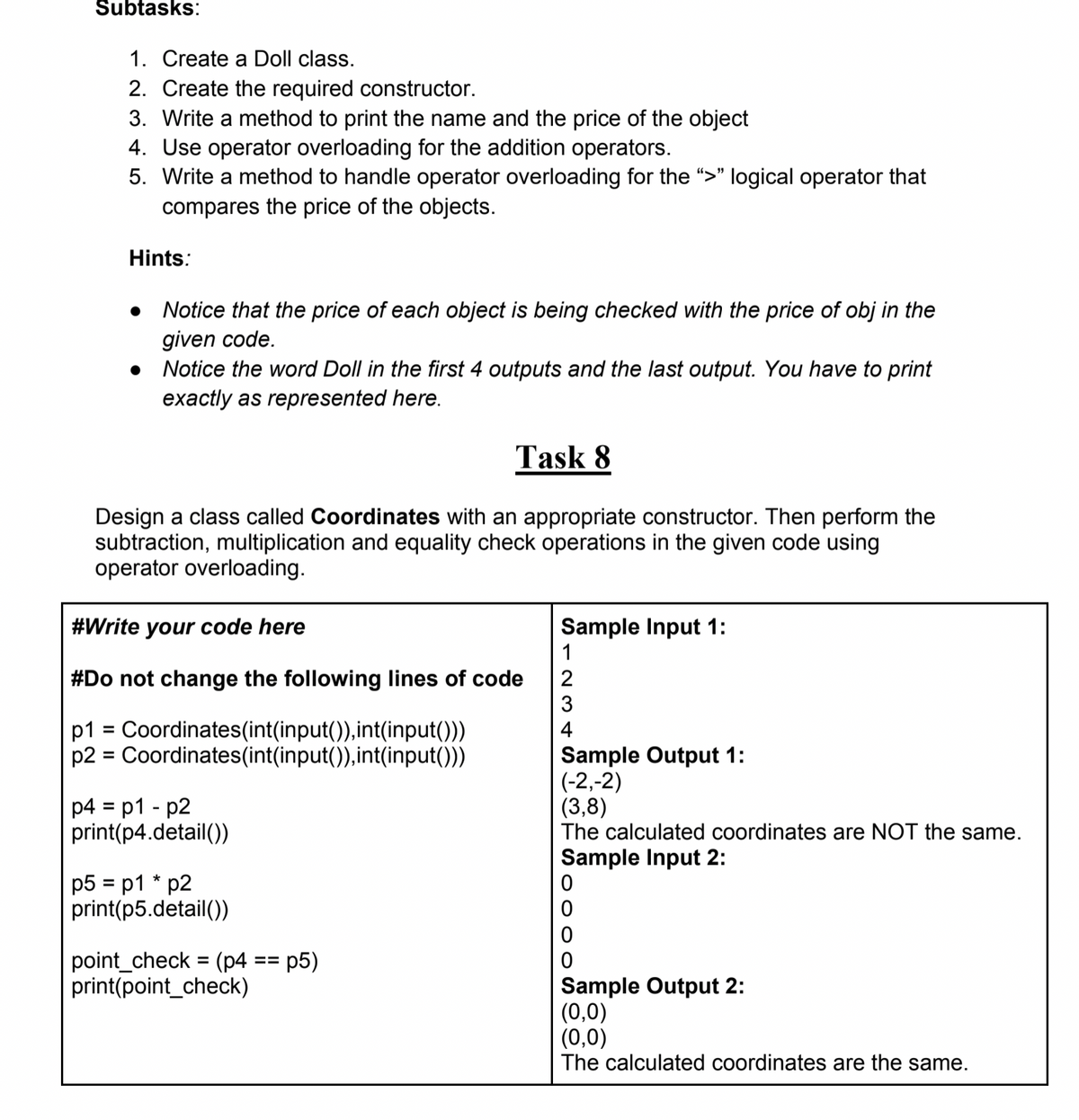
Transcribed Image Text:Subtasks:
1. Create a Doll class.
2. Create the required constructor.
3. Write a method to print the name and the price of the object
4. Use operator overloading for the addition operators.
5. Write a method to handle operator overloading for the ">" logical operator that
compares the price of the objects.
Hints:
Notice that the price of each object is being checked with the price of obj in the
given code.
• Notice the word Doll in the first 4 outputs and the last output. You have to print
exactly as represented here.
Task 8
Design a class called Coordinates with an appropriate constructor. Then perform the
subtraction, multiplication and equality check operations in the given code using
operator overloading.
Sample Input 1:
1
#Write your code here
#Do not change the following lines of code
3
2
p1 = Coordinates(int(input()),int(input()))
p2 = Coordinates(int(input()),int(input()))
4
%D
Sample Output 1:
(-2,-2)
(3,8)
The calculated coordinates are NOT the same.
p4 = p1 - p2
print(p4.detail())
%3D
Sample Input 2:
p5 = p1 * p2
print(p5.detail())
point_check = (p4
print(point_check)
p5)
%3D
==
Sample Output 2:
(0,0)
(0,0)
The calculated coordinates are the same.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

Programming with Microsoft Visual Basic 2017
Computer Science
ISBN:
9781337102124
Author:
Diane Zak
Publisher:
Cengage Learning