Suggest a simple scheme for creating a new class SafeMember that would allow us to export a reference to a Member. The classes outside the system should be unaware of this additional class, and access the reference like a reference to a Member object. However, the reference would not allow the integrity of the data to be compromised. Remember that when designing the “Return Book with fines” use case, Member object is returned to the UserInterface to be able to display the member information such as owed fine. But this also means that the UserInterface can access all the Member methods. Your implementation of SafeMember class should prevent this.
Suggest a simple scheme for creating a new class SafeMember that would allow us to export a reference to a Member. The classes outside the system should be unaware of this additional class, and access the reference like a reference to a Member object. However, the reference would not allow the integrity of the data to be compromised. Remember that when designing the “Return Book with fines” use case, Member object is returned to the UserInterface to be able to display the member information such as owed fine. But this also means that the UserInterface can access all the Member methods. Your implementation of SafeMember class should prevent this.
Chapter11: Advanced Inheritance Concepts
Section: Chapter Questions
Problem 3PE
Related questions
Question
Suggest a simple scheme for creating a new class SafeMember that would allow
us to export a reference to a Member. The classes outside the system should
be unaware of this additional class, and access the reference like a reference
to a Member object. However, the reference would not allow the integrity of the
data to be compromised. Remember that when designing the “Return Book with
fines” use case, Member object is returned to the UserInterface to be able to
display the member information such as owed fine. But this also means that the
UserInterface can access all the Member methods. Your implementation of
SafeMember class should prevent this.
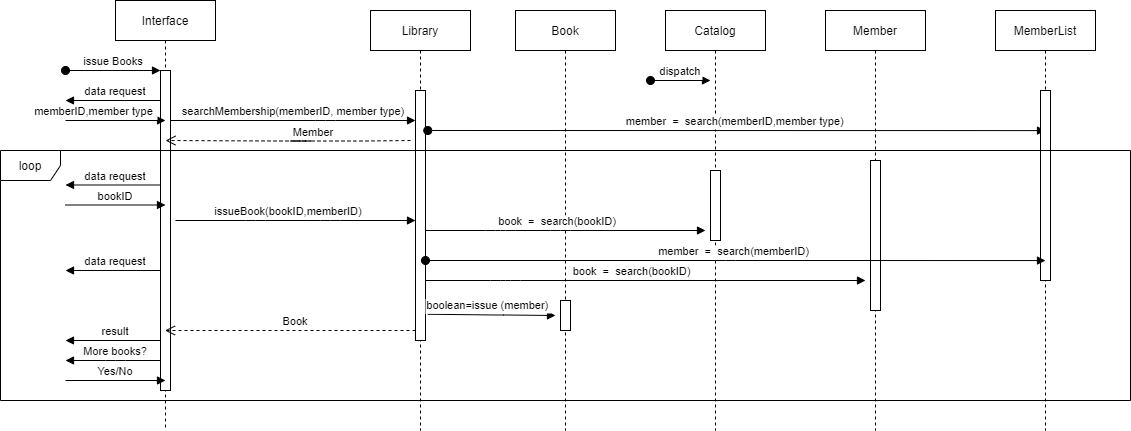
Transcribed Image Text:Interface
Library
Вok
Catalog
Member
MemberList
issue Books
dispatch
data request
memberlD,member type
searchMembership(memberlD, member type)
member = search(memberlD,member type)
Member
loop
data request
bookID
issueBook(booklD,memberlD)
book = search(bookID)
member = search(memberlD)
data request
book = search(booklD)
boolean=issue (member)
Вook
result
More books?
Yes/No
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 4 steps with 4 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

Microsoft Visual C#
Computer Science
ISBN:
9781337102100
Author:
Joyce, Farrell.
Publisher:
Cengage Learning,