Suppose we have a method with header: public ArrayList meth (ArrayList list, int n) Which of the following describes the general behaviour of this method? Select one: O a. It is not called on any object. It takes an ArrayList and an integer, and returns an ArrayList whose content type is the same type as the content type of the ArrayList it takes. O b. It takes two ArrayLists whose content is of the same type, and an integer, and returns an object of the content type of the ArrayLists. It is called on an ArrayList object, and takes another ArrayList object as its argument along with an integer. It returns an object of the same type as the contents of the ArrayLists. O d. It is called on an object of the type the method is declared in. It takes an ArrayList and an integer, and returns an ArrayList whose content type is the same type as the content type of the ArrayList it takes.
Suppose we have a method with header: public ArrayList meth (ArrayList list, int n) Which of the following describes the general behaviour of this method? Select one: O a. It is not called on any object. It takes an ArrayList and an integer, and returns an ArrayList whose content type is the same type as the content type of the ArrayList it takes. O b. It takes two ArrayLists whose content is of the same type, and an integer, and returns an object of the content type of the ArrayLists. It is called on an ArrayList object, and takes another ArrayList object as its argument along with an integer. It returns an object of the same type as the contents of the ArrayLists. O d. It is called on an object of the type the method is declared in. It takes an ArrayList and an integer, and returns an ArrayList whose content type is the same type as the content type of the ArrayList it takes.
Chapter9: Advanced Array Concepts
Section: Chapter Questions
Problem 18RQ
Related questions
Question
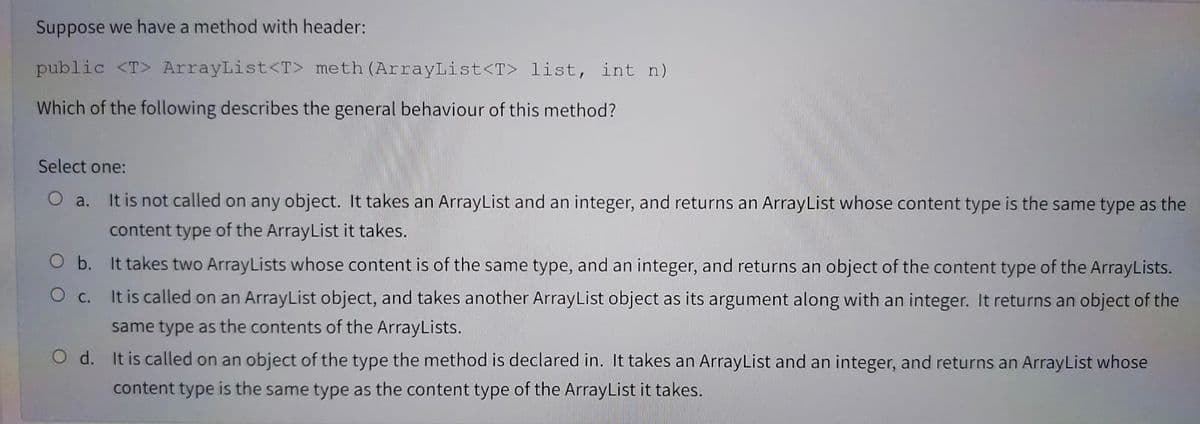
Transcribed Image Text:Suppose we have a method with header:
public <T> ArrayList<T> meth (ArrayList<T> list, int n)
Which of the following describes the general behaviour of this method?
Select one:
O a. It is not called on any object. It takes an ArrayList and an integer, and returns an ArrayList whose content type is the same type as the
content type of the ArrayList it takes.
O b. It takes two ArrayLists whose content is of the same type, and an integer, and returns an object of the content type of the ArrayLists.
O c.
It is called on an ArrayList object, and takes another ArrayList object as its argument along with an integer. It returns an object of the
same type as the contents of the ArrayLists.
O d. It is called on an object of the type the method is declared in. It takes an ArrayList and an integer, and returns an ArrayList whose
content type is the same type as the content type of the ArrayList it takes.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 3 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT

EBK JAVA PROGRAMMING
Computer Science
ISBN:
9781337671385
Author:
FARRELL
Publisher:
CENGAGE LEARNING - CONSIGNMENT