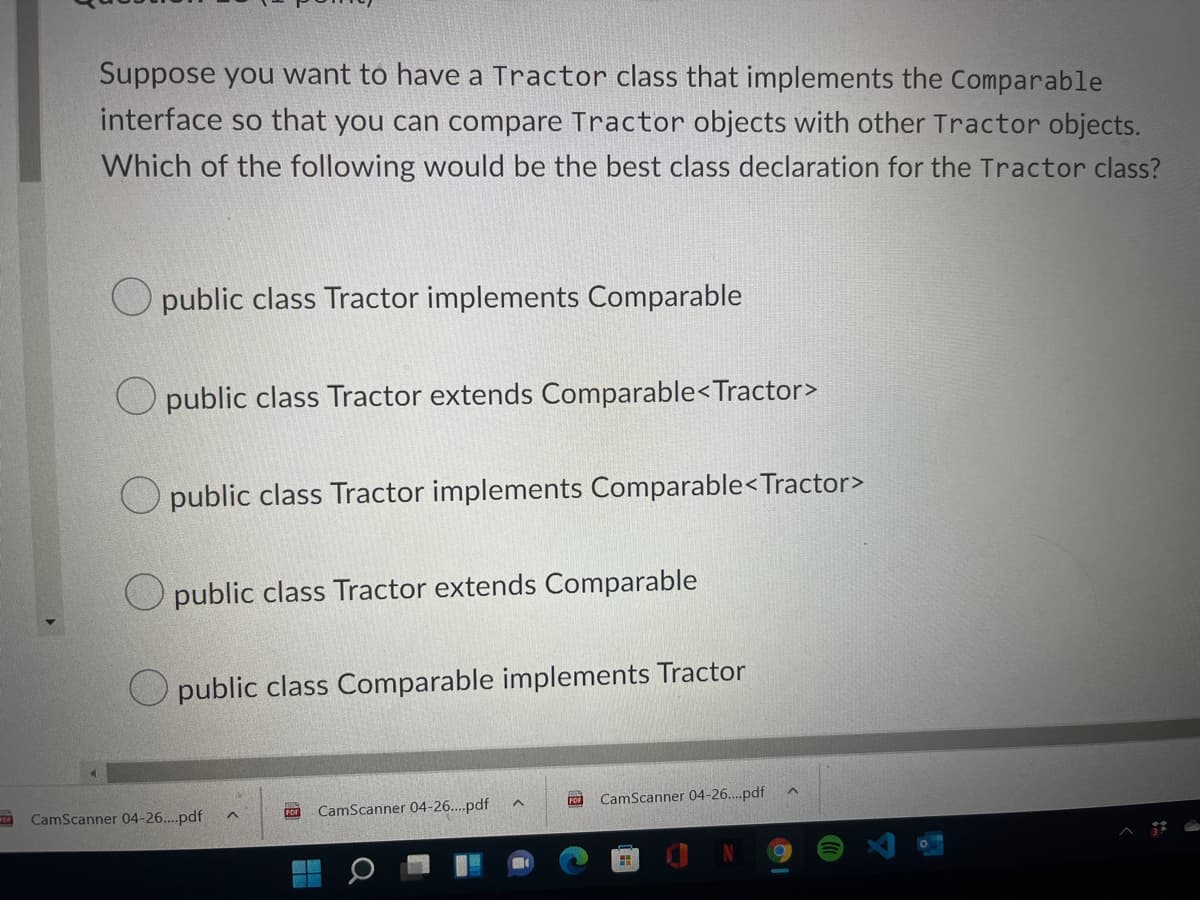
Suppose you want to have a Tractor class that implements the Comparable interface so that you can compare Tractor objects with other Tractor objects. Which of the following would be the best class declaration for the Tractor class?
Q: What is a perceptron network model? How could such a model be used to perform simple linear…
A: The answer is
Q: Wireless networks have a few difficulties that need to be addressed." Find three of these issues and…
A: It's infuriating when you're unable to connect to your wifi network. Worse still, the reasons for…
Q: For each graph representation, select the appropriate worst-case complexity: Adjacency Matrix:…
A: For each graph representation, we need to find the appropriate worst-case complexity.
Q: Let p, q, and r be the propositions p: Grizzly bears have been seen in the area. q: Hiking is safe…
A: Given p: Grizzly bears have been seen in the area.q: Hiking is safe on the trail.r: Berries are ripe…
Q: To what extent was it possible to prevent illegal activity in the area of computer science?
A: Given: Cybercrime, also called computer crime, is the use of a computer to do illegal things, like…
Q: Take a look at the difference between disaster recovery and business continuity planning
A: Business continuity planning lays out how a company will operate during and after a calamity. It may…
Q: What role may cloud computing play in the structure and operations of an organization?
A: Cloud computing is a common term for anything that involves delivering services hosted online. These…
Q: What kind of security system does an IDPS resemble the most? In what respects do these two systems…
A: IDPS or Intrusion Detection and Prevention System: This Intrusion Prevention System, also known as…
Q: What is the secret to a successful disaster recovery plan?
A: Answer: Take the Inventory Asset List:You will need to first draw all your belongings to see which…
Q: likes(John, C++). likes(Bob, C#). likes(John, Java) likes(Bob, Lisp). likes(Julia, Python).…
A: likes(John, C++). likes(Bob, C#). likes(John, Java) likes(Bob, Lisp). likes(Julia, Python).…
Q: How can an interactive system be designed to be user-friendly? Give an example to illustrate your…
A: Interactive system design and usability of these systems we design leaves an effect on the quality…
Q: Is it possible that machine learning algorithms and data formats may become dated?
A: Given: Each data format shows how the input data is stored in memory. This is important because each…
Q: Explain what "using dummy data in a specific run" means in a few words.
A: Explanation: Dummy data are similar to genuine data (that is, a collection of meaningful…
Q: Suppose we have a class called App that has a main method (so that it is a program as well as…
A: The answer is given below.
Q: In Pseudocode, the root node is supplied for a specified BST-based symbol table non-recursive method…
A: Can use the following algorithms to determine a key's rank in BST: Method 1:- Traverse the tree in…
Q: In computer science, what does it mean to "widen conversion" mean?
A: Foundation: Computer programming is the process of writing and running a computer programme that can…
Q: A function owl_and_rat() has been analyzed to run with O(n²) complexity to process a list of size n.…
A: As per the company policy, we are only allowed to solve the first given question among the two, So…
Q: What is detentions of process in operating system pleas give me correct answer
A: Answer the above question are as follows:
Q: Explain THREE (3) basic elements of access control.
A: ANSWER:-
Q: relationship among HCI and SDLC with the help of diagram
A: Life Cycle of Software Development The Software Development Life Cycle (SDLC) is a technique used by…
Q: public class HelloWorld{ public static void main(String[] args) { System.out.println("Hello,…
A: Please refer below for your reference: public static void main(){ St....;}
Q: "RUE or FALSE for each of the following statem« A threat is a possibility that someone identifies…
A: Lets see the solution.
Q: A flattened Neural Network for handwritten digital classification takes in 43X43 pixel images. How…
A: The answer is
Q: Explain the thread's most important features at a high level. Describe what a "hyper-thread" is.
A: What Exactly Is a Thread? Within a process, a thread is a route of execution, Multiple threads may…
Q: What are the various operators of pointer? Describe their u How will you declare a pointer in C++?
A: Lets see the solution.
Q: this code is in java. Explore the given classes. Implement a getter method on the WasteRobot class…
A: Answer
Q: How would you explain each of these jobs in your own words, with specific examples to back up your…
A: Given: Use examples to show how system programming and application programming are different. Then…
Q: The mean of a list of numbers is its arithmetic average. The median of a list is its middle value…
A: Start enter 9 number by defining median `calculate median calculate mean and print it
Q: Q1 The C.I.A. triad consists of computers, intrusion, and attacks. Q2 Information security is about…
A: C.I.A. triad consist confidently, integrity, and availability. Information security is about…
Q: In Pseudocode, the root node is supplied for a specified BST-based symbol table non-recursive method…
A: Binary Search Tree(BST) Binary Search Tree is a type of tree data structure with following…
Q: SELECT customer.LastName, COUNT(Orders.OrderID) As NumberOfOrders FROM orders, customers WHERE…
A:
Q: Assuming that a processor addresses are 2 Bytes or 16 bits size, what is the default increment of…
A: Ans.) Option A i.e. 2
Q: In computer science, what does it mean to "widen conversion" mean?
A: Given Question: What does "widen conversion" mean in the field of computer science?
Q: Distinguish between wireless networking challenges that may develop when two stations are visible at…
A: Given: The main difficulty is that everything, from cellphones to the company's security system,…
Q: Assembly language instructions may be optimized by writing compilers and assemblers that rearrange…
A: The solution to the given question is: PIPELINE/RISKS - Pipeline is an execution technique in which…
Q: create C language tic tac toe game Program requirements: The program should be designed…
A: Tic-tac-toe is a game of two players taking turns marking spaces on the grids with an X or O. The…
Q: It's more typical to use multithreading than to have a large number of processes operating in the…
A: Foundation: Within a single process, many threads may be generated, each running independently yet…
Q: It explains how incident teams are utilized in companies and how they are organized. A solid…
A: An episode reaction group is a group of information technology experts responsible for preparing for…
Q: What are the criteria for selecting an appropriate SPI approach for the company and project context?…
A: Software Process Improvement (SPI) methodology defines the sequence of actions, tools, and…
Q: The use of wireless networking has both benefits and drawbacks. Is wireless networking a viable…
A: Wireless networking cannot be used as the sole mode of transmission in the workplace; instead,…
Q: Consider the HelloWorld program public class HelloWorld{ public static void main(String[] args) {…
A: Answer in step 2
Q: Are algorithms and data formats in machine learning susceptible to becoming dated?
A: Are algorithms and data formats in machine learning susceptible to becoming dated? Machine learning…
Q: What are the criteria for selecting an appropriate SPI approach for the company and project context?…
A: SPI HAS THE FOLLOWING ADVANTAGES: The primary benefit of employing the SPI is its ease of…
Q: This is to explore running Prolog. We have family information as follows. For example, louis-mary…
A: Note: The answer of the first question is given. Please repost the remaining question to get their…
Q: What makes threads "light-weight" processes? When a new thread is started, what system resources are…
A: light-weight: These lightweight programmes have their own stack but may access shared data. Because…
Q: User-level and kernel-level threads differ in what ways? What are the circumstances in which one…
A: User-level threads are threads that the OS is not aware of. They exist entirely within a process,…
Q: What are the four different sorts of primtives used in standards to specify the interaction between…
A: PRIMITIVES: Service primitives are utilized for each protocol in the OSI reference model. Each…
Q: Examine the parallels and contrasts between Big Data and classic marketing research ideas.
A: Explanation: Traditional marketing and big dataBigdataBig data is described as a large volume of…
Q: Is it possible to sum up the primary goal of software engineering? What's the matter with this?
A: The primary objective of software engineering is to create robust and efficient software. Software…
Q: In what way does a code of ethics for software engineers serve a practical purpose?
A: The Answer is in step2
Step by step
Solved in 2 steps

- Your assignment for this course is to implement a beginner level Book Management System (BMS) in Java language. BMS contains 2 classes: Bookand BookList. The Book class has the following attributes: code: a String object, that hold the book’s code. title: a String object, that hold the book’s title. qua: int variable, that hold the number of books with the same code in the library. price: a double variable, that hold the book’s price. The BookList class contains only one data member: ArrayList<Book> t. When running the program display the menu as below:1. Input & add book(s) to the end.2. Display all books.3. Search a book for given code.4. Update the book’s price for given code.5. Find the (first) max price value.6. Sort the list ascendingly by code.7. Remove the book having given code.8. Load data from file.0. Exit.Notes:(1) The book’s code must be unique in the list.(2) Display all books in format (code, title, quantity, price).(5)…Is there a different way of doing this problem? Question: Create a class AccessPoint with the following attributes: x - a double representing the x coordinate y - a double representing the y coordinate range - an integer representing the coverage radius status - On or Off Add constructors. The default constructor should create an access point object at position (0.0, 0.0), coverage radius 0, and Off. Add accessor and mutator functions: getX, getY, getRange, getStatus, setX, setY, setRange and setStatus. Also, add a set function that sets the location coordinates and the range. Add the following member functions: move and coverageArea. Add a function overlap that checks if two access points overlap their coverage and returns true if they overlap. Add a function signalStrength that returns the wireless signal strength as a percentage. The signal strength decreases as one moves away from the access point location. Test your class by writing a main function that creates five access…Now we are going to use the design pattern for collecting objects. We are going to create two classes, a class AmazonOrder that models Amazon orders and a class Item that models items in Amazon orders. An item has a name and a price, and the name is unique. The Item class has a constructor that takes name and price, in that order. The class also has getters and setters for the instance variables. This is the design pattern for managing properties of objects. The setName() method should do nothing if the parameter is the empty string, and the setPrice() method should do nothing if the parameter is not positive. The class also has a toString() method that returns a string representation for the item in the format “Item[Name:iPad,Price:399.99]”. For simplicity, we assume an Amazon order can have at most 5 items, and class AmazonOrder has two instance variables, an array of Item with a length of 5 and an integer numOfItems to keep track of the number of items in the…
- Using Java - Creating an Abstract Class Shape II Create an abstract class "Shape" with the following specifications: an abstract method "area()" of return type double an abstract method "perimeter()" of return type double. Put your code in a Java source file named "Shape.java." I. Create a class "Rectangle" that extends the Shape class with the following specifications: Attributes: width, length Constructor: Implement a parameterized constructor needed initialize the data. toString: Implement a "toString" method that prints out the area and perimeter. Implement methods to compute the area and perimeter. II. Create a class "Circle" that extends the Shape class with the following specifications: Attributes: radius Constructor: Implement a parameterized constructor to initialize the data. toString: Implement a "toString" method that prints out the area and perimeter. Implement methods to compute the area and perimeter. III. Create a class "Triangle" that extends the Shape class…This is the question - Create an abstract NewspaperSubscription class with fields for the subscriber name, address, and rate. Include get and set methods for the name field and get methods for the address and subscription rate; the setAddress() method is abstract. Create two subclasses named PhysicalNewspaperSubscription and OnlineNewspaperSubscription. The parameter for the setAddress() method of the PhysicalNewspaperSubscription class must contain at least one digit; otherwise, an error message is displayed and the subscription rate is set to 0. If the address is valid, the subscription rate is assigned $15. The parameter for the setAddress() method of the OnlineNewspaperSubscription class must contain an at sign (@) or an error message is displayed. If the address is valid, the subscription rate is assigned $9. Code I was given - public class DemoSubscriptions { public static void main(String args[]) { PhysicalNewspaperSubscription pnsGood = new…Create the following classes based on the given declaration. Also, each class should have the default constructor. Just place the prototype of the constructors in the class but you dont have to implement them. The default constructor is a public member. A) CSUSM is an object of class University. Class University has the follow private attributes: -UnivName: string -UnivDepts: a vector of Department class -UnivStudents: a vector of student class -UnivAddress: string -UnivAge: int B) Each department has the following private attributes: -deptName: string -deptFaculty: vector of Faculty class -deptYearCreated: int C) Each student has the following private attributes: -studName: string -studYearOfStudy: int -studNumber: long -studCoursesTaken: vector of Course class D) Each faculty has the following private attributes: -FacName: string -FacYearofExperience:int -FacId: long -FacCoursesTeaches: vector of Course Class E) Each course has the following private attributes:…
- Consider this scenario, a mehtod in some class needs to access a data field in another class, here are two possible implementations: public class Process { /* * Check if student qualifies for financial help */ void check(Student student) { //.... } /* * Check if student qualifies for financial help */ void check(double studentGPA) { //.... }} In class Process, which check method you think is better, why? In other words, should we pass the object to the method or just the data member it needs? Disucuss the Pros and Cons of each approach (if any). Assume class Student has a mehod called getGPA( ).This question involves the design of a class that will be used to produce practice problems. The following StudyPracticeinterface represents practice problems that can be used to study some subject. public interface StudyPractice. { /**Returns the current practive problem */ String getProblem(); /** Changes to the next practice problem */ void nextProblem(); } The MultPractice class is a StudyPracticethat produces multiplication practice problems. A MultPractice object is constructed with two integer values: first integer and initial second integer. The first integer is a value that remains constant and is used as the first integer in every practice problem. The initial second integer is used as the starting value for the second integer in the practice problems. This second value is incremented for each additional practice problem that is produced by the class. For example, a MultPractice object created with the call new MultPractice (7, 3)would be used to create the practice…What does the super keyword represents and where can it be used? Give an example of a superclass and subclass. Be sure to make all the instances variables of the super class private. Include at least one constructor in each class and ensure that the constructor of the subclass calls the constructor of the superclass. Also include a toString method in both classes that returns the values of the instance variables with appropriate labels. Ensure that the toString method of subclass calls the toString method of the superclass so that the string returned contains the values of all the inherited instance variables.
- Assume we have a Book class that includes authorInit and pubYear attributes of type Stringand int, respectively, both set by the constructor. Write a compareTo method for this class, so thatbook objects are ordered based on the author’s initials first and then (if needed) the publication year. DO NOT assume the length of String type authorInit to be 2.Suppose you have written constructors for two JavaScript object classes, Fruit and Kiwi, and you want the properties and methods of the Fruit class (the base class) to be shared with the Kiwi class. What statement can you use to chain these object classes together in this way? Question options: A Fruit.prototype = new Kiwi(); B Kiwi.prototype = new Fruit(); C let Kiwi = new Fruit(); D let Fruit = new Kiwi();Write a class named Person with data attributes for a person’s name, address, and telephonenumber. Next, write a class named Customer that is a subclass of the Person class. TheCustomer class should have a data attribute for a customer number, and a Boolean data attributeindicating whether the customer wishes to be on a mailing list. Demonstrate an instance of theCustomer class in a simple program.

