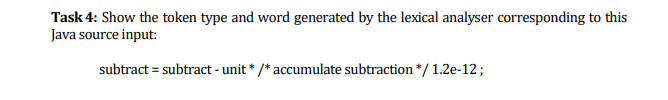
Task 4: Show the token type and word generated by the lexical analyser corresponding to this Java source input: subtract = subtract - unit * /* accumulate subtraction */ 1.2e-12;
Q: Given: F(X,Y,Z)=(X+Y)Z' + {(X'+Z') Y}' . Use boolean algebra method to derive its simplified Sum of ...
A: Boolean Expression: It always produces a Boolean value which means it is composed of a combination o...
Q: A step in a space vehicle checkout depends on four sensors (A,B,C,D) . Every circuit is functioning ...
A: Solution:-
Q: Enter user name to view: msmouse 1) username_fullname.py For lab, adapt the starter file to create a...
A: Here is the approach : Create functions for every work like view user , add user , edit user , dele...
Q: main parts, sub parts" of this laptop ( Spectre x360 2-in-1 16
A: The main or the sub parts of the laptop includes the following: Keyboard Battery Hinges Optical dri...
Q: What are the two important factors that affect whether or not you can use a binary search algorithm ...
A: The two important factors are,
Q: 1. Find the postfix equivalent of the following expression and evaluate the result. (4+8) *(7-5)/ ((...
A: Answer : 48+75-*42-22+*/
Q: outer and th
A: Routing: Routing is the process of picking a path across many networks, which might be one or more,...
Q: Why is it asserted that the String class's length() method does not deliver accurate results?
A: Introduction Why is it asserted that the String class's length() method does not deliver accurate re...
Q: You just recently opened a business that will be selling items on the Internet. You don’ t actually ...
A: Shipping fee is based on the weight of the item purchased Name of the store- Chegg Electronics ...
Q: Homework Assignment Chapter 4b Create a Java Project folder named Chap4b Create a class named Studen...
A: Actually, Java is a high level programming language. And also object oriented . It. Is a platform f...
Q: NameAndZipList NameAndZip - firstName : String - lastName : String - zipCode : String + main(args : ...
A: Given :- CODE IN JAVA It should have 2 java files one acting as server and other the client Please l...
Q: Java Consider the following class definition for an array-based stack implementation: pubic clas...
A: import java.util.Scanner; class Stack{ private int[] m_array; private int m_index; ...
Q: What are Java Loops? What are the three kinds of loops?
A: Introduction: The loop is a control flow statement that iterates a part of the program multiple tim...
Q: write code to determine if the first character in an input string str is an uppercase character.if t...
A: Introduction: write code to determine if the first character in an input string str is an uppercase ...
Q: hat is obtain from G − ε by merging 2 and 3 into a single vertex w. (As in the notes, v is adjacent ...
A: A graph can exist in different forms having the same number of vertices, edges, and also the same ed...
Q: To find the parametric polynomial equation df a curve using the the following infomation: f(t1) f(12...
A: We need to find the polynomial equation of the curve using the given information. The answer is NO...
Q: Write a program that allows two players to play the tick-tac-toe game. Your program must contain the...
A: Write a program that allows two players to play the tick-tac-toe game. Your program must contain the...
Q: What exactly is PCI DSS? What are the PCI DSS's twelve requirements? What are two recommended practi...
A: PCI DSS: The PCI DSS (Payment Card Industry Data Security Standard) is a collection of security guid...
Q: Describe the different types of collaboration technology and how they may be used to improve project...
A: Introduction: Collaboration Technology: Tools and technologies that facilitate group work, both in t...
Q: Write a java program using a two dimensional array and store a 10X10 multiplication table results in...
A: Program Explanation: Define a public class for implementation of the multiplication table Declare a...
Q: Write a loop to compute and print the number of occurrences of ‘!’ in a string named question. in ja...
A: public class Main{ public static void main(String[] args) { String question="hello! world!"; ...
Q: Contrast user threads with kernel threads.
A: Introduction The question is about Contrast user threads with kernel threads and here is the solutio...
Q: Write a single-line MATLAB expression that can be used to compute t cos (35°) V3n + log!35 3π+
A: Consider the given expression :
Q: Demonstrate how Service Oriented Architecture is done in practise and the distinction between SOA an...
A: Introduction: SOA is a framework that enables different services to communicate with one another. In...
Q: What is the name of the Ethernet cable's port? What is the name of the port that a dial-up modem use...
A: Answer Name of the port used by an Ethernet cable - LAN port Name of the port used by dial-up...
Q: Write a python program using loop to print the pattern given below %24 $$ $$$ $$$$ $$$$$$$$$$$S$$$ $...
A:
Q: What is dynamic method dispatch or runtime polymorphism?
A: Introduction What is dynamic method dispatch or runtime polymorphism?
Q: Please don't use replace(inbuilt method). Th about the words list. Write a python program to remove ...
A: Code: print("Enter the String: ")text = input() print("Enter a Word to Delete: ")word = input() text...
Q: itemswithtax (before_tax, tax): accepts a dictionary of items and their costs, and uses a dictionary...
A: def itemswithtax(before_tax,tax): # considering tax is given in percentage i.e. # 10% will tax = 10 ...
Q: What are the flaws in "Wi-Fi Direct" technology? Conduct a penetration test on "Wi-Fi Direct" techno...
A: Introduction: Wi-Fi Direct is a wireless technology that enables two devices to establish a peer-to-...
Q: Explain insulin pump control systems with neat diagrams of hardware and activity model. BIU AE
A: Fault Tree Analysis for the failure of “insulin pump” for the given case study is as follows:
Q: Base 16 Base 8 Base 10 2. Base 2 1. 3. 11000111.111101
A: As per our guidelines we are suppose to answer three subparts of a question, please post other quest...
Q: For each of the following simulation applications identify one discrete and one continuous-change st...
A: arrow_forward Step 1 Before identifying which variables are discrete and which are continuous, let i...
Q: What is the definition of Dual IP Layer Architecture?
A: The term "dual-stack" usually refers to a complete copy of the protocol stack from the application l...
Q: Group of answer choices A. list_t is already thread-safe and does not need any locks in any of its...
A: B. Add a lock to the list_t struct, initialize the lock in the List_Init, and then any operation tha...
Q: Compare and contrast Business Intelligence (BI), Machine Learning, and Data Mining. Provide real-wor...
A: Answer: Business Intelligence: This area is ...
Q: How to search horizontally a words in any matrix nxn, using "for" loops. For example, I want a metho...
A: // C++ program to check if the word// exists in the grid or not#include <bits/stdc++.h>using n...
Q: In the context of cryptography, what are the differences between a cipher that uses symmetric keys a...
A: Encryption is a type of process which logically changes the form of messages to protect it from som...
Q: What is data visualization, and how does it work?
A: DATA VISUALIZATION: The graphical depiction of information and data is known as data visualization....
Q: tween a mainf
A: Supercomputers: Supercomputers are the world's largest and most expensive computers. The Supercomput...
Q: Write a Java program, GradeApp that reads a series of exam scores given as integers in the range 0 t...
A: The Answer is
Q: Ex/ if the following message “paperx” is encrypted by using Hill cipher and converted into ciphertex...
A: The cipher key is the matrix used for encryption, and it should be selected at random from a collect...
Q: Question 3: Complete a Simulation table for checkout counter using the Event Scheduling/ Time Advanc...
A: The answer of this question is as follows:
Q: Write a console / terminal application in C language that will simulate and visualize the course of ...
A: Hi Dear!! Please Like my answer!! Your like will be valuable. Please find below for c code. Termin...
Q: What are the most important needs for cloud integration?
A: Cloud integration is a set of tools and technologies that allow real-time data and process exchange ...
Q: What are the two Windows apps that make use of the RDP protocol and port 33899?
A: Introduction: Application of RDP protocol and port 33899 in windows
Q: 1) Which of the following is NOT true about application software. Select 2 answers from the options....
A: 1. a. An example of this is Operating System. false b. It is a set of computer programs that helps a...
Q: Done in Perl. Someone gave the wrong answer. Write a Perl program to accept in an HTML string. Be a...
A: See the solution below-
Q: Show the string that would result from each of the following string formatting operations. If the op...
A: "Looks like {1} and {0} for breakfast".format("eggs","spam") Answer Looks like spam and eggs for bre...
Q: make each line of the following mips assembly program into a hex machine code A) addi $9,$0,1 add...
A: 1) addi $9,$0,1 I-type instruction op rs rt address/immediate addi $0 $9 1 6 bits 5 bits 5 bi...
Step by step
Solved in 2 steps with 1 images

- How long until there is a hiccup? Exactly how does context flipping relate to any of this?According to digitization levels, all three use cases inTrønderEnergi have already been implemented for the first three levels, summarized them.What code do i need to use to get an histogram output whereas the showing pictures of the table. For 32 bins and 1 for x values
- Aggregation is the process of unification of the outputs of all rules Select one:TrueFalseDescribe the input system used by a UX-generated lexical analyzer. Input system has many of the qualities that are desirable in a complier's input system and as such can be taken as charcteristic?If the levels of a factor (B) are not the same across the levels of a second factor (A) then factor B is said to be nested within factor A. True or false
- Question is for lexical tokens I need answer very quicklyH1. Show proper step by step explanationFrom a list of participants’ ids, find which id is missing from the list. The participant ids sorted in ascending order with a certain difference. Output explanation: the difference for each id is 12, from the list the missing number Is 120073 which is after 120061 and before 120085. Design an algorithm using C language! (PS: use divide and conquer algorithm)
- E. Determine the truth value for compound statement q using your assigned compound statement q and the corresponding assigned truth values without using a truth table. Show all steps. Can you add this part?A group's performance may be improved by using reflection.What options do I have for linguistic feature extraction using NLP? When it comes to putting my strategy into action, what choices do I have available to me? especially when working with a dataset that is only comprised of audio recordings

