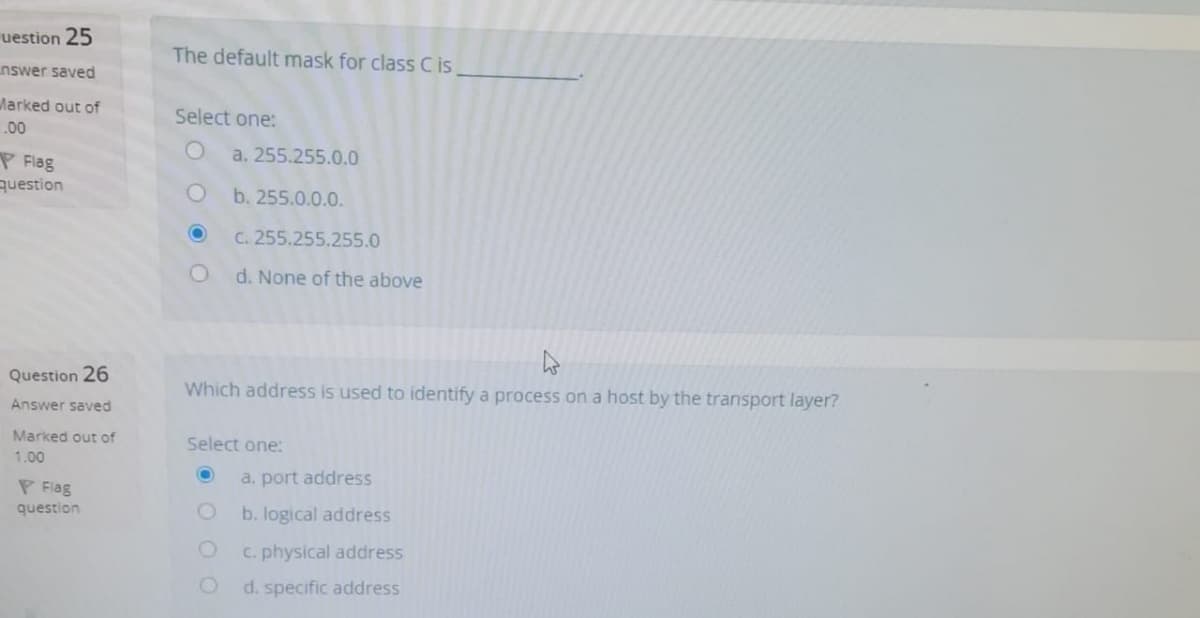
The default mask for class C is Select one: a. 255.255.0.0 b. 255.0.0.0. C. 255.255.255.0 O d. None of the above Which address is used to identify a process on a host by the transport layer? Select one: a. port address b. logical address C. physical address O d. specific address
Q: 1. What is a socket? 2. What does a client do when it has UDP datagrams to send? 3. What are the…
A: Socket :- It is a software structure within a network node of a network that is an endpoint for…
Q: Consider a fixed subnet partition of the class A network 104.0.0.0. a. How many bits will be…
A: Note: in Class A network:first 8 bits are network bitsand last 24 bits are host bits in subnet mask…
Q: QUESTION: Analyze the following script. What type of scan is the script used to run on a target…
A: Introduction:This is a python script which is scanning all the ports in a given host using multi…
Q: Is it feasible for a single Media Access Control (MAC) address to be used by more than one network…
A: Media access control: Is it possible for two different network interfaces to have the same MAC…
Q: Refer to the diagram below. What ACL would prevent any of the host computers from accessing any of…
A: Q1). The ACL would be applied to the Fa0/0 interface in the inbound direction. This would prevent…
Q: Is it feasible for a MAC address to be shared by two different network interfaces? Is there a reason…
A: Introduction: When a computer connects to a network, whether it be public or private, this is known…
Q: 6. Refer to the figure below. The NAT functionality of the router is enabled to provide Internet…
A: The IP address that needs to be changed is =>Option c. 192.168.2.2 As per the given diagram , the…
Q: Network Address: 135.60.0.0 with Subnet Mask 255.255.0.0 1. If we would like to build 7 subnets,…
A: As per our guidelines, only 3 sub parts will be answered. So, please repost the remaining questions…
Q: Assume that routing works in the diagram shown below. PC1 sends an ICMP ECHO request to PC2. Which…
A: For sending data packets from one system to another system, intermediate routers are used. These…
Q: One of the following port security violation modes causes the packets from unfamiliar source address…
A: protect--when the number of secure MAC addresses reaches the maximum limit allowed on the port,…
Q: How to implement USB authentication using raspberry pi using protocols like X.509?
A: Let us see the answer: There are also two micro-usb ports: one for charging through a micro-usb…
Q: Which of these is a MAC Address? A. 9C-35-5B-5F-4C-D7-IC-00 B. 00:0C:29:IC:BC:6B C. 0912 491 1234…
A: Let us see the answer:-
Q: As a network trainer for a large firm, you are needed to deliver a thorough explanation of the…
A: Before transferring an Ethernet frame to its destination, the switch checks a source address table…
Q: Q1: Choose the correct answer of the following 1- Storage facilities are distributed across all…
A: The answer for the above question is given in the below step
Q: 1. Which three statements describe differences between Storage Area Network (SAN) and Network…
A: Question 1. Which three statements describe differences between Storage Area Network (SAN) and…
Q: Consider the following topology. iMac2 wants to send a file to iMac3. iMac2 knows the destination IP…
A: Each device that is integrated into a computer network requires a network adaptor. This adapter…
Q: Given the following subnet mask, what is its representation in CIDR notation? 255.255.255.248 Are…
A: Please note we are only allowed to solve one question in one post. please post the remaining…
Q: 7. Identify the IPV4 address on your current network interface. Create a virtual MAC address pool in…
A: Follow these steps to configure the computer to obtain an IP address from a DHCP server. You must…
Q: What is the default subnet mask for a Class B address? Select one: a. 255.0.0.0 b. 255.255.255.0 c.…
A: A class B network may be a sort of network within the networking architecture. The networking…
Q: Let's say that you are given a network address block as 192.168.16.0/24, and are asked to divide it…
A: The answer is...
Q: iv. Class has the greatest number of hosts per given network address b)B a) A c)C d)D UDP needs the…
A: iv) Number of hosts in class A = 2 24 Number of hosts in class B = 2 16 Number of hosts in class C =…
Q: When a machine obtains its subnet mask with BOOTP instead of ICMP, it places less load on other host…
A: ICMP: The ICMP stands for the Message Protocol for Internet Control. It's a protocol for the network…
Q: If the default mask for network was 255.255.255.0 and after subnetting had become Subnet mask…
A: Given default subnet mask is 255.255.255.0 After subnetting , mask is 255.255.255.192 We have to…
Q: In the following MAC protocols, which one performs the worst in terms of throughput per packet time?…
A: The throughput per packet time is lowest for pure ALOHA, so it performs worst.
Q: consider 3 hosts (A , B and C) where A is running 3-TCP process, B has 1-TCP process and C is…
A: INTRODUCTION: We need to tell the number of socket.
Q: Assume Host C runs a Web server on port 80. Assume that this Web server accepts requests from Hosts…
A: INTRODUCTION: WEB SERVER: It connects to the Internet and facilitates the exchange of biological…
Q: Lapfopo Lapop2 120 hosts Switcho 61 Hosts vitch 1 30 Hosts 15 Hosts Swich2 Swich3 R2 R3 Sample MAC…
A: Given the following topology.By calculating a network address yourself(Calculation process:First…
Q: 10- What are two potential network problems that can result from ARP operation? (Choose two)? *…
A: The correct option will be Option(a) and Option(d) Option(a) Attackers can respond and pretend to be…
Q: MAC address on hosts, switches and routers? Explain Draw the switch table (fully populate
A: Do we need to configure MAC address on hosts, switches and routers? Explain Draw the switch table…
Q: Write any three differences between the Physical and Logical Addresses based on the table given…
A: Physical address is a permanent hardware level address embedded in a network interface card by its…
Q: Choose a set of class C, /24 addresses that could be successfully combined into a supernet that…
A: Super netting: It is a process of combining small networks into big networks. It is also called as…
Q: Suppose you are subnetting a class-C network address 192.168.65.0, which of the following subnet…
A: ANSWER IS OPTION B 255.255.255.240
Q: What is the error message that occurs when the manager sends Set_Request to a read-only object?…
A: Q1) What is the error message that occurs when the manager sends Set_Request to a read-only object?…
Q: What is the simplest way to tell the difference between an IP address and a MAC address?
A: Introduction: MAC - Media Access Control IP - Internet Protocol The easiest way to distinguish them…
Q: Q1. Given that Number of needed subnets:10 Network Address: 192.70.10.0 What is: Address class:…
A:
Q: (a) What is the network address for this host? (b) What is the range of host addresses in dotted-…
A: A) The subnet mask contains 27 1's and 5 0's. This means total number of host bits is 5. For network…
Q: 5. In 1024 QAM, a) how many bits are represented in a single point of the constellation diagram?…
A: QAM is the quadrature amplitude modulation , which is used as enhancement in WIFI 6. Constellation…
Q: What is the maximum addressable host with the above NA? 10.23.0.0/16
A: The range for the addresses is ranges from 0.0 to 255.255. Hence the last address is always 255.255.
Q: 192.168.10.10 255.255.255.O This address and mask example of Select one: O a. IPV6 b. Classful OC…
A: The above address and mask are the examples of subnetting.
Q: 192.165.1.0 11000000.10100101.00000001.00000000 255.255.255.224 11111111. 11111111.11111111.11100000
A: Here, The subnet mask contains 27 1's and 5 0's. This means the number of host bits is 5. A) For…
Q: Answer this? (a) What is the network address for this host? (b) What is the range of host…
A: The Answer is in Below Steps
Q: network on the internet has a subnet mask of 255.255.240.0. What is the maximum number of hosts it…
A: Given network on the internet has a subnet mask of 255.255.240.0 is in subnet mask represents both…
Q: Q. Which address is used to identify a process on a host by the transport layer? A. physical address…
A: According to the Question below the Solution
Q: Refer to the exhibit: Host A sends a frame with the destination MAC address as FFFFFFFFFFFF. What…
A: First lets under stand what happens with frame with destination MAC address FFFF,FFFF,FFFF.…
Q: 1.Which one is the smallest address class in classfull addressing? A C B D
A: Note: - As per the guidelines we can only answer one specific question at a time. Please resubmit…
Q: Question 2. Answer all the questions below Number of needed subnets 1000 Number of needed usable…
A: ANSWERS : Number of needed subnets 1000 Number of needed usable hosts 60 Network Address…
Q: If the default mask for network was 255.255.255.0 and after subnetting had become Subnet mask…
A: Question about Given default mask is 255.255.255.0 After subnetting mask is 255.255.255.192 We have…
Step by step
Solved in 2 steps

- This question relates to auditing command(s) that are ran on the MS2 VM.Use the auditing commands you have learned in class thus far to explore the MS2 VM. SSH into MS2 (from your Kali VM or your physical host). Question: What is the parent process of the SSH daemon service?4. [Socket] What is a socket? Suppose a process in Host C has a UDP socket with port number6789. Suppose both Host A and Host B send a UDP segment to Host C with destination portnumber 6789. Will both segments be directed to the same socket at Host C? If so, how will theprocess at Host C know that these two segments originated from two different hosts? 5. [Demultiplex] Define multiplexing and demultiplexing. Briefly explain how TCP demultiplexing isdifferent than UDP demultiplexing. 6. [rdt] Consider a reliable data transfer protocol that uses only negative acknowledgments.Suppose the sender sends data only infrequently. Would a NAK-only protocol be preferable to aprotocol that uses ACKs? Why? Now suppose the sender has a lot of data to send and the end-to-end connection experiences few losses. In this second case, would a NAK-only protocol bepreferable to a protocol that uses ACKs? Why?One of the following port security violation modes causes the packets from unfamiliar source address until sufficient number of MAC addresses drop below maximum value: Protect Shutdown Restrict Violate
- Exercises: 1. Use InetAddress class to display the local host address over the console. Your program should also print the name of address. 2. Create your own MyNetworkingServer and MyNetworkingClient applications as following: The client send two numbers and the server sends back addition of the two numbers. Contents: 1. InetAddress class 2. Socket class 3. DatagramSocket class and DatagramPacket classIn the context of switches the term “sticky” is used to describe: a. A port security mode, where learned MAC addresses are stored in non-volatile memory b. The process of tagging VLAN frames for the purpose of forwarding them over a trunk port c. A default VLAN where unused ports are placed d. A particular attack that fills the switching table with imaginary/false MAC addresses1. Persistent HTTP requires?a. 2(round trip times) + file transmission timeb. as little as two RTT for all the referenced objectsc. one file transmission timed. as little as one RTT for all the referenced objects 2. UDP has no connection between client & server?a. RCVR extracts sender IP address and portb. sender explicitly attaches IP destination address and portc. three other answers are incorrectd. no handshaking before sending data 3. A socket in computer networks is correctly defined as?a. A combination of IP address and port number, connected by a "/" symbolb. sender explicitly attaches IP destination address and portc. RCVR extracts from the socket, sender IP address and portd. A combination of IP address and port number, connected by a"." symbol 4. The data link layer provides?a. the functional and procedural means to transfer data between network entities and the means to detect and possibly correct errors that may occur in the link layer.b. the functional and procedural…
- consider 3 hosts (A , B and C) where A is running 3-TCP process, B has 1-TCP process and C is running 2-UDP process all process are trying to connect to a web server to download a file . How many new socket(s) will be created at the server side? Explain why?Question 4: (17 marks) From the MAC address 4E:A2:C6:BB:D9:C8 determine the IPv6 address Interface ID of the IPV6 address using the EUI-64 process. Answer the following questions related to Frame forwarding. (4 marks) Figure B Refer to figure B and identify the port(s) where the switch should forwards the frame. (2 marks) When the switch forwards the frame, determine which statement(s) are true and which are false? (2 marks) a) Switch add the source MAC address which is currently not in the MAC address table. b) Frame is a broadcast frame and will be forwarded to all ports. c) Frame is a unicast frame and will be sent to specific port only. d) Frame is a unicast frame and will be flooded to all ports. Inter-VLAN routing can be achieved via different ways: Legacy Inter-VLAN routing Router on a stick Layer 3 switch using Switched Virtual Interfaces “SVIs” Write s short report (200 words max), using your own…COM Assume a web browser at a client host (212.13.14.16) wants to send a message to a web server (156.10.10.2) but a firewall at the client's gateway (212.13.14.1) is configured to block all outgoing packets to 156.10.10.2. The client does have access to a VPN application (similar to the one used in the labs) and can use it to connect to a VPN server (130.16.10.2). Describe how the client should set up a tunnel to bypass the firewall so that the web browser can send a message to the web server (156.10.10.2). You must trace the pathway of the message originating at the web browser on the client host and headed to the VPN server explaining how it traverses through different layers (application, transport, network etc.) in the client host and finally reaches the VPN server application. You must also trace the relevant hops (i.e., the IP addresses) the packet navigates through along the way. You need not trace the reply message and you also don't need to focus on the encryption details.…
- What kind of secret handshake does a process running on one host use to recognize a process running on another host?How does a network partition failure differ from a general network failure? a) Messages get delivered but the data within them is corrupted. b) Messages may take a long and unpredictable amount of time to reach their destination since they have to take alternate routes. c) A group of machines will be able to communicate among systems within the group but not with other groups of machines. d) Messages to fail to transmit only in one direction. A client may send requests to a server but never receive responses.Think about the Scenario network. Assume that all hosts A and B have such a configuration. timeout parameters a. Convince the reader that increasing the size of the router's limited buffer may reduce output (out). b. Assume that all hosts adjust their timeout (like TCP) dynamically based on the router's buffer time. Will increasing the buffer size assist to improve output? Why?

