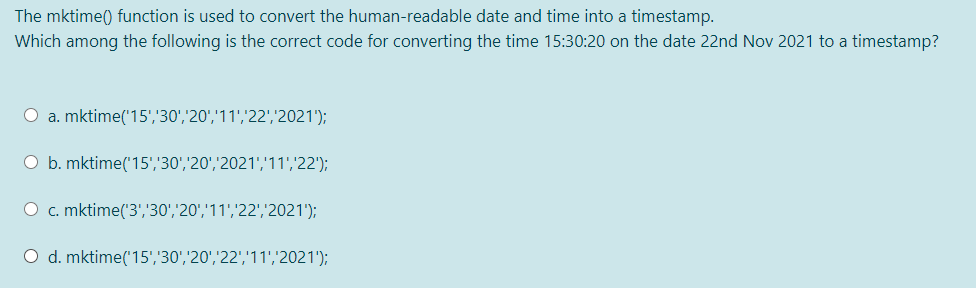
The mktime() function is used to convert the human-readable date and time into a timestamp. Which among the following is the correct code for converting the time 15:30:20 on the date 22nd Nov 2021 to a timestamp? O a. mktime('15','30','20','11','22',2021'); O b. mktime('15','30','20','2021','11','22'); O c. mktime('3','30','20','11','22',2021'); O d. mktime('15','30','20','22','11','2021');
Q: A system administrator gives each new user a new password using 7 pieces of password he has…
A: given data : A system administrator gives each new user a new password using 7 pieces of password…
Q: Accept from the user today’s date and your Date of birth in the format dd-mm-yyyy. Assuming you…
A: The program is to find the total time user had spend in sleeping, eating an reading. Sleeping and…
Q: Write a program that asks a data entry specialist to input employee information as comma separateu…
A: I have provided PYTHON CODE along with CODE SCREENSHOT and OUTPUT SCREENSHOT----------
Q: #include #include char sz_1[] = "Upper/LOWER."; char sz_2[] = "mIXeD CaSe.."; /* copies psz_2…
A: ASSEMBLY LANGUAGE: Assembly language is basically the low level language which is used for various…
Q: #include main() { int eno; char enam[20],sc,pc,s,p; float nhw,rph,gp,ot,sss,med,wtax,ins,td,np;…
A: The edited code is running successfully. If you are running the code in turboC include clrscr(). If…
Q: Which of the following best characterizes the statements, where A, B, and C are sets: A. (An B = C)…
A: The statements given:- (A∩B = C) is a set (A ∪ B / C) is a set
Q: Which of following function declaration makes a double parameter x to be passed-by-reference?…
A: Java is a programming language. It contains extensive libraries (package). It can be used to create…
Q: Which action fixes the error in the given code? OA) replacing line 6 with Long c2 = vI; O B)…
A: Java Code:- public class App { public static void main(String[] args) { int vI = 10; float vF =…
Q: Write a more generalized format() function that works like this: double amt = 1234.25; cout //…
A: Code: #include <iostream>#include <iomanip> #include <cmath> using namespace…
Q: © ৭:r * For the following script, if n=4 then the result is 24 -12 #include using namespace std;…
A: Correct Answer False is the correct option Explanation:- This is false because n was not declared in…
Q: Create a function that will test if a string is a valid PIN or not via a regular expression. A valid…
A: Input - String Ouput - Boolean Logic - for(int i = 0; i < pin.length(); i++){…
Q: Create a function that will test if a string is a valid PIN or not via a regular expression. A valid…
A: In this problem, we need to design the JAVA program. Input - String Output - Boolean Logic -…
Q: Using the fixed length field file called famous.dat make a one-line Unix command - using pipe(s) -…
A: the solution is given below:
Q: Which of the following is called ?insertion/put to operator اخترأحد الخيارات ;a. > ;b. < ;c.…
A: Please give positive ratings for my efforts. Thanks. ANSWER &lt; stands for lesser than…
Q: create a function using java to check csv file for the total number of different phone numbers
A: CSV stands for Comma Separated Value It is a simple file format which is used to store tabular data…
Q: Which of the following is the incorrect statement.? a. upper() function is used to convert the whole…
A: Actually, given question regarding function.
Q: change this code to do the same purpose and same output :
A: #include <iostream> using namespace std; void convert_from_AED(float amt, int to) { float…
Q: How many bytes are allocated by the compiler for the following string? char weather[]={“Hot…
A: The Final Answer is 10 bytes
Q: Create a function that will test if a string is a valid PIN or not via a regular expression. A valid…
A: Step-1: Start Step-2: function validate(string) Step-2.1: if length of string is equal to 4 or 6,…
Q: Draw a flow chart according coding statement below. #include #include #include #include using…
A:
Q: 1. Which code segment results in "true" being returned if a number is even? Replace "MISSING…
A: Given:
Q: Write a function that determines the number of missing entries for a specified column in the…
A: Function is provided in the next step:
Q: Create a function to test whether the character unit is a valid PIN or not in the normal way. Valid…
A: Your java program is given below as you required with an output.
Q: Create a function that will test if a string is a valid PIN or not via a regular expression. A valid…
A: In this problem we need to design the JAVA program. Input - String Ouput - Boolean Logic -…
Q: Which of the following is not true regarding the printf() function?
A: Answer is b: The printf() function will convert a double into an int if the %d code is used. "The…
Q: Determine whether or not the following expressions are valid, i.e., whether the left- and right-hand…
A: As per our guidelines we are supposed to answer only one question. Kindly repost other questions as…
Q: Which of the following code snippets represents well-written code and the best desi problem (assume…
A: For the given all the code Ans (B) is correct ans
Q: Which of the following is the correct name for the unary " operator in C and C++? O interpolating…
A: In computer programming, a dereference operator, also known as an indirection operator, operates on…
Q: The function show_bytes(val, pos) returns the byte at position pos for the integer value val; Let…
A: Little endian and Big-endian These are two ways of storing multi byte datatype. In little endian…
Q: Which header file has the functions scanf()? a. stdlib.h b. stdio.h c. string.h d. math.h
A: stdio.h => standard input output It has the information related to input/output functions
Q: q13) Which of the following is the incorrect statement.? a. upper() function is used to convert…
A: Answer: upper() function is used to convert the given string i.e., all lower case characters into…
Q: Which of the following is correct format specifier for the data type Character? a. %f b. %c…
A: Format Specifier: This term is utilized for specifying the specific data type of values to the…
Q: Transcribed Image Text - How many will the program write to the screen as a result of the following…
A: Solving following statements: 1. printf("%d", (7-5)*6-3/6) = 12 2. log((abs(exp(1)))) = 1 3.…
Q: sin z 3! 5! 7! 9! x2n+1 E(-1)(n=1) E(-1)" (2n – 1)! (2n + 1)! n=1 n=0…
A: Algorithm: StartRead x and n valueSet m=xSet x = x*(3.1415/180)Implement caculateSin() which takes…
Q: Create a function called tempF2C that will accept as input a single temperature in degrees…
A: Given :- In the above question, the term function is mention in the above given question Need to…
Q: On a previous question: "Write a C code that creates an honor list for the top six students at…
A: Explanation: The given program runs without any error. Here, we cross check the program in “Dev…
Q: Assume that numi starts with the value 3.2. What are the values of numi and num2 after the following…
A: Given data, num1 = 3.2 double num2 = 3.2 * 5.0 + 5.0 = 21.0. Now find values of num1 and num2.
Q: 4. Create a tuple that contains course codes: ('2400', '3560', '3140', '3040','4100', '4700',…
A: logic:- define a list list=['2400','3560','3140','3004','4100','4100','4700','4500'] store a…
Q: Create a function that will test if a string is a valid PIN or not via a regular expression. A valid…
A: Algorithm - Take one string as input. Now use the below logic pin.matches("^(\\d{4}|\\d{6})$");…
Q: Which header file has the functions scanf()? a. stdio.h b. stdlib.h c. string.h d. math.h
A: stdio.h generally contains many macros & functions for input and output. these includes scanf()…
Q: Create a function that will test if a string is a valid PIN or not via a regular expression. A valid…
A: In this problem, we need to design the JAVA program. Input - String Ouput - Boolean Logic -…
Q: The DateAdd function returns which data type? Select an answer: integer long date decimal Question…
A: The int data type is the primary integer data type in SQL Server.
Q: Fill in the blanks for the code below.
A: # assembly program# a0: rv# a2: base# a3: powersimplePow: addi sp, sp, -4 # reserve space for…
Q: Which of the following is called insertion/put to operator?
A: Explanation: &lt; stands for the less-than sign: <&gt; stands for the greater-than sign:…
Q: Given: (3,6) int numi, num2, newNum; double x, y; Which of the following assignments are valid? If…
A: Given:- int numl, num2, newNum; double x, y;
Q: Which of the following functions convert the first letter of each word in a given sentence to the…
A: Solution: option d is correct: void upstr(char *str){ int k=1; *str=toupper(*str);…
Q: Create a function that will test if a string is a valid PIN or not via a regular expression. A valid…
A: Algorithm - Take one string as input. Now use the below logic pin.matches("^(\\d{4}|\\d{6})$");…
Q: 10. Create a function based on the following information: Your mission is to encrypt a secret…
A: This C++ program takes the input of the string.
Step by step
Solved in 2 steps

- Which function maps values between 0 and 1? * a) Sigmoid b) Tanh c) Error d) None of the aboveWhich of following will add 3 bytes at where the operation is specified and initialize it to "Hi" with a null terminated character appended to it? Question 6 options: msg: .STRING "Hi\x00" msg: .ASCII "Hi\x00" .WORD "Hi\x00" msg: .ASCII "Hi" Select the statement that is true about a parameter of a function that is passed-by-value. A. the reference to the real parameter is passed to the formal parameter B. changing the formal parameter inside the function causes change to the real parameter C. the real parameter cannot be a constant and has to be a variable D. changing the formal parameter inside the function will not change the realPYTHON3 Complete the given function, encrypt_text that encrypts the variable text using the provided key by applying a modified version of Caesar’s Cipher with the following rules: The key will contain a word made up of the letters ‘u’ and ‘d’. The cipher will use the key to determine the direction of the shift, with a ‘u’ indicating that the character must be shifted upwards while a ‘d’ indicating a downward shift. The number of characters in the key will determine the number of positions to shift. The given text variable will only contain characters from the ASCII table with values between 32 and 126. If the key is invalid (empty string, contains characters other than u and d) or the text is invalid (empty string), no encryption occurs and the function returns the original text. If the text has more characters than the key, the key will loop through again to accommodate the additional text characters. An iterative approach should be used to solve this problem. Brute force…
- Which of the following is not true regarding the printf() function? a. The printf() function requires a format placeholder for each of the values it prints.b. The printf() function will convert a double into an int if the %d code is used.c. Any text in the format string that is not a format placeholder is printed exactly as it isfound.d. A single printf() function can be used to output more than one line of text.Hi create _ the function 10. Create a function based on the following information: Your mission is to encrypt a secret message (text only, without special chars like "!", "&", "?" etc.) using Caesar cipher where each letter of input text is replaced by another that stands at a fixed distance. For example ("a b c", 3) == "d e f" Input: A secret message as a string (lowercase letters only and white spaces) and number to move text Output: The same string, but encrypted Return: The same string, but encrypted.In cell B14, create a formula without using a function that adds 1 to the value in cell B12 and then multiplies the result by the value in cell B13. In this formula, use a mixed reference for cell B12 by including an absolute reference to row 12. Copy the formula from cell B14 to the range B15:B17 and then copy the formulas from the range B14:B17 to the range C14:H17.
- 2. Caesar Cipher Create a function that takes two arguments (text, key) and returns a new encrypted text using the key. For example, if the input is "a" and the key is 1, it should move that letter 1 step in alphabetic order so the output would be "b". Examples: caesar_cipher("hello", 5) "mjqqt" caesar_cipher("hello world", 1)"ifmmp xpsme" caesar_cipher("a", 2)→ "c" Notes: The input is only letters and spaces; no special characters. What is Caesar cipher? Method in which each letter in the plaintext is replaced by a letter some fixed number of positions down the alphabet. The method is named after Julius Caesar, who used it in his private correspondence. Try it out yourself: https://cryptii.com/pipes/caesar-cipher = Python String Methods: https://www.w3schools.com/python/python_ref_string.aspWhich of following will add 3 bytes at where the operation is specified and initialize it to "Hi" with a null terminated character appended to it? msg: .STRING "Hi\x00" msg: .ASCII "Hi\x00" .WORD "Hi\x00" msg: .ASCII "Hi"I WANT 3 FILES. TRIANGLE.H, TRIANGLE.Cpp and MAIN.CPP Given Triangle struct (in files Triangle.h and Triangle.cpp), complete main() to read and set the base and height data members of triangle1 and of triangle2, determine which triangle's area is larger, and output that triangle's info, making use of the relevant Triangle functions. Ex: If the input is: 3.0 4.0 4.0 5.0 where 3.0 is triangle1's base, 4.0 is triangle1's height, 4.0 is triangle2's base, and 5.0 is triangle2's height, the output is: Triangle with larger area: Base: 4.00 Height: 5.00 Area: 10.00
- On a previous question: "Write a C code that creates an honor list for the top six students at SMC. Your program does this by asking the user to enter the full names of all the top students, their majors, and their GPAs. Your program then prints the listing of the students in a sorted fashion based on their GPAs, in a three-column format (Name, Major, and GPA). " I received the below code, but I received errors when ran. Attached is a screenshot of the errors. Is there something I should change? #include <stdio.h>#include <string.h> int main(){ int i,n=10,a,j; char NAME[n][30],MAJOR[n][30],str[10]; float GPA[n]; //execute for loop from 0 to number of top student for(i=0; i<n; i++) { //input student NAME printf("Enter student NAME:"); scanf("%d",&a); scanf("%[^\n]%*c",NAME[i]); //input MAJOR name printf("Enter MAJOR:"); scanf("%[^\n]%*c",MAJOR[i]); //take GPA from user…Create a function using python that count the 10 words that appear most frequently in these tweets and print them in reverse order of frequency from the txt file named tweets.txt Example of result: Most frequent words************************covid, 204Fauci, 134the, 122…In python, create a function adjust_values() with the arguments binaries and data. Binaries are only composed of binary values, and data are made up of integers. If binaries[0] is ‘0,’ the data should only be an even number. If it is, don’t change its value. If not, subtract 1 from it. If binaries[0] is ‘1,’ the data should only be an odd number. If it is, don’t change its value. If not, add 1 to it. Return the edited data in tuples of 3. Should the length of data be greater than the length of binaries, simply keep the remaining values as it is. To do (example below): binaries = 01001101 data = [201, 22, 93, 23, 344, 21, 53, 56, 22] The output should be in tuples of 3: [(200, 23, 92), (22, 345, 21), (52, 57, 22)]



