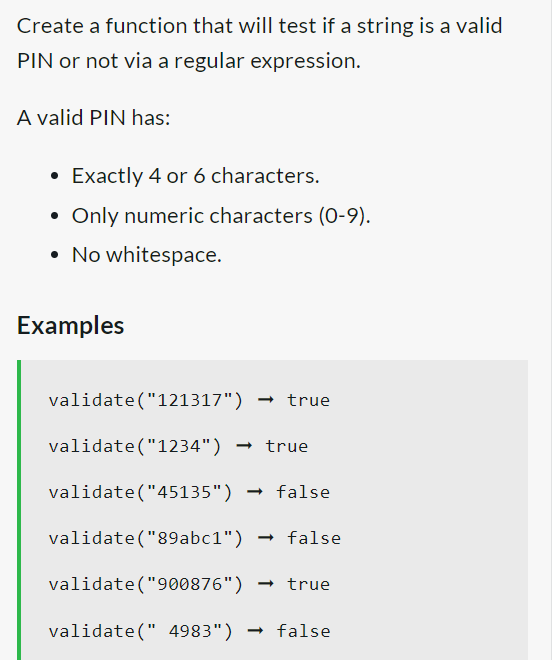
Create a function that will test if a string is a valid PIN or not via a regular expression. A valid PIN has: • Exactly 4 or 6 characters. Only numeric characters (0-9). • No whitespace. Examples validate("121317") validate("1234") → true validate("45135") → false validate("89abc1") → false validate("900876") → true validate(" 4983") → true → false
Q: s meant by the term "Symmetric Multiprocessing" (SMP)?
A: Introduction Symmetric Multiprocessing: Multiple processors working together to process data using…
Q: e a comparison table comparing HTTP and WebSocket difference
A: It is defined as : HTTP : The Hypertext Transfer Protocol (HTTP) is an application-level protocol…
Q: What possible use may a motherboard power connection in the SATA type serve?
A: It is possible for the power connection for a SATA hard drive to come from the motherboard. This…
Q: describe
A:
Q: d describing some advantages and disadvantages.
A:
Q: Lab6-1 Problem Submissions 1 2 3 4 5 6 7 899 Sample Output 0 Use a one-dimensional array to solve…
A: Here we have given the code in c++. you can find the program and output in step 2.
Q: 5. Creating Lookups 6. Automatic Lookups 7. Geospatial Lookups 8. External Lookups 9. KV Store…
A: 5. Creating lookups: Creating a lookup field not only improves the meaning of the data, but helps…
Q: What is JVM and is it platform independent?
A: Java bytecode (.class files) can be executed in a runtime environment that is provided by the Java…
Q: Considering the c++ program below, and [4, 5, 8, 3] as user inputs, answer the following questions:…
A: We need to answer the questions based on given C++ code.
Q: What is Information Technology strategic plan? Mention three Objectives of an IT Strategic Plan…
A: The IT strategic plan should outline a mission statement that states what it plans to achieve and…
Q: What is one type of mode for printing in Windows? EMF PNT PRT…
A: Answer:-. Spooled
Q: Write c# code to reverse order of words in string Input : this is me Output : me is this…
A: As given, we need to write a C# code to reverse words in a string. I have provided the complete code…
Q: ing computer gear. Do you believe that the strongest sales opportunities for recent college…
A: Introduction: To put it another way, the physical Computer hardware is a set of components required…
Q: An interesting application of a PLA is conversion from the old, obsolete punched cards character…
A:
Q: A computer consists of a processor and an I/O device D connected to main memory M via a shared bus…
A: Given that, on an average, six cycles are required by the instruction.
Q: The ______ folder is used to provide a user interface that lists documents the user has created or…
A: All installed apps' cached data and specific launch parameters are kept on the computer in the Temp…
Q: Create a Java Program using the scenario below. You made a $6,000 purchase for a car using an…
A: We need to write a Java code for the given scenario.
Q: Question 7: “../info/data.htm" is a(n) A. relative URL B. absolute URL C. none of above
A: In this question a Uniform Resource Locator (URL) is given we need to identify which type of URL is…
Q: 4. An ISP is granted the block 80.70.56.0/21. The ISP needs to allocate addresses for two…
A: If you specify the ISP as the address 80.70.56.0/21, the prefix length will be 21. • The number…
Q: To be more explicit, in what ways are the BIOS and UEFI passwords on certain PCs able to be…
A: Introduction: Basic Input-Output System, or BIOS, is what it stands for. It speaks about the…
Q: Where exactly are the weaknesses in the security architecture located?
A: Security architecture can be defined as a model which is unified as a design for the security which…
Q: Assume an 8088 is executing a program in which the probability of a program jump is 0.1. For…
A:
Q: How should someone continue if they have forgotten both the administrator password and the system's…
A: Remove the CMOS battery to reset your BIOS. This patch causes the computer to forget that you were…
Q: Fixed-price contracts, where the contractor bids a fixed price to complete a system development, may…
A:
Q: In java, create a program that uses printf to format currency in the proper form. The value in…
A: According to the information given:- We have to define the program that uses printf to format…
Q: c) What is the inductive hypothesis of a proof that P(n) is true for all positive integers n? d)…
A: Answer is given below a) P(1): 1^3 = (1(1+1)/2)^2 b) 1^3 = 1 (1(1+1)/2)^2 = (2/2)^2 = 1^2 = 1…
Q: To be more explicit, in what ways are the BIOS and UEFI passwords on certain PCs able to be…
A: On the windows which contains the system informations in the start panel and under the BIOS mode we…
Q: Question 8: The following statement is a right way to link to an e-mail address: Say HELLO!!!. A.…
A: We need to find the correct option regarding html email tag.
Q: To be more explicit, in what ways are the BIOS and UEFI passwords on certain PCs able to be…
A: The answer of the question is given below
Q: What are some best practises for configuring a firewall, and why are they recommended?
A: Introduction: To begin, configure the firewall to limit all traffic, with the exception of network…
Q: 3.10 Using the DUP directive, allocate space for 5 doublewords and 2 bytes in a data segment, then…
A: Using the DUP directive, allocate space for 5 doublewords and 2 bytes in a data segment, then fill…
Q: Many commands in Linux work exactly as they do in Linux, but why and how does this happen?
A: INTRODUCTION The Linux operating system is a piece of software that sudden spikes in demand on top…
Q: How should someone continue if they have forgotten both the administrator password and the system's…
A: To reset the BIOS on your device, you will need to remove the CMOS battery. Because of this fix,…
Q: How many times is the body of the loop executed? The numbers on left are line numbers. 1 int…
A: The correct answer is given below with explanation
Q: What distinguishes Windows OS from the Linux OS?
A: Linux is a Unix-like, community-developed, open-source operating system (OS) for PCs, servers,…
Q: Fixed-price contracts, where the contractor bids a fixed price to complete a system development, may…
A: Answer :
Q: What are the two advantages of layered protocols
A: Layered protocols refers to design of protocols with respect to the layer. Each layer has some…
Q: What is the name of the integrated memory cache that houses the CPU on the same die?
A: Cache memory is a chip-based PC part that makes recovering information from the PC's memory more…
Q: You can view the registry in a Windows environment by using which of the following commands at a…
A: Answer :- regedit
Q: Explain the distinction between the written sequence and the time sequence of an instruction.
A:
Q: What advantages might a RAID Level 2 system provide to a university payroll system? What, if any,…
A: The answer of the question is given below
Q: What other administration strategies for a firewall are you acquainted with? Explain.
A: Intro: Here is a list of a few of the most effective approaches for the administration of firewalls:…
Q: The Common TCP/IP Ports are an example. To correctly design security, businesses must comprehend the…
A: A PC network is a group of computers that share resources on or given by the organization hubs. They…
Q: Conduct research on the virtualization industry's security flaws and risks.
A: Virtualization is defined as the creation of virtual rather than actual operating systems, storage,…
Q: Report key similarities and differences between HTML and XML with the use of examples to distinguish…
A: NOTE: AS PER THE BARTLEBY GUIDELINE IF THERE ARE MULTIPLE QUESTION THEN WE ARE ALLOWED TO ANSWER ONE…
Q: What are some of the drawbacks of having pages that are fragmented?
A: Paging is a storage mechanism that allows OS to retrieve processes from the secondary storage into…
Q: A new type of keyboard is being developed with the same functionality as a regular QWERTY keyboard.…
A: We will be using priority encoder digital circuit to implement the keyboard
Q: How can the practical use of virtual servers and services be shown and explained?
A: Virtualization is becoming more substantial in the world of innovation as people realize how it may…
Q: a. If the last operation performed on a computer with an 8-bit word was an addition in which the two…
A: Your answer is given below with solution as you required.
Q: Assume an 8088 is executing a program in which the probability of a program jump is 0.1. For…
A:
In JAVA - Provide output ss
Trending now
This is a popular solution!
Step by step
Solved in 2 steps with 1 images

- The following functions are all intended to check whether a string representing a dna sequence contains any characters that are not 'a','c','g','t', 'A', 'C', 'G', or 'T'. At least some of these functions are wrong. Which ones are correct? A) def valid_dna1(dna): for c in dna: if c in 'acgtACGT': return True else: return False B) def valid_dna3(dna): for c in dna: flag = c in 'acgtACGT' return flag C) def valid_dna4(dna): for c in dna: if not c in 'acgtACGT': return False return True -------------------------------------------------------------------------------------------------------------------------------------------------------- valid_dna1 only valid_dna4 only None of them. valid_dna1, and valid_dna4 onlyWrite a function that returns true if the two provided license plates strings are visually similar. For this test, we will only need to consider the 26 English uppercase characters A to Z and the digits 0 to 9. def similar_license_plates(plate1: str, plate2: str) -> bool: return FalseWrite a program called p3.py. Write a function called validate() that takes a string as input, validates that it is a single letter, and returns the letter in lowercase.Example:validate(“A”) returns avalidate(“abc”) returns invalid
- Write a program that reads in a line consisting of a student’s name, Social Security number, user ID, and password. The program outputs the string in which all the digits of the Social Security number and all the characters in the password are replaced by x. (The Social Security number is in the form 000-00-0000, and the user ID and the password do not contain any spaces.) Your program should not use the operator [] to access a string element. Use the appropriate functions described in Table 7-1 below. Expression Effect strVar.at(index) Returns the element at the position specified by index strVar[index] Returns the element at the position specified by index strVar.append(n, ch) Appends n copies of ch to strVar, where ch is a char variable or a char constant strVar.append(str) Appends str to strVar strVar.clear() Deletes all the characters in strVar strVar.compare(str) Returns 1 if strVar > str returns 0 if strVar == str; returns −1 if strVar < str strVar.empty() Returns…Improve the given code below, make sure that the code will require input from the user. Problem: Write a JavaScript function that would accept a string and checks whether a passed string is palindrome? function check_Palindrome(str_entry){var cstr = str_entry.toLowerCase().replace(/[^a-zA-Z0-9]+/g,''); //changes the str -> lowercase && rem all non-alpha numeric charsvar count = 0; if(cstr === ""){console.log("String is not found");return false;}if((cstr.length) % 2 === 0){ //checks if the str is even or oddcount = (cstr.length) / 2;} else {console.log("Num4");if(cstr.length === 1){ //if str length === 1 then it is palindromeconsole.log("The string is a palindrome.");return true;} else {count = (cstr.length - 1) / 2; //if the str length is odd, ignores the mid char}}var p;for(p = 0; p < count; p++){if(cstr[p] != cstr.slice(-1-p)[0]){ //compares char that doesn't matchconsole.log("The string is not a palindrome.");console.log("\n");return false;}}console.log("The string…Write a Boolean function called contains_whitespace() that accepts a string as a parameter and returns True if the string contains one or more whitespaces (" ", "/t", "/n") characters, or False otherwise. Write a main() function to demonstrate how it works.
- Write a function to determine whether a string is a permutation of a palindrome given a string. A word or phrase that reads the same both forward and backward is known as a palindrome. Letters are rearranged in a permutation. The palindrome need not contain only words from dictionaries. EXAMPLEInput: Tact CoaOutput: True (permutations: "taco cat'; "atco eta·; etc.)Question 12 kana .Which of the following statements is false? The re module's findall function finds every matching substring in a string and returns a list of the matching substrings. The following code extracts all phone numbers of the form ###-###-#### from a string:contact = 'Wally White, Home: 555-555-1234, Work: 555-555-4321're.findall(r'\d{3}-\d{3}-\d{4}', contact) The re module's finditer function works like findall, but returns a greedy iterable of match objects. For large numbers of matches, using finditer can save memory because it returns one match at a time, whereas findall returns all the matches at once. Full explain this question and text typing work only We should answer our question within 2 hours takes more time then we will reduce Rating Dont ignore this lineThis function should reverse the words in a string. A word can be considered to be any characters, including punctuation, separated by spaces (only spaces, not tabs, \n etc.). So, for example, if s is “The Giants won the Pennant!” the function should change s to “Pennant! the won Giants The” void reverseWords(char *s)
- C++ is my answer correct ? Write a function to convert a given string : Answer: #include <iostream> #include <string> using namespace std; void toUpper(string &str) { for (int i = 0; i < str.length(); i++) { str[i] = toupper(str[i]); } } void toLower(string &str) { for (int i = 0; i < str.length(); i++) { str[i] = tolower(str[i]); } } int main() { string str = "khaled"; toUpper(str); cout << str << endl; str = "MOHAMMED"; toLower(str); cout << str << endl; return 0; } Write a function to calculate the sum of the even number from 1 - 100. Answer: #include <iostream> using namespace std; int sumEven() { int sum = 0; for (int i = 1; i <= 100; i++) { if (i % 2 == 0) { sum += i; } } return sum; } int main() { cout << sumEven() << endl; return 0; }Create a function that accepts a string (of a person's first and last name) and returns a string with the first and last name swapped. Examples NameShuffle("Donald Trump") - "Trump Donald" NameShuffle ("Rosie O'Donnell") - "O'Donnell Rosie" NameShuffle ("Seymour Butts") - "Butts Seymour" • There will be exactly one space between the first and last name. In c#The international standard letter/number mapping for telephones is: Write a function that returns a number, given an uppercase letter, as follows:def getNumber(uppercaseLetter):Write a test program that prompts the user to enter a phone number as a string. The input number may contain letters. The program translates a letter (uppercase or lowercase) to a digit and leaves all other characters intact. Here is a sample run of the program: Enter a string: 1-800 flowers1-800-3569377



