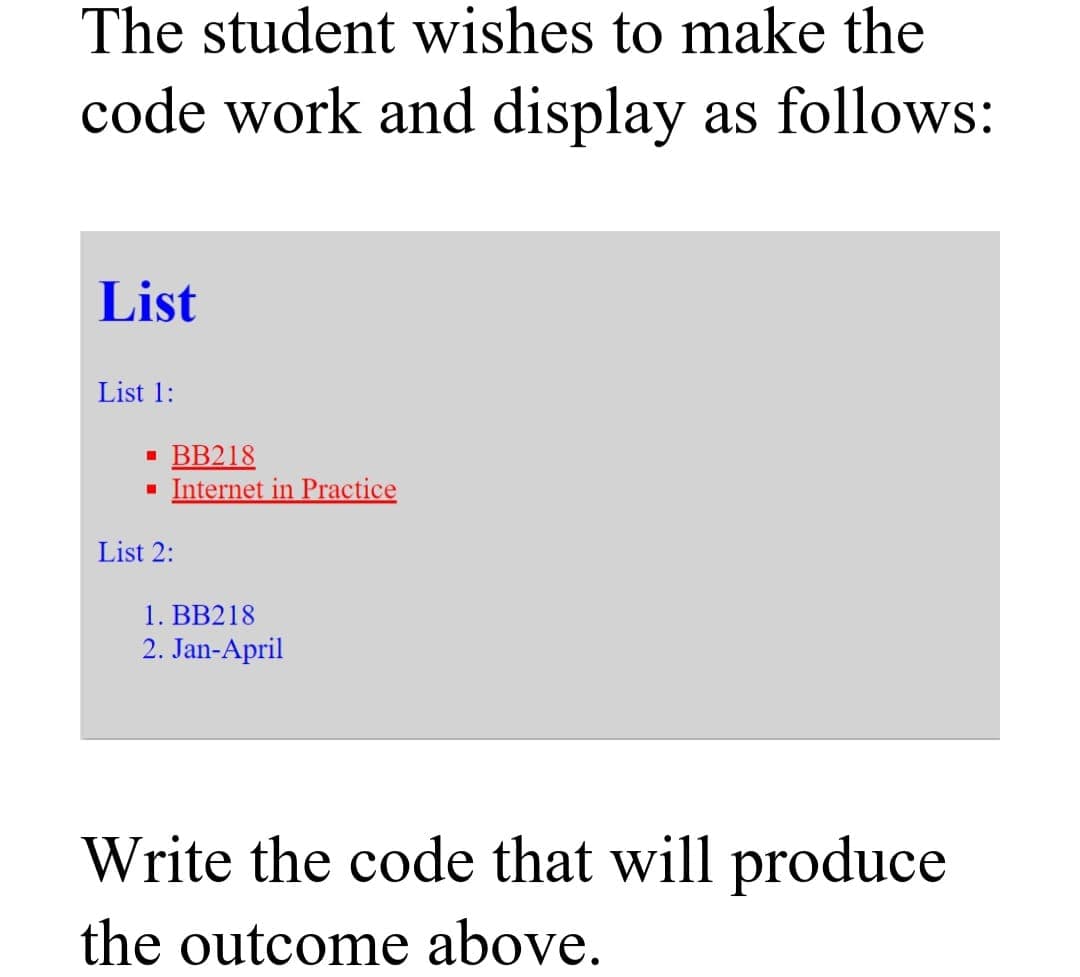
The student wishes to make the code work and display as follows: List List 1: · BB218 · Internet in Practice List 2: 1. BB218 2. Jan-April
Q: Provide a description for WaitMsg.
A: Introduction: In Javascript, the waitMsg method is used to show a message while waiting for an event...
Q: Write a python code to build regression models using the following learning algorithm
A: import matplotlib matplotlib.use('GTKAgg') import matplotlib.pyplot as plt import numpy as np f...
Q: Instruction: Write VB.NET code using For Loop to produce the output shown below:
A: Program Approach:- 1. Import System 2. Create the class Test 3. Create the Function Sub Main() a)Dec...
Q: In the context of switches the term “sticky” is used to describe: a. A port security mode, where le...
A: In the context of switches the term “sticky” is used to describe: a. A port security mode, where ...
Q: 1. Write a Verilog code to design a clock with period = 100 ns and a duty cycle of 35% by using alwa...
A: Please refer below for code as well as initial and always in verilog: 1) always: By using always sta...
Q: Dim a As Int
A: Given as, while(a<>1)- condition
Q: Networks 172.16.0.0/16, 172.20.0.0/16 and 172.23.0.0/16 can all be reached out of port S0/1/0 of a r...
A: For the given network as 172.16.0.0/16, 172.20.0.0/16 and 172.23.0.0/16 can all be reached out of po...
Q: 2. Write a program that returns the minimum of a single-variable function g(x) in a given region [a,...
A: Step 1 INTRODUCTION: Python is a strong general-purpose and high-level programming language. It is u...
Q: Make a view corresponding to SELECT CUS_AREACODE, SUM(CUS_BALANCE) AS TOT_BALANCE FROM CUSTOMER GROU...
A: Updateable View : It is a kind of deletable view. An updateable view is a type of view whose column...
Q: make a c prorgam input 5 7
A: As per the requirement program is written. Algorithm: Step 1: Write main()method Step 2: Define the ...
Q: oth RIP and OSPF discover a route to a particular network. The two routes are different, but their c...
A: Option a is the correct option. OSPF will be preferred because it has a lower administrative distanc...
Q: Give at least 10 HTML Tag. Give an example on how to use each inside the html document. 1. Example c...
A: The 10 HTML tags are: h1 tag p tag em tag b tag ul tag button tag img tag anchor tag i.e a tag div ...
Q: Given a Python list L of n positive integers, each represented with k = àlog nà + 1 bits, describe...
A: Given :- Given a Python list L of n positive integers, each represented with k = àlog nà + 1 bits,...
Q: I need a full computer science senior project
A: All computer science students need to prepare the projects which will be needed to finalize their ed...
Q: Determine which of the examples (R₁), (R, +), (M₂ (R), .), and (P(X), U) have idempotents. Try to fi...
A:
Q: d)How do video games work? e) How did video games impacted the world f) What is the environmental im...
A: d) how do video games work? Ans:- A primary processor, generally with numerous cores, is called the ...
Q: What does the Maple command mean?
A: Introduction: Maple command: The maple command is used to automatically finish the work of specific ...
Q: Consider the following edge-weighted graph G with 9 Vertie 40 60 90 50 70 20 30 80 10 130 150 120 10...
A: Steps: 1. Sort all the edges in non-decreasing order of their weight. 2. Pick the smallest edge. Che...
Q: In general terms, describe the main logical database design techniques and how they relate to each o...
A: In general terms, describe the main logical database design techniques and how they relate to each o...
Q: 1. Design a Windows application named Wallpaper App to calculate the number of single rolls of wallp...
A: Answer :-
Q: Write a c++ code that takes a 4-digit binary number as an input and converts it into decimal then ou...
A: Input : 4 digit binary number Output : Print the number in decimal Programming Language : C++ Exa...
Q: Using logical equivalence (not the table), show that the following propositions are equivalent and s...
A: Please upvote me Please. I need it badly. Please. 1. Given, ¬p ∧ (p V q) => (¬p ∧ p) V (¬p ∧ q)...
Q: What is the Big O of insert and search on a BST? ANswer is not O(1) O(N*lg N) O(N) ...
A: Answer The correct answer will be option (b) that is O(N) Explanation:- Binary search tree time comp...
Q: What is data mining and how does it work? Compile a list of data mining tasks?
A: Introduction: Data mining is the process of collecting information from data by identifying patterns...
Q: lement and demonstrate the 1-bit full adder on the Nexys A7 board with the following switch/LED conf...
A: // VERILOG CODE// module fulladder1bit(a,b,cin,s,co); input a,b,cin; output s,co; assign s=a^b^cin; ...
Q: What is the difference between a heuristic and an algorithm ?
A: Introduction: Heuristic - It is a technique for determining the best path based on a heuristic value...
Q: Specify the architecture of a computed unified device.
A: Architecture of computer unified device
Q: In computer memory, what are the three main types of data?
A: In computer memory, what are the three main types of data:-
Q: Write a php script to display 1! 2! 3! 4! 5! 6! 7! On one line There is no! At starting and ending p...
A: Algorithm: Start Iterate through the loop from x=1 to x=7 If x<7, print "$x!" Else print "$x" St...
Q: public Boolean insertBefore(String newItem, String itemToInsertBefore)
A: class link { Node h; static class Node { String str; Node next; Node(String a) { str= a; } } pub...
Q: Detail the components of the spheres of security paradigm. The document must have a sufficient quant...
A: Introduction: Information security is primarily concerned with preventing unauthorized access to dat...
Q: Fetch and decode Instruction Boolean condition RTL name Fetch TO)L: AR<--PC, SC<-- 0 TI)L: IR<.- M[A...
A: RTL I E AC DR IR PC AR M[AR] Initial Value 0 0 3024 3015 3015 314 ...
Q: how decay in memory retrieval happens and cite a personal experience.
A: the answer is given below:-
Q: please code in python You are given an array of strings arr. Your task is to construct a string fro...
A: Here I have created the function named finalString(). In this function, I have extracted the length ...
Q: Type the program output Input 6 3 target = int(input()) n = int(input()) while n <= target: pr...
A: Type the program output Input 6 3 target = int(input()) n = int(input()) while n <= target: print...
Q: 4. Complete the following truth table by finding the truth values of the Boolean expressions for all...
A: operators used in given expressions: && :And operator p && q is: true when both p an...
Q: Give the GetConsoleMode method a description.
A: Introduction: GetConsoleMode is a function that returns the current console mode.GetConsoleMode retu...
Q: What type of protocol is BGP? a. Link State Protocol b. Distance Vector protocol c. Brigde Gateke...
A: BGP PROTOCOL: A BGP stands for Border Gateway Protocol.The BGP protocol is the one of the most impor...
Q: Give Description for ReadKey
A: Description for ReadKey
Q: create a complete program that will accepts string of characters or sentence and print each word in ...
A: Since no programming language is mentioned, I am using python. Algorithm: Start Read a string Split...
Q: What is DNS scavenging, and how does it work? Describe the advantages.
A: Introduction: To avoid the accumulation of unwanted records, the DNS scavenging feature allows you t...
Q: In a three-tier design network where would access points be placed? a. Wireless Layer b. Access Lay...
A: Defined in a three-tier design network where would access points be placed
Q: Suppose that you plan to develop an e-commerce website for selling books. - Create 1 use case
A: Use case diagrams are the ones which are used in describing the high level function and system scope...
Q: What is the meaning of deep web and dark web? In your opinion which is more advantageous the dark we...
A: What is the meaning of deep web and dark web? In your opinion which is more advantageous the dark ...
Q: A(n) _____ network is a method of connecting to a network from the Internet using a code to protect ...
A: INTRODUCTION: A storage area network (SAN) is a dedicated, self-contained high-speed network that l...
Q: Write a function called multiplyMe in c programming which has a variable number of integers as argum...
A: Algorithm: Start Read number of elements n Read n numbers in an array Implement a method named mult...
Q: TCP session sends 50 packets per second over an Ethernet Local Area Network (LAN). Each packet consi...
A: TCP session sends 50 packets per second over an Ethernet Local Area Network (LAN). Each packet consi...
Q: Suppose a processor of Harvard architecture has 4 MB instruction memory and 32 MB data memory. If th...
A: solution
Q: Let A = {P, Q, R} be the set of nodes in a computer network. Show a communication link relation on s...
A: Given set of of nodes in set A= {P, Q, R} The communication link must contain 8 links and each commu...
Q: An address space is the area in a memory block where you can put things.
A: Introduction: Only binary bits of '0' and '1' are used in the computer world to process information ...
Step by step
Solved in 2 steps with 2 images

- A)Draw the linked node structure created by the following program and , B)List the output of program. struct node{ struct node *left; char letter; struct node *right; }; typedef struct node *NODEPTR; NODEPTR getnode(void); void displayList(NODEPTR); void main() { NODEPTR p , list , save; char one; p=getnode(); p->letter='A'; list=p; p->right=p; p->left=p; save=list; for(int i=2;i<8;i+=2) { one='A'+ i; p=getnode(); p->letter=one; p->left=save; save->right=p; save=p; printf("Letter= %c\n",p->letter); } list->left=save; save->right=list; list=p; displayList(list); } void displayList(NODEPTR head) {NODEPTR save; printf("\nLIST\n"); save=head; do {printf("%c ",save->letter); save=save->left; }while(save!=head); } NODEPTR getnode() { NODEPTR q; q = (NODEPTR) malloc(sizeof(struct node));…Consider again a list of hourly temperature readings from a fridge, as described in Question 9. Write a program that prints the hour at which the temperature first reached its maximum value. Assume position 0 is the reading at midnight (which will be printed as 0 : 00), position 1 is the reading at 1am (1 : 00), etc. The list has at least 1 and at most 23 readings. Write the corresponding code beneath each comment. Use variable names appropriate to the problem at hand instead of the generic names used by the pattern. The first step has been done for you. Note that the output is expected to have a space before and after the colon. For example: Input Result [4.7] 0 : 00 [4.7, 3] 0 : 00 [4.7, 3, 4.8] 2 : 00 start of code followsWhen the cursor is on the first letter of a word in vim, you may capitalize it by typing x, then p. Walk us through what transpires.
- A. write a code to find the number of students who pass CS course, when their marks>=40 . As thelist has 85 students. B. wite a code to print this shape: *** *** **** C. Write a code to find the area and parameter of a Tringle; Area =1/2 * High * BaseParameter= S1+S2+ BaseWhat would be the content of the list from left to right of the following code //each node contains a string and a pointer to the next Nodeclass Node{ public String name; public Node next; public Node(String name) { this.name = name; } public Node() { name = null; }}//********************************************//A list of Nodesclass Students{ Node front; public Students() { front = new Node(); }// add nodes to the list public void add(String s ) { Node cur = front; while(cur.next!= null) { cur = cur.next; } Node n = new Node(s); cur.next = n; n.next= new Node(s); } }class Driver{ public static void main(String[] args) { Students list = new Students(); list.add("a"); list.add("b"); list.add("c");list.add("d"); list.add("e"); list.add("f"); }}Perform the following. 1) Conver the infix expression a/b-c+d*e-a*c into postfix expression and trace that postfix expression for given data a=6, b=3, c=1, d=2 , e=4 .2) A student is asked to develop an application as part of mini project which reverses the order of numbers, such that the number that is placed last in the list will be removed first. The list can hold any number of elements. Implement the following menu based C++program for the same.
- in coral language Write a program that first gets a list of 5 integers from input. Then, get another value from the input, and output all integers less than or equal to that value. Ex: If the input is 50 60 140 200 75 100, the output is: 50 60 75 For coding simplicity, follow every output value by a space, including the last one. Then, output a newline. Such functionality is common on sites like Amazon, where a user can filter results.Write a statement that creates a two-dimensional list with 5 rows and 3 columns. Then writenested loops that get an integer value from the user for each element in the list.When the cursor is placed on the first letter of a word in vim, you need to input an x followed by a p. Explain the events that take place.
- A readinglist is a doubly linked list in which each element of the list is a book. So, you must make sure that Books are linked with the previous prev and next element. A readinglist is unsorted by default or sorted (according to title) in different context. Please pay attention to the task description below. Refer to the relevance classes for more detail information. Implement the add_book_sorted method of the ReadingList class. Assume the readinglist is sorted by title, the add_book_sorted method takes an argument new_book (a book object), it adds the new_book to the readinglist such that the readinglist remain sorted by title. For example, if the readinglist contain the following 3 books: Title: Artificial Intelligence Applications Author: Cassie Ng Published Year: 2000 Title: Python 3 Author: Jack Chan Published Year: 2016 Title: Zoo Author: Cassie Chun Published Year: 2000 If we add another book (titled "Chinese History"; author "Qin Yuan"; and published year 1989) to the…Allow student to insert one arbitrary string. Save the letters of the string into a list. Design and perform the following tasks and display your results: • Summarizing letters in a string. Write a function that receives a string and returns a list of tuples containing the unique letters and their frequencies in the string. Test your function and display each letter with its frequency. Your function should ignore case sensitivity (that is, 'a' and 'A' are the same) and ignore spaces and punctuation. When done, write a statement that says whether the string has all the letters of the alphabet. • Present descriptive statistics and graphs about the string data. • Sorting letters in different order and removing duplicates • Write a code that produces anagrams of a given string. An anagram of a string is another string formed by rearranging the letters in the first. program must accept inputs from a user, performs an operation using a userdefined function which will accept parameters and…Given two ArrayLists: list1=[10,20,30], and list2=[40,50], what is the content of the list1 after executing the following statement: list1.addAll(list2) a. [40, 50] b. [10, 20, 30] c. [10, 40, 50, 20, 30] d. [10, 20, 30, 40, 50]











