The two encryption/decryption methods are: Substitution cipher Caesar cipher You will need to research each and determine how to implement them. Remember in the case of the Caesar cipher there are 25 possible shifts, you must be able to choose or test for all 25 options.
The two encryption/decryption methods are: Substitution cipher Caesar cipher You will need to research each and determine how to implement them. Remember in the case of the Caesar cipher there are 25 possible shifts, you must be able to choose or test for all 25 options.
C++ for Engineers and Scientists
4th Edition
ISBN:9781133187844
Author:Bronson, Gary J.
Publisher:Bronson, Gary J.
Chapter10: Pointers
Section10.1: Addresses And Pointers
Problem 3E
Related questions
Question
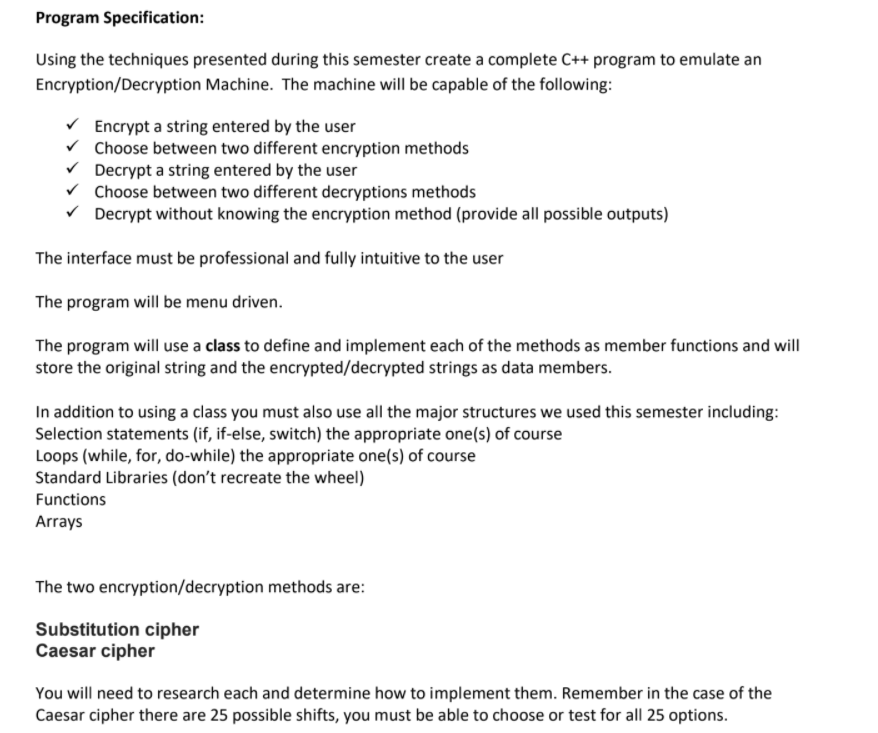
Transcribed Image Text:Program Specification:
Using the techniques presented during this semester create a complete C++ program to emulate an
Encryption/Decryption Machine. The machine will be capable of the following:
V Encrypt a string entered by the user
v Choose between two different encryption methods
V Decrypt a string entered by the user
v Choose between two different decryptions methods
V Decrypt without knowing the encryption method (provide all possible outputs)
The interface must be professional and fully intuitive to the user
The program will be menu driven.
The program will use a class to define and implement each of the methods as member functions and will
store the original string and the encrypted/decrypted strings as data members.
In addition to using a class you must also use all the major structures we used this semester including:
Selection statements (if, if-else, switch) the appropriate one(s) of course
Loops (while, for, do-while) the appropriate one(s) of course
Standard Libraries (don't recreate the wheel)
Functions
Arrays
The two encryption/decryption methods are:
Substitution cipher
Caesar cipher
You will need to research each and determine how to implement them. Remember in the case of the
Caesar cipher there are 25 possible shifts, you must be able to choose or test for all 25 options.
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 2 steps

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ for Engineers and Scientists
Computer Science
ISBN:
9781133187844
Author:
Bronson, Gary J.
Publisher:
Course Technology Ptr

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning