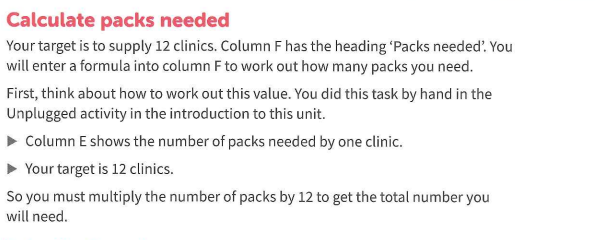
The World Health Organization (WHO) WAS ESTABLISHED BY THE United Nations in 1948. Its job is to promote good health around the world. The WHO uses technology to collect and analyze data about health needs and how to stay healthy. It provides supplies to 12 mobile health clinics. The table 1. Shows the extract of the data, number of packs needed by each clinic. There are 12 clinics.
Q: Object code is produced from source files by compilers and assemblers. The process of linking object…
A: Compilers and assemblers are crucial tools in software development as they convert high-level source…
Q: "Application programming interface" (API) explains it. What's the equipment's impact? Integrating it…
A: An Application encoding Interface (API) is message etiquette between diverse software machinery,…
Q: Please explain the concepts of Data Communications and Networking.
A: Data communication refers to transfer data signals sandwiched between two or more devices. The…
Q: To what extent does the Internet truly merit its recognition as an exceptional illustration of…
A: he Internet has undoubtedly earned its recognition as an exceptional illustration of information…
Q: The viability of the company is contingent upon the production of computers that possess superior…
A: In today's cutthroat business environment, survival frequently rests on a company's ability to…
Q: A comprehensive comprehension of firewalls is imperative in the realm of computer network security.…
A: In the realm of computer network security, firewalls play a crucial role in safeguarding an…
Q: What are the benefits of utilising a compiled language in contrast to an interpreted language? Under…
A: Programming languages can be broadly classified into two categories: compiled languages and…
Q: Your company's email server password changes must be verified by you. You don't think you changed…
A: What is Password: A password is a string of characters that provides authentication and access…
Q: Could you please provide more context or information about the topic you are referring to? What are…
A: For any company to exercise caution it is very important to exercise caution during the working of…
Q: Describe a scenario/design where a polymorphic behavior is utilized in C++. In the lecture this week…
A: Polymorphism is a fundamental concept of object-oriented programming (OOP) that allows objects of…
Q: Executable-attaching viral operation. Reworking the executable-why and how?
A: In the realm of software development and cybersecurity, the process of reworking executables has…
Q: What distinguishes software services from software modules?
A: The essential building blocks of software systems are software services and software modules, each…
Q: What distinguishes certificate-based authentication from password-based authentication? RADIUS…
A: What distinguishes certificate-based authentication from password-based authentication? RADIUS…
Q: Create a Java program about Music that demonstrates the function of Java Interface.
A: Here's an example of a Java program that demonstrates the use of interfaces in the context of music…
Q: Why use output devices?
A: Output devices are crucial in creation the contact stuck between a mainframe and a customer…
Q: Please discuss the ethics of crunching time in video game industry based on Social Contract theory
A: The ethics of "crunch time" in the video game industry can be analyzed through the lens of social…
Q: Which three database administration duties are most important?
A: What is database: A database is a structured collection of organized data stored electronically,…
Q: UML and EER models vary. UML development.
A: UML (Unified Modeling Language) and EER (Enhanced Entity-Relationship) models are both widely used…
Q: The virtual private network (VPN) is a technology that enables secure and private communication over…
A: A Virtual Private Network, in general called a VPN, is a means used to tender an added layer of…
Q: DBMS query optimisation strategies and DBA time savings.
A: Answer is given below
Q: Elucidate the advantages and disadvantages of every Linux installation alternative.
A: Linux offers various installation alternatives, each with its own advantages and disadvantages.…
Q: What are the essential characteristics that a desktop operating system ought to possess?
A: a desktop operating system should possess several essential characteristics to provide a reliable,…
Q: Using linked list Part 1: Creating C structures to hold crucial information C structure to store…
A: Given, C structure to store course information Course name Course code Semester (Bonus: Choice to…
Q: What are the internal mechanisms of SQL Server Integration Services?
A: A platform for creating data integration and workflow solutions, SQL Server Integration Services…
Q: Among the five distinct methods of memory management, which approach presents the most and least…
A: Stuxnet is often referred to as "The First Cyber Weapon" due to its unique characteristics and the…
Q: 5. Distributions (a) Write down the formula for the density of the exponential distribution. (b)…
A: The exponential distribution is a widely used statistical distribution that is commonly used to…
Q: Enumerate two issues related to simulation models.
A: Simulation models are numerical portrayals or computer programs that impersonate the way of behaving…
Q: 1. A router receives a packet with destination address (222.186.114.16) Show how it finds the…
A: Subnetting must be used to determine the network and subnetwork addresses for routing a packet with…
Q: implications of the ongoing trend towards the convergence of digital technologies for portable…
A: Portable electronic devices are electronic gadgets or devices that are designed to be easily carried…
Q: Project Optimization and regression: Exact and approximate methods to solve 0-1 Knapsack problem…
A: Start by using the greedy approach to solve the Knapsack Problem. This is an approximate solution.…
Q: What is the process for selecting an image on a computer that has limited resources?
A: Selecting an image on a computer with limited resources can be a challenging task. Limited resources…
Q: The viability of the company is contingent upon the production of computers that possess superior…
A: The first step in developing a low-cost yet resourceful compute device is balancing performance and…
Q: What is the rationale behind consolidating processes and programmes into subsystems within a sizable…
A: Your answer is given below.
Q: imilar to other emerging technologies, wireless networks are not immune to glitches and challenges…
A: Wireless networks, like any other technology, can experience glitches and challenges that can have…
Q: The term "local area network" refers to a computer network that spans a relatively small geographic…
A: Hello student Greetings A local area network (LAN) is a computer network that encompasses a…
Q: What are the possible modes of transmission for a virus across an organization's server…
A: Virus can permeate a server communications in a massive amount of ways. Some of these include: •…
Q: What is the specific numerical value that serves as the unique identifier for Java class files?
A: Class files are essential in the realm of Java programming because they contain compiled bytecode…
Q: When and how should you use a checklist during testing? Similarly to selecting a relevant real-life…
A: When it comes to testing, a checklist can be a valuable tool to ensure thoroughness and consistency.…
Q: Why use output devices?
A: Output devices play a vital role in computer systems by presenting information or data generated by…
Q: How does computer "local storage" work?
A: Local storage is the space on a computer or other device where data and files can be kept. Usually…
Q: The concepts of data flow diagram (DFD) smoothing and data process modeling have been delineated.
A: DFD smoothing is an iterative procedure second-hand in scheme plan to refine the Representation of…
Q: What is the visual representation of an individual utilising cloud storage as a means of data…
A: A visual representation of an individual utilizing cloud storage for data backup can help illustrate…
Q: What distinguishes the top server operating systems?
A: Unlike traditional systems, member of staff helping at table operating systems are calculated to…
Q: Discuss your project's CPU scheduling approaches.
A: The management and effective running of an organization's databases is mainly Controlled by database…
Q: The DBA's time saved by the DBMS's query optimisation algorithms.
A: Query optimization is an necessary Database Management System (DBMS) feature. It represent the phase…
Q: Wireless networks are vulnerable to malfunctions, which can have severe consequences. The user…
A: The open nature of wireless message makes wireless network more susceptible to Assaults and failures…
Q: Is the coherence and connection of software a significant factor? What is the impact of precise…
A: The coherence and connection of software is indeed a significant factor in software development.…
Q: Data or control parallelism? Which MIMD programme parallelism is best?
A: In practice, the best approach is often a combination of both data parallelism and control…
Q: Show instances of data manipulation, forgeries, and internet jacking.
A: In the realm of computer science, instances of data manipulation, forgeries, and internet jacking…
Q: What measures do various operating systems employ to safeguard against theft or corruption of the…
A: In the digital age, operating systems play a crucial role in safeguarding data and services from…
The World Health Organization (WHO) WAS ESTABLISHED BY THE United Nations in 1948. Its job is to promote good health around the world. The WHO uses technology to collect and analyze data about health needs and how to stay healthy.
It provides supplies to 12 mobile health clinics. The table 1. Shows the extract of the data, number of packs needed by each clinic. There are 12 clinics.
Step by step
Solved in 3 steps

- Consider the following task of building a zoo for Drexel! You've gathered m donors to fund the creation ofyour new park, and you've picked the location, so now you just need to choose the inhabitants. Ideally you'dget every animal imaginable, except you just don't have space. As it is, you have room to comfortably tk animals. Since you'd like to ensure that your funding doesn't dry up, you gure your donors should getto make requests about which animals will be kept. After sending out a few emails, you collect from eachdonor i a list of animals Ai which donor i would like to have at the zoo. As you suspected, the total numberof di erent animals appearing on the m lists exceeds k, so you won't be able to satisfy all of their requests.You decide the fairest thing to do is to ensure that at least 1 animal from each Ai is chosen.Given all these lists, we want to know whether we can select a set H of at most k animals to put in thezoo such that each donor i will be able to see at least one…In addition to being a Computer Scientist, you have a (side-hustle) business where you sell flower bouquets.Each of your flower bouquets consists of a certain number of red roses, with a minimum of 1 and a maximum of 6. This is the profit you make from each of your bouquets, which is a function of the number of red roses in that bouquet. You have 6 roses with you, and now you need to decide what bouquets to make in order to maximize your profit. I have presented this data as a set of tuples below. (Roses, Prices) = {(1,$3),(2,$5), (3, $9), (4,$13), (5,$14), (6,$18)} For example, if you make two 2-rose bouquets and two 1-rose bouquets (2+2+1+1=6), then your profit is 5+5+3+3=16 dollars. Note- for this problem you can have multiple rose bouquets in each category. However, if you make a 5-rose bouquet and a 1-rose bouquet (5+1=6), then your profit is 14+3=17 dollars. Determine the maximum profit you can make.You are a professor who has a summer business that makes custom sheds. During the three monthsof operation, you do not know the demand, but you know it will be 1 or 2 sheds for each month, andeach choice is equally likely. There is a storage cost of $100 per shed in each month that you haveany held over, and the most you can hold over is 3 sheds. Every month that you make any shedscosts you $300 to rent shop space, and each shed costs you an additional $200 in materials. You sellsheds during the summer for $1500 each, and any that are left over at the end of the summer yousell to a woodworker for $200 each.(a) Use probabilistic dynamic programming to determine an optimal production schedule.
- An electronics mega store is getting opened in "India". Under the same cap of Indian Mega store other two mega stores for North and South are getting opened. Under cap of North Store, two more sub-stores are getting opened. In this manner, total of 15 stores are opened which each having their own regions to cater to. At a particular time a store can handle at the most two sub stores. A particular store makes an earning of "X" amount for a given month. Ultimately at the end of month, all sub store submit their collected amount to their managing store. An model is needed to add more store, and print their monthly revenue. What do you think will be good data structure and how. What other facility can you provide to it. Implement the given model. using c languageA small engineering consulting firm is establishing a plan for next year. The director and thethree partners need to prioritize the eight projects. The expected profit for each project is givenin the following table together with the number of person-days required to prepare each project.Another measure included is the computing resource measured as the computer processingunit (CPU) time (in hours). You have been tasked to evaluate which projects they ought topursue based on efficiency. Given the sample data below, you plan to construct a dataenvelopment analysis (DEA) model:a. Which measures would you regard as inputs and outputs, respectively? Pleaseprovide your justification.b. Conduct data envelopment analysis, explain what type of DEA model is selectedand describe the project you regard as “efficient” and “inefficient”, respectively.c. Which project would you recommend and why?d. In what ways can you improve on your recommendation? You are free to openlysource for other datasets…A small engineering consulting firm is establishing a plan for next year. The director and thethree partners need to prioritize the eight projects. The expected profit for each project is givenin the following table together with the number of person-days required to prepare each project.Another measure included is the computing resource measured as the computer processingunit (CPU) time (in hours). You have been tasked to evaluate which projects they ought topursue based on efficiency. Given the sample data below, you plan to construct a dataenvelopment analysis (DEA) model:a. Which measures would you regard as inputs and outputs, respectively? Pleaseprovide your justification.b. Conduct data envelopment analysis, explain what type of DEA model is selectedand describe the project you regard as “efficient” and “inefficient”, respectively.c. Which project would you recommend and why?d. In what ways can you improve on your recommendation? You are free to openlysource for other datasets…
- It has been observed by management that some faculty members at theuniversity demonstrate a lackadaisical attitude toward teaching. They seldom go to class yet at the end of each month they receive full salary. Management has decided that GHs 200, 300, 400, and 500 will be deducted from a faculty’s salary if he/she offends once, twice, third time and forth time respectively in a month. This means that if a faculty member offends once in a month GHs200 will be deducted, if a faculty member offends twice in a month, GHs 500 (i.e. 200+300) will be deducted, if a faculty member offends three times in a month GHs 900 (i.e. 200+300+400), will be deducted and if a faculty member offends four times in a month GHs 1,400 (i.e. 200+300+400+500). Assuming all faculty members are on a flat salary rate of GHs 2000.a. Write a program to request for the names of four faculty members and number times he/she has absented him/herself from class in a month.One of them should have absented him/herself…An engineer working in the quality control laboratory of a construction company is 4800, 5810 and 5690 dm3 respectively.It needs sand, fine gravel and coarse gravel. There are 3 quarries where these can be bought. Of these stovesTheir composition is given in the table. How many dm3 from the quarries so that the engineer can make the necessary analysis?sampleUse the Cramer method to solve the need to be taken.To cut an 'n' centimeter-long gold bar into 2 pieces costs $n. When a gold bar is cut into many pieces, the order in which the cuts occur can affect the total amount of costs. For example, to cut a 20 centimeter gold bar at length marks 2, 8, and 10 (numbering the length marks in ascending order from the left-hand end, starting from 1). If the cuts to occur in left-to-right order, then the first cut costs $20, the second cut costs $18 (cutting the remaining 18 centimeter bar at originally length mark 8), and the third cut costs $12, totaling $50. If the cuts to occur in right-to-left order, however, then the first cut costs $20 time, the second cut costs $10, and the third cut costs $8, totaling $38. In yet another order, the first cut is at 8 (costing $20), then the 2nd cut is at 2 (costing $8), and finally the third cut is at 10 (costing $12), for a total cost of $40. Given an 'n' centimeter-long gold bar G and an array C[1..m] containing the cutting points in ascending order): a.…
- There are N cranes (numbered from 0 to N -1) arranged in a line along a road. Road begins at position 0. The K-th crane is located at distance P[K] from the beginning of the road and its arm length is equal to A[K]. The cranes cannot change their positions. There is a package, initially located at position B, that has to be moved by the cranes to position E. The K-th crane can pick up the package only if the distance between its position...... Task from I need solve by JavaFind minimum number of platforms required for railway station You are given arrival and departure time of trains reaching to a particular station. You need to find minimum number of platforms required to accommodate the trains at any point of time. For example: arrival[] = {1:00, 1:40, 1:50, 2:00, 2:15, 4:00} departure[] = {1:10, 3:00, 2:20, 2:30, 3:15, 6:00} No. of platforms required in above scenario = 4 Please note that arrival time is in chronological order. In java pleaseEvery campus has full time students who attend classes between 8h00 and 17h00 during theweek. Every campus also has part time students who attend classes between 18h00 and 21h00 onweekdays. In the scenario provided at the beginning of Q.1.1, it is stated that no student shouldbe allowed to access the campus after 12h00. The campus has decided to change this rule to state“no full-time student will be allowed to access the campus after 12h00. Part time students canaccess the campus as from 17h00 By making use of a class diagram, demonstrate how the concept of inheritancecan be used to represent the scenario provided at the beginning of thisquestion. Marks will be awarded as follow: Class diagram showing inheritance; Attributes; Instance methods; Access specifiers

