Then swap the first half of each block with the second half. For example: 7840 becomes 4078, 3013 becomes 1330, 6558 becomes 5865, and 9971 becomes 719 As a final result, the encrypted integer becomes 4078133058657199.Only if k and block known, it can be decrypted. Apply the same steps for the encrypt.cpp and decrypt.cpp files. This time ask the user to number, a k value and a block size value.
Then swap the first half of each block with the second half. For example: 7840 becomes 4078, 3013 becomes 1330, 6558 becomes 5865, and 9971 becomes 719 As a final result, the encrypted integer becomes 4078133058657199.Only if k and block known, it can be decrypted. Apply the same steps for the encrypt.cpp and decrypt.cpp files. This time ask the user to number, a k value and a block size value.
Chapter8: Data And Network Communication Technology
Section: Chapter Questions
Problem 41VE
Related questions
Question
100%
C++ Nothing too advanced please. Learning the basics
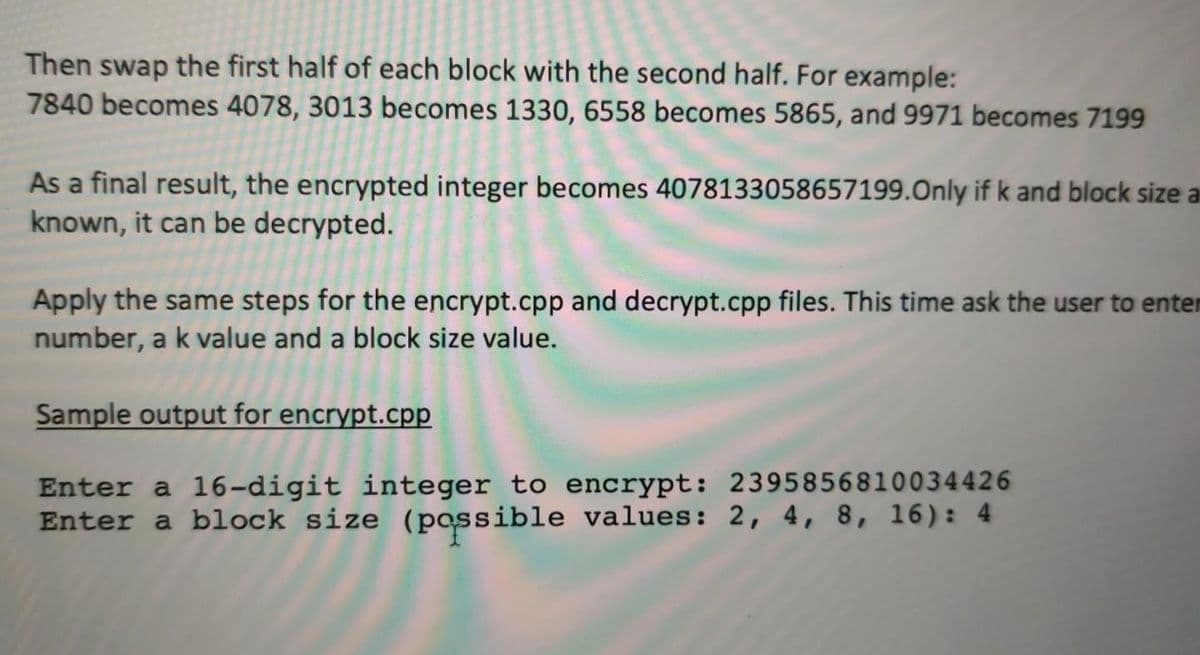
Transcribed Image Text:Then swap the first half of each block with the second half. For example:
7840 becomes 4078, 3013 becomes 1330, 6558 becomes 5865, and 9971 becomes 7199
As a final result, the encrypted integer becomes 4078133058657199.Only if k and block size a
known, it can be decrypted.
Apply the same steps for the encrypt.cpp and decrypt.cpp files. This time ask the user to enter
number, a k value and a block size value.
Sample output for encrypt.cpp
Enter a 16-digit integer to encrypt: 2395856810034426
Enter a block size (passible values: 2, 4, 8, 16): 4
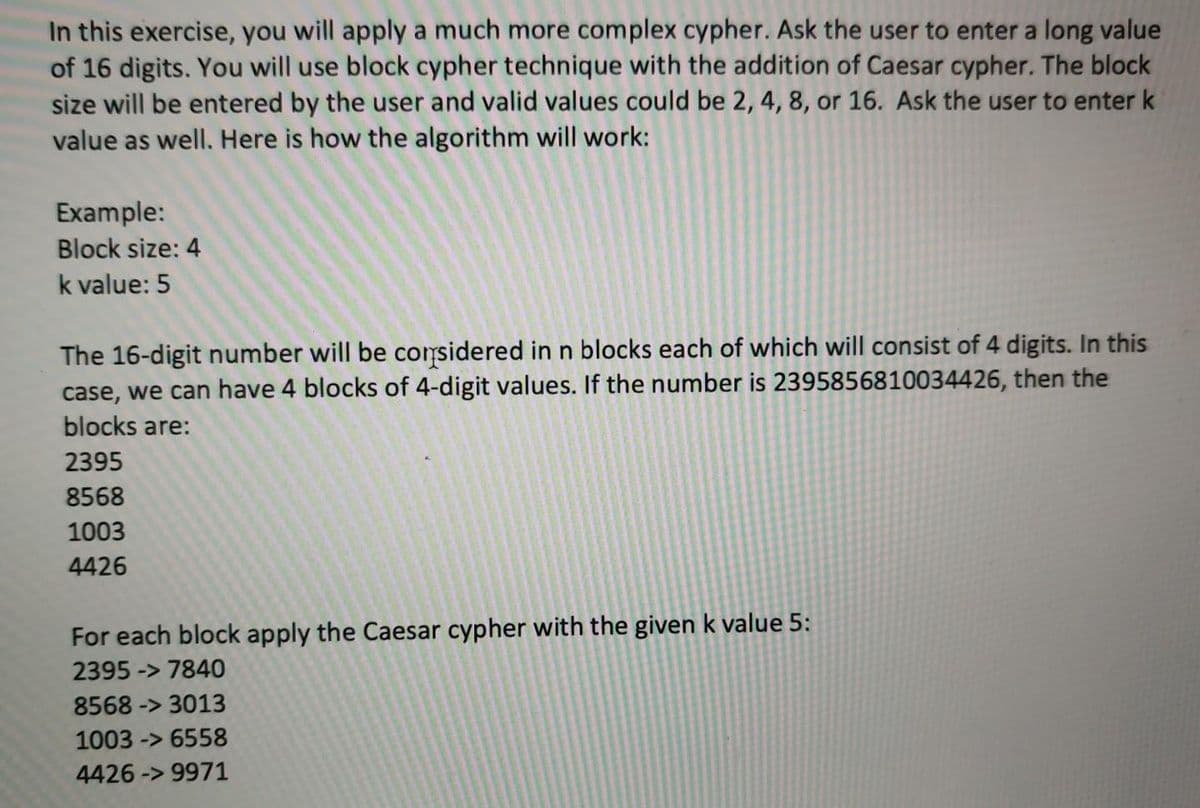
Transcribed Image Text:In this exercise, you will apply a much more complex cypher. Ask the user to enter a long value
of 16 digits. You will use block cypher technique with the addition of Caesar cypher. The block
size will be entered by the user and valid values could be 2, 4, 8, or 16. Ask the user to enter k
value as well. Here is how the algorithm will work:
Example:
Block size: 4
k value: 5
The 16-digit number will be corsidered in n blocks each of which will consist of 4 digits. In this
case, we can have 4 blocks of 4-digit values. If the number is 2395856810034426, then the
blocks are:
2395
8568
1003
4426
For each block apply the Caesar cypher with the given k value 5:
2395 -> 7840
8568 -> 3013
1003 -> 6558
4426 -> 9971
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 2 steps with 1 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning

Systems Architecture
Computer Science
ISBN:
9781305080195
Author:
Stephen D. Burd
Publisher:
Cengage Learning