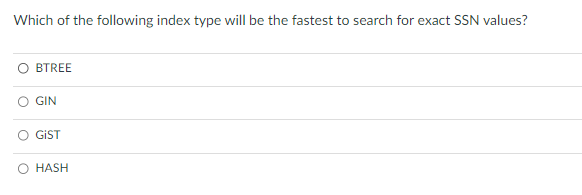
Which of the following index type will be the fastest to search for exact SSN values? O BTREE O GIN GIST HASH
Q: Open-source software is produced by the Network Funtime Company. The business features a small sales…
A: My main responsibility as the system administrator for the Network Runtime company is to protect it…
Q: There are several factors to take into account while discussing attribute inheritance.
A: An inheritance attribute is defined as the one that inherited from the parent class so that changes…
Q: Give an explanation of how starting with a blank sheet of paper is different from utilising a…
A: A data model A packaged data model makes the metadata of a consistent, industry-validated data…
Q: Why should you utilise an Open and/or Save As dialogue box in an application that deals with files?…
A: Benefits of Open and/or Save as dialog box in an application used in files: For OpenFileDialog…
Q: Please provide a brief explanation of Unicode.
A: A Unicode is a character encoding standard that has well-known recognition. It is a structure to…
Q: Briefly describe the procedure.
A: Process: The term "Process" refers to the instance that is being produced whenever the application…
Q: Clearly describe the device driver.
A: Items, especially mechanical or electronic devices, manufactured or modified for a specific purpose.…
Q: Clearly describe the motherboard.
A: Answer the above question are as follows
Q: Assuming a business has already implemented a KMS system, how can a manager ensure that internal…
A: Answer is
Q: What are the two parameters that a TryParse function expects from you when you write code?
A: "TryParse()" arguments include: If the "TryParse()" method successfully converts the string…
Q: 1. In using scanf the reference to data was always passed. When using printf the reference was…
A: Answer: We need to write the what is the differenced between the scanf and printf, compile time and…
Q: Talk about the potential for attackers to use your system as assault. platform for a widely spread
A: Introduction Our society, economy, and critical infrastructures have become largely dependent on…
Q: What is a case where the disjoint rule is applied to a supertype/subtype connection?
A: Disjoint rule: According to the disjoint rule, an instance of the supertype cannot be a member of…
Q: What benefits do enumeration types provide over a collection of named constants? What benefits does…
A: Benefits that enumeration type provide over a collection of named constant is:- 1.There is a lower…
Q: Why should you utilise an Open and/or Save As dialogue box in an application that deals with files?…
A: Let us see the answer:- Introduction:- The user can specify the drive, directory, and name of a file…
Q: Describe how software systems and software systems engineering have changed as a result of the…
A: Answer is in next step.
Q: Choose the approach that is ideal for a project involving an online pharmacy after comparing the…
A: Introduction: The development of software may be reduced to a breeze with the help of this method.…
Q: What distinguishes a text file from a binary file? Can a text editor be used to see a binary or text…
A: Text files are typically used to store a stream of characters and are those in which data is stored…
Q: Give a brief explanation of sign extension.
A: Sign-extension means copying the sign bit of the unextended value to all bits on the left side of…
Q: What two categories do the.NET Framework and the C# data types fall under?
A: C# data types: All data types in C# and the.NET framework can be divided into two categories. It's…
Q: What are the two parameters that a TryParse function expects from you when you write code?
A: In c# int.TryParse method accepts two parameters. first one is a string and second one is an integer…
Q: How does visual programming operate? What is it?
A: The solution is given in the below step with explanation
Q: Give a brief explanation of the concept of virtual machines.
A: Definition Virtual machine: A virtual machine is a straightforward piece of software that replicates…
Q: Description of Each request has its own object. b. Directions versus c. Model-View-Controller
A: objects for requests and responses The Hyper Text Transfer Protocol underlies the whole internet…
Q: It is recommended that you format CDs or hard drives at least seven times before discarding them…
A: Introduction: A WAV file is the ideal source format to use when producing an audio CD (MP3s are…
Q: The words prefix, infix, and postfix notation should be defined. What does the term "Cambridge…
A: Initial notation: Here, we move the operator's operands to the left. Ex: In this case, (A+B) is…
Q: Directions: Construct a program flowchart using a sequence control structure to answer the given…
A: In this program we will write the C program to input the temperature convert in Fahrenheit(F) and…
Q: What should beginners to computers keep in mind first and foremost?
A: The two aspects of a computer's hardware and software are the most essential when first learning…
Q: What are universal reference types? What are their functions?
A: Lets see the answer:
Q: Does a method that accepts an array as an argument really have access to the original array, or is…
A: Does a method that accepts an array as an argument really have access to the original array, or is…
Q: This may include anything from calculators and smartphones to supermarket scanners.
A: Explanation: These are the computer types: digital computerComputer.digital in a computer.combined…
Q: What does the keyword out mean when it is placed before an argument to the method in a method call?
A: keyword out: The C# language's out keyword is used to deliver arguments to methods as a reference…
Q: There are differences between type conversion, type coercion, and nonconverting type casts.
A: There are differences between type conversion, type coercion, and non-converting type casts. While…
Q: Assume that because a computer is becoming more of a need than a toy, you will build one to satisfy…
A: The answer to the question is given below:
Q: Explain the differences between supervised and unsupervised learning and why you value each kind of…
A: presented data is Explain the differences between supervised and unsupervised learning and why you…
Q: Why does Pinterest see Google as one of its biggest rivals? Pinterest prioritises the smartphone…
A: Why Pinterest see Google as one of its biggest rivals Pinterest sees Google as one of its biggest…
Q: Explain the following: Categories of backups: a. Full b. Differential c. Incremental
A: As per Bartleby's rules, we can answer only first 3 questions. I request you to post the other…
Q: What precisely is a grouping of items (also known as a container instance)?
A: In my view the grouping of items means :
Q: What does iteration in a loop really mean?
A: A loop is used to repeat a set of task multiple times.
Q: The words prefix, infix, and postfix notation should be defined. What does the term "Cambridge…
A: Three distinct but comparable methods of expressing expressions are infix, postfix, and prefix…
Q: Justify why the professional software produced for a customer is more than simply a collection of…
A: Software development lifecycle consists of many phases.
Q: There are several factors to take into account while discussing attribute inheritance.
A: answer is
Q: What's the difference between type compatibility and type equivalence?
A: Answer : Type compatibility Compatibility between types refers to the similarity of two types to…
Q: The definitions of "strict" and "loose" name equivalency are given.
A: GIVEN: The definitions of "strict" and "loose" name equivalency are given.
Q: What does having a digital envelope entail? Can you describe how it operates?
A: Digital envelope: A digital envelope is a secure electronic device. It is used to protect a message…
Q: This page discusses what a barcode is, how it's used, which industries use them, how it helps the…
A: Economic Policy Implemented: As a direct result of this, the policies that would become known as the…
Q: In just a few phrases, describe ALIGN.
A: Given: We have to ALIGN in just few Phrases .
Q: Description of Each request has its own object. b. Directions versus c. Model-View-Controller
A: The objects Request and Response Hyper Text Transfer protocol is what the whole internet is based on…
Q: Does a method that accepts an array as an argument really have access to the original array, or is…
A: Explanation An array may be supplied as a value to a function in "C" programming by specifying its…
Q: What should beginners to computers keep in mind first and foremost?
A: Beginners to computer must learn below skills 1. Basic microsoft word 2. Formulas and functions in…
Before question copy past not allow
Step by step
Solved in 2 steps

- This tutorial has all you need to know about DNS records, authoritative servers, and iterated and non-iterated queries.Q. What field specifies how long a DNS record should be cached for?Create a php file based on this table. If the search keyword is "*", the program should display all employees in the table. <?phpinclude "dbconfig.php"; $ip = $_SERVER['REMOTE_ADDR'];echo "<br>Your IP: $ip\n";$IPv4 = explode(".", $ip); if (($IPv4[0] == '10') || ($IPv4[0] == '131' && $IPv4[1] == '125')) { echo "<br>You are from Kean University.";} else { echo "<br>You are NOT from Kean University.";} $keyword = isset($_POST["keyword"]) ? $_POST["keyword"] : ''; $conn = mysqli_connect($servername, $username, $password, $dbname);if (!$conn) { die("Connection failed: " . mysqli_connect_error());} if ($keyword === '*') { $query = "SELECT * FROM EMPLOYEE"; $result = mysqli_query($conn, $query); if ($result) { $employeeCount = mysqli_num_rows($result); echo "<p>There are $employeeCount employee(s) in the database.</p>"; if ($employeeCount > 0) { displayEmployeeTable($result); } else {…
- This tutorial is everything you need to learn about DNS records, authoritative servers, and iterated and non-iterated queries.MD5 hash can be applied to which of the following data streams? .ppt file .doc file .dll file all of the above1) Update your SQL server to allow mixed authentication mode. You can do it in SSMS or by running the following TSQL code: use master; EXEC xp_instance_regwrite N'HKEY_LOCAL_MACHINE', N'Software\Microsoft\MSSQLServer\MSSQLServer', N'LoginMode', REG_DWORD, 2;
- You have the option of categorizing DNS records by category. Every single one of them has to be segmented into manageable pieces and accompanied with examples and arguments. Is it possible for an organization's email server and web server to have the same hostname?Which of the following has no partial or transitive dependencies? unnormalized data 1NF 2NF 3NFWhich of the following has no partial dependencies but can contain transitive dependencies? a. unnormalized data b. 1NF c. 2NF d. 3NF
- Which of the following has no repeating groups but can contain partial or transitive dependencies? unnormalized data 1NF 2NF 3NFType A resource records contain a. Mail Records b. IPv4 mappings c. Host Aliases d. IPv6 mappingsConsider the following command: UPDATE customerSET customer_id = customer_id --1; What happens if we run this command in MySQL? The customer_id in the customer table for all records is incremented by 1. The customer table has every customer_id set to the same value as it previously had. An error is thrown due to the --. The customer_id in the customer table for all records is decremented by 1.





