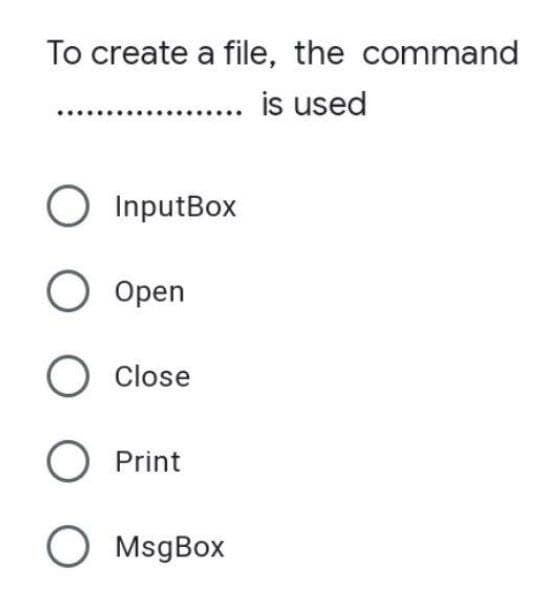
To create a file, the command is used O InputBox O Open O Close O Print O MsgBox
Q: With a PCI Express video card port and built-in video, switching to Windows 8 will provide you an…
A: We are searching for a graphics card that can fulfil the following specifications, which are as…
Q: Is having an internet connection beneficial or detrimental?
A: Please refer below for your reference: Having an internet connection is so far beneficial but it…
Q: The graphics card is the most power-hungry part of a high-end gaming PC.
A: Given: Even the Nvidia GeForce RTX 3090, which is currently the consumer GPU with the highest power…
Q: What decimal value does the 8-bit binary number 10010110 have if it is represented using Excess-M…
A: In Excess-M representation, 10010110 has a decimal value of 150. The excess-M representation in…
Q: 4. Given an array, arr[] = {90, 15, 10, 7, 12, 2), does this array represents a Max-Heap? if it…
A: I will explain it in details,
Q: There should be an increment of one level made to Flynn's taxonomy. At this level, what…
A: The categorization offered by Flynn : Systems that use the single-instruction, single-data (SISD)…
Q: The life cycle of a system can be represented by five methodical steps.What exactly are they?
A: Introduction: A secure SDLC contains five phases, which are as follows:-
Q: What are some of the problems that firms face while moving to disadvantages and advantages of this?…
A: Cloud computing is easing the process of utilizing of data and the delivery of computing services…
Q: 1. Word field bit is" O O Q4: If the size of the main memory is 64 blocks, size of the cache is 16…
A:
Q: As an alternative, could you maybe provide a more comprehensive explanation of the metrics that are…
A: Given the following: Could you offer a more detailed description of the software development…
Q: Cloud scalability: How does it all work? How does cloud computing develop, and what are the…
A: Introduction: The supply of resources such as data storage and processing power on demand without…
Q: How much power is required to operate a powerful gaming PC?
A: Intro: Name a premium gaming computer component that will probably use the most power. Gaming PCs…
Q: How well versed are you in computer networking? Describe the many kinds of computer networks…
A: A computer network is a collection of interconnected computers so they may exchange data or…
Q: What type of transport layer protocol do you use for video streaming?
A: Explanation: One of your most important jobs as a network administrator is to make sure that your…
Q: talk about nanotechnology in the clinical laboratory
A: Introduction: The study of substances on a size ranging from 0.1 to 100 nanometers is what is meant…
Q: You will be responsible for developing a comprehensive testing strategy when you take on this…
A: Software testing : Having filled in as software developers for countless years, we get to have…
Q: What is the performance guarantee for Splay trees?
A: Introduction: A splay tree seems to be a typical binary search tree (BST) from the outside. The key…
Q: What might a cloud migration business case look like?
A: Introduction: When we develop a business case, we are ultimately driving a representation of ROE.…
Q: The function below implements Quicksort. void Quicksort(int first, int last) { int i= first+1, j =…
A: Answer:- The correct option is C that is the worst-case time complexity of the given quick sort…
Q: The Internet is made up of a network of networks. What paved the way for it to happen in the first…
A: I will explain it in details,
Q: The Internet of Things (IoT) may be described. Consumer IoT vs. industrial IoT: What's the…
A: IoT: IoT has slowly and steadily captured almost every aspect of our lives — both at an industrial…
Q: Discuss four logical security controls that would increase the level of control available to the…
A: Introduction: Logical security controls are those that limit system users' access capabilities and…
Q: In the waterfall model, what are the stages? The Iterative Waterfall Model may also be used. If this…
A: Introduction: The steps of the iterative waterfall model are as follows:
Q: Consider Diffie-Hellman protocol. What is the Diffie-Hellman protocol used for? Given p = 13, g = 4,…
A: Answer first:
Q: To get the most out of a gaming system, you should run Windows 8 on top of a machine with built-in…
A: Gaming system: A gaming PC is basically an average computer with higher specs—faster speeds, sharper…
Q: In this day and age of RAID-capable storage, is it still important to make regular backups of an…
A: Start: By merging at least two hard disc drives (HDDs) or solid-state drives (SSDs) into a single…
Q: What exactly does it mean to practise defensive programming, and how can we do so?
A: programming for defense: Defensive programming is a kind of "defensive design" that aims to maintain…
Q: Does the internet of things have any historical predecessors or current uses in our time?
A: Introduction: Internet of things (IoT) refers to physical items (or groups of such objects)…
Q: In the event that it is possible to do so, what are the key differences between the von Neumann and…
A: The Harvard architecture: The Harvard architecture is a kind of computer architecture featuring…
Q: In the event that it is possible to do so, what are the key differences between the von Neumann and…
A: Inspection: An older kind of computer architecture known as the Von Neumann Architecture is based on…
Q: Explain how the cloud can be scaled. We need to know how cloud computing is expanding.
A: Answer: cloud scalability is expanding or descending the IT resources as per requirement. This…
Q: How can you tell the difference between the numerous kinds of networks in a computer? use a…
A: The question is to differentiate between different kind of networks in a computer.
Q: The Internet of Things (IoT) may be described. Consumer loT vs. industrial loT: What's the…
A: The question is to write the difference between Consumer IoT and industrial IoT.
Q: computing theory and practise For example, how does the DNS approach for connecting to a wireless…
A: Answer: DNS? DNS is Internet's phonebook. Domain names like nytimes.com and espn.com provide…
Q: Which high-end gaming computer component consumes the most power on a daily basis?
A: Start: Although just one graphics processing unit (GPU) is assumed to be present in these reference…
Q: It is vital to compare online data entry methods with batch data entry techniques. Automation of the…
A: Batch data processing method: The processing of a large amount of data at once is called batch…
Q: Could you please describe the difference between the Harvard and von Neumann computer architectures?…
A: Introduction According to the question the von Neumann architecture is that digital computer of the…
Q: Using the same resource at the same time might result in a stalemate.
A: Stalemate: In the game of chess, a stalemate is a specific kind of draw that happens when the player…
Q: Would it be possible for you to offer a more detailed description of the metrics that are involved…
A: Would it be possible for you to offer a more detailed description of the metrics that are involved…
Q: What is the difference between the Internet of Everything (loE) and the Internet of Things (IoT) in…
A: Answer: The Internet of Things (IoT) is sometimes confused with the Internet of Everything (IoE),…
Q: Which high-end gaming computer component consumes the most power on a daily basis?
A: Overview: People use electricity for lighting, heating, cooling, and refrigeration, as well as the…
Q: using Java, from a file, read a list of integers, insert them into an integer array and then print…
A: A file is being picked and opened in our program, and using a loop this Java program is going to…
Q: There should be an increment of one level made to Flynn's taxonomy. At this level, what…
A: The categorization offered by Flynn : Systems that use the single-instruction, single-data (SISD)…
Q: It is important to remember the relevance of wireless networks in developing countries throughout…
A: Start: Billions of individuals now have access to the internet and can participate in the modern…
Q: What are the advantages and disadvantages of using the internet as a storage medium? Is using the…
A: Computing in the cloud: The Internet, often known as "the cloud," is responsible for distributing…
Q: When using Windows 8 on a gaming machine that already has a video card installed and has room for a…
A: Introduction: To ensure that your gaming PC meets your requirements, you must construct it from…
Q: Conduct an online search using the phrase "object-oriented systems analysis." You've received quite…
A: The above question is solved in step 2 :-
Q: 1. What will be the output of the following statement: ? cout = 2 || !y == 8) (x != 3 && y == 8)…
A: In C++, the Order of precedence for operators in an expression is as follows: Highest () ^…
Q: 4. Write a MATLAB script to get the answer displayed as Command Window shown below. Use a for-end…
A: To find sum of the given series. %Taking user inputn = input("Enter the number of terms, n = "); y…
Q: What is the Effective memory access time for a machine with a cache hit rate of 90%, where the cache…
A: Hit Ratio = 90% = 0.90 So Miss Ratio = 1 - 0.90 = 0.10 Cache access time = 20 ns Memory access time…
Step by step
Solved in 2 steps

- Please help me. Description of what to do is below. A user must be able to enter any phrase or sentence that they would like to encrypt or decrypt Then if you can in a txt file create a gui for that program. An example is below in the photosCreate a file using any word-processing program or text editor. Write an application that displays the file’s name, containing folder, size, and time of last modification. Save the file as FileStatistics.java.Which statement creates an input file object named inData? Group of answer choices fstream inData; instream:inData; ifstream inData; inputfile.inData
- When you double-click a file in Windows Explorer, Windows knows which application to use to open it.M7Pro_Files Upload your accounts python file here What to do: U are to create a report for users that will list their student id number, last name, and first name. Also, you will list their username and email address The input file is linked below studentInfo.txt (opens in new window) Note: You are to add YOUR first and last name in the first row ( instead fo Mr. Cameron's), the ID SHOULDN'T be your real ID, just a imaginary number there The output file that your program will generate should look like the one linked below: loginInfo.txt (opens in a new window) Given a text file , studentInfo.txt , linked above (or U can use one you created) that contains only last name( field size = 10) and first name(field size is 10) and student id numbers (field size is 7) you will create a report that will generate the usernames as well as student email accounts as shown in the loginInfo.txt linked above. Notice that the login name consists of the first 7 characters of the last name, the…Explain your approach to reading individual bytes from a file Some of the data may be encrypted by adding 5 to a byte. If encrypted data has a value between zero (0) and four (4), what will the decrypted value be? GUI Design. Create a wireframe(s) for the GUI (See CRUD table in homework assignment) Create an algorithm for the required program. Submit a flowchart (as an image file
- Linux OS using terminal Create a directory and name it with any name you wish then enter the directory and create inside it a file then write a note about the weather, then add premissions to both directory and files; using absolute mode (octal) change the premission of the directory with 732 and finally change all permission file using symbolic mode.It's possible to open and edit four files called asiasales2009.txt if you create four file objects named asia, eu, africa or latin and use them to open and edit the files.What does a file extension do? Identify three file extensions and the application that created them for three files in a random folder on your computer. Most file extensions should be visible after right-clicking and selecting properties on a file (Microsoft Windows environment).
- The homework needs to be in Visual Studio :1)Where in the text box you can add by the button Add.2)Where you can open (by the button Open ) a file dialog by selecting a text file and all the contents should be display in the multiline box.3)Where you can save like a .textfile (by the button Save) a file dialog which all contents are in multiline box .The _____ option on an application file menu allows you to save the latest version of a file under its current name and its current location. a) backspace b) save as c) save d) deleteThe __________ control displays a standard Windows Save As dialog box. a. SaveAsDialog b. FileDialog c. SaveFileDialog d. StandardDialog











