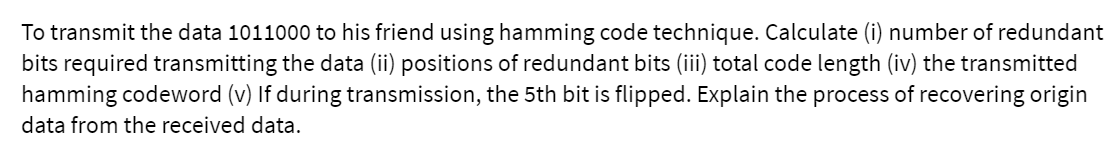
To transmit the data 1011000 to his friend using hamming code technique. Calculate (i) num
Q: Q4: Sketch the state diagram for a Mealy sequential circuit which investigates a single input…
A: Answer is given below-
Q: Explain the meaning of the word "linker" in only a few sentences.
A: Linker: A linker is computer software that combines many object files created by a compiler into a…
Q: . WAP to reverse string in Java by using while loop without reverse function.
A: The answer of this question is as follows:
Q: 7. Use K-Maps to find the minimal expansion as the Boolean sum of the product of each of the…
A: HI THEREI AM ADDING ANSWER BELOWPLEASE GO THROUGH ITTHANK YOU
Q: What advantages and disadvantages does a relational database management system have?
A: Relational Database Management System: A relational database management system is software that…
Q: Understand the difference between encoding and encryption
A: Encoding: It's the procedure for converting a string of words into a specific format for storage…
Q: Do you know of any examples of the Boyer-Moore string search algorithm? Give instructions on how to…
A: Boyer-Moore-Horse pox is a method for discovering substrings within strings.This method compares…
Q: rget language and machine lang
A: Given: target language and machine language
Q: To eliminate duplication in relational databases, what phrase is used to refer to the practice of…
A: Solution: The correct answer is: D:Normalization explanation: Normalization is the process of…
Q: Show that xy' + yz' + x'z = x'y + y'z + xz'
A: This theorem of set theory that expresses that the complement of the association of two sets is…
Q: Description Write a C program that will input 10 names of student. Each student name has 4 exam…
A: Code as par your requirement: #include <stdio.h> struct student { char name[20];…
Q: When does Oracle 12c automatically generate an index for a table that it has been given access to?
A: Answer:
Q: When written out in its whole, the acronym GSM refers to what exactly? Your phone wouldn't be able…
A: The GSM (Global System for Mobile Communication) digital network is well-known among mobile phone…
Q: Imagine that you are employed by a company as a system analyst for the company that you work for. Do…
A: System development life cycle: The systems development life cycle (SDLC) is a project management…
Q: Many controls have characteristics that influence whether or not they are shown on a form during…
A: Controls in graphical user interface programming: Controls are fundamental elements of graphical…
Q: In order for an OS to function properly, a characteristic known as "mutual exclusion" (ME) is…
A: answer is
Q: When an attacker can successfully alter certain ciphertext blocks without knowing the key used,…
A: Each section of plaintext is encrypted independently in an ECB. This method has a disadvantage in…
Q: Show that De Morgan's Law applies to Boolean algebra, by showing that for all x and y, (x ⋁ y)’ =x’…
A: Demorgans law: Demorgans law state that the complement of the union of two sets is equal to the…
Q: Show how Service Oriented Architecture (SOA) and microservices are different and how they work…
A: Introduction: SOA is a framework that enables different services to communicate with one another. In…
Q: The fact that computer security is almost often considered as an afterthought rather than an…
A: Answer : Yes , it is true that Computer security comes after the development phase but it make a bad…
Q: What kinds of software tools can we use to successfully finish the firmware development project?
A: For development of firmware project, the software tools are used. With help of tools many are…
Q: SAMPLE DISPLAY OUTPUT: Arithmetic Operation Enter number 1: 10 Enter number 2:5 [A] [+] Addition [S]…
A: logic:- read two number num1 and num2 start while true loop display menu in the above format. read…
Q: Describe the internal and external security dangers that exist in the twenty-first century.
A: Internal and External Security threats : Internal attackers have greater advantages than external…
Q: A look at how big data allows businesses to keep tabs on vast quantities of personal information.…
A: Extensive data collections that surpass actual databases and data processing infrastructures are big…
Q: 0006
A: Solution - In the given question, we have to tell how many nodes are visited by searching node 15.
Q: How does an application resume once an interrupt service procedure completes?
A: Resuming the execution of an application programme: RITE (interrupt return) instruction is reached…
Q: What are some of the advantages that virtualization offers?
A: HI THEREI AM ADDING ASNWER BELOWPLEASE GO THROUGH ITTHANK YOU
Q: Do you believe that reviewing and judging a text based on a set of criteria is a good strategy to…
A: Consider examining and judging a text based on a set of criteria to prevent being misled by false…
Q: the basic tricks you learn using advanced search and also Are you finding any better results?
A: Advanced search techniques are Boolean searching, narrowing searching, broadening searching,…
Q: Privacy of data: what is it? Is there a method to protect your personal information in five separate…
A: Institution: The link between data collection and distribution, technology, public expectations of…
Q: Draft a threat model for the following situation, making sure to include all of the relevant…
A: Given: Build a risk assessment for the following scenario, taking into account all of the relevant…
Q: Look into the graph colouring issue. To solve the issue, compare greedy and backtracking algorithms.…
A: Introduction: One definition of an algorithm is "a collection of instructions for solving a problem…
Q: Hashing passwords in files and keeping them encrypted are two different things. What is the…
A: Introduction: Data in a database is changed from a readable state to a ciphertext of unreadable…
Q: Write a C program that reads an integer n ≥ 2 and prints the smallest integer d > 2 such that n is…
A: Algorithm to find the factors of the given number Take input n which must be greater than 2. Take…
Q: 1)When our predictor variables have ranges and units that are quite different, it is pertinent to…
A: Given: There are two mcqs given in this question, lets discuss them one by one
Q: How do the words two-tier and three-tier architecture compare and contrast with one another?
A: Given: There is a distinction between two-tier and three-tier architecture. is asked.There are two…
Q: How does the iterative and incremental nature of the agile methodology relate to the more…
A: Introduction: Agile approaches try to make the right product by delivering small pieces of…
Q: In Oracle 12c, what different kinds of privileges are there to choose from? Clarify each category.
A: It's critical to keep track of allowed accesses when a database contains different users. The…
Q: Where exactly does a command line come into play when it comes to the actual execution of a program?
A: Command line: The command line is a blank line on the screen with a cursor that allows the user to…
Q: Is it possible to define Agile software development processes in a standard way?
A: Agile Software Development: Agile software development is flexible. Adaptive development techniques…
Q: What advantages and disadvantages does a relational database management system have?
A: Relational database management system is a database that stores data items and sets based on how…
Q: Answer the following sentences true or false 1. The loop execution is terminated on the basis of the…
A: here in the question ask true false for this statements.
Q: Explain how any business analytics courses influenced our group projects and/or tasks in terms of…
A: By applying their analytical abilities and reflecting on their experiences, students who participate…
Q: **JAVA PROGRAM** Create a class calledEmailTask1. Assume that email address is constructed by…
A: import java.util.Scanner; public class Main //calledEmailTask1{ public static void main(String[]…
Q: User-level instructions differ from privilege-level instructions.
A: Instructions for people with access: Privileged Instructions are the instructions that can only run…
Q: Define a function: Void Insert(char str1[], char str2[], int pos) to insert str2 to str1 from pos.…
A: Code: #include <stdio.h>#include <string.h>//Defining the required functionvoid…
Q: In cryptography, the term "salt" refers to the process of encrypting data. You must describe how it…
A: Explain the meaning of the term "salt" in the context of cryptography and why it's employed. It's…
Q: 5.1.2. (-) Prove that the chromatic number of a graph equals the maximum of the chromatic numbers of…
A:
Q: Why are there so many different partitioning algorithms in use by operating systems, and why are…
A: Partitional clustering are clustering methods used to classify observations, within a data set, into…
Q: What aspects of these designs are lacking in coherence, and what sorts of things may be done to make…
A: Lacking in coherence: characterized by a lack of coherence, including typical clarity or…
Step by step
Solved in 2 steps

- What are the CRC bits (R) associated with the payload containing first four bit 1101 and last four bit is the last digit of your reg number (i.e. 5, payload = 1101 0101). Suppose that the 4-bit generator (G) is 0101, and r = 3Question 17 Aa.For an original message size of 14 bits in a Hamming code FEC system, which one of the following bit position in the resulting message does the third parity bit NOT protect? 5 13 7 4 16 14 6 12 15 Full explain this question and text typing work only We should answer our question within 2 hours takes more time then we will reduce Rating Dont ignore this linea. Compute for the data efficiency of transmitting if the data format is a General Synchronous Data Frame. b. For an asynchronous data transmission (wherein 1 byte of data is accompanied by a specific number of auxiliary bits), how many start and stop bits are there if the data efficiency in transmitting is ? The number of start bits is equal to the number of stop bits.
- If an error happened in the following scenario, please mention whether it occurred. The sender sends the number “001011010” to the recipient. The devices make use of odd parity, 8-bit data, and a 1-bit (LSB) parity for each bit of information. What happens if the devices are utilizing even parity instead than odd? What are the communication protocols that are utilized in TESLA automobiles? Insert the schematic of the one(s) that you have discovered.We want to transmit 1000 characters with each character encoded as 8 bits. a. Find the number of transmitted bits for synchronous transmission. b. Find the number of transmitted bits for asynchronous transmission. c. Find the redundancy percent in each case.2) Compute data sent for a bit stream of 101011 with CRC using a generator 1010 Randomly assume any bit to have been corrupted, Illustrate how the receiver can detect if the data was corrupted.
- Any errors in the following scenario would be greatly appreciated. The sender sends "001011010" to the recipient. For each piece of information, it utilizes 8-bit data with odd parity and 1-bit (LSB) parity. If devices utilize even parity, why don't they use odd parity as well? The communication protocols used in Tesla vehicles may be found on the company's website. Provide a schematic if you have one.Why is the gap time between bytes vary in asynchronous transmission?Please check my answer and correct the part which is need to be foxed.And provide justification for the answer. a) The transmission time of a frame can be calculated as follows: Propagation delay (Tp) = distance/speed = 5km / 200000 km/s = 0.0025ms Transmission time (Tt) = frame size/bandwidth = 10000 * 8bits / (1Mbps * 10 ^ 6) = 0.008sec = 8ms Total time for transmission = 2 * Tp + Tt(since the frame has to travel from A to D and then D to A) = 2 * 0.0025ms + 8ms = 0.005ms + 8ms = 8.005ms The transmission time of the frame from A to D is 8.005 ms. b) The efficiency of the CSMA/CD protocol is given by the formula: Tt is the transmission time of a frame C is the number of collisions, Tp is the propagation time of a signal from one end of the segment to the other. Efficiency = Tt / (C * 2 * Tp + Tt + Tp) Assuming that there are no other stations transmitting or attempting to transmit on the segment, the transmission from A to D will succeed without collisions. Therefore,…
- 1. If they each want to send the following bit show the total signal sent Reciever Code R1 1 R2 1 R3 0 R4 1 2. How would R1 recover its signal?. 3. Consider a case with the same codes but only R1 wants to send. Reciever Code R1 1 R2 - R3 - R4 - What signal would be sent, and how would R1 recover its signal now? 4. If an error occurs in question 12, and some bits are flipped in the signal sent from positive to negative or the other way around, how many bits minimum would need to be flipped for R1 to recover the wrong signal? 5. CDMA has another important real-world use in addition to multiple access. Given the answer to the previous question, what do you think that purpose is? How does it accomplish this? Note: this is one big question where each part couldn't be seperately asked. The picture below is the 4 recievers from the start of the question.Consider the 3rd ,6th , and7th digits of your student ID composed of seven digits. Convert it to binary format (each digit is represented by a maximum of 3 bits). For example, 1060385 is simplified to 685 and then converted to 0110 1000 0101. Assume now that we want to send your simplified student ID while being able to detect and correct single bit errors. 1.1) Using two-dimensional parity check show what will be transmitted using datawords of size 4 bits.Consider the example below that shows both the payload and the two-dimensional parity bits (shown in blue), and where exactly one of the payload or parity bits shown has been corrupted. In this example, odd parity is used.

