Tom and Jerry recently saw the movie inception. Inspired by that movie they decided to play a complicated game. Analogous to the movie inception, Jerry is the dreamer and Tom is the thief who enters Jerry's dream in order to extract the secret code. Tom wins the game if he is able to extract the secret code, else Jerry wins the game. Note that here Tom has to extract the idea from Jerry. Tom after performing a lot of mathematical analysis finally ended up to one last step for which he requires a little computation. He has got an array of positive integers. If atleast one of them is prime, he will be able to crack the secret code and win the game, else Jerry wins the game. Output = For each test case output "Tom" (without quotes) if Tom wins the game, else output "Jerry" (without quotes). Example input
Tom and Jerry recently saw the movie inception. Inspired by that movie they decided to play a complicated game. Analogous to the movie inception, Jerry is the dreamer and Tom is the thief who enters Jerry's dream in order to extract the secret code. Tom wins the game if he is able to extract the secret code, else Jerry wins the game. Note that here Tom has to extract the idea from Jerry. Tom after performing a lot of mathematical analysis finally ended up to one last step for which he requires a little computation. He has got an array of positive integers. If atleast one of them is prime, he will be able to crack the secret code and win the game, else Jerry wins the game. Output = For each test case output "Tom" (without quotes) if Tom wins the game, else output "Jerry" (without quotes). Example input
Programming Logic & Design Comprehensive
9th Edition
ISBN:9781337669405
Author:FARRELL
Publisher:FARRELL
Chapter5: Looping
Section: Chapter Questions
Problem 2GZ
Related questions
Question
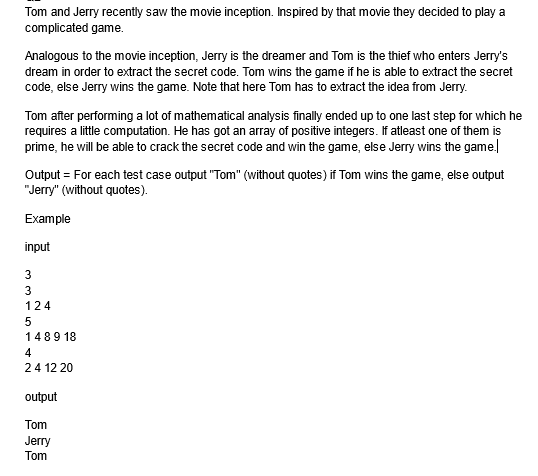
Transcribed Image Text:Tom and Jerry recently saw the movie inception. Inspired by that movie they decided to play a
complicated game.
Analogous to the movie inception, Jerry is the dreamer and Tom is the thief who enters Jerry's
dream in order to extract the secret code. Tom wins the game if he is able to extract the secret
code, else Jerry wins the game. Note that here Tom has to extract the idea from Jerry.
Tom after performing a lot of mathematical analysis finally ended up to one last step for which he
requires a little computation. He has got an array of positive integers. If atleast one of them is
prime, he will be able to crack the secret code and win the game, else Jerry wins the game.
Output = For each test case output "Tom" (without quotes) if Tom wins the game, else output
"Jerry" (without quotes).
Example
input
3
لا ل ف ال
3
124
5
1489 18
4
2 4 12 20
output
Tom
Jerry
Tom
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
Step by step
Solved in 4 steps with 3 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole

Programming Logic & Design Comprehensive
Computer Science
ISBN:
9781337669405
Author:
FARRELL
Publisher:
Cengage

Operations Research : Applications and Algorithms
Computer Science
ISBN:
9780534380588
Author:
Wayne L. Winston
Publisher:
Brooks Cole