UNCTIONS AND RECURSIVE FUNCTIONS Use #include Implement the picture sho
Q: In terms of SoS interface design, how useful is a unified user interface? What are the aspects that…
A: Answer:
Q: pooling,stride-2 --->3X3-filter (128-filters),Stride-2,padding-0 --> 2X2 max-pooling,stride-2 --->…
A: The answer is
Q: What kind of language do computers use to talk to one another? information travelling from facts to…
A: Machine code and Human language: The communication that occurs between computers and people is quite…
Q: What are the main ways you should use if you want the computer to look for operating system boot…
A: When a computer is switched on, its operating system begins booting. It is the first sequence of…
Q: fundamental steps should you take if you want the computer to first examine the CD-ROM for operating…
A: What fundamental steps should you take if you want the computer to first examine the CD-ROM for…
Q: Two different kinds of memory are referred to by the words RAM and Register respectively.
A: Please find the detailed answer in the following steps.
Q: What will the following Code segment print on the screen? int P = 30; int Q = 20;…
A: Given data: int P = 30;int Q = 20;System.out.println("Your Total purchase is \n" + (Q*P) +"…
Q: The Internet Protocol (IP) address of a computer is its unique identity on the Internet. How do…
A: Solution: To talk about IP addresses and mnemonic addresses, go to: Determine the greatest number of…
Q: When designing a compiler that can produce code that is both correct and efficient, what are the…
A: Answer:
Q: Cloud security is achieved by the use of IAM and the shared responsibility architecture. What is…
A: Answer: cloud security, exactly Cloud security is a myriad of technologies, agreements, and best…
Q: Question 3: Consider a non-standard Ethernet segment. The maximum distance between the two computers…
A:
Q: 1.) What is the fundamental difference between finite-difference and finite-element approaches?
A: NOTE :- As per our guidelines we are supposed to answer only one question. Kindly repost other…
Q: What variables influence the selection of a testing tool? What are the criteria for choosing a…
A: Answer:- The factors that must be considered while selecting an appropriate testing tool are as…
Q: What exactly is the meaning of computer science integration?
A: Introduction: Computer system integration is the linking of data, applications, APIs, and devices…
Q: What exactly do you mean by program?
A: Answer: Programs stored in computer memory allow the computer to perform various tasks…
Q: Create a list of the five most important areas or fields of internet governance, as well as the…
A: Areas or Fields of Internet governance: Modern organizations must struggle with a multitude of rules…
Q: A discussion is offered on how formative assessment may be utilised to answer user issues and…
A: NOTE :- Below i explain the answer in my own words by which you understand it well.…
Q: People often ask, "What are the top six reasons people want to learn about compilers?"
A: Compilers: A compiler changes the type or language of a programme. Machine code is generated by some…
Q: class diagram f
A: diagram in below step
Q: Should two different security architecture models be contrasted and compared?
A: Definition: While security architecture has many distinct meanings, it ultimately boils down to a…
Q: Do you believe that being locked in a deadlock with just one single-threaded process is possible?…
A: What is the actual nature of the impasse: A deadlock occurs when two computer programs sharing the…
Q: What is the influence of decreasing screen sizes on user interface design methodologies and…
A: The smartphone and tablet industry have revolutionised the market.
Q: How do I create a Jframe button the opens another jframe in java gui
A:
Q: Discuss the situation in which there is inadequate memory for new processes and the activities that…
A: The above question is solved in step 2 :-
Q: The study of computer science has nothing to do with actual computers, just as the study of medicine…
A: I Completely agree with the given sentence "The study of computer science has nothing to do with…
Q: Write at least one difference between items below (1)i++ versus ++i Answer: (2)int versus…
A: Here in this question we have asked to give at least one difference between these i++ versus ++i…
Q: waterfall model of the software development life cycle (SDLC), what are the stages? Where did Barry…
A: Answer:
Q: Examine the system's development, paying specific attention to significant persons and events.
A: Definition: Discuss the development of information systems, concentrating on the key persons and…
Q: 7. How would you declare a variable storing a person's name? String name = Jeff; String name =…
A: Answers of the problem is given below. in step 2 A declaration of flexibility in a computer…
Q: Which is a non-standard version of computing language? A. PROLOG B. APL C. ARMY D. PL/1
A: Some of the programming languages are not standardized by an international (or national) standard,…
Q: This is because computers have gotten so powerful. How can we prove that computers have been more…
A: Encryption: Computers have proven reliable since their introduction, but they are now omnipresent;…
Q: What does the word "computer programming" imply, and how does the process work? What are some of the…
A: Computer programming: The DML language is used in a basic SELECT query to create a list of table…
Q: When it comes to teaching and learning, how may the use of technology be beneficial? What impact has…
A: Introduction: When teachers are digitally literate and understand how to integrate ICT into the…
Q: "Which kind of network architecture is most suited for a university?" What is the most effective…
A: Answer: Client/server and peer-to-peer networks are both prevalent. Peer-to-peer LANs are…
Q: One alternative to take into consideration is purchasing a computer with Linux pre-installed from a…
A: Given: "Many computer makers sell PCs with Linux pre-installed," claims one computer manufacturer.…
Q: Write the appropriate or instruction to reset bits 5 and 7 of register AX, and keep all others…
A: MVI A, 00: instruction copies 00 to A. ANI 00: instruction performs bit by bit AND operation of…
Q: What impact will AI have on the future? What are some of the current AI software applications?…
A: Please find the answer below :
Q: Is it helpful to have a basic grasp of how computers work? What are the advantages that technology…
A: Computers: A computer is a programmable device for data storage, retrieval, and processing. The word…
Q: What's the use of cache memory if we already have volatile transistor-based RAM? What are the…
A: Answer:
Q: What exactly is a Software Process Model? Give three examples.
A: Explanation Software process model is a small representation of the vast software development…
Q: Is it possible for a single process to get stuck in a deadlock? Your responses must be justified.
A: For deadlock to occur following conditions must be satisfied:- 1. Mutual exclusion 2. Hold and Wait…
Q: The impact of a data leak on cloud security is still up for debate. There are a number of…
A: Data leakage from the cloud: Data infringement occurs when secure/confidential information is…
Q: this is Artificial Intelligence (AI) 1-draw a semantic nets for cat,dog, monkey,mammals, marmoset,…
A: Semantic network are an alternative to predicate logic as a form of knowledge representation. The…
Q: What are the top six justifications for one to educate themselves in compilers?
A: Answer:
Q: arable computing, including the Apple Watch and Android Wear, and provide your thoughts on how it…
A: We are acquainting clothing as a way with consider new aspects in the teaching construction of the…
Q: Write at least one difference between int vs integer
A: Integer is a class, while "int" is a primitive. A int is a data type that stores 32 bit signed…
Q: What precisely does it mean to "prototype" anything when it comes to the field of software…
A: Introduction: Making models of software applications, or inadequate versions of the software…
Q: gram so that the value of (X) is entered into Text N) is entered into input box. Calculate the value…
A: The code of the given VBA is given as,
Q: In a single command, append the contents of the /etc directory to the file called number2 that you…
A: In Linux, the output of the command can be redirected to a file using redirection operators. > :…
Q: Open source and proprietary word processors are compared, with an example provided for each. Free…
A: An application software programmer, sometimes referred to as a "App," is a computer programmer that…
MULTIPLE FUNCTIONS AND RECURSIVE FUNCTIONS
Use #include<stdio.h>
Implement the picture shown below.
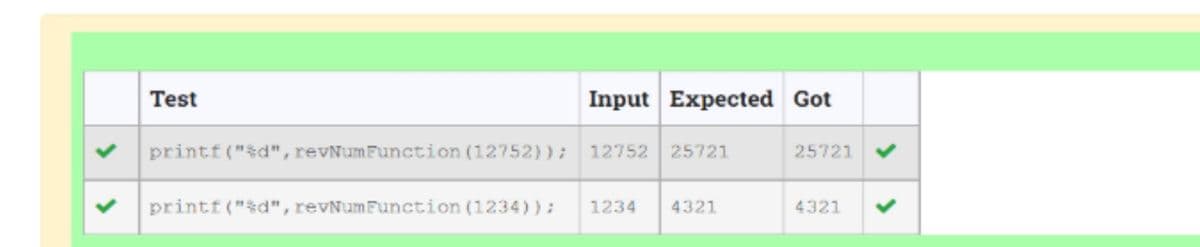
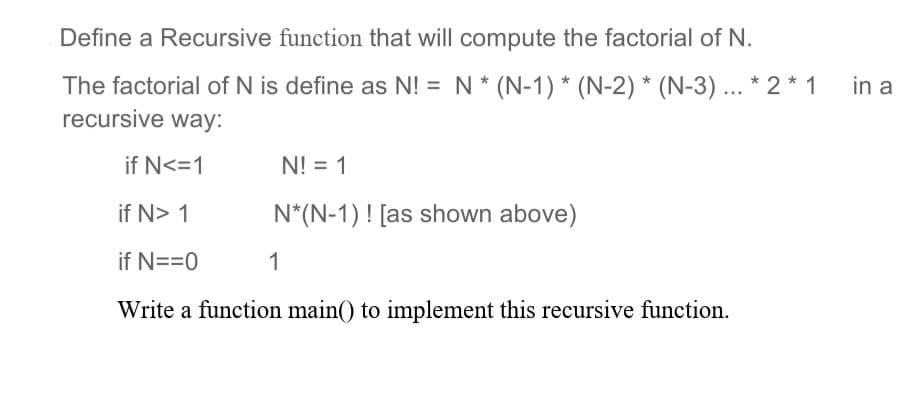
Step by step
Solved in 5 steps with 3 images

- For function log, write the missing base case condition and the recursive call. This function computes the log of n to the base b. As an example: log 8 to the base 2 equals 3 since 8 = 2*2*2. We can find this by dividing 8 by 2 until we reach 1, and we count the number of divisions we make. You should assume that n is exactly b to some integer power. Examples: log(2, 4) -> 2 and log(10, 100) -> 2 public int log(int b, int n ) { if <<Missing base case condition>> { return 0; } else { return <<Missing a Recursive case action>> }}The binomial coefficient C(N,k) can be defined recursively as follows: C(N,0) = 1, C(N,N) = 1, and for 0 < k < N, C(N,k) = C(N-1,k) + C(N - 1,k - 1). Write a function and give an analysis of the running time to compute the binomial coefficients as follows: A. The function is written recursively.In C programming Mathematically, given a function f, we recursively define fk(n) as follows: if k = 1, f1(n) = f(n). Otherwise, for k > 1, fk(n) = f(fk-1(n)). Assume that there is an existing function f, which takes in a single integer and returns an integer. Write a recursive function fcomp, which takes in both n and k (k > 0), and returns fk(n). int f(int n);int fcomp(int n, int k){
- Write a recursive function in f#, named specialSum, that has the followeing signature: int * int -> int, where sum(m,n) = m + (m +1) + (m+2) + ... + (m + (n-1)) + (m+n) for m >= 0 and n >= 0: (Hint use two clauses with (m,0) and (m,n) A PATTERNS.) start code with let rec specialSum (m,n) match m,n with | m,0 -> | m,n - >Write a recursive fibonacci (n) function with an expression body. The function should return an Int; it will be too slow to deal with inputs whose fibonacci numbers are too large anyway. You do *not* need to use memoization. Note that: fibonacci(0) = 0 fibonacci(1) = 1 fibonacci(n, where n is greater than 1) = fibonacci(n-2) + fibonacci(n - 1)Write a recursive function using python for the problem: A palindrome is a sequence of characters which is the same when the sequence is reversed. Given an array A indexed from p to q containing characters, determine if the sequence of characters in A[p..q] forms a palindrome. Return True is a palindrome is formed and return False if it does not.
- Write a recursive function that, given a sequence of comparable values, returns the count of elements where the current element is less than the following ( next ) element in the given sequence. See the examples given below. def count_ordered ( seq ) : """ Input : A sequence of comparable elements Output : The number of elements that are less than the following element in the sequence Example : >>> count_ordered ( [ 1 , 2 , 3 , 4 , 5 , 6 ] ) 5 >>> count_ordered ( ( 1 , 12, 7.3 , -2,4 ) ) 2 >>> count_ordered ( 'Python' ) 2 >>> count_ordered ( [ 6 ] ) 0 >>> count_ordered ( [ ] ) 0 """ In the first example above , count_ordered ( [ 1,2,3,4,5,6 ] )the returned answer is 5 because for all the first 5 numbers the current number is less than the next number. In the second example above, count_ordered ( ( 1,12,7.3 , -2,4 ) )the…a) Write a non-recursive function in C++/ to multiply all even numbers from 2 to n, where n is an input to the function, and n>=2. (reminder: An even number is divisible by 2 and generates a remainder of 0. for example 2,4,6,... are even numbers). b) Analyze your algorithm in part (a) in the worst-case. Show all your work. Then express the time as Big-O().(a) Give a recursive definition of F(n) where F(n) =1+2+3+....+n. (b) Find the value of a4 if a1 = 1, a2 = 2, and an =an−1 + an−2 +· · ·+a1
- Write a recursive function named decrypt, which takes a string s and a dictionary d where each key in the dictionary is a string word associated with a secret code as its key. This function should return the list of all possible ways (order it returns it in doesn’t matter) in which the string s can be decoded by splitting it into secret codes and separating the corresponding words of the decoded word with spaces. For instance, calling decrypt('turing', {'turing': 'A', 'tur': 'B', 'ing': 'C', 'tu': 'D', 'ring': 'E', 'ri': 'F', 'ng': 'G'}) returns ['A', 'D E', 'D F G', 'B C']. def decrypt(s: str, d: {str: str}) -> [str]:Write a recursive function for Euclid's algorithm to find the greatest common divisor (gcd) of two positive integers. gcd is the largest integer that divides evenly into both of them. For example, the gcd(102, 68) = 34. You may recall learning about the greatest common divisor when you learned to reduce fractions. For example, we can simplify 68/102 to 2/3 by dividing both numerator and denominator by 34, their gcd. Finding the gcd of huge numbers is an important problem that arises in many commercial applications. We can efficiently compute the gcd using the following property, which holds for positive integers p and q: If p > q, the gcd of p and q is the same as the gcd of q and p % q.Define a recursive function (rem r b) that, given a regular expression r and a bool b, returns a new regular expression r′ that matches exactly the set of all strings s such that string bs is matched by r. We will call r′ the remainder of r after division by b. For example, if r matches {T,FF T,TFF} and b = T, then r′ can be any regular expression that matches exactly the set {ε,FF} (because T and TFF are the only strings matched by r that begin with b = T, and their remainders are ε and FF, respectively). Here are some examples of what your function could output (but these are not the only answers!): • rem (false(false+true)∗) false = (false+true)∗ • rem (false(false+true)∗) true = ∅• rem (false∗ + true∗) true = true∗• rem ((false∗)(true∗)) true = true∗ Your implementation need not output these exact regular expressions as long as it always outputs an equivalent regular expression (i.e., one that matches the same set of strings as the given answer). These are also not the only test…

