Use cin to read floating-point numbers from input as area readings until four readings are read that are greater than 35.0. Output the four readings in the given range. End each output with a newline. Ex: If the input is 35.0 35.6 35.9 36.0 35.2, then the output is: 35.6 35.9 36.0 35.2 Note: Use fixed and setprecision (1) to set one digit after the decimal point. 1 #include 2 #include 3 using namespace std; 4 5 int main() { 6 7 8 9 10 11 12} double currentArea; int numSuccesses; /* Your code goes here */ return 0;
Use cin to read floating-point numbers from input as area readings until four readings are read that are greater than 35.0. Output the four readings in the given range. End each output with a newline. Ex: If the input is 35.0 35.6 35.9 36.0 35.2, then the output is: 35.6 35.9 36.0 35.2 Note: Use fixed and setprecision (1) to set one digit after the decimal point. 1 #include 2 #include 3 using namespace std; 4 5 int main() { 6 7 8 9 10 11 12} double currentArea; int numSuccesses; /* Your code goes here */ return 0;
C++ Programming: From Problem Analysis to Program Design
8th Edition
ISBN:9781337102087
Author:D. S. Malik
Publisher:D. S. Malik
Chapter5: Control Structures Ii (repetition)
Section: Chapter Questions
Problem 7SA
Related questions
Question
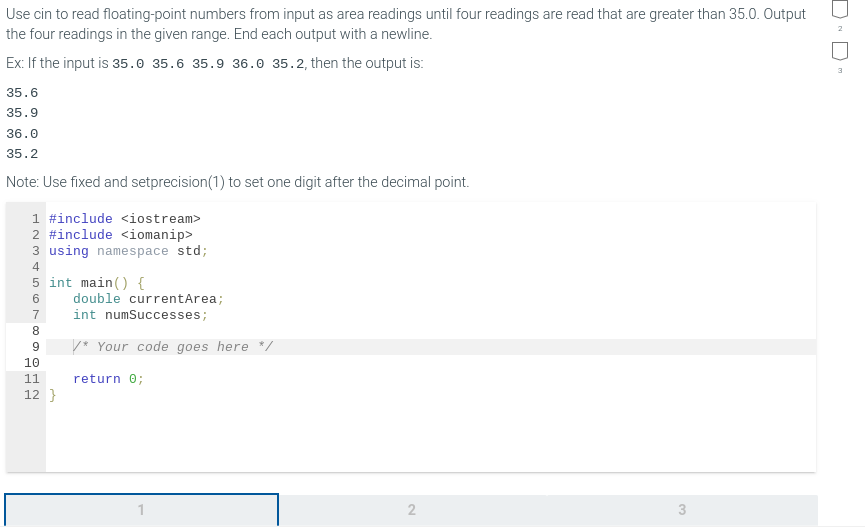
Transcribed Image Text:Use cin to read floating-point numbers from input as area readings until four readings are read that are greater than 35.0. Output
the four readings in the given range. End each output with a newline.
Ex: If the input is 35.0 35.6 35.9 36.0 35.2, then the output is:
35.6
35.9
36.0
35.2
Note: Use fixed and setprecision (1) to set one digit after the decimal point.
1 #include <iostream>
2 #include <iomanip>
3 using namespace std;
4
5 int main() {
6
7
8
9
10
11
12}
double currentArea;
int numSuccesses;
* Your code goes here */
return 0;
2
3
Expert Solution
This question has been solved!
Explore an expertly crafted, step-by-step solution for a thorough understanding of key concepts.
This is a popular solution!
Trending now
This is a popular solution!
Step by step
Solved in 4 steps with 2 images

Knowledge Booster
Learn more about
Need a deep-dive on the concept behind this application? Look no further. Learn more about this topic, computer-science and related others by exploring similar questions and additional content below.Recommended textbooks for you

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning

C++ Programming: From Problem Analysis to Program…
Computer Science
ISBN:
9781337102087
Author:
D. S. Malik
Publisher:
Cengage Learning